
Beware if you’re paying your bills for local government services – the payment information you type into that web form may be heading straight to cybercriminals.
Security experts at Trend Micro report that they have identified eight cities in the USA where online payment portals have been compromised to host Magecart-style credit card skimming code.
Magecart is a family of Javascript malware used to steal credit card details and personal information from unsuspecting internet users as they interact with websites – often as sensitive details are entered to make a purchase.
What makes this type of attack often more serious than a conventional data breach, is that most companies do not store your full credit card details, such as your CVV security code. But those details are entered on online checkout forms by consumers, and can be stolen by a malicious script hidden in the website’s code.
As Trend Micro explains, the common factor between the affected websites they have uncovered is that they all use the third-party Click2Gov platform:
These sites all appear to have been built using Click2Gov, a web-based platform meant for use by local governments. It is used to provide services such as community engagement, issues reporting, and online payment for local goverments. Residents can use the platform to pay for city services, such as utilities.
According to the researchers, the attacks against the eight unnamed US cities started in April, when malicious Javascript code was planted on the websites, silently harvesting credit card details and residents’ personal information as they entered it into online payment forms.
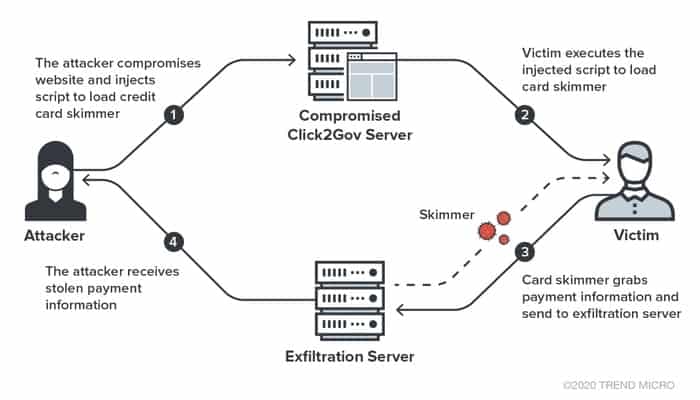
Unlike other skimmers which grab data on various types of payment forms, the skimmer used here is rather simple and only works on a Click2Gov payment form. No obfuscation or anti-debugging techniques were used. The skimmer hooks the submit event of the payment form; when a victim clicks the button to send the payment information, the skimmer will grab the information from the selected columns inside the payment form and immediately send the collected information to remote server via a HTTP POST request.
Details exfiltrated by the script to a remote server under the hackers’ control included credit card numbers, CVV security codes, card expiry dates, cardholder’s name, address, and postal code.
Simple the skimming code might be, but that doesn’t mean it’s not effective.
Rightly or wrongly, Click2Gov is earning itself a bad reputation. In recent years security researchers have been tracking attacks launched against the Click2Gov payment portal, with reports of breaches involving city websites stretching across the United States and Canada.
Late last year, for instance, the city of College Station admitted its Click2Gov online utility payment system had been hacked for some months, as had the City of Waco’s Click2Gov portal for water bill payments.
The onus is on cities to follow best practices when building and maintaining its online payment systems, ensuring that patches and security updates are applied in a timely fashion and that networks are properly secured.
Meanwhile, other websites with payment forms online would be wise to remember that credit-card skimming attacks are not limited to local governments taking payments from residents.
Magecart-style attacks have been seen hitting a diverse range of victims, including hotel chain booking websites, academic campuses, as well as the likes of Ticketmaster, British Airways, Forbes, Umbro, Vision Direct, and Newegg.
If you’re making online purchases (and hey, these days, who isn’t?) you might want to investigate disposable virtual payment cards, so you’re never exposing your real life credit card to the websites to which you are making a payment. A virtual card could be locked to a single merchant, have a limited amount that can be used in a single payment, or be single-use.
There is more discussion of virtual credit cards in this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
I'll probably bleep out, actually. But the name is... Keep collapse. Yes, that's... Keep collapse? Yes. You're just going to keep me busy with the bleeper, aren't you? Is that what's going to happen? The entire fucking episode. So how do you spell keep collapse? Smashing Security. Episode 182. Space Force. Hello, hello and welcome to Smashing Security episode 182. My name's Graham Cluley.
And I'm Carole Theriault.
And this week, Carole, we are joined on the show by, well, someone who's a fellow podcaster. He's been on the show before, but since then, his podcast has been relaunched. It's host unknown sole founder, Thom Langford. Hello, Thom.
Hello, hello.
Welcome back to the show, Thom.
Thank you very much. Thank you very much. I listened a couple of weeks ago and you said something about having guests on who are less security minded and, you know, don't have any expertise in security. And lo and behold, here I am.
Well, actually, Thom, that's not the reason
we invited you on. Oh, really? No, no. Graham, I'm going to hand over to you because you uncovered this little thing, didn't you?
Well, yes, I did. Yeah, do you see, since Thom has relaunched his host unknown podcast about, I don't know, probably a couple of months ago, I've been listening in each week. And there have been a fair few mentions of Carole and myself on the podcast. Although you seem to refer to it as Graham's podcast.
Oh, only once or twice.
Wow. And this was Javad who jumps to Carole's defence. Oh, Javad. It is Javad, yeah. But more than that, I hear you're really desperate for sponsors. And we...
Whoa, whoa, you're not donating one, are you, Graham?
Well...
Are you giving us one of your sponsors?
