
Note: Originally this article’s headline and text referred to 135 million Arris modems being at risk from this vulnerable. Arris has since been in touch to tell us that it would be more accurate to say the figure is more like “up to 13.5 million devices”. We have updated the headline and article accordingly.
Up to 13.5 million Arris modems are at risk of being knocked offline for between three and 30 minutes, because of an easily patchable vulnerability.
Security researcher David Longenecker explains that the SB6141 model Arris (formerly Motorola) SURFboard modem, one of the most popular cable modems in the world with up to 13.5 million currently in production, is vulnerable to unauthenticated reboot attacks due to two flaws.
The first issue is quite basic: the user interface for the modem has absolutely no authentication set up. Astonishingly, this allows a local attacker to look up 192.168.100.1 and access the administration web interface without entering a username and password.
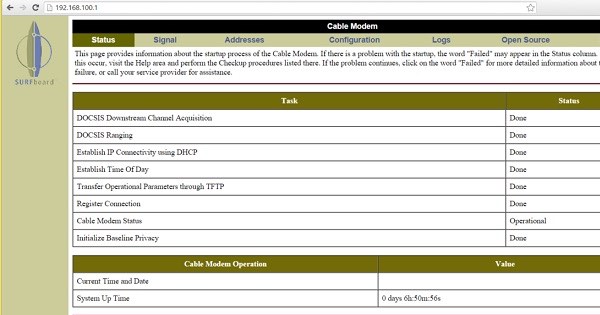
From there, they can have a little fun according to Longenecker’s blog post:
“With access to a local network, it is a trivial matter to reboot the modem serving that network, causing a denial of service while the modem reboots. Granted the modem only takes about 3 minutes to reboot, but for those three minutes, Internet access is offline. Additionally, activity sensitive to network outages (long downloads or remote desktop sessions, for example) may abort.”
Three minutes of no web connectivity is undoubtedly a pain, but in most cases, it’s bearable.
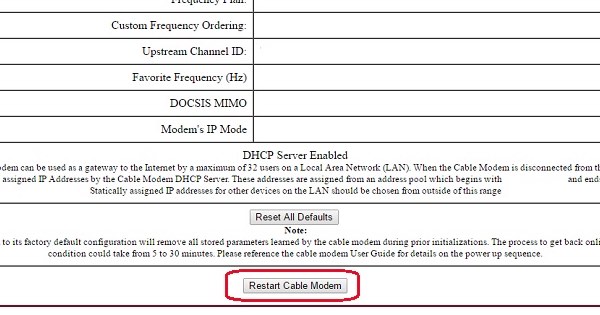
Unfortunately, if an attacker were looking to be an all-out nuisance, that same web user interface provides them with the ability to factory reset the modem. This process takes as long as a half hour to complete, though in some cases it could take an additional phone call to the internet service provider (ISP) to reactivate the modem.
This leads us into our second security issue. Not only can attackers reboot and reset the modem themselves. They can also use social engineering to trick someone else into messing around with the SB6141 for them.
Longenecker explains that all it takes is a simple cross site request forgery (CSRF) attack, as the application does not verify whether the command to reboot or reset the modem actually comes from the modem’s UI.
“Did you know that a web browser doesn’t really care whether an ‘image’ file is really an image? Causing a modem to reboot is as simple as including an ‘image’ in any other webpage you might happen to open… Of course it’s not a real image, but the web browser doesn’t know that until it requests the file from the modem IP address – which of course causes the modem to reboot.”
Pretty serious stuff.
 I have good news and bad news.
I have good news and bad news.
The good news is that these flaws are easily patchable in theory. All Arris needs to do is create a firmware update that does two things: first, requires authentication before someone can use the UI to reboot or reset the modem; and second, verifies that a request originates from the application and not from an external source.
The bad news is that it’s not that simple in practice. Cable modems are not consumer-upgradable, which means even in the event Arris were to develop a fix, customers would need to wait for their ISPs to push the update to them.
This potentially leaves millions of Arris customers out of luck for an indefinite period of time.
While they wait for a patch, those familiar with IP tables could add a rule that limits access to the modem’s LAN interface to only one local IP address and which disallows web browsing from that address. Besides that, there’s not much that can be done.
At this time, Arris has still not created a firmware update… even though Longenecker notified the company of the issues back in January. That is an incredibly long time to delay rolling out such an easy fix.
Update 11 April 2016: Arris has been in touch with a statement:
“ARRIS recently addressed the reported GUI access issue with a firmware update. We are in the process of working with our Service Provider customers to make this release available to subscribers. There is no risk of access to any user data, and we are unaware of any exploits. The 135 million number is not an accurate representation of the units impacted.”



Interesting to know, as I have one, but I will never get a Comcast firmware flash.
Censored, dammit!
So basically, nothing sold to consumers has ever been secure, nor will EVER be made secure, because corporate profits.
What is the point of even trying to use the Internet anymore…
Well the least the attackers could do if they decide to reboot it, is to apply the patch first. This way they have their fun but they also do a service to the victim.
I know many would believe that no attacker would ever do that but they're mistaken: attackers have patched holes (after compromising the site) and e.g. worms have also patched holes (including the Linux Ramen worm – which as I recall shouldn't have compromised any system since fixes for the software were available). Not all that common but it has happened (and probably won't here).
I love this: hackers can access these boxes, but can we mere OWNERS install the [STILL NOT EXISTENT] firmware? NOPE. Nice to know cable modems are not much different than cell phone abandonware. The FCC should fine both Arris and the ISPs for doing jack-squat for nearly three months.
Anyone word on this affecting the 6183?
Can the attacker alter DNS records on the router…? Then the fun would begin.
You can't do anything in the modem there is literally no reason to be worried. They can reboot a modem there's nothing gained nothing lost. They can literally do nothing
Its not true that nothing can be done about this. Many routers can block access to the modems IP address. Problem solved. I wrote about this last year
www.computerworld.com/article/2887243/using-a-router-to-block-a-modem.html