If you visit the company profile page on the website of hardware manufacturer LaCie, you’ll find this message from the company’s chairman:
If you visit the company profile page on the website of hardware manufacturer LaCie, you’ll find this message from the company’s chairman:
It’s easy to replace a keyboard, processor, or printer – but not your data. Your life is on your hard drive; you need to be able to back up to a second place easily, and feel like you’ve made the best choice for your data’s safety and security.
He is, of course, absolutely right. It is easy to replace a broken PC or buy a new printer if the old one goes on the blink.
But it’s enormously awkward and painful (and perhaps impossible) to replace your data if it is lost, let alone make it private again if it is exposed.
Here’s another interesting article, newly publish on LaCie’s website under the warm-and-cosy title of “LaCie Incident Notification”.
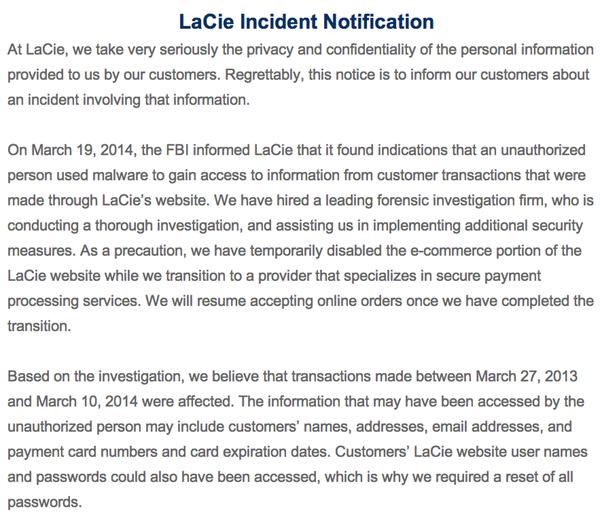
At LaCie, we take very seriously the privacy and confidentiality of the personal information provided to us by our customers. Regrettably, this notice is to inform our customers about an incident involving that information.
On March 19, 2014, the FBI informed LaCie that it found indications that an unauthorized person used malware to gain access to information from customer transactions that were made through LaCie’s website. We have hired a leading forensic investigation firm, who is conducting a thorough investigation, and assisting us in implementing additional security measures. As a precaution, we have temporarily disabled the e-commerce portion of the LaCie website while we transition to a provider that specializes in secure payment processing services. We will resume accepting online orders once we have completed the transition.
Based on the investigation, we believe that transactions made between March 27, 2013 and March 10, 2014 were affected. The information that may have been accessed by the unauthorized person may include customers’ names, addresses, email addresses, and payment card numbers and card expiration dates. Customers’ LaCie website user names and passwords could also have been accessed, which is why we required a reset of all passwords.
We began notifying affected customers on April 11, 2014. If you used your card on LaCie’s website between March 27, 2013 and March 10, 2014 and did not receive a letter, you should review the additional information below on ways to protect yourself.
If you see a fraudulent charge on your card, please immediately contact the bank that issued your card. Major credit card companies typically guarantee cardholders will not be responsible for fraudulent charges. Please be on the lookout and review your account statements for any unauthorized activity.
We regret any inconvenience this may cause. Keeping customer information secure is a top priority at LaCie and we are working with the forensic firm to implement additional security measures. If you have questions, please call 866-236-8208 Monday through Friday between the hours of 9:00 AM and 7:00 PM EDT.
Oh dear.
Security blogger Brian Krebs believes that the attackers may have exploited vulnerabilities in Adobe’s ColdFusion software to gain access to LaCie’s online store.
As I told PC Pro when they asked for comment this morning, this kind of security breach has to be deeply embarrassing for any organisation.
It’s unclear at this time just how many LaCie customers may have been exposed, but it would seem sensible for anyone who has bought a product from the firm in the last year to keep a close eye on their credit card bills and be on the lookout for unusual transactions.
(Worryingly, LaCie don’t make any mention of encryption or password hashing).
But more than that, customers should also be asking the company tough questions about why it didn’t spot the intrusion earlier, and whether it had put enough resources into properly penetration testing its site to find and resolve weaknesses.
Customers also need to ensure that the password they used for LaCie is not also being used on any other sites – as hackers will often try to use hacked passwords to unlock other online accounts.
This isn’t a good time for LaCie’s competitors to feel too smug, however. How confident can other organisations be that their systems have not been compromised, and that they have taken enough precautions to deflect intruders?
Let us hope that LaCie is more proactive about sharing what it learns from this attack than it was in detecting it in the first place.