Can we pick? Well, specifically on your sponsor page, you say Smashing Security has enough sponsors, and so give your money to us instead.
Yeah.
I'm a master negotiator. I believe in win-win.
Yes. So if Smashing Security sponsors an episode, will you take that shit off your site and
start saying something nice instead? I will personally delete that before this recording is over if you're going to sponsor a show.
Graham, what do you reckon?
Right, right. We are going to record an ad for Smashing Security on the Host Unknown podcast.
Perfect. There you go, Thom.
Awesome.
Okay, let's get this show on the road.
All right.
Can I go now?
Hey, you sit right there and buckle in. What's coming up this week? First, let's thank this week's sponsors that sponsor Smashing Security. Meta Compliance and LastPass. Their support helps us give you this show for free. Now, stay tuned at the end of the show for a special feature interview with Robbie O'Brien of Meta Compliance. Not only does he share some great info on onboarding staff into better cyber awareness, but he has quite the dreamy voice. He does, let me tell you. Hello. Now, on today's show, Graham tells us what happened when a security firm suffers a security breach. Thom talks about the importance of brand reputation in our new world. And I'm looking into how we can make it harder for credit card hackers to dup us. All this and much more coming up on this episode of Smashing Security. Now, chums, chums, I want to talk to you about something which has sort of affected me personally in the time since we last recorded a podcast. I want you to picture this. I want you to imagine this scenario. Imagine that you personally suffered a security breach. Okay, you leaked data in some way. What would you do?
The one time I almost replied all in email that would have got me fired. I ripped the cable out of my computer. So this is before Wi-Fi. This is when I still had a manual leap over the desk and almost ripped the machine off the desk.
You thought you'd be faster than the electrons.
Well, do you know what? I think I made it. Yeah.
I was lucky. The advantage of having a 286 processor, I guess. Thom, what about you? If you suffered a security breach?
So there's two words spring to mind. honesty and transparency. And having done something similar myself, which affected 15,000 people in a company all getting notifications of my meeting requests for a day, I decided the best bet was to basically email everybody and say, sorry, this is what I did. Make sure you don't do it.
Okay, just adding to the spam.
Excellent.
Let's take it one stage further. Imagine you're a security firm. Oh, the pain that must be involved in that. If you suffered some kind of security breach, what would you do then? What's your recommendation? Thom, I guess it's still transparency and honesty.
Honesty. Absolutely.
Yeah, I think I would maintain that as well. Right. Come clean real quick.
Let's go even crazier. Imagine you are a popular and handsome award-winning security blogger. I'm not talking about Thom, who did win a security blogging award.
Damn, I thought you were going to talk about me.
Last week. No, I said handsome and popular. And imagine you heard that this security firm had a security breach. What would you do? If you're a blogger, you're going to write about it, right? It's interesting. Well, it's public knowledge, right? It's in the public domain. You'd think, well, this will be an interesting story to write about. Now, here's the final little leaf of the...
So who's the handsome guy again?
Apparently not me. Hypothetical one. Okay. Now, imagine you are the security firm that realises a security blogger has written about your security firm that had the security breach, what would you do? I hope you wouldn't send in the lawyers.
Okay, can I ask some questions? Did the security blogger say anything that was untrue?
I don't think he did.
Did the security blogger put the knife in and twist it ridiculously hard?
I think I was most...
Oh, you're the handsome guy? Oh, my God.
Sorry. I think I was balanced and reasonable in my blog post. Did you ask them for comment? I did ask them for comment, yes. I asked them if they would like to comment on the breach. So what happened was this. I wrote about this UK security vendor who I'll probably bleep out, actually. I'll probably redact them from the podcast, but the name is \[REDACTED\]. I wrote about them. You're just going to keep me busy with the bleeper, aren't you? Is that what's going to happen the entire episode? So how do you spell \[REDACTED\]? It's spelled K-E-E-P, right? And then edit.
And then beep, beep, beep.
OK, so I wrote about this incident. In fact, it wasn't me who originally discovered it. Bob Diachenko, who's an extraordinary security researcher, he's always uncovering massive databases that have been left exposed online, unprotected without even the simplest password. He came across a database containing more than 5 billion records. Which had actually been derived from past security breaches. So what happened is this security found...
Was he just looking at Troy Hunt's collection?
No, it wasn't Troy Hunt. His personal collection. Yeah, his personal email collection. It wasn't Troy Hunt's database. Let's not start another legal fight. He's much taller than all of us. No, no. So a similar kind of operation, I imagine. They were collecting data about past data breaches, but they then accidentally exposed it in some fashion, right? So I wrote about them, and I named the company. And what I noticed over time was that that company's name, which had been reported in other places on the internet, began to disappear mysteriously. Suddenly, no one was naming the company. And then I received an email from this company saying, oh, hello, can you please update your article to remove our name from it because it's inaccurate and it's bad for our image.
You know, Graham, this is not the only time this happened last week. With you. What else happened?
What have I done? Who else have you pissed off, Graham?
Remember the other email you received suggesting that you change your blog article to reflect a different company point of view than the one that was factual.
You're talking about Sophos' PR agency who wanted me to change my article about the Naked Security blog being decimated and their staff being made redundant.
Your old employer was going to sue you.
Well, no, no, no, no. Nothing like that. I received a very friendly email from Sophos' PR agency saying that Naked Security would continue to operate. And they were unable to answer any questions I might have regarding the editor and the writers being made redundant. Yes, so that was something else we had last week. But, you know, good luck to them, and let's hope that all gets resolved.
