The must-see movie of the moment is surely not “The Hobbit: Battle of the Five Armies”, “Unbroken” or even “Paddington”. No, the one movie that everyone is talking about is “The Interview”.
Following the devastating hack upon its computer systems by a hacking group which might (or might not) have the blessing and backing of North Korea, Sony Pictures flip-flopped as to whether the Seth Rogan comedy about the assassination of Kim Jung-un would have a Christmas Day release.
Eventually, the movie had a limited Christmas Day release in the States, much wider online availability for US internet users via sites like YouTube, and an even wider still copyright-infringing distribution via torrent sites.
But the computer security story surrounding “The Interview” doesn’t end there.

Researchers at McAfee – in a joint investigation with the Technische Universität Darmstadt and the Centre for Advanced Security Research Darmstadt (CASED), has identified that a threat campaign has been active in South Korea in the last few days, attempting to exploit the media frenzy surrounding “The Interview”‘s release.
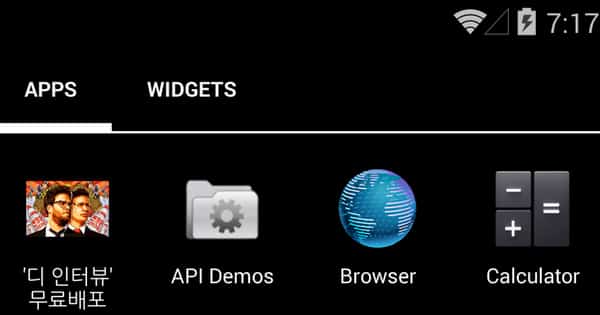
McAfee security expert Irfan Asrar tells me that a torrent making the rounds in South Korea, poses as an Android app to download the movie to mobile devices.
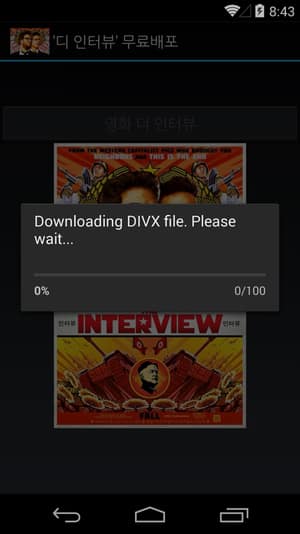
However, in truth, it contains an Android Trojan detected by McAfee products as Android/Badaccents.
Android/Badaccents claims to download a copy of “The Interview” but instead installs a two-stage banking Trojan onto victims’ devices.
The banking Trojan, which was hosted on Amazon Web Services, targets customers of a number of Korean banks, as well as one international bank (Citi Bank).
One aspect which will probably raise eyebrows, is that the malware code includes a routine to check the device’s manufacturing information. If it is set to either 삼지연 (Samjiyon) or 아리랑 (Arirang), smartphone manufacturers whose Android devices are sold in North Korea, the malware will not infect, and instead display a message that an attempt to connect to the server failed.

Asrar says that he does not currently believe the limiting of infections to non-North Korean made devices was politically motivated, but instead a commercial decision not to waste bandwidth on users who were outside the targeted region (as North Koreans were unlikely to be customers of the targeted banks).
The researchers uncovered that bank account data from infected Android devices was being relayed back to a Chinese mail server, and that approximately 20,000 devices appear to have been infected to date.
McAfee has notified Amazon Web Security of its findings, with a view to having the Amazon-hosted files removed to prevent further infections. Of course, it’s always possible that other web storage services could be used to host the malicious code in future – potentially using different disguises.
Hat-tip: Thanks to security researcher Irfan Asrar for the information he provided about this threat.
Update (31 December 2014): An Amazon Web Services spokesperson has been in touch, with the following comment:
We have a clear acceptable use policy and whenever we have received a complaint of misuse of the services, we have moved swiftly to strictly enforce it. The activity being reported is not running on AWS.
Note the Amazon statement’s careful wording. They say that the activity reported *is* not running on AWS. They don’t say *wasn’t* running on AWS.
Thanks to the security researchers for raising the alarm, and to Amazon for removing the offending content.



the best trick on the right time ! and a 20,000 Infected device is a nightmare !
btw! i would be highly appreciated if you could provide the ".APK" so i can do my research
best regards.
How easy is it to uninstall once someone knows about this malicious app. Or does McAfee have a write-up of this. Does it gain administrator privileges? Run on startup? Etc.
So how does Android/Badaccents actually work? Is it exploiting known flaws in the relevant banking apps, hijacking the Android network stack or keyboard input, or something else… ?