Last week, a storm erupted on the net after it became widely known that Superfish – software that was being pre-installed on Lenovo PCs – could compromise users’ security and privacy.
The problem with Superfish was not just that it injected money-making ads into websites, but that it used a self-signed root certificate to intercept encrypted HTTPS traffic for every website users visited – replacing legitimate site certificates with its own.
As a result, a major security vulnerability was introduced, potentially allowing online criminals to launch man-in-the-middle attacks, and destroying any trust users might have had that their communications were secure.
Superfish, you could say, had brought Lenovo into deep water.
What makes Superfish particularly bad from the security point of view is that it uses the same digital certificate on different computers, using an “SSL hijacker” software development kit sold by Israeli firm Komodia.
What’s more the certificate’s private key password was swiftly cracked by security researcher Robert Graham.
And what was the password used by Komodia’s code? “komodia”. Yes, really. You have permission to bang your head against the wall at this point.
Lenovo handled the situation badly, firstly not realising the importance of the issue, then thinking the only concern was the adware-nature of the code, before finally admitting that it had messed up badly and producing a tool to remove Superfish (and, crucially, its certificate-meddling) from affected PCs.

The furore about Superfish has turned a spotlight not just onto the software, but onto other software developers who might have incorporated Komodia’s controversial HTTPS-breaking code.
More than a dozen software programs have been found using “SSL hijacker” – the same code that was being used by Superfish.
One of the most worrying is PrivDog.
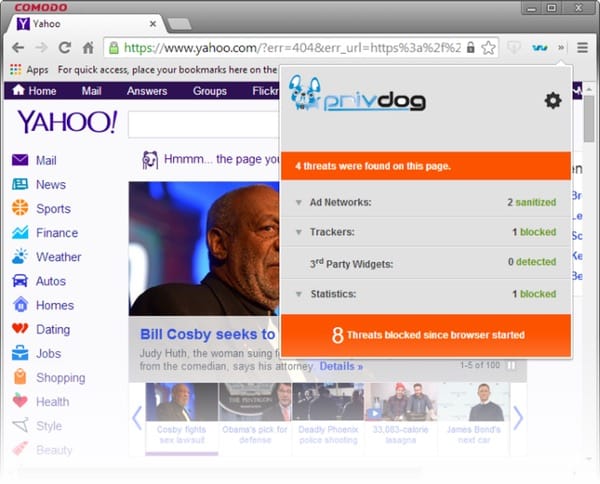
PrivDog, ironically, describes itself as “a new layer of internet security”, ensuring that “your browser will only display ads from a trusted source.”
That, in itself, sounds like a noble aim. Time and time again, popular websites help infect visiting computers via malvertising.
But while replacing ads, PrivDog is also leaving computers vulnerable to attack.
And it appears to be even more dangerous than SuperFish, as technology blogger Hanno Böck explains:
“While Superfish used the same certificate and key on all hosts PrivDog recreates a key/cert on every installation. However here comes the big flaw: PrivDog will intercept every certificate and replace it with one signed by its root key. And that means also certificates that weren’t valid in the first place. It will turn your Browser into one that just accepts every HTTPS certificate out there, whether it’s been signed by a certificate authority or not.”

In short, PrivDog doesn’t validate certificates at all.
How are you supposed to trust the web ever again, if you’re running “a new layer of internet security” that destroys the entire concept of web certificates? A web where every rogue certificate is accepted, where no browser warnings are triggered, and where certificates (bad or not) are replaced by one that the browser will trust.
A hacker could exploit such a system to intercept and decrypt communications with a secure website.
Astonishingly, according to a CERT advisory, PrivDog is promoted by Comodo Group, an organisation known around the world for… wait for it… selling SSL certificates and authentication solutions.
This article originally appeared on the Optimal Security blog.


