More than two weeks after the mysterious demise of the TrueCrypt encryption tool we’re none the wiser about why the project abruptly shut down.
But now some are claiming that the clue was right beneath our nose all along.
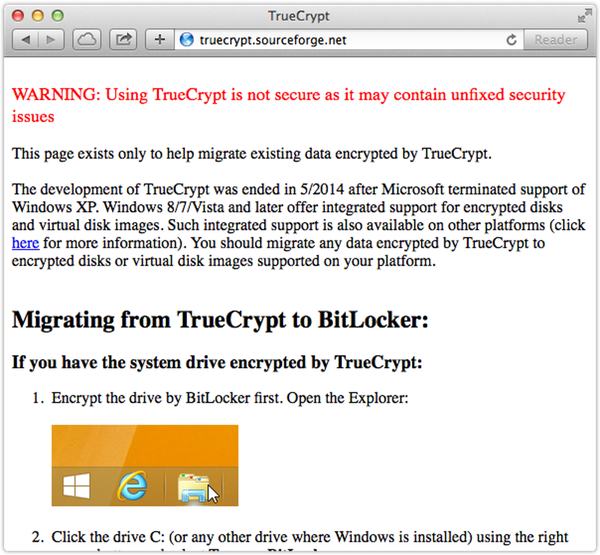
See that first sentence on the TrueCrypt project’s homepage on SourceForge?
WARNING: Using TrueCrypt is not secure as it may contain unfixed security issues
If you take the first letter of each word (except the word “WARNING”) you get:
Using TrueCrypt is not secure as it may contain unfixed security issues
or
utinsaimcusi
Gibberish?
Perhaps not, allege those with a love of unravelling puzzles. Because if you split “utinsaimcusi” up with a few judicious spaces you end up with…
uti nsa im cu si
Which Google translates from Latin as:
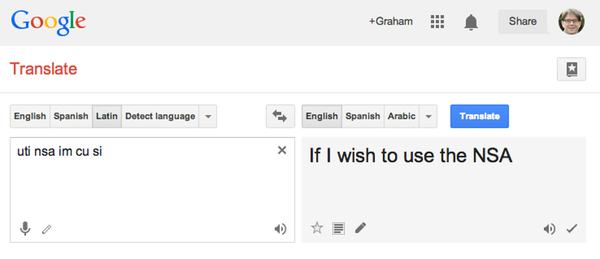
Some claim that – in context – the letters roughly translate to:
Don’t use TrueCrypt because it is under the control of the NSA
(Boy, I wish I had been taught Latin at my school…)
You can read more about the conspiracy theory (trust me, it goes far beyond what I’ve reported above) in a post here.
Maybe it doesn’t really matter to most of us quite why TrueCrypt shut down. What’s clear is that no-one who is security conscious can trust the software ever again.
As I said at the end of last month, it’s time to start looking for an alternative way to encrypt your files and hard drive.
Crazy or genuine conspiracy? Let us know what you think by leaving a comment below.
Hat-tip: @xavier2dc



Clever! ;)
Apparently the Google translation is a bit of a fluff, and as latin goes it is a very poor attempt.
There are many threads across the web looking at it, and in one (http://www.dslreports.com/forum/r29309869-TrueCrypt-Latin-Translation-Nipping-this-in-the-bud) one respondent – who gives the impression of knowing what they are talking about – begins their answer "Google indeed translates it as the pastebin blurb suggests, but in reality, it makes no sense."
Like all good conspiracy theories the the evidence favours a conclusion against, but the elegance is the idea is too appealing for some people to let go.
Agree, but your point is based on the assumption that truecrypt devs know Latin as well as latinist. What about the hypothesis that they use an automatic translation tool too?
Anyway the deduction is true indeed: don't user truecrypt anymore.
Good point! Plus we have to remember that it would be very difficult to build a sentence which makes sense and the first letter of each word makes another sentence in different language and is completely correct.
