 We’re not really any closer to finding out the real reason why the TrueCrypt project was abruptly shut down last week, but at least some on the internet aren’t prepared to see the open source encryption tool disappear without a fight.
We’re not really any closer to finding out the real reason why the TrueCrypt project was abruptly shut down last week, but at least some on the internet aren’t prepared to see the open source encryption tool disappear without a fight.
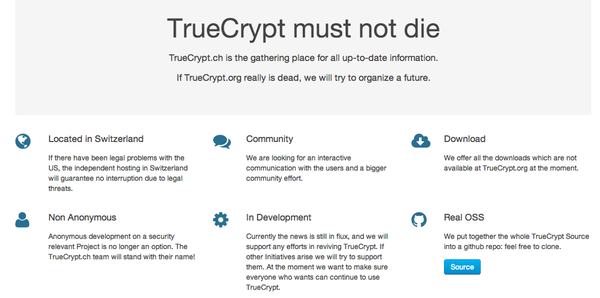
A team of developers led by Thomas Bruderer and Joseph Doekbrijder are hoping to rescue TrueCrypt, or – at the very least – develop a new product based upon its code.
To that end they have set up a website – www.truecrypt.ch – where they are offering downloads of TrueCrypt 7.1a.
If you recall, the anonymous developers behind the umm.. “true” TrueCrypt withdrew version 7.1a, claiming it was “not secure as it may contain unfixed security issues” and replaced it with a decrypt-only version 7.2 edition.
That announcement surprised everybody. TrueCrypt is a respected piece of security software, used by many to encrypt their sensitive files and entire hard drives. Earlier this year, independent auditors found “no evidence of backdoors or intentional flaws” when examining its code.
Nonetheless, the anonymous coders behind TrueCrypt have shut the door and pulled down the shades.
The TrueCrypt.ch team are clearly frustrated by the abrupt cessation of the software, and say that they will do things differently.
Non Anonymous
Anonymous development on a security relevant Project is no longer an option. The TrueCrypt.ch team will stand with their name!Community
We are looking for an interactive communication with the users and a bigger community effort.In Development
Currently the news is still in flux, and we will support any efforts in reviving TrueCrypt. If other Initiatives arise we will try to support them. At the moment we want to make sure everyone who wants can continue to use TrueCrypt.Real OSS
We put together the whole TrueCrypt Source into a github repo: feel free to clone.
 What I find interesting about Bruderer’s and Doekbrijder’s move is that TrueCrypt is different from most other “open source” software, in so much as although the source code can be examined by anyone who might want to explore if there are any vulnerabilities or backdoors, you are explicitly *prohibited* from modifying the code, or using it as the basis for your own products.
What I find interesting about Bruderer’s and Doekbrijder’s move is that TrueCrypt is different from most other “open source” software, in so much as although the source code can be examined by anyone who might want to explore if there are any vulnerabilities or backdoors, you are explicitly *prohibited* from modifying the code, or using it as the basis for your own products.
It’s clear that TrueCrypt’s anonymous developers have never wanted others to build upon their code.
And yet, that appears to be precisely what the truecrypt.ch project is planning to do.
This, it appears, is one of the reasons why truecrypt.ch is being run from a web server based in Switzerland. As the site explains:
Located in Switzerland
If there have been legal problems with the US, the independent hosting in Switzerland will guarantee no interruption due to legal threats.
In short: we don’t care if the original developers don’t want us to mess around with their code, we’re too far away for them to have any control over what we do.
Hmm… I’m not sure I feel too positive about that approach, and I hope they will have a good think about it.
Of course, such a geographic location may also be beneficial if some of the conspiracy theorists are correct and TrueCrypt was shut down after pressure was placed upon it by law enforcement agencies.



pretty sure the "legal problems" thing is primarily a reference to national security letters / nsa interference and not the truecrypt license, which nobody is scared by
The wording "If there _have been_ legal problems _with the US_" confirms that interpretation. First, it refers to possible past legal issues, not potential future ones. Second, it says that the possible legal issues are with a nation rather than with any person or private entity. Both point away from licensing issues and toward three-letter-agency interference.
See my point about encryption export restrictions, below. It isn't that simple always. Does it apply here? Without looking at the source (and I'm way too tired for that) I cannot confirm what algos it uses and without that I cannot even check which countries it would be a problem with. But since they're supposedly using their names, it could be an issue. Never underestimate a country's power (will power even) and always expect (legal) loopholes to be abused. After all, they are abused without any remorse and quite often, even in non national/international cases. National and international more so!
