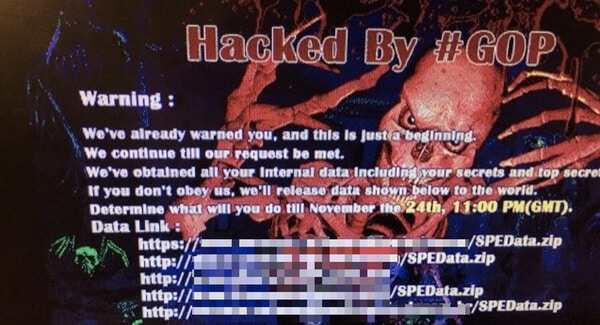
 There’s a new development in the ongoing story of the Sony Pictures hack and the alleged involvement of North Korea – supposedly angered by Kim Jong-Un assassination comedy, “The Interview”.
There’s a new development in the ongoing story of the Sony Pictures hack and the alleged involvement of North