If they had used an automatic translation tool, this would have been the result https://translate.google.com/#en/la/If%20I%20wish%20to%20use%20the%20NSA
I wonder how long it took them to discover the spacing so that translating it from multiple languages actually gave something that made a bit of sense in english.
I did five years of Latin (and in the end, I loved it), but this is genius in figuring out this one.
Bravo to you.
How about using CryptoLUKS containers or full-disk enc?
LUKS is certainly nice. But most don't use an operating system using the Linux kernel. Or are we thinking of something else? Nowadays there is another way (well, as if there ever was only one way) – ecryptfs (not sure when it first arrived, as in first release to the world, but I do know it is one of the options that is readily available for some time now).
Of course, even XOR encryption or ROT-13 (depending on what you're "encrypting") is better than encryption that is in limbo (in the sense of validity) like TrueCrypt as at least with those you know (or should know) that they are hardly sufficient whereas in the latter you are believing you are better off but may in fact be at risk.
I'm always skeptical of conspiracy theories. Use of the word "unfixed" is the least surprising thing about the shutdown message, which at first sight looked like the work of a troll. It's amazing what you can make of friends' or celebrity's names with an anagram solver with a bit of effort. And the things that people have made out of the Bible using tricks like this are without number. To my mind, this comes under the same category. Perhaps if we really tried we could find something in Nostradamus which predicts the demise of TrueCrypt!
Credible evidence is presented at https://www.grc.com/misc/truecrypt/truecrypt.htm of a conversation which resulted from an email response from an address which had previously been used to communicate with the TrueCrypt team. This specifically refutes any government involvement.
If they wer forced by a judge order to be silent, they MUST refute or they risk jail.
The order may be secret. Therefore, because of that secrecy in US courts, any disclaimer would not be credible.
So who is going to jail them when nobody even knows what country they're in?
We don't know who they are. That doesn't mean someone with the resources on the level of security agencies of one of the biggest (in economical terms) countries in the world can't figure it out.
Credible evidence and grc.com do not mix. Steve Gibson is a charlatan, plain and simple. That is old news but if you don't believe me, try google search "steve gibson charlatan". Here, I'll do it for you:
https://www.google.com/search?output=search&sclient=psy-ab&q=steve+gibson+charlatan&btnG=&gbv=1&sei=RnCgU9fKGNClqAbMl4L4Aw
And I can personally verify the (at least at this time) first result as being valid (but hell, don't believe me; look at their evidence, sources and then some. Then think about it). Attrition is sound and he (that is, the folks behind Attrition) goes way back. He's also exposed other charlatans (I'll refrain from naming them as they just make me cringe…). But even then, some of the things Gibson has claimed/stated/whatever is just so far technically incorrect it is beyond ridiculous. His claim that he created a better version of syn cookies? Sure he did. He did a lot of supposedly brilliant things – in his own fraudulent reality, that is. That raw sockets are what are the source of DDoS attacks? Again, nonsense. Here's a good one on Attrition which explains only one of many of his (Gibson's) fraudulent claims and supposed feats (his only real feats (!) are those he fools as in those who believe things too easily and/or are not experienced in the subject!):
http://attrition.org/errata/charlatan/steve_gibson/grc-xss.html
Anything Gibson has written/sold/said/whatever else is highly suspect.
Rather stated: his only feats are fooling others. And he only fools others who believe things too easily or are not experienced in the subject (or know of the person). In other words, like all frauds, he keeps it up so that he can make money out of it. It's a right shame more don't call him out. But he is anything but a security expert (let alone a computer expert). Don't even get me started on his so called stealth ports… Especially ironic as when his site scans your system you are exposing quite a lot about it (more than you might think). Imagine how that works with non charlatans….
Congratulations, you've managed to figure out something that has been known since the very first day truecrypt shut doors.
Very well done, slow one!