Actually, open source licenses _can_ lead to serious problems even if it is more often done by public shaming (the reason most cases are not pursued in courts is shaming is far more vocal and far more hurtful to an organisation/company/whatever – reputation is quite important, after all… and why bother beyond that? This is especially true when it is non-profit or otherwise not a company making money from the product. What would they gain by suing? Compare that to shaming them, though.. even if it doesn't effect the end product/service negative publicity is never nice). I can think of an example that is well known (to a certain community) but it isn't relevant to security so I'll avoid that.
Also, there is something else related to encryption and legal matters: encryption export restrictions (though this may not apply here, there is this issue all the time with open source operating systems and what software is installed and specifically what encryption algorithms it uses… depending on what country you reside in – more specifically: the location of the machine – you can land yourself in major legal trouble – with a country). Don't kid yourself: it can be very serious and realistically, what individual wants that from a country? None that I'm aware of. And it is actually less restrictive nowadays. Indeed, the US used to have far more restrictions, even on weaker algorithms (think DES was one of them but I'm so tired at this time and I cannot be bothered confirming that this one is now clear… the point remains the same though).
From the TrueCrypt license agreement:
“2. You may not use, modify, copy, create derivative works of, (re)distribute, or sublicense this product, or portion(s) thereof, except as expressly provided in this license (even if an applicable law gives you more rights). Any attempt (even it permitted by applicable law) otherwise to use, modify, copy, create derivative works of, (re)distribute, or sublicense this product, or portion(s) thereof, automatically and immediately terminates your rights under this license and can constitute copyright infringement (which may be prosecuted). Any conditions and restrictions contained in this license are also limitations of the scope of this license and also define the scope of your rights under this license. Your failure to comply with the terms and conditions of this license or failure to perform any applicable obligation imposed by this license automatically and immediately terminates your rights under this license and can cause or be considered constitute copyright infringement (which may be prosecuted). Nothing in this license shall imply or be construed as a promise, obligation, or covenant not to sue for copyright or trademark infringement if you do not comply with the terms and conditions of this license.”
I don’t know about anyone else, but the intent of the TrueCrypt owner(s) seems pretty clear to me. They don’t want anyone stealing their code.
The slogan “TrueCrypt must not die” has all the earmarks of an impassioned crusade — an attempt to invoke some emotional, ill-defined, fuzzy pseudo-principle that (the crusaders hope) will strike a resonant note that will draw a mass of others to their cause, and thereby justify their actions by force of numbers. It’s the moral equivalent of, “There are lots of us, therefore we must be right.”
Apart from the intellectual bankruptcy of such a notion, the crusaders appear to be falling back on another cherished belief of those who steal—namely, “My need is a claim on your property.” Because they feel they “need” TrueCrypt, that justifies stealing it.
Wow.
I suspect that if it were their own work product and someone else stole it, they’d be squealing like stuck pigs.
"I don’t know about anyone else, but the intent of the TrueCrypt owner(s) seems pretty clear to me. They don’t want anyone stealing their code."
That is not at all the case. Did you even read the rest of the license, in particular section III which exactly specifies the conditions under which a derivative product is permitted?
"III. Modification, Derivation, and Inclusion in Other Products
1. If all conditions specified in the following paragraphs in
this Chapter (III) are met (for exceptions, see Section III.2)
and if You comply with all other applicable terms and conditions
of this License, You may modify This Product (thus forming Your
Product), derive new works from This Product or portions thereof
(thus forming Your Product), include This Product or portions
thereof in another product (thus forming Your Product, unless
defined otherwise in Chapter I), and You may use (for non-
commercial and/or commercial purposes), copy, and/or distribute
Your Product."
Sorry but it is never that simple. Not in other fields even. But _especially_ with the TrueCrypt license. Perhaps you should look here:
http://threatpost.com/audit-aims-to-put-concerns-over-dubious-truecrypt-license-to-rest
or better yet, here: http://comments.gmane.org/gmane.comp.licenses.open-source.general/13108
As well as searching "TrueCrypt license dangerous" and/or "TrueCrypt license problems". In fact, the OSI (and I refer to the Open Source Initiative – NOT the networking OSI) does not consider it open source. It is a poorly written license and the fact the OSI doesn't even consider it open source (by license) says a lot. No, make no mistake: legal issues aren't as simple as reading certain sections, all sections or any in between (and let's not forget words like notwithstanding which completely changes up the meaning of the law/license/whatever). Do you really believe law is that simple? You know, the exams required for lawyers are not exactly 1 + 1 = 2. Not only that, name one lawyer who has not ever abused a loop hole and I'll name one lawyer who isn't a lawyer, is lying, or is very naive (and a very poor lawyer). And to think this issue is so simple (despite what license/legal folks suggest) is either very naive (or really brave). There's a reason why open source operating systems (e.g., Fedora Core) don't have certain software in their repositories. Licensing is one of them. It is a pain in the side of users of said operating system (including me). Bluray comes to mind too (no matter any ways around it, legalities cause issues, for sure). In fact, I can think of many examples of this but I think the point should already be clear.
