
Controversial short-term loan firm Wonga has some bad news for its current and former customers:
We believe there may have been illegal and unauthorised access to the personal data of some of our customers.
We are urgently working to establish further details and contacting those who we know have been impacted. The information may have included one or more of the following: name, e-mail address, home address, phone number, the last four digits of your card number (but not the whole number) and/or your bank account number and sort code.
We do not believe your Wonga account password was compromised and believe your account should be secure, however if you are concerned you should change your account password. We also recommend that you look out for any unusual activity across any bank accounts and online portals.
As The Guardian reports, current and former customers in the UK and Poland are thought to have been impacted by the security breach – a total of some 270,000 individuals, including 245,000 in the UK.
If you are one of those affected, my advice is to be very wary of unsolicited phone calls and emails that might be from scammers attempting to exploit the information. You would also be wise to keep a close eye on your finances for any unexpected transactions.
Wonga hasn’t yet shared details of how hackers might have accessed such sensitive information, but its website is surely high in the list of likely candidates.
That, after all, is how UK telecoms provider TalkTalk suffered a high profile hack in October 2015 through an elementary SQL injection attack.
Wonga has previously claimed that its website is “extremely secure”.
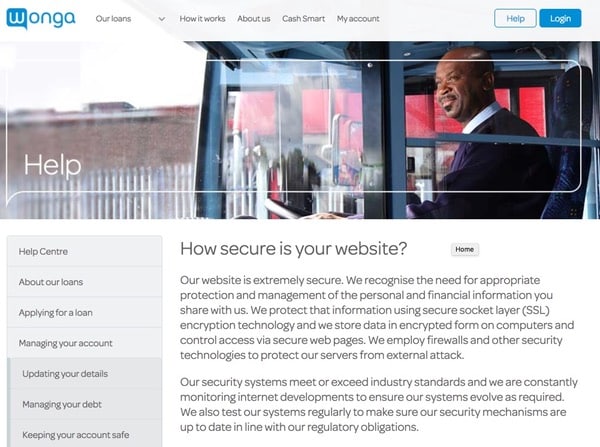
Our website is extremely secure. We recognise the need for appropriate protection and management of the personal and financial information you share with us. We protect that information using secure socket layer (SSL) encryption technology and we store data in encrypted form on computers and control access via secure web pages. We employ firewalls and other security technologies to protect our servers from external attack.
Our security systems meet or exceed industry standards and we are constantly monitoring internet developments to ensure our systems evolve as required. We also test our systems regularly to make sure our security mechanisms are up to date in line with our regulatory obligations.
Of course that reassuring text was written by Wonga before it discovered that it had suffered a data breach that had potentially exposed details of a quarter of a million former and current customers.
I guess in due course it will be all too clear whether they should have felt so confident.
I, for one, will be watching with high interest.
Update: We discuss the Wonga data breach more in this edition of the “Smashing Security” podcast.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Yeah, those are the guys who produce the Cyber Daily newsletter, which you can get at recordedfuture.com/intel.
And they go scouring the web looking for the latest information on new vulnerabilities and emerging threats, and then they deliver lots and lots of details about all that kind of stuff straight into your inbox.
Hello, hello, and welcome to another episode of Smashing Security, number 16, for the 13th of April, 2017. And as always, I'm joined by my buddy Carole. Hi, Carole.
And a few things have cropped up. But here's one which has really caught my eye. Have you guys ever heard of these things called IMSI catchers?
They sort of come in suitcase-sized boxes and they can use—
And effectively they get between your phone and your cell phone provider's real cell towers, which means, of course, that they're fantastic for intercepting communications.
They could also be used, of course, for sending fake messages to phones, not only intercepting messages, but also sending a fake message to someone, which could have interesting consequences.
Now, in the wrong hands, I think you'd agree that is a pretty powerful bit of kit, isn't it?
The good news is that the average Joe in the street isn't going to find it terribly easy to get hold of one themselves, right? They're pretty expensive.
