
Security researchers say that they have uncovered a new way to serve up malware to computer users, by exploiting the way in which videos are embedded inside Microsoft Office documents.
Researchers at Israeli security outfit Cymulate explain that the attack takes advantage of how online videos (like those on YouTube) can be embedded inside Microsoft Office documents.
In a proof-of-concept demonstration, the researchers first embedded an online video inside a Word document.
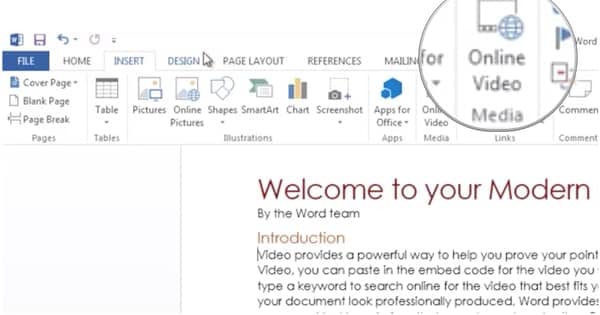
This is done by clicking Insert > Online Video inside Microsoft Word…
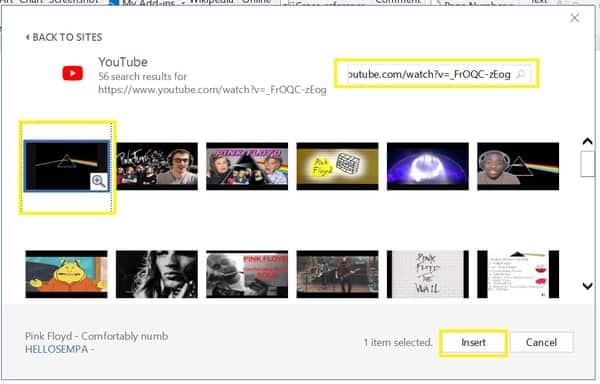
…and then providing a link to an online video (one hosted on YouTube in this example.)
The Word document is then saved as a .docx file and unpacked – revealing its innards, which include a file called document.xml. At this point someone maliciously-minded can edit the embedded YouTube iFrame code in the document.xml file to replace it with malicious HTML and Javascript code.
The now tampered-with Word document can now be repackaged, and sent to its intended victim.
And, unlike a Microsoft Office document which contains an embedded macro (and asks the user for permission before it executes, warning of the potential dangers), a recipient of a Word document containing an embedded “video” will see no such warnings.
The researchers speculate that the attack could be used to phish credentials from unsuspecting users, or to install fake software updates.
However, don’t hold your breath waiting for Microsoft to release a patch to fix the problem.
The researchers contacted Microsoft three months ago with their findings, only to be told that the software giant would not recognise the issue as a vulnerability.
As Jeff Jones, a senior director at Microsoft, told Threatpost, Microsoft Office doesn’t believe it needs to make any changes to its software:
“The product is properly interpreting HTML as designed – working in the same manner as similar products.”
Now, you could ask why on earth Microsoft ever thought in the first place that allowing users to embed active content within a Word document was a good idea from the security point of view… but I fear that particular boat sailed some time ago.
In Microsoft’s opinion this is “someone else’s problem.” And as it’s unlikely anyone else is going to step forward to claim responsibility, that means it’s your problem.
It should be stressed that no evidence is being offered by Cymulate that the technique has been used by malicious hackers to compromise systems, and this is very much a proof-of-concept attack.
But now that it has been publicised, as has Microsoft’s shirking of responsibility and admission that it has no plans to mitigate the threat, any organisation which believes it may be under threat may be wise to consider blocking documents containing embedded videos, and ensuring that layered anti-malware defences are in place to intercept any potential payloads.


Oh, Microsoft, Microsoft, Microsoft, after previous vulnerabilities in Microsoft Office with macros, you still haven't learned to make sure the embedded comment is only from safe sources…
Their response is still silly! "Oh, sure, the potentially-dangerous embedded content is working as intended, no one will run Davi dangerous screener scripts and websites, it's just harmless HTML…"
'Safe sources'? Humans aren't safe. But then again executable code in images… No surprise, this
But as for their reply? That's nothing! I still remember well when cDc released BO how pathetic MS was with that. They still have it archived, the cDc. It's both hilarious and also scary. But this is one of the reasons you have 0days – refusing to accept vulnerabilities even when they're pointed out to you (if they are in the first place)!
https://www.cultdeadcow.com/tools/bo_msrebuttal.html
Microsoft's standards are crumbling.
A little curiosity for you guys. I have kept an old XP SP3 system updated using the XP Embedded updates downloaded from the Microsoft Updates Catalog. The system runs on old hardware, an AMD Athlon XP 3000+ which does not support SSE2 instructions. Up to and including August 2018 the security updates ran as they should on this old processor. However, in September the updates installed successfully but on restarting I saw messages about illegal instructions. I knew straightaway what the problem was and located the troublesome update (which corrected a GDI vulnerability) to uninstall it and all was well. This month more updates were similarly troublesome and I ended up with only the Internet Explorer 8 update being installed.
My point is that Microsoft has gone back on a rule that it only issued software for Windows XP and XP Embedded which would run on processors supporting SSE instructions or later. Those who still run POSReady systems on old (pre-SSE2) hardware will be in a bind as support does not end until April 2019. Clearly standards are breaking down in Microsoft so that different teams seem now to be using whatever compilers suit their mood. The GDI and .NET teams have probably changed their compilers whereas the IE teams seemingly have not. A retrograde change of culture at Microsoft seems to be in progress.
Windows 10 is flaky. It loses data. Looks like Linux for me from now on.