
The Tordow v2.0 Android banking trojan seeks to gain root privileges on infected devices and is capable of mimicking ransomware.
In late November 2016, Comodo Threat Research Labs came across the second version of a trojan originally discovered by Kaspersky Lab several months earlier.
Both versions rely on a common-enough distribution vector: rogue apps.
Comodo’s research team explains in a blog post:
“Tordow spreads via common social media and gaming applications that have been downloaded, reverse-engineered, and sabotaged by malicious coders. Apps that have been exploited include VKontakte (the Russian Facebook), Pokemon Go, Telegram, and Subway Surfers. Infected programs are usually distributed from third-party sites not affiliated with official websites such as the Google Play and Apple stores, although both have had trouble with hosting and distributing infected apps before. Hijacked apps usually behave just as the original ones, but also include embedded and encrypted malicious functionality including the C2 communications, an exploit pack for root access, and access to downloadable Trojan modules.”
Not much of a surprise that attackers are going after Pokemon Go. They’ve been disguising their attacks as versions of the game for months now.
But don’t think for a second Tordow v2.0 is like other banking trojans. It isn’t. That’s primarily because the malware seeks to gain root privileges on infected devices so that attackers can achieve as much functionality as possible with their program.
Here’s some of what Tordow v2.0 can do with superuser rights:
- Download and install programs.
- Make telephone calls.
- Intercept and send SMS messages.
- Remove security software.
- Steal login credentials.
- Reboot a device.
Not scary enough for you? There’s more.
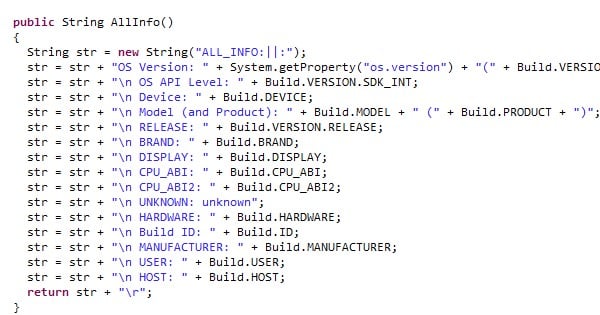
Tordow v2.0 collects a whole bunch of data from the infected device including hardware and software, operating system, manufacturer, Internet Service Provider, and user location before sending it off to its command and control (C&C) server.
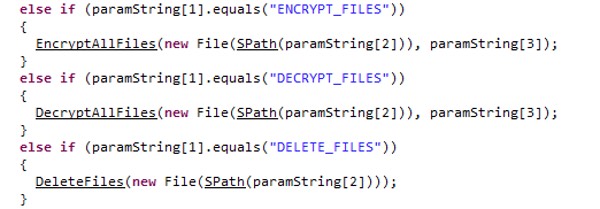
It also can mimic ransomware insofar as it’s capable of encrypting files.
Per Comodo’s analysis:
“Tordow 2.0 possesses CryptoUtil class functions with which it can encrypt and decrypt files using the AES algorithm with the following hardcoded key: ‘MIIxxxxCgAwIB’. Its Android application package (APK) files, with names such as ‘cryptocomponent.2’, are encrypted with the AES algorithm.”
To top it all off, root privileges make Tordow v2.0 a real pain to remove from an infected device. In fact, the only way to exorcise the malware might be to flash the Android operating system.
Users don’t want to go through all that trouble. Understandably so.
That’s why they should maintain an anti-virus solution on their mobile devices that’s capable of detecting attacks like Tordow v2.0. They should also make sure they download their apps from only the official app marketplaces like Google Play Store and Apple App Store.
Doing so doesn’t guarantee a completely safe experience, but it will certainly lowers the chances of ending up with a nasty malware infection.


