
Accidents happen. We all understand that. And the consequences of a dumb mistake, such as a click on the wrong button, can cause enormous harm to many innocent people.
Take, for instance, what happened at the University of East Anglia in June 2017.
A member of staff sent a spreadsheet to a group mailing list, containing some 298 students from the University’s School of Art, Media and American Studies (AMA).
But she shouldn’t have sent the spreadsheet. Not only because it wasn’t intended for those students, but because inside the spreadsheet were the names of 42 AMA undergraduates, alongside the extenuating circumstances they had registered for essay extensions and other concessions.
Those extenuating circumstances included private medical details, whether they had been victims of sexual assault, if they had had suicidal thoughts, and personal family trauma such as bereavements.
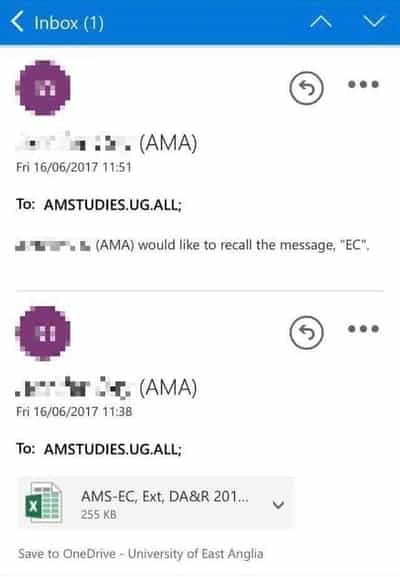
A little over ten minutes later, the email’s sender – realising their terrible error – attempted to recall the email.
I don’t know about you, but the one thing that’s almost certain to make me open an email is if the very next message is one asking for it to be recalled..
Anyway, mere minutes later there was another email sent – practically begging students not to open the spreadsheet and just delete the message.

Dear All,
You may have erroneously received an email with a spreadsheet attachment. Could you please delete this without opening/reading.
Thank-you very much.
Like that was ever going to work… :(
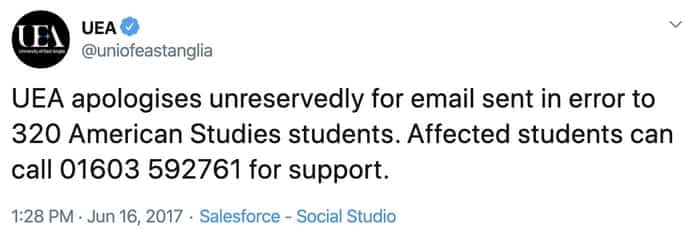
UEA offered support to those impacted, and referred itself to the Information Commissioner.
A subsequent investigation by the University, explained how the spreadsheet came to be sent to the wrong recipients:
A member of staff who was updating information concerning extenuating circumstances (personal circumstances which might affect a student’s performance in assessment or examinations) had not been provided with access to the shared drive. The information was, as a consequence, provided to the staff member as a spreadsheet attachment (that was not password protected). The information was being collated for consideration by a panel on behalf of the examining board for AMS (a sector of AMA).
Following the updating process the spreadsheet was intended to be sent to an internal LTS address that began with “ams…”. The autofill function in the outlook email provided a number of options beginning with “ams…” and unfortunately an incorrect address was used, which was a group email address covering some 298 students. The attachment contained personal data relating to 191 students.
Bet they wished they had password-protected that spreadsheet now. And perhaps had some mechanism inside their email client for asking confirmation before sending a message to a large number of people.
It has now come to light that the University of East Anglia’s insurers ended up paying more than £140,000 in compensation to those whose private details had been treated so carelessly.
You would like to imagine that UEA learnt its lesson from its ghastly June 2017 data breach, but just months later a similar incident occurred – this time breaching the privacy of a member of staff, as a message sent to students, asking them to respect the individual’s privacy, makes clear:
On Sunday afternoon you were sent an email that contained personal information about the health of a member of staff. This message was sent to you in error, and due to the sensitive nature of its contents, we have worked with colleagues in ICTS to remotely extract the message from all recipients’ accounts.
We are aware that many of you will already have read the message, and ask that you respect the privacy of the individual concerned, treat the message as confidential, and do not share or take any action in relation to the information disclosed. If you have auto-forwarding set up on your email account (to send copies of UEA emails to a personal account), we ask that you delete all copies of the message concerned.
Again, the sensitive email was sent to some 300 students.


So, now you've just told an attacker how to trick you into opening his macro-filled-doc: recall it a few minutes latter.