
On New Year’s Eve foreign currency exchange service Travelex took its systems offline after it discovered a “software virus” (as opposed, presumably, to a common cold) had compromised some of its systems.
The company, which claims to be the world’s largest foreign exchange bureau, is still offline today – as anyone visiting its website can see for themselves:
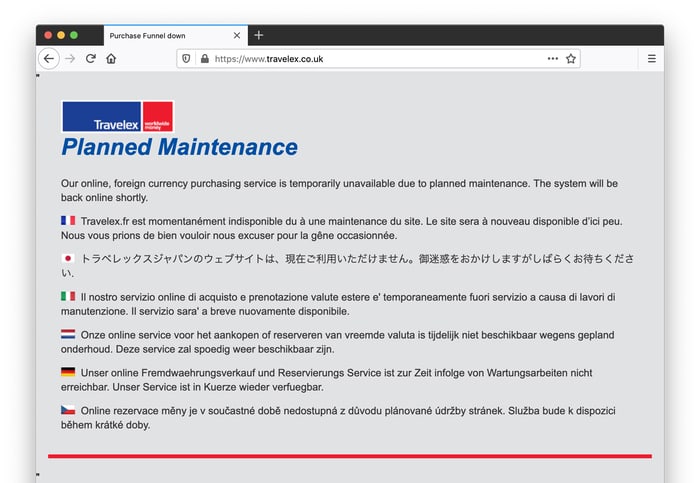
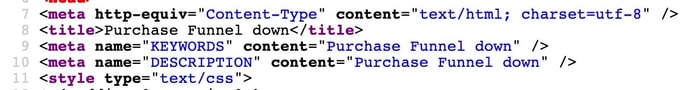
The holding page, which offers apologies in a variety of languages, has a title of “Purchase Funnel down” – hardly the friendliest customer-facing way to describe the issue, but I guess they have other problems on their plate at the moment.
According to BBC News, other banks including Barclays, HSBC, Sainsbury’s Bank, First Direct, and Virgin Money have been unable to offer online currency services due to the problems at Travelex.
The Travelex smartphone app has also suspended while the firm’s IT team attempts to resolve the issue, and purchasers of Travelex’s pre-paid currency cards have been complaining online that they have not been notified that services have been disrupted.
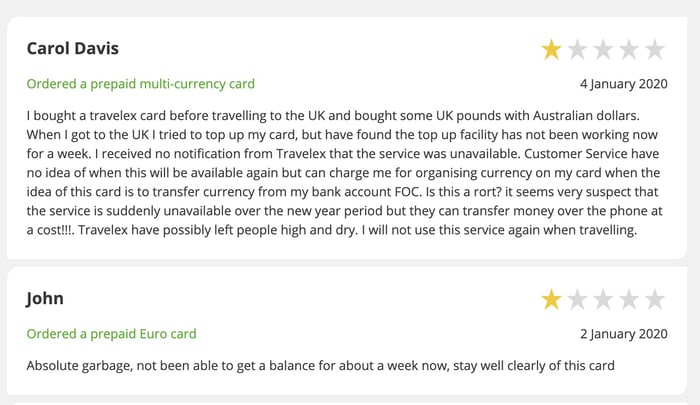
Customers needing foreign currency for their overseas trips are being advised to visit a Travelex store in person where staff can conduct transactions manually.
So, we know that the cyber attack against Travelex has been enormously disruptive. But what we don’t know at the moment is the nature of the malware involved – although some are suggesting it is likely to be ransomware-related.
Whatever the nature of the attack, there clearly needs to be a proper investigation as to whether Travelex’s systems were properly resilient and if enough resources were being put into ensuring that systems were being properly secured.
Disturbingly, security researcher Troy Mursch shared on Twitter details of security vulnerabilities he discovered on Travelex’s infrastructure back in September 2019, but for which he claims he never received a response.
Further reading: “Planned maintenance”? Travelex’s masterclass in how not to respond to cyberattack