I Imagine your next move will be to grunt and swing a mace around…
if you whant you can find the older versions of truecrypt online there are various sites with them, i have tested them and the 2 versions before the last one , test always positive for malware, maby i´m wrong but… maby not
That would likely be heuristics. Encryption, antidebugging techniques, polymorphism and more, are all ancient tricks used by both virus writers and antivirus writers. These are also used to (help) in protecting software in the sense of license/registration (see next point also). Yes, this is the same reason that some legit (as in, not malware – not referring to legalities) utilities meant to crack (proprietary) software are found to be malicious. In fact, some are just false positives. That is expected though. Nothing is fool proof and heuristics are no different. You'll even find antivirus software reporting one virus as another as well. Some times (but not always) you'll see rather general names for these cases and there's a reason for that: it isn't a known identified piece of malware.
Sorry, but you just can't trust Google Translate that much. There are only two Latin words there: "uti" (to use) and "si" (if). "im" and "cu" are not Latin. However, their presence tickles Google Translate in some strange way to add in "I wish" (which in actual Latin would be "volo").
(For another example of Google Translate doing weird things, ask it to translate "I hope you can read French" from English to Latin – why does it start "Lorem ipsum"??? And then add "." at the end of the sentence and watch how the translation changes. Do you still trust Google Translate?)
In Serbian language:
"uti nsa im ću si" -> "I hear they're nsa"
(by google translator)
Thank you for your help! I did an update to my article based on this information, have a look:
https://www.livebusinesschat.com/smf/index.php?topic=5629.0
And of course, thank you to Graham Cluley for writing about this topic.
In Alpha Centaurian the phrase means: "We're surrounded by Illuminati, hail Iris!"
Serbian guy here. That stuff doesn't mean anything in Serbian, nor Bosnian/Croatian. I can't recognize a single word of it as Serbian.
I hear they're nsa would be something like "čujem da su NSA" or "čujem da su oni NSA" to make it closer in google translate.
Using google auto language detect, it appears to be Serbo-Croatian, not latin.
uti im ću si translates to 'I hear they're'. Putting the nsa bit either after uti or at the end makes it 'I hear they're NSA'.
Surely this makes more sense?
I never felt entirely comfortable about using TrueCrypt due to the developer anonymity and the license, despite its recommendations by people I know and generally trust. However, if the encryption is properly implemented its strength will be in the keys and the algorithms, which are some of the standard and well-analyzed ones.
If NSA or anyone else has found a way around some of the algorithms it would be news that we have not yet heard. If weaknesses in the implementation expose keys or provide another workaround, it would not be unusual. It is to be hoped that the code audit Matthew Green and others undertook will be completed and provide information about whether that is the case. Until and unless that happens, speculation about NSA back doors is just that, and fairly pointless apart from entertainment value.
Re: " However, if the encryption is properly implemented its strength will be in the keys and the algorithms, which are some of the standard and well-analyzed ones."
MiTM? Or maybe you are indeed referring to that by "properly implemented" … Also you do cover strength itself which is something to consider too.
Re: "Until and unless that happens, speculation about NSA back doors is just that, and fairly pointless apart from entertainment value."
Indeed. Spreading such is unhelpful and in fact dangerous. Of course, those who have been into computers (even without security in mind) for long enough are sure to remember certain incidents which led to companies put out of business… all related to speculation/sensationalism/other things.
As for the NSA, while I think a lot of it is fear-mongering (rather sensationalism… as at least some of it is not all that technically advanced and much of it is not surprising), I think also true is that the NSA has far more for them than is generally thought. They were critical (read: protective) of encryption standards long before their supposed reasons (or excuses) as to why they are so in to it 'now' (the problem is: it isn't now, it was and is 'always' but they now make excuses that make some people – admittedly naive – feel safe). They were involved with (although not the creators of and it is supposed they did not tamper with it) DES and that is from the 70s, for one example. Keep in mind encryption export restrictions too. None of this is new by any definition of the word 'new' (except that odd one where some people use a word with the exact opposite definition… but that is a people problem, not a word problem).