First of all, they can cost hundreds of thousands of dollars.
And the reason why I'm talking about IMSI catchers in this particular episode is that there's just been released an undercover Al Jazeera investigation.
Al Jazeera TV have uncovered that firms are prepared to break global sanctions to ship this kind of surveillance and spying equipment to dodgy authoritarian regimes around the world.
And of course, they're going to be used against their citizens. They're going to be used by rogue nations to spy upon activists, political rivals, dissidents, and—
Our undercover reporter exposes the spy merchants willing to sell powerful eavesdropping equipment to anyone willing to pay.
Europe's most advanced producers of spyware explain how they circumvent international sanctions with ease.
The surveillance state is the acid that eats out democracy from within.
Inside the spyware game: big money, dirty tricks, and a legal structure unable to control who is spying on you.
So the full report lasts something like 45 minutes, and I recommend people go and check it out on YouTube if you don't get Al Jazeera TV.
But they do name and shame some of the companies who they spoke to, including companies in Italy.
And you think, hang on, you know, what are the Italians doing, doing this kind of thing?
Well, there are a number of agencies in Italy or corporations who are building surveillance equipment. There's a sort of mini industry out there.
Iran, there are global sanctions against them.
South Sudan, there's obviously been a lot of unrest and there's been a lot of spying upon people because of the many deaths which have been going on down there.
And it's far easier for those sort of countries to get hold of this kind of equipment if they want.
In one case, the Al Jazeera guy, what Al Jazeera actually did was they found an insider, someone who worked inside the industry. They called him only James.
And so he's filmed throughout the report in sort of shadow and they've given him sort of a computer-y kind voice.
But he was the guy who was actually meeting these guys, secretly filming them as they were discussing it.
And he even came across one Chinese-based company who said, "We don't actually care who your customer is," which meant that potentially it may not just have been a dictatorship, it could have been an organized criminal gang, it could even have been terrorists who are using this information.
Also, you have to apply for export licenses.
Any technology which is encrypting or decrypting information, you have to be very careful where you sell it around the world because it could be used potentially for these sort of nefarious purposes as well.
They're using gray markets. And so what they might do is they say, look, you can't buy this directly from us in Italy. So we can't sell this to you in Sudan, for instance.
But if you had a company in Tanzania who—
Or you could buy it from our manufacturers in Turkey who may find it easier to get an export licence than we would in Italy because this kind of thing is— obviously governments are trying to crack down on this kind of thing, but it looks like these companies, so much money at stake, they are finding ways in order to sell it.
Well, I'll let you be your own judge when you watch the video as to how believable you actually find that.
In one case, one of the companies actually said this guy who came to us and talked to us about purchasing this, we identified him as potentially an employee of a rival firm.
And so we were just stringing him along, and we were never planning to sell anything to him. And you're kind of like, come on.
The truth is money talks in this business, and people are prepared to do anything if the right greenbacks are on the table.
It's quite good that it's the size of a suitcase, because it's not something you can just hide out easily without it being detected in a corporate or political environment.
They're producing documentation without the logos on of the company again.
So it's sort of white-labeled stuff because they don't want it coming back to them because potentially not only could they be making tens of millions of euros, but also potentially they could end up serving jail time as well.
And obviously there will be people listening to our podcast who work in security and may even work for some of these firms who produce this kind of technology.
And I guess what we're really saying is if you're one of those people, I'm sure from time to time you're questioning whether you're doing the right thing.
And I'd argue that you know, you need to change your company from the inside or you need to get out of that company.
And that is that the way that they found these catchers sprinkled throughout town and at Montreal Airport was that they used this gadget called CryptoPhone that's out of a German company.
I forget the name. It actually kind of turns the tables. It actually can find the use of IMSI catchers in an area. The CBC, in their investigation, talked to the U.S.
supplier of these devices to catch these things, and he analyzed the stuff they were finding in Ottawa and Montreal and said, oh, this has got the stamp of a Chinese IMSI catcher.
