
A researcher has published a proof-of-concept (POC) confirming that the Nintendo Switch games console is vulnerable to a WebKit exploit.
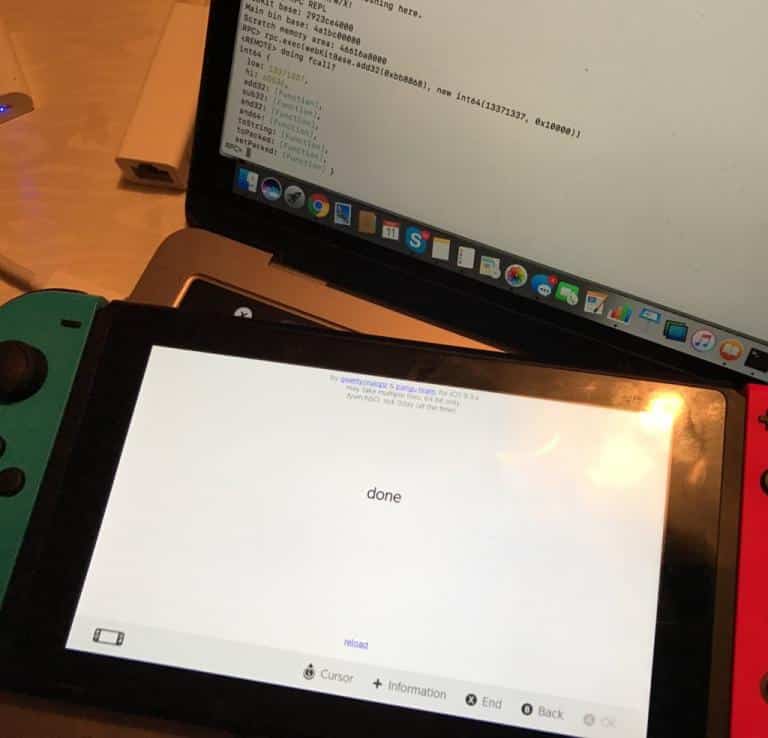
On 11 March, a hacker by the name of “qwertyoruiop” posted a screenshot of what appeared to be a WebKit exploit running on the Nintendo Switch gaming console.
WebKit is a piece of software that helps display web pages in web browsers like Apple’s Safari. This fact isn’t alien to qwertyoruiop. After all, they’ve earned quite a reputation for publishing jailbreaks of multiple iOS versions. They even developed a remote code execution proof-of-concept for iOS 9.x they named “jailbreakMe“.
It’s extremely convenient they did.
You see, Nintendo Switch shipped out with the same WebKit version for which qwertyoruiop developed their jailbreakMe exploit. All they needed to do was remove iOS-specific code from jailbreakMe, a POC which exploits an arbitrary code execution bug in WebKits found in Apple iOS before 9.3.5.
Qwertyoruiop then used the modified code to force Nintendo Switch’s browser, which isn’t pre-programmed to normally access the web, into accessing files hosted on a local server. These files could allow the attackers to play pirated games or create homebrew projects.
At the time of qwertyoruiop’s release, some people in the game hacking community doubted whether the exploit was real. It was just a screenshot, after all.
But that all changed with an update released by developer LiveOverflow on Wololo:
“What’s been released is just a proof of concept: it confirms that the browser is vulnerable to the attack. To the end user, this brings pretty much nothing at this point. For hackers, however, this is an entry point to start analyzing the internals of the Nintendo Switch OS: it is now possible to start looking at the RAM and understand a bit more about the device’s firmware. Typically this kind of exploit then leads to the possibility to dump a few libraries, which is then followed by a hunt for a privilege escalation vulnerability (basically, a kernel exploit), which would give full access to the device.”
You can view a video demonstration of LiveOverflow’s POC below. You can also view their POC files on GitHub.
Fortunately, Apple patched the WebKit vulnerability that’s active in Nintendo Switch’s browser back in August 2016. Nintendo just needs to send out an update to fix the issue.
That should be forthcoming… as will likely be a full Nintendo Switch jailbreak.