Edit: Ah, yes, you do cover my first thought, if I interpret it right this time: “If weaknesses in the implementation expose keys or provide another workaround, it would not be unusual.”
Your thoughts on this are pretty close to what I was thinking. Why would the NSA specifically target TrueCrypt? Why was TrueCrypt in particular a very big problem for them, compared to other (even open source) encryption solutions?
Maybe it has something to do with the encryption methods/ciphers offered. I cannot think of any other encryption programs at the time that offered cipher cascading. Maybe this presented an issue for them, if the NSA had knowledge of a way to weaken "standard", one-cipher encryption in some way?
Some more disturbing news: If you take the pure text on truecrypt.org, strip all whitespaces, linebreaks, interpunction and numbers, you get a string with 3217 characters. "Three (letter agency) to one's even" – got it? But there's even more:
1732 is the year George Washington was born – the first president of the United States!
Now take every 1188th letter. 1188 is not only the number of the German directory assistance, it contains "18" or "AH" which is Nazi code for "Adolf Hitler". In the year 1188 the Newgate Prison in London was built. And if you take every 1188th letter, you get – "WTF"! You want to know more? "WHO" you ask (which is every 1214th letter) and as a response you get "WAU" as every 1215th letter. Wau Holland is a very famous German Hacker, co-founder of the Chaos Computer Club.
Still need some more proofs? Take every 541th letter and you get "WTCEOT" – World Trade Center Eclipse Of Terrorism! And finally, take every 495th letter "WCUYNSA" – We see you. Why? NSA.
There are loads of more hidden message in this text. You simply have too keep your eyes open and your mind awake.
The entire thing is an anagram. Solve it.
Well… if you ask me, I'll keep it simple. The reason they stated for shutting down is because Microsoft suspended support for Windows XP.
Why hasn't anybody pointed this out?
Please excuse me while I use Truecrypt on Linux like I always have.
So what ?
TrueCrypt worked perfectly well on Vista, and Windows 7 too, both which had plenty of time before retirement back then.
XPs end of life wasn't any real reason for closing down TC.
People who refute that there is a hidden message by stating that the language is incorrectly used are in fact themselves, incorrect. In the mind of a cryptic, a service such as Google translate is just that – a code or decoding tool for their Null Cipher (ancient roots just as Latin) and therefore the underlying language has less significance than that of the underlying message. Why use Latin and why use Google? Because it is not completely obscure and readily available and is nothing more than a common algorithm available to all just as Latin is the common root of most language. Now let's take this to the next level – if you take the initial Null Cipher and reverse it, you receive two lines of "Code." Shift the letters a bit from previous author's interpretation, and you get this:
"uti nsa im c usi
is u c mi a sni tu"
Notice that the top line is the Cipher left to right, and the bottom line is the Cipher reversed or right to left.
Literal translates from Latin to English as this:
"c im used to NSA
c u is awarded by my art"
What does the "c" mean? Perhaps it signifies an abbreviation for "Comment," "Code," "C Language" or even, "YES" as in the Spanish "si" (Spanish has common Latin Roots). But either way, there is little room for coincidence as the message logically translates into near perfect English. So what does this literal message mean?
The message may be interpreted as follows:
1. The Author left a code that he/she "used to be NSA" and that "his/her art/program will grant you an award/anonymity
2. The Author is "used to the NSA" causing him/her difficulty in life and that they are leaving the this message as a way for you to continue to reap the benefits of their "art"
Either way, there is no doubt that someone of this caliber logically wouldn't leave some form of cryptic message. Even if they were shut down by the NSA, or simply wanted to retire and wanted to leave a puzzle for you to figure out, a cryptic mind combined with a form of human ego would surely leave them with little room but to keep their legacy alive – and what better way that to keep you guessing?
To me, the message is clear – the Author acknowledges that their program is a work of Art and cannot be tainted by the NSA, even if they must peel back layers of the onion and go underground.