Just saying you had a busy week. That's all I'm saying.
I had a busy week. Anyway, so these guys wanted their name removed. And so I said to them, oh, can you tell me what's wrong about my article? Because I would love to fix it. I don't want to have inaccurate information up there. And they said, well, none of our customers were involved in the data breach. And so I said, well, I didn't say any of your customers were involved in the data breach. So I haven't got any words to fix about that. And they said, well, it wasn't really a breach because this was data which had already been breached. And I said, well, I think that's still a security breach because people can find it that didn't have access to it before.
Yeah, you've facilitated potentially, who knows if it actually happened or not, but potentially other people may have been able to access that data because you handled it carelessly in some fashion.
Fair point. This carried on for a couple of months, and I wasn't talking about this publicly, but they did say we are going to have to engage our lawyers to deal with this now. And I said, well, that's fine, but, you know, if you've got something to say, please let me know, and I will put it up on the thing, or if you've got any refutation or any statements you'd like to officially make, I will post it up on my article so that you can have your position. And they didn't want to do that. They didn't want to give me any statements whatsoever. But what they did do is they said, oh, and by the way, maybe you'd like to work with us on some business opportunities in future.
So what, bribe you?
Well, you might say that, Carole.
So say basically, hey, work with us, but we'll only think about doing that if you just do a little tweaky, tweak, tweak on that blog article. Thanks so much. So I said, thank you very much. That's interesting. But let's have that as an entirely separate conversation from the conversation about your blog post. Let's resolve that first before we discuss any other sort of business. Next thing I knew, I got a letter from their lawyers telling me to take down their name and redact it and saying it was bad for their company and all the rest of it. Now, I believe I haven't said anything inaccurate in that blog post, right? And I've given them a chance to have their say as well. So you backed down, but you couldn't do it without taking a dump. Well, people need to know. People need to know. I agree. Well, I agree with your stint. Don't get me wrong. Why should they win if you've done nothing wrong?
Well, what I did was I tweeted, and I said, following a legal threat from beep beep and I redacted the name I've removed their name from this article on my site and I said you know I apologize to readers but you know I can't afford to get into a legal fight now that did have an unforeseen consequence which I couldn't possibly have imagined would happen there were people on Twitter who were able to determine what the company's name was Wayback Machine so it appears.
Crawl yeah Wayback Machine i tweeted something similar about Streisand effect and Wayback yes there you go so.
There were quite a lot of people who sort of responded to it in fact apparently over a hundred thousand people saw the tweet and it was there were lots and lots of comments on it i haven't commented on my tweet or anyone else's comments regarding it or liked it.
Oh, that's very mature of you.
Well, I thought so too. Well, I just didn't want to...
You poked the bear enough already.
I didn't want to... I mean, you know, you don't want to put a bear trap out. I didn't want to pour any... The thing is, Carole, I'm not the only person who was possibly intimidated by this company to... Are you intimidated? There was an attempt at intimidation, I think, the legal threat. I do know that Javad Malik of the Host Unknown podcast, because he spoke about it on his latest episode...
Folded like a pack of cards.
He was contacted. He hadn't written about it.
No, that's the best part of it. You explain what happened, Thom. So, quick summary, Javad has been asked for a quote about this breach for an article by another writer. He supplied some quotes. He actually used the term breach because, let's face it, nowadays it's kind of a generic term, really, a bit of a catch-all for anything that's been lost or not secured or whatever. He mentioned that. And this particular company in question reached out to him and said, take your comments down, to which Javad said, I can't, it's not my article. I suggest you contact the owner of the article. And he also said, as a courtesy, I have contacted them to ask them to review it, but I can't do anything. And then they basically then came back threatening legal action, at which point he said, speak to my lawyers, and left it at that.
The difference is Javad has lawyers, whereas I don't.
Yeah, exactly. That's the joy of being employed by a company.
The only legal thing I can even think of it, and I'm no lawyer, is just the breach. What does a breach mean? How is it defined by the Computer Misuse Act? And how was it used?
There has been a breach of security. A breach of trust. Oh, careful, Carole, what you say. Who knows what you might get in the post.
It's like saying well it's not a breach because it's already been lost is ridiculous it's like sending somebody an email to get it to the top of their inbox what it is is putting it out there again in another easy to find format on the plain regular internet so that even more people can get access.
To what they should have done instead was as soon as they were aware of it they should have contacted the appropriate authorities contacted anyone affected and put it up on their website that this happened. This is how they're handling it. And if they have any questions, please see this FAQ. Done.
So it's only after one week of Twitter outrage and people sort of going after them with pitchforks. And to be honest, some people I feel have been, have gone a little bit too far on Twitter.
No. Really? That's not like Twitter at all. On Twitter? Holy God, I didn't realize this was this big.
So the security firm, keep that loud, beepity beep, they have now, now, today, hot off the press, just before we recorded this podcast, they have now published a statement about the exposure on their website where they try and explain what happened and try and excuse what happened.
Let me guess, they don't use the word breach anywhere.
I'm not going to get into the nitty gritty of the accuracy of their statement. Are you named in there? No, I'm not.