I just found it interesting to see this, you can actually find something that catches the catchers with that CryptoPhone.
As one side develops something to snoop upon the other, the other side will attempt to find ways to detect that they are being snooped upon.
Okay, Lisa, what have you got up your sleeve for us today?
And a developer left this telemarketer— well, the telemarketer went out of business, didn't pay its filing fees in Florida and just went belly up.
And a developer who was working with the telemarketer for some reason left with a copy of the database.
And we're talking about a database that has incredibly sensitive information in it. It's got Social Security numbers, names, email addresses, whether you're on insulin or not.
Do you have sleep apnea? Are you being assisted by a healthcare aide or by a child? What's their name? So what springs to your mind?
Probably what springs to my mind is this is just a goldmine for phishers.
So, you know, somebody could call you up and it's happened in the past, somebody would call you and they know your doctor's name, and yes, doctor's names were included in this recently exposed database.
So the database did belong to the telemarketer. So it comes from them. They didn't necessarily break any laws.
There aren't necessarily— databreaches.net, which is run by this licensed healthcare professional who's really interested in security when it comes to medical stuff, pointed out that we don't know that any laws have been broken.
What it sounds more to me is sort of this neglect of data.
And it points to, it was one of those intentions to have a business that provides database solutions for medical suppliers.
But he said, he told Zach Whittaker over at ZDNet and the DataBreaches.net blogger that it just was, it was too gnarly, it was too hairy, the creation of things. So he shelved it.
He left it on this AWS instance and it wasn't encrypted.
Yeah, it's that search engine for everything that's internet connected that comes up with this lovely index of insecure open services online.
And once you no longer have any use for it, destroy it, etc. But what sort of advice can we give the regular man and woman in the street regarding?
Well, you know, it's kind of tough.
If you can't move to Canada, then you've got to be really mindful of the information that you give telemarketers.
I mean, these people are coming at elderly people who probably aren't real cash flush, and they're saying, oh, we've got these discount programs for diabetic supplies.
Those supplies are super super expensive. I know lots of people in the Facebook forums for diabetics that say, oh, go to this one, go to that one.
I would suggest that instead of handing over your doctor's name and your Social Security number, your taxpayer ID, all that jazz, just back away from somebody calling you or even making these calls.
Talk to the drug companies themselves. If you're in the US, they know that it's an issue to pay for this stuff. And many of them have programs that can help.
At least I am aware of such programs at insulin makers such as Lilly.
When you think about somebody calling you and wanting really specific, really intimate knowledge about you, you don't even know if the caller is legitimate.
If you think your details might've been doxxed, you can always go look up your email or your name on Have I Been Pwned? 'Cause Troy Hunt over there has uploaded the whole database.
That's particularly important because there's no company left over that can pay for that fraud alert for you, or that's going to necessarily reach out and tell you that it's been done.
I mean, they do have something like 391,000 unique email addresses in that database.
And at least that's a start to reaching out to people, but who exactly is gonna do the reaching out now?
So we're really reliant upon journalists and podcasts and ZDNet and others to get the word out there.
We've got this great resource in Have I Been Pwned run by Troy Hunt where people can enter their email address and find out if their details have potentially been leaked as a result of this, as well as obviously checking with many of the other breaches which have occurred.
And generally, the advice to people is just be really careful of people ringing you up out of the blue, trying to sell you medication to do with your diabetes, right?
Okay, Lisa, tell me, what does wonga mean? Do you know that term wonga?
So there's no hidden charges or nasty surprises.
Now, Wonga basically offer, they're a payday loan company. So they have high-cost credit, short-term loans.
And during this breach, which we actually don't know a lot about yet, I'll get to that in a second, but what seems to be stolen was name, email address, home address, phone number, the last 4 digits of your credit card, your bank account number and sort code.
Oof, right?
So they're saying they take customer data and security very seriously and that, you know, cyber attacks unfortunately are on the rise. So, yeah.
I mean, Wonga did tell TechCrunch that they're investigating illegal and unauthorized access to personal data.
