Yesterday, an abrupt shutdown notice arrived in my mail from a favorite encrypted cloud storage service, Wuala.
Effective as of today, you will no longer be able to purchase storage or renew existing accounts. Full account service will continue through 30 September 2015, at which point all active accounts will shift to read-only mode. Effective Sunday, 15 November 2015, the Wuala cloud service will terminate.
In short, if you were a consumer or business relying upon Wuala to store and share your files, you’ve been given just over a month’s notice to make alternative arrangements.
Wuala is owned by LaCie, who in turn were acquired by parent company Seagate in 2012. Clearly, for whatever reason, the firm has decided to rethink its plans for offering cloud-based storage services.
One thing that crossed my mind for a moment, was whether Wuala might have fallen for a similar fate as other products and services which had encryption at their heart.
 TrueCrypt, and Lavabit, for instance, shut down amongst concerns that they might no longer offer the protection and privacy that users might wish for, after receiving undue interest from law enforcement agencies keen for the secrets customers protect with the services to spill out.
TrueCrypt, and Lavabit, for instance, shut down amongst concerns that they might no longer offer the protection and privacy that users might wish for, after receiving undue interest from law enforcement agencies keen for the secrets customers protect with the services to spill out.
I have no reason to believe that Wuala’s demise is anything more than a commercial decision by LaCie/Seagate, but I am left with no way to easily tell.
After all, *if* the shut down was because Wuala believed it no longer had a way to protect the privacy of users from the undue attention of surveillance agencies, how would it tell me if was also served with a gag order at the same time?
When a company receives a notice that they must share private information with a government entity, the notice is usually accompanied with a gag order that prohibits the company from mentioning that they have been forced to give up the information.
 Wuala, unlike rivals such as SpiderOak, does not appear to have a warrant canary which (in its absence) could alert users that something peculiar was afoot.
Wuala, unlike rivals such as SpiderOak, does not appear to have a warrant canary which (in its absence) could alert users that something peculiar was afoot.
A warrant canary, named after the canary taken to the coalface of the early days of mining.
Canaries are sensitive to carbon monoxide and other lethal gasses. If a canary in a coal mine stopped singing (and subsequently died), the miners knew that the air had become toxic, requiring immediate evacuation.
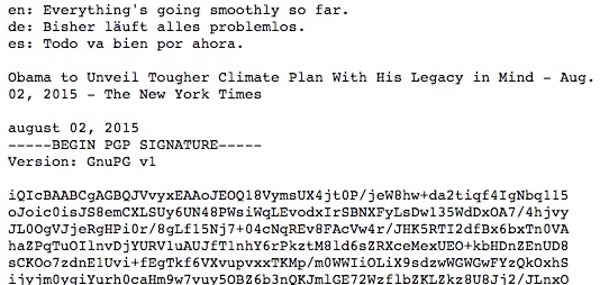
A clever method in use by some organizations to tacitly notify clients about any binding gag orders is to pre-emptively state that they have not been issued any such notice in the last few months.
Here is the current SpiderOak warrant canary page, for instance:
It may never be clear why Wuala decided to close down, but its rapid farewell can only make one wonder if there is the remotest chance, like others before it, that it preferred to close its doors rather than comply with a court-order to reveal its encryption keys.
Wuala is thankfully giving customers an opportunity to download their data, and is offering refunds to those customers who have paid in advance for the service. It is also recommending users that they might consider switching to a similar encrypted cloud storage service called Tresorit.
If you find a warrant canary on Tresorit’s site, let me know.



Graham, were you aware that ANOTHER online backup service has now been shutdown (as of August 18, 2015)?
Here’s the letter they sent out to their users:
Dear Cyphertite User,
It is with a heavy heart that I am announcing the coming closure of the Cyphertite online backup service in 2 months’ time, on August 18th, 2015.
Due to limited interest in Cyphertite, we were not able to generate enough revenue to justify continuing to operate the service. In an attempt to make transition away from using the Cyphertite service less
painful for existing users, we are giving a 2 month notice that the service is ending. In some cases, this means you simply need to find another online backup service and make the initial backup there before
discontinuing use of Cyphertite. In other cases, the migration process away from Cyphertite may be more involved, e.g. you need to restore some data before the service closes. I suggest you start thinking about
finding a replacement for Cyphertite sooner rather than later, as in “have a proper backup at another backup provider before August 18th”.
It has been a pleasure to serve all of our customers over the past several years. We feel very strongly that everyone, not just select groups, should have access to secure data storage tools as a matter of personal privacy. As such, we truly appreciate everyone who joined us in asserting their right to online data privacy. Since we are closing Cyphertite, some customers may be left wondering “Well, great… what now? I have to find a new secure online backup service.” so I figured a
few suggestions for alternatives would be helpful:
Windows users – For our existing windows users, we recommend SpiderOak – https://spideroak.com
Linux/UNIX/OSX users – For all our command line people, we recommend Tarsnap – https://www.tarsnap.com
Despite shuttering Cyphertite in the near future, we will continue to have a presence in the data security software space, albeit via a new company, Company 0 LLC (https://companyzero.com). In the next few months we will be making an announcement regarding a new project that may be of interest to existing Cyphertite users, so stay tuned.
Sincerely,
Jacob Yocom-Piatt
CEO
Conformal Systems, LLC.
Regarding Tresorit I've looked high and low on their website but I can't find a warrant canary.
Switzerland don't have a provision allowing law enforcement to compel companies to provide backdoors and prosecutors must disclose any requests for data (so at to allow an appeal) in advance – according to Wikipedia. Their strict privacy laws make it unlikely any backdoor would be allowed.
From looking at the technical whitepaper your data is encrypted on your device before being sent to their servers so unless the software is backdoored then even if a request for disclosure was received (and fulfilled) all they'd have access to is the ciphertext. Because they use Microsoft Azure to host their already encrypted data, Microsoft themselves encrypt and break the ciphertext into chunks before being re-encrypted.
They're apparently looking at making their encryption/decryption routines open-source. My only criticism is their high-price, but perhaps that's the price to pay for the privacy conscious.