What, a special thanks to Graham. But the thing is, here's the thing about the security industry. It was an Elasticsearch database, I believe, which ships and installs with everything security-wise switched off, as I understand it. And we get it. As security professionals, we get it. You know, switching security on is difficult because it limits functionality. It can slow things down in some cases. You know, it's difficult. But if you are a security company, you need to have your shit together. You've got to have these processes in place that make sure that anything that faces the internet or anything that contains personal or confidential information needs to go through a hardening script of some kind, be it automatic or manual. And if it doesn't work for some reason and you get found out, then tell us why it didn't work and what you should have done so that we can all learn from it.
So I think your advice is absolutely right, Thom Carole. I think transparency, honesty, prompt response to these kind of incidents means that, you know, when something bad happens, it doesn't have to be as big a deal as you can make it by responding badly. Deep, Graham. Yeah, well, fuck off deep. What's their name? Fuck off keeping their lives and their lawyers. Yeah. I'll keep an eye on the letterbox.
That's right. And your bank account.
Thom, what have you got for us this week?
What have I got? So there was a lovely tweet that I saw the other day about brand reputation and how important it is to control your brand. And we know this because, you know, many of us in security roles have experienced this when other companies register domain names that are either very close to your company name or they are the same, but with a different, you know, .com or .co.uk at the end and start impersonating you. And this is a big deal. And as a result, there's a whole sort of almost a sub industry of, you know, brand management. And when you register a domain, you can automatically get similar domain names registered. There are services that search out to see if there are domain names that are registered with, you know, Cyrillic alphabet characters, but still looking like your domain, etc.
I think we've actually had this ourselves. I think we had a listener who bought the domain smashinsecuritywithoutag.com to redirect to us, which was very generous of them. Oh, that was very decent. We had very decent listeners.
That's why we love them. We should have done that and redirected it to host online. Okay. See, he just screwed up again, Thom. Yeah. Well, if you'd listen to the podcast, you'd know that that's regularly what we do. But talking about someone else who screwed up is the US, believe it or not. So the US a couple of years ago, or Mr. Trump, announced Space Force, the fifth wing of the US military. You can
totally see that he came up with that name too, right? You can totally tell. Oh, my God, yeah.
He's just sitting in the back going, oh, I want to get the laser guns. But bottom line is he watched Moonraker and decided that's for him. So they've yet to get involved in any kind of serious operations. They've yet to launch anything. They've kind of just been bubbling under. They're probably still deciding what sort of camouflage they should have on their uniforms.
I think they did actually design a logo, didn't they? They did, yes. It looked very much like the Star Trek Enterprise logo, the Federation of Planets or whatever they're called. Yeah, exactly. Or Blake 7, yeah.
Blake 7, now that would have been good.
So what's going on with Space Force?
So also, you may have noticed recently on Netflix, there's a new series called Space Force, which is a little spoof on that, and it stars Steve Carell and John Malkovich. Very funny. Oh, cool. Very funny. I've just watched the first season. It's very good, very lighthearted, lots of fun. The problem is Netflix have trademarked Space Force. Well, of course they did.
But let me guess, let me guess, the government didn't.
Didn't, that's right. That's right. So maybe we're going to see rockets launched with Netflix on the side of it in order to pay them back for use of their trademark. But it just strikes me that it doesn't matter how big your organisation is or how well-funded it is, and let's face it, the US government has got to be kind of up there, size, complexity and amount of cash. They could just change the name, though, right? Why wouldn't they just change it to something like Space Fork?
Or Space Fars. Space Fars, exactly.
Yeah, which is roughly the zone around Trump's head. But yeah, I just find it amazing that such basics like this, it's a bit like when you hear that somebody forgot to renew their certificates for their domains and stuff like that. I find it just stunning that such basic stuff is not being done. You know, I would imagine US Army is probably trademarked or copyrighted or something.
So when you brought up this topic, I, of course, went and searched for Space Force, right? Oh, yeah. Found Netflix. Well, yeah, Netflix came in first. And then there's a few IMDB sites, stuff like that. And then there's a review from The Verge saying the title is Astonishingly Bad Show. Really? Yes. Which I'm,
because I'm looking at... Are they talking about the president?
Carole, what's your story for us this week?
Before we start, can I just ask credit cards or do you guys have a strong relationship with them? Do you have many or just one?
I have a debit card. I don't tend to use a credit card unless it's for very painful purchases really.
Even when you shop online.
Well that's what I'm saying. When it's a painful purchase, in fact I have someone else in my household who does most of the shopping. So I think they may have a credit card, but I don't. Damn me, you should use a credit card when you shop online. The what's-its. Yes, get the protection. No, not for that. No, the protection, I mean. The protection.
The toilet rolls. No, it's because the creditors and you share responsibilities. So if you buy something stupid or you don't get it. Yes, protection. I'm trying to explain it to the listeners too, Graham. It's a radio show, right? So it's not just about your knowledge. Sometimes you have to pretend you don't know stuff to make it fun. So what would be the benefit of me shopping with a credit card?
Well, very good question, Graham.
It's poetry in the making.
The reason is that if you buy with a debit card, you are 100% responsible for that loss if you don't get the item you've purchased. But with a creditor, you share responsibility. And you can sometimes claw money back from it from your creditor if you can prove it wasn't your fault. So always purchase a credit card.
Very cool. Very good advice.
Now listen, straight up, credit cards, not a very funny conversation topic to cover. Seriously, I was thinking...
I'm sure you can sort that out.
Well, you know, I decided I would, and this is how I've decided to do it. I have peppered my story with a few jokes, which I got off the internet by looking for credit card jokes. And that is how we're going to keep this light.
Will you signpost them in some fashion?
