
A security hole allows attackers to crash Android phones and force them to soft-reboot.
Discovered by Nightwatch Cybersecurity software engineer Yakov Shafranovich, the bug hinges on what are known as Proxy Auto Config (PAC) files, or text files which may constitute part of a network setting configuration that allows web browsers to access the internet.
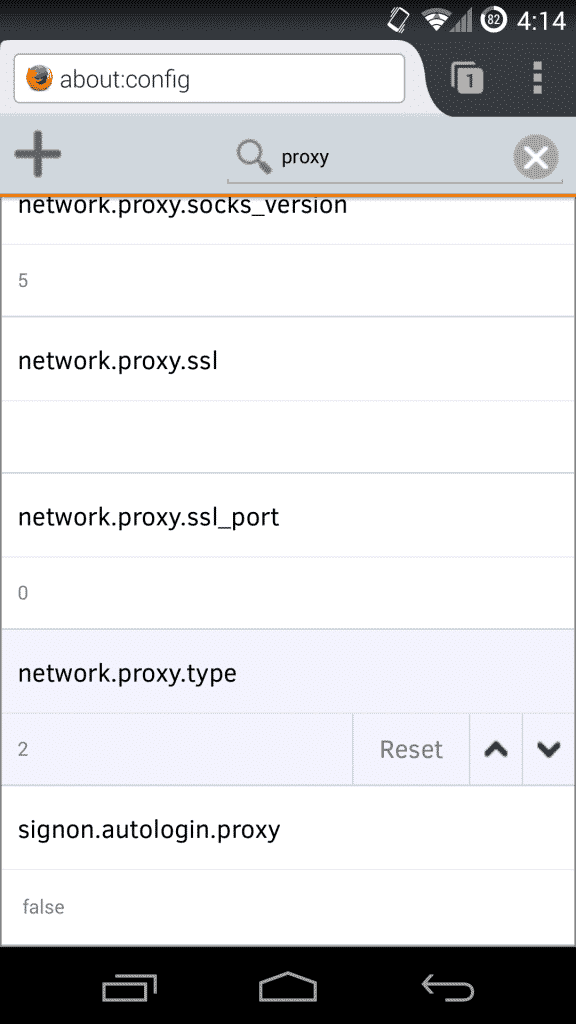
The files generally rely on a JavaScript function to look up what type of proxy server should be used for each type of request. On Android phones, users can set a PAC URL that point to a particular file.
Great! There’s just one problem.
The JavaScript code in most Android PAC files don’t bother check to see if the files are too large for a phone’s memory. As a result, an attacker could conduct a man-in-the-middle attack to intercept a PAC file served without SSL, replace it with a larger PAC file, and thereby force the phone to crash.
Shafranovich explains in a vulnerability advisory:
“The vulnerability is that the Java code does not check how large the data file actually is. If a file is served that is larger than the memory available on the device, this results in all memory being exhausted and the phone halting and then soft rebooting. The soft reboot was sufficient to recover from the crash and no data was lost.”
The software engineer went on to say that an attacker could potentially leverage the vulnerability to achieve remote code execution. But in the absence of further research, the jury’s still out on that one.
Shafranovich first filed a report on the issue with Google on 11 July. After some back and forth, Google released a patch for the issue on 7 November. All users should therefore implement the fix as soon as possible.

“We encourage all customers to accept these updates to their devices.”
If only it were that easy.
The fact of the matter is that many users don’t have the ability to update their phones. That’s because Google is not responsible for directly pushing out security fixes to Android users. It’s in the hands of mobile carriers and manufacturers instead, and some abide by different time frames to do so.
Convenient for them, but dangerous for millions of users who might still be vulnerable to other bugs like the QuadRooter flaw or a critical flaw affecting the Qualcomm’s Secure Execution Environment (QSEE).
So what’s an Android user to do?
Technical users can install a third-party ROM that accepts updates more regularly. But the average user won’t go to those lengths to protect themselves.
Fortunately, this vulnerability isn’t all that easy to exploit, as Shafranovich elaborates:
“Because this attack require a user to configure a PAC file, and an attacker to be present and know about that file, and the file needs to be served without SSL to make the attack work, the possibility of an attacker pulling this off is low. This is also true because Android, unlike other operating systems does not support the WPAD protocol to retrieve PAC files automatically which can be exploited using a rouge access point or network.”
Fine, but that’s not the case with other vulnerabilities.
For how long must users endure Android’s erratic patching scheme? Let’s hope for not much longer. If that’s not the case, security-conscious users might want to seek alternative operating systems.



0.1% of the world's smartphone users can afford a new pixel or iphone every 2-3 years. "they're all right, Jack" For the other 99.9%, it's "let 'em eat malware!"