
As we described a few days ago, foreign currency exchange service Travelex discovered on New Year’s Eve that its systems had been compromised by hackers.
The company’s websites worldwide were brought down unceremoniously, and a few days later users were still being greeted by an error message.
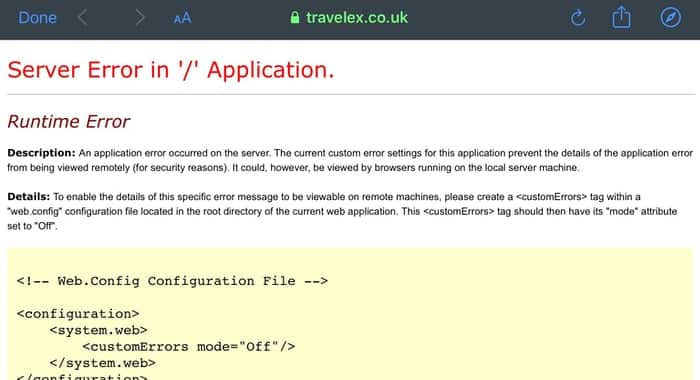
Whether the website downtime was a consequence of the attack, or a deliberate action by the company is unclear.
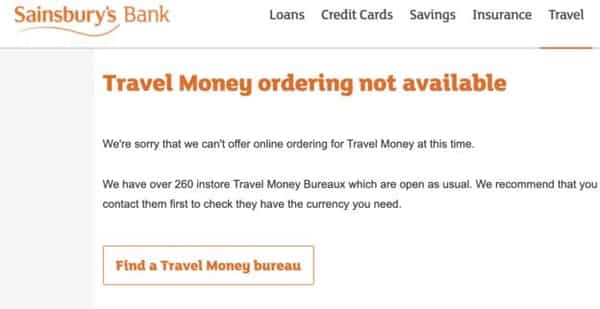
But it’s certainly hardly the most informative message for customers who might have found that they couldn’t access their accounts, or use the Travelex app, or were attempting to purchase currency online through many of Travelex’s partners such as Barclays, HSBC, Sainsbury’s Bank.
But never fear! After a few more days the Travelex website was updated – albeit to explain that the website was “temporarily unavailable due to planned maintenance.”
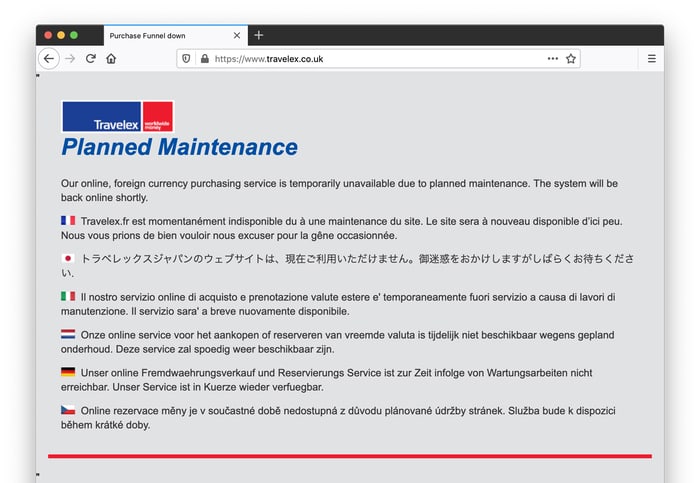
“Planned maintenance”? Hmm… Travelex’s official Twitter account was a little more forthcoming with the truth, admitting that its systems had been hit by a “software virus”.
Speculation rose meanwhile in the technology press that Travelex had been hit by ransomware, and that staff had been ordered by bosses not to answer any questions about the incident but simply refer to it as a “system problem.”