Yeah, yeah, we're going to start with a joke. So what do Trump and maxed out credit cards have in common? Nobody likes them, they both deny all charges! Oh hey, okay, very good bit of science. Now, so credit cards are powerful tools, right? People are setting up new online accounts, registering their credit card details with them willy-nilly because guess what, they can't go to the bank and they can't go to the stores to buy the things that they require. People, even if you could pay in cash, people don't really want to receive cash at the moment, do they? Because it's... dirty. Filthy lucre. Now I don't tend to use credit cards either, but I'm kind of glad that I've got one that's all paid up and ready if a bigger emergency hits me directly. But others who are in the eye of the storm, you know, may be jobless or they're out protesting unbelievable injustices or they're staving off the bills with credit card payments. Joke time, right?
Oh yeah, good, you see?
So why did the dad put the credit card statement on his feet?
I don't know.
Because it said New Balance on it. It's a shoe company.
Oh, okay. Thank you, such a fucking dad. Such a dad, such a dad.
Did you know that, Thom?
I did, but I didn't get the joke though. Ah, maybe it's my telling. I'm not very good, I'll work on this. I'll work on it.
Oh really?
And these have become so pervasive that some executives at a community bank thought they'd been hacked before learning that it was just cardholders were falling victim to these scams. That's how bad the numbers were.
Oh, so they saw so many weird transactions happening that they thought there must be someone inside the infrastructure. Oh crumbs.
But actually it was just the customers. It was just the customers falling for stuff. Oh my God.
Could you give us another joke? Would that be all right?
Yeah, I've already got lined up.
Okay, well good.
Plenty more where they came from, yeah, because the last one about New Balance didn't really work for me.
So you're such a dad.
I'm really good at managing my credit card. My bank keeps sending me letters saying my account is outstanding.
Yeah, right.
So types of scams we're seeing, one is a kind of service scam. So a typical one is they're talking about Netflix. So you might get an SMS or an email that says, hey, free Netflix for a month or three months or six months. Now, the reason this is hard for people to spot is because Netflix and other service video companies are offering incentives to get more users. So it's our job to be able to tell the difference between a real one and a bogus one. Now, the other one is government info or stimulus checks. So in the States, there's loads of people that have filed for legitimate stimulus checks coming in from the government. So what if you get a phone call or an email, someone purporting to be a bank or government official, saying we need to get some more information to make sure you get your check, or we just want to double check your postal address, we get the check in the mail for you. Ironically, I saw on Twitter that people are mistaking that there's stimulus checks for junk mail or a scam because I don't know if you've seen what it looks like and it also has done.
It's been signed by a scam artist.
Exactly. I don't know if you've seen the signature.
But he doesn't look like I'd rely on him. Oh so because the check comes with Donald Trump's signature people think this must be a hoax. Oh my goodness. I wonder if Stormy Daniels has got a check from Donald Trump. Many checks.
I think, okay then. Of course we don't even have to go into it with all the COVID stuff and we know why that's happening. Well, you were talking about that last week, weren't you, about the track and trace websites? There's also the bank and credit card stuff. This makes it hard again because banks are offering services. I am getting legitimate text messages from my bank saying, hey, we're going to freeze your interest that you owe us during this period. Get a $500 stimulus check from your bank. Just tap here. But.
Here's the thing. You say, you know, is that legitimate? Well, go to their website and find out. Do you know what I mean? You know, click here, please.
I guess that's the problem, though, isn't it? If the communication includes a link, many people will use the link in the communication or told to them down the phone rather than finding out what the real link is.
Yeah, of course.
Yeah, and that's so important, that advice. So maybe you should say that again, Graham, just to make sure everyone hears it. It's super important.
So you have to be careful. Don't click on the link which is given to you in the communication, in the email or in the text message or told to you down the phone. Instead, work out what the real link is and go to it directly on your computer.
Exactly. One guy on Twitter was saying that he keeps getting calls and the way they start the call off is, credit card services, how are you doing? And then they offer to lower your credit card interest.
Is it Joey from Friends? How are you doing? Also be careful of insurance scams. So, of course, many of us had plans for the summer, like perhaps we were renting a vacation home or going on a flight or doing something with the family. And some of us have had trouble getting money back from those things. Emails saying, here's your Airbnb cancellation. We just need your banking details to refund your card could also work pretty well. I think we do.
Graham, I don't know if you're going to get this one.
I've done so well so far. Let's.
See how you do. Let's see how you do. A tangent applied for a credit card but was denied. He couldn't find anyone willing to co-sign.
Oh yeah, okay, that is quite an intellectual joke. A little trick for you there, Graham. I like that one, okay, I understand that.
Okay, so advice time now. Before I get into advice, the reason I wanted to bring this up today is because you guys are both smart and you will have better advice than the advice that is given on the official FBI credit card fraud site.
Oh, okay. Oh, dear. Right.
So there's things like before using the site, check out the security and encryption software it.
Uses. Let's see if it has a padlock on the website.
Don't judge a person or company by their website. Flashy websites can be set up quickly. And then they say somewhere else, make sure you buy from a reputable source.
The Host Unknown podcast website looks pretty flashy, I have to say, but I wouldn't necessarily. I'm not sure it's entirely reputable.
Oh, it's certainly not reputable, but it is genuine.
So, okay, so I'm not saying any of the information here is wrong. I think it's all very difficult to follow.
It's a wall of text. You can't give this volume of advice and expect people to follow it. It's got to be a far simpler message that people can emotionally attach to.