In fact, just to make it more interesting: You could call their license a proprietary license. There, that summarises it quite well. In other words, you’re playing with fire. Also being in another country isn’t exactly a safe haven _especially_ with encryption (though standards/etc is different in that regard).
Location in Switzerland does not mean anything. The Blackphone also announced they will "move" to Switzerland. However, since June 2014, e-mails, phone and text details must be stored by the provider for one year. And there is no guarantee the data won't be shared with the U.S. Just look at happened with the bank data (U.S. clients in Switzerland). Actually, getting a warrant for obtaining communications data is quite easy for regional (county) police.
"In short: we don’t care if the original developers don’t want us to mess around with their code, we’re too far away for them to have any control over what we do."
Ummmm no, it does not sound like that is what they are saying at all. It makes more sense that they are referencing the widely discussed theory that a US government threat is behind the shutdown, a la Lavabit. And so this statement (“If there have been legal problems with the US, the independent hosting in Switzerland will guarantee no interruption due to legal threats.”) is to say that they will be immune to such threats, not to say F-U to the TrueCrypt developers.
Plagiarism ring a bell? It should. Then consider these points:
I suggest you look up encryption export controls, among other things. They're (potentially) playing with fire. Also, even in the case that Switzerland is not restricted (or that TrueCrypt does not use a restricted algorithm), that does not mean they are completely clear as there is still the issue of licenses in general. Then there's the fact (that I just wrote about) that this license is anything but clear, has problems in many forms and is not considered open source (by the open source initiative, aka OSI).
Whether they are _also_ referring to the US agencies is irrelevant. As a programmer who uses open source every single day, as well as a programmer who has no problem submitting patches (to fix a bug or add features to) software developers, and more, all on free time, there is nothing more infuriating than some arrogant loser who takes credit for what they wouldn't have without someone _else_. I would argue that it is way better they take the end result (e.g., the actual software after being compiled and linked) and use it than they take the source, rip it apart and then claim it is their creation. Simple reasons really and that's why even schools (you know, seriously lacking ethics among other things) do not tolerate plagiarism! The sad part is all it takes is citing your sources to not only add interesting bits to (whatever) but it also shows your credibility, it shows you can do research (for whatever) and it shows you can actually put thoughts into words and sentences (and ultimately into to paragraphs and into an actual article/essay/whatever it may be). In short: you have elementary skills in reading and writing. Instead, you show how pathetic you are (because let's be real: those who plagiarise often use very well known texts. Why? Again: they cannot read and write and they likely cannot think through things thoroughly and therefore simply take what they find, usually being the most well known sources).
Coyote, what are you going on about?! I'm not talking about book reports. I'm talking about the fact that the new developers are referring to legal threats from the US government, not from the previous developers, and that seems pretty obvious if you carefully parse their statement. Anyhow, as for hypothetical legal threats from the previous developers, wouldn't the previous developers' bigger obstacle be not where the defendants are based but that they, as anonymous plaintiffs, are going to find it impossible to establish standing to bring a suit? ;-) That is, unless they plan on coming out into the open, which could be a positive thing in the end however for everyone wanting to understand the provenance of the software.
Graham, have you noticed that the URL slug for this page is
/truecrypt-must-die ?
Freudian slip?
If I were part of an anonymous team of developers and I wanted to publicly 'out' myself while severing all legal ties to, risks from, and future repercussions of prior work, while under a gag order, my behaviour might look something like…
'New'? group going public in a safe haven. Provisions for use in the 'badly written' license. The probability of an anonymous group stepping forward to assert their copyright. The likelihood of jail time for *plagiarism* under dubious restrictions. Abrupt termination with (hah!) exhortations to use a proprietary alternative.
Maybe the developers were aware of future potential repercussions 10 years ago when they started writing unbreakable crypto for the masses. TrueCrypt pays significant attention to plausible deniability.
More power to whoever continues supporting this awesome tool for the decades to come. It is sorely needed in the modern world.