But that doesn't necessarily tell us whether it was an attack via their website or a zero-day or vulnerability or whatever.
Interestingly, they have a section on their website about how secure their website is. And it starts with, our website is extremely secure. So I hope for their sake.
It's the sort of thing you learn on Security 101, first day as a web security expert, how to protect against that. If it's something that, that's gonna be embarrassing.
Of course, it might not be that sort of technology. It could be maybe, because they haven't really told us, have they?
It could be an insider inside the organization, something that, but—
You use it because, you know, maybe you can't meet your rent and you need to get it out quickly or this kind of thing. So it's not people that have a lot of extra dosh lying around.
And now a lot of their details can be used. I mean, their home addresses are there, right? Their phone numbers, everything.
So advice for anyone who's been affected by this, first, our apologies. It sucks. But I looked up at Wonga. They do have an FAQ page at Wonga.
They actually do have something on their homepage saying if you've been affected, go here.
At least their FAQ, they think your account is secure and that you do not need to take any action. I would suggest that you change your password.
And, you know, this is a very good time for those of you that may have used this password elsewhere to make sure that those are, you know, change those to unique passwords.
This is the exact reason because they could try, if they had access to that password, they could use it using your username and your email address, which how many people use their email address as their username?
Now, Wonga also say they're going to be alerting financial institutions on the issue, et cetera.
But I think that everyone would be wise to contact them themselves, contact your bank, tell them to look out for suspicious activity, tell them your name's on the list and that you've been impacted by this.
I'd also suggest keeping a record actually of any conversations you have with people, with bankers if you call. Actually, Wonga say if you have any questions, you can call them.
And an article in The Sun today was saying that in fact, it's a pay-for line. So it's not a free toll line.
And people calling from mobiles can pay up to 55p, that's 70 cents a minute. And one guy spent 40 minutes on the phone.
So if he'd called from one of those pay plans, it'd be 20 quid or 25 bucks for the privilege.
Now the other thing you guys want to watch out for here, really, just last piece of advice, is you want to watch out for lateral attacks, right?
So these are people now who might want to try and reach out to you via email or call you on the phone or send you a letter that may be requesting information from you that looks official or new social connections.
So you just got to be on your guard and watch out for this stuff.
And what happens is the scammers have got your phone number and they maybe know something about your account details as well.
They ring you up, they may pretend to be from the company that has been breached, and that way they can gather additional information because of course they can reassure you that, oh, they're legitimate because they know the last 4 digits of your card number, or they know your bank account number and sort code, they know your home address.
And it can be very convincing and people often can be fooled by someone who calls them up on the phone, things that they maybe wouldn't believe if it arrived in an email.
So if you are concerned, go to their website and check.
I think there's people in, I think Poland, a database in Poland and in the UK that have been impacted, but not all of Wonga's customer base.
This is if you've used it once, your name and, you know, your details could be in the wrong hands now.
You could leave a review if you would as well. You can— we're also available in many other podcast apps too, including now iHeartRadio.
If you have iHeartRadio, you can check us out there as well. Please do check us out and subscribe. And that way you'll always get the latest episode in your podcatcher.
Really appreciate having you available and sharing your stories with us. Always a pleasure. Cheers. And if you would the show, tell your friends, follow us on Twitter.
We're @SmashingSecurity on Twitter. That's Smashing without a G security. And until next time, toodle-oo, bye-bye.



Stealing the financial details of people that in general are suffering financially somehow is probably not the most lucrative. That said, how remarkable.
One can see the nature of the security notice they have on their site – worded in such a way as to need no foreseeable updates. For example, "We also test our systems regularly" does not describe a frequency. A publicly available monthly security check bulletin on their website would be a better solution.
Puntastic.
"Stealing the financial details of people that in general are suffering financially somehow is probably not the most lucrative."
Those people are highly corruptible. Find out where they work and if that's 'interesting' offer them 'help' with their debts. There's your insider threat.