 The researcher who rang alarm bells about a serious Javascript security hole in the popular Mailbox iPhone app, says that there is still a problem – even though the company itself believes it has resolved the issue.
The researcher who rang alarm bells about a serious Javascript security hole in the popular Mailbox iPhone app, says that there is still a problem – even though the company itself believes it has resolved the issue.
Following Italian security researcher Michele Spagnuolo’s revelations that the Mailbox app will execute *any* Javascript which is present in the body of received HTML emails, the company clearly wanted to reassure users that it had the situation under control.
First they said that they were “working on an improvement to mail formatting that will mitigate the issue entirely…” Then Mailbox posted an update on its blog, announcing it had made changes to its backend systems to filter out Javascript from messages it relayed to iPhone and iPad users:
Javascript now filtered from Mailbox messages
Yesterday evening a security blogger raised concern about Mailbox running javascript within HTML email messages. As many have noted, the real risks presented by running javascript within Mailbox are extremely limited thanks to how iOS is designed.That being said, today we implemented a process that strips javascript from messages before delivering them to mobile devices. This feature is now live on Mailbox servers and filtering new mail. This will be particularly important as we develop for other platforms, where javascript vulnerabilities could be more of an issue.
But Spagnuolo, on his own blog, claims that he quickly found a way to bypass Mailbox’s filtering:
While I verified that they now strip some Javascript and no longer load external images, I quickly found a way to bypass it, and Javascript is currently still executed without any user interaction. I will not publicly disclose details – I privately reported details to Mailbox.app and am waiting for a reply.
While it’s good that Mailbox did *something* about the problem, clearly the best fix would be for Mailbox to update their application, rather than relying upon filtering, to permanently prevent Javascript from executing inside their iOS email client.
Although we haven’t seen any reports of criminals exploiting this vulnerability, it’s clearly something that needs to be patched as quickly as possible.
While we’re waiting for Mailbox, now owned by Dropbox, to develop and update and fast-track it through Apple’s vetting to public release in the App Store, we should all be grateful that Spagnuolo hasn’t published details of how to bypass the rudimentary protection Mailbox put in place.
Additionally, the security-conscious might be wise to switch to a different iOS mail client (perhaps the standard Apple-developerd that ships within the operating system, that doesn’t allow JavaScript to execute?)
“We’re working on it!”
Meanwhile, it has also been confirmed that Spagnuolo wasn’t the only researcher to alert Mailbox about the security vulnerability.
Earlier this year, Twitter user @bp_ sent Mailbox a message asking them when they would stop JavaScript in email bodies from being executed.
Their response? “We’re working on it!”
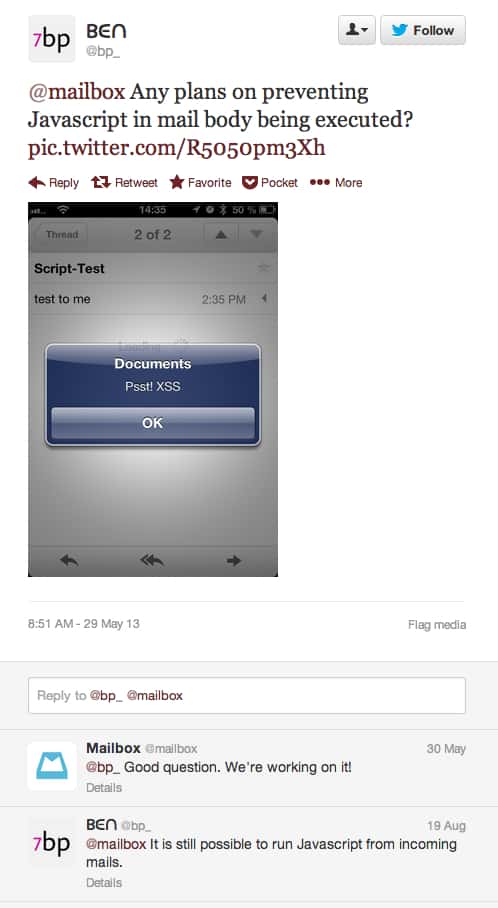
“We’re working on it”? Hmm. That was at the end of May…



This is how it works these times (and tbh, always has): as long as its not a problem(not really encountered "in the wild"), vendors won't care if theres a problem with their code. This, however, does not apply to every company – luckily.