Yeah. You know, I want to hear Carole's tips. Let's hear them.
I think the best one is sign up for alerts. So every time your bank number or credit card is used for a purchase, you get a secondary notification that tells you, hey, your card has just been used. Great idea, right? And that way, at least, it doesn't mean it stops it from happening in the first place, but means you are on to it super quickly. Limit the number of websites you save your credit card information. You don't have to save everything. I know it makes everything a little bit faster, but actually, it's much safer not to save it with a bunch of different companies out there. And you can also use things like either PayPal or Apple Pay or Google Pay. These might be a smarter way to be able to manage your money because then you have a kind of an account you can manage.
Also use LastPass to store a credit card and have it automatically fill in the site.
Very good point. Yes, you can. So I like this idea of using Apple Pay or PayPal or Google Pay and things like that, particularly on sites which you aren't familiar with, you know, for an additional level of protection. That's a great idea.
I do. So you get either a virtual credit card, which is you've got your regular card, but then your app will generate a virtual card. So you don't actually get a physical card and you can use that for all your purchases, say, at Amazon or John Lewis or wherever. You know where I've heard those are excellent to use? If you're signing up for a one month trial or membership of something and you know they're not going to let you out easily. And this way you follow the rules. And at the end, it just goes poof and they can't, you know, hold you for money. The folks at Meta Compliance are fabulous, not only because they're sponsoring our podcast this week, but also because they're offering listeners a free Cybersecurity Awareness for Dummies book.
Are you having trouble remembering your plethora of passwords? Maybe it's time you look to get a password manager.
And welcome back. Can you join us at our favourite part of the show? The part of the show that we like to call Pick Of The Week.
Pick Of The Week. Pick Of The Week. Pick Of The Week. Pick Of The Week
is the part of the show where everyone chooses something they like. It could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app, whatever they wish. It doesn't have to be security-related necessarily.
Oh, you said that weird. Better not be, Mr. Cluley.
Yeah, well, it isn't security-related. It is shoelace related because—
Oh, you've done this before.
No I haven't, have I? Okay, go ahead.
After 182 episodes he can't remember. Crack on, crack on. Now I'm frightened. A chap called Iain Fieggen runs a website called Iain's Shoelace Site. He is the inventor of the Iain Knot which he claims is the world's fastest way of tying your shoelaces. Well, shoes are big business. Billion dollar industry that company New Balance is really big.
Anyway I will put in a link in the show notes.
I think he has been your pick of the week in previous week. I would call on to our more avid listeners to see if they remember which episode that came out of because I don't remember.
Are you kidding me? Are you serious? You think I've done this before?
Yep, I think you have a little pick of the week document bunch of links and maybe perhaps you haven't been doing very good hygiene.
Normally I clear out my old entries.
This is what happens when we get to episode one. Well look, I'm sure—
Our listeners will give me feedback.
It's worth it. It's worth it.
It certainly is worth going to. I'm a bit worried now.
Don't be worried. It's fine. You're old. You're forgetful. Everyone's understandable.
Okay, Thom, what's your pick of the week?
So it was going to be an app called Magnet, which is totally non-security related because I know how much Carole desires non-security pick of the weeks.
Just a touch. Just a little bit. Yeah. It's the one thing that stands out every week that I listen. But, yeah, this app for Magnet for the Mac, very simple app. It just sits in your taskbar. And what it does is it allows you to very quickly and easily resize your windows.
Oh, for goodness sake. I actually use Magnet. I have to say, I have to endorse this product as well. It's a great little product.
Okay, where's their privacy agreement? Do you know what? Their privacy agreement says, we do not collect any information at all, period.
Okay, I was looking for it and I couldn't find it on their webpage and I was typing in slash agreement slash term slash privacy and nothing came up and then—
I see a terrific we capture nothing and that in itself is a good lesson in infosec if you don't need it don't capture it you don't have to worry about it.
Thom, you have done your homework.
I have, I have especially on the Host Unknown podcast which I think everybody should listen to.
Graham hand over to roll talk talk what have you got.
My pick of the week this week is a TV series from BBC2, or at least that's where we saw it. It's Alex Garland's. He's the guy who made Ex Machina or Ex Machina. Yeah. Oh, yes.
Did you guys see that? This is his first time dipping his toes into the small screen waters and it's called Devs. And I say, Alex, baby, dive in. He rocked it.
Oh my God, yes did you watch it I've seen the first episode yes.
It's got your man from Parks and Recreation Nick Offerman's in it. Yeah yeah yeah he plays the main kind of Elon Musk god of the whole Devs lab but it's kind of technically, you know, it's sci-fi, but there's some technically sound stuff going on. A bit like Mr. Robot, you know, was obviously in our universe.
And what do they do in this Devs thing?
Because it's actually a physically separate lab and it's a big deal getting into it. And it's kind of crazy. They kind of tease the audience. They tease you, drip feeding you a little bit of information of what's going on in there. Plus, they have the coolest statue ever in the kind of campus, which I just think we should litter the entire planet with them as a reminder of what kind of future we want to build. So I say watch it. I watched the entire thing in two nights. Loved it. Loved it. Loved it. Geeky, dark, beautiful, smart, well acted.
How many episodes are there, Carole?
I have no idea. I gobbled them up. I don't know. Six, maybe. Six.
Carole still thinks it's Saturday. Isn't it? Yeah, I saw the first episode of that. I was really impressed. but then I had to finish something else before I started, you know, it's worth it. It's worth it. Graham, you'll love it. So will Mrs. Cluley.
Okay. All right. Well, fantastic. Well, on that note, I think it's just about time to wrap it up. Thom, I'm sure lots of our listeners would love to follow you online. What's the best way for folks to do that?
So I'm on Twitter at Thom Langford. That's Thom with an H because Twitter made me have an H. And also, So my website, TomLangford.com and HostUnknown.tv and podcast.hostunknown.tv.
Very cool. And you can follow us on Twitter at Smash Insecurity. No G. Twitter wouldn't allow us to have a G. And also join us on our Smashing Security subreddit as well. And don't forget, if you want to make sure never to miss another episode, subscribe in your favourite podcast app, such as Apple Podcasts, Spotify or Pocket Casts. And why not leave us a nice review as well? Always love reading those.
Huge thank you for listening and supporting us. It means everything. Also, thank you to our sponsors, Metacompliance and LastPass. Their support helps us give you this show for free. And don't forget, stay tuned after the show for our special interview with Robbie O'Brien of Metacompliance. Check out smashingsecurity.com for past episodes, sponsorship details and information on how to get in touch with us.
Until next time, cheerio. Bye bye. Later, skaters. Bye bye.
So we have a very special guest, a new guest, someone who hasn't been on the show before. I'd like everyone to meet Robbie O'Brien from Metacompliance. Robbie, thank you so much for coming on.
That is why we're here today. You have helped write, or did you write the entirety of it?
I wrote the entirety of it, and a colleague, thankfully, edited out the more crazy things that I was trying to put into the book.
So this is the author of the Cybersecurity for Dummies book that has launched from Metacompliance, and it's totally focused on how a company can help get employees on board to be safer and help protect the company and themselves. Is that fair?
That's fair. And I think we have condensed all the learnings and low-hanging fruit and approaches that we've seen organizations use to move this along and really brought it into an easy-to-use playbook.
Now, it is not a tiny playbook. It's 50 pages. And is this free for anyone to download?
It's available from the Metacompliance website. And if you reach out to us, we can also send you a physical copy, which interestingly is an excellent way to get those Luddites within your organization to move forward where they have a physical book in front of them and they'll actually read that more than go and read a PDF.
Obviously, we're going to encourage everyone to go download it because I've taken a look at it. I think it's an impressive amount of work that went into that. There's some really, really good information. Maybe we can start with the idea of what motivates a hacker.
I think that there are as many different types of hackers as there are people. And I think that every time the human race has come up with a brand new way of commerce, there has always been piracy. You know, when the Americas were opened and we were transferring goods between the old world and the new world, you had this blossoming of piracy, Pirates of the Caribbean type thing. And hacking is no different than that. It's really a way of people gaining advantage, mainly for money. In my experience, that is the great motivator. There are certainly other issues, political, national players. And so you find that it's a very, very complex issue. Then we have businesses who are going about their mission, involved in what they've been doing typically for a very long time. And we have this brand new backdrop and they find themselves really at a disadvantage. And you know, the hacker spends months possibly thinking about the organization. The organization wouldn't necessarily be thinking months on awareness or security. The demands of the day, the crises of the day typically distracts them from approaching this problem in a more systemized fashion.
Oh, I know. It's true, isn't it? I remember when I used to work in the corporate land, even working in cybersecurity, in a cybersecurity company, you could still see plans always fall off for an immediate reactionary job that everyone had to be all hands on deck. So, do you find that people have good intentions with awareness, but sometimes just don't do their homework or don't actually follow through?
Cybersecurity culture change is a change management project. And I don't think there's any organization out there that hasn't seen change management projects really crash and burn. I think everyone's history is littered with the failures of those things. And the problem is that you really require two things. Number one, you require the leadership team to be 100% behind it and give it the resources that it needs. And the second thing is that the organization is braced for the long term because change takes time. And in my opinion, to move the needle substantively for cybersecurity takes at least 18 months, possibly two years, because you have some real hardened attitudes to change. And the minute that people see a wavering of the commitment from senior management, the whole thing falls apart like a game of cards.
I love that you say both those things. I love that you say that it takes 18 months because that's kind of my experience too. And I find a lot of companies kind of say, oh, you can do this overnight. It's not an overnight job trying to change a culture within an organization. And two, you're absolutely right. If you don't have absolute buy-in from the senior management team, and if they are kind of cutting corners, that's not a good thing, right?
It's not a good thing. And I also think that, unfortunately, so up until now, cybersecurity doesn't make you profit. It doesn't get you revenues. And therefore, it was seen as an IT thing. Now, interestingly, that's changing massively. And I've seen a change really from the introduction of GDPR, where within the supplier contracts that every company uses as an engagement mechanism, you now have a couple of things that have come to the fore. Number one, you have cybersecurity insurance. 10 years ago, that was unheard of. But now, what is the level of liability that is covered by your cybersecurity insurance. The second thing is, where does the liability sit for GDPR? Who is responsible for a data protection failure and who takes a liability? And the third thing then is, you get a risk assessment from your potential customer and you have to fill in that risk assessment. Now, before GDPR, that was largely a box ticking exercise. But now the risk assessment will be called upon to defend the decision to go with that vendor, that vendor selection, as part of an overall privacy lifecycle. And also the lawyers are heavily focused on it. So really having high levels of cyber hygiene, high levels of being able to demonstrate your cyber credentials now becomes a competitive advantage. Having ISO 27001 now becomes a competitive advantage. And I think going forward, that is going to become more and more a feature of how people look at cybersecurity, the people that they deal with. But more importantly, I think will justify the spend that's needed in these type of projects.
I think that's one of the big problems is resources, especially now with, you know, the COVID-19 happening. Lots of IT teams have been culled or have had to deal with resource issues on that front. Plus, they're having to manage a whole new workforce working from home and they want to keep it safe. So, you know, obviously you wrote this before all this happened, but did you touch upon remote working and do you have any views on that?
In the industry, we have seen the incidence of phishing and cyber activity just go through the roof. And the reason for that is that people involved in cyber criminal activity they love change. They love different things happening to us as human beings so they can exploit the moves between, you know, working in an office, working from home, people not being within their social circle and things like that. The issue is vigilance. The issue is then having messaging or having a subject on a monthly basis that you address to your audience. And so, for example, a lot of our clients who take this really seriously immediately switch to secure remote working, immediately began sending out training based on, you know, the dangers of working from home, the increased levels of people trying to cajole you to do things that you wouldn't normally do in the office, and they increased their vigilance. Those companies also continued with their simulated phishing attacks. And then some people just killed them off altogether saying, oh, you know, our staff are dealing with working from home. They're having a bad time and they stopped. Some people stopped simulated phishing. And my view there was, well, in actual fact, that's what the hacking community is betting on you doing, betting on your change and the fact that everybody is disarranged. And so I think the people that did continue with the phishing attacks actually increased the vigilance in this new environment, which is likely to continue in some form or fashion well beyond COVID.
Say, I'm going to try and put a scenario to you just to drive the point home to everyone how important this is, right? So let's say I'm an IT guy, and I really want to get through to my CEO, right? They're just not taking this seriously. They've cut my budget, they've cut my resources, and I really need them to see the importance of cybersecurity. Do you think a better approach is to go in with a bunch of stats to explain how dangerous it is out there? Or do I want to talk more about how the company can be, can grow and, you know, make more money and be safer, more secure, lower risk. I mean, I really feel for people in that situation. Me too. Yeah. There has to be some good come out of this pandemic. And I think there is for cybersecurity because our concept as a society of what's possible has expanded now. If someone had told me before Christmas that my entire organization would be working from home, all these controls would have been put into place, I wouldn't have believed them. But now I'm prepared to believe much more in terms of change and the world that we lived in. So getting someone to believe that we could have a cyber event that could cripple the organization, I think is easier to believe. So I think that envelope expanding will help us. Totally. And you know what else, actually, this may be an excellent opportunity for IT people to actually approach their CEOs about investment in this area. Because of the change in environment, there is inherently a little bit more risk there until they can lock down both security and cyber awareness for home workers. So this might be the time to kind of say, look, the environment's changed. We need to be on top of it to make sure we're safe. I don't know. What do you think about that? Look, people have gone home and we implemented one of the biggest changes in organizational working in centuries. And we did it in weeks where normally that would take months or maybe years for organization to put it into place and you would train everybody and so on and so forth. But we flicked the switch and we got it done. The other thing is the digital assets that the organization rely upon now exist within those homes, now exist within those firewalls, within those homes and rely on people within and indeed rely on their families, not just the people that work for you, to be aware of the dangers and aware that certain things could happen. And the only way to do that is to engage with your staff population and give them the information and give them the resources to actually make the change. Because thinking it'll happen by osmosis is naive. It just won't. And what has happened, whilst there are many benefits from homeworking from a security perspective, our perimeter has just morphed into something that is unrecognizable now. You know, the more I'm thinking about this, I think a lot of different people need to read this book. At first, I was thinking this is really, really good for IT staff to kind of understand what they're facing and how they can kind of get their hands around all the different components. But maybe, maybe, you know, maybe I was blindsided, maybe C-levels need to read this too, just to understand all the different components and the complexities that need to be understood so that they can be more sensitive when they're budgeting and dealing with IT. Carole, I mean, you've hit the nail on the head. I mean, when I was writing this book, I sort of had an image in my mind of, you know, a CISO at a board meeting, you know, with a number of these books and basically handing them, physically handing them. So, you know, I have the power of a gift. Here's a gift. And it's a wily book that we've all seen, The Dummies Guide. And even if someone dips in and out of it, you've already made an impact. Because I think if you can get the C-level, the executive team on your side, you can change so much. Because the problem I found with cybersecurity is that it isn't user-friendly. It involves implementing controls, and people hate controls, and they hate policies, and they hate e-learning. So it's not a popular job, but once you get the C-level involved, you get a tone from the top. And people never focus on that. Well, what does our organization stand for? Do we have zero tolerance on these things or are we laissez-faire? Where do we fit? And once the people in charge say, this is where we stand, then your initiatives are not diluted by middle management. You know, someone who goes, look, don't bother with that e-learning. Keep doing your jobs. Get around to it whenever you, and suddenly your awareness campaign has just died because you have a manager somewhere who is just not supportive. But if the CEO is supporting the actual initiative, you typically get people to buy into it. Well, with this book, you have given a lot of IT people and indeed companies a helping hand. Robbie O'Brien from Metacompliance, thank you so much. I thought it went very well. Listeners, you can get your free copy of Meta Compliance's Cyber Awareness for Dummies book by going to smashingsecurity.com slash cyber aware. That's smashingsecurity.com forward slash cyber aware. See you next week.