Now, finally, Travelex has ‘fessed up that yes – it was ransomware that infected their systems. Its beleaguered webpage was updated with a press statement yesterday:
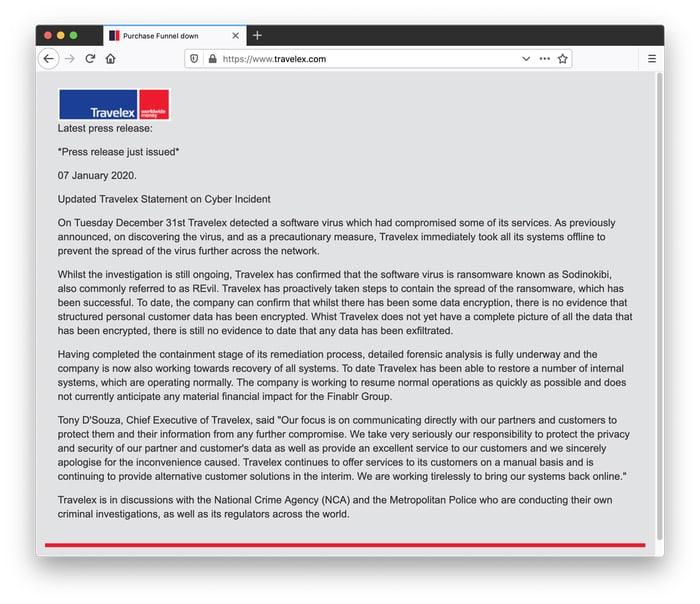
Part of the press release reads:
Whilst the investigation is still ongoing, Travelex has confirmed that the software virus is ransomware known as Sodinokibi, also commonly referred to as REvil. Travelex has proactively taken steps to contain the spread of the ransomware, which has been successful. To date, the company can confirm that whilst there has been some data encryption, there is no evidence that structured personal customer data has been encrypted. Whist Travelex does not yet have a complete picture of all the data that has been encrypted, there is still no evidence to date that any data has been exfiltrated.
Having completed the containment stage of its remediation process, detailed forensic analysis is fully underway and the company is now also working towards recovery of all systems. To date Travelex has been able to restore a number of internal systems, which are operating normally. The company is working to resume normal operations as quickly as possible and does not currently anticipate any material financial impact for the Finablr Group.
Travelex doesn’t mention it in their press release, but according to BBC News, the hackers responsible for the attack have demanded a US $6 million (£4.6 million) ransom be paid for the safe recovery of Travelex’s encrypted data.
What Travelex does say in its press release is that it doesn’t believe that there will be any financial consequences for its parent company Finablr resulting from the incident.
That’s an odd message to put in a statement for customers who are simply trying to get their Travelex money card to work properly. And my suspicion has to be that it’s not actually a message intended for Travelex’s customers, but instead for their blackmailers.
In short, it says to me that Travelex is not intending to pay the ransom.
Bleeping Computer says that it has been in touch with the cybercriminals who infected Travelex’s systems, and that they claimed they would release personal details of Travelex customers if the ransom is not paid:
In addition to the ransom note, the Sodinokibi crew told Bleeping Computer that they encrypted the entire Travelex network and copied more than 5GB of personal data, which includes dates of birth, social security numbers, card information and other details.
We were told that they deleted the backup files and that the ransom demanded was $3 million; if not paid in seven days (countdown likely started on December 31), the attackers said they will publish the data they stole.
Looking again at the latest statement on Travelex’s website I’m shaking my head in disbelief. Any company with even the smallest level of concern for its customers would surely offer a link to an online FAQ, or a phone number or an email address which users could turn to if they had any questions or concerns after being left without access to foreign currency.
I can’t help feel that Travelex would be in less of a mess now if it had been more transparent with the customers and media about what was happening from the beginning.
As it was it was technology journalists and security experts who were revealing facts about the attack, long before they were admitted by the company itself. Inevitably that didn’t make (and continues not to make) Travelex look good.
Last year Norsk Hydro suffered a much more serious cyberattack than Travelex, and yet managed to come out of it with its reputation not only intact – but actually enhanced.



I wonder whether the savings made by firing some of their Cyber Security Consultants will cover the cost of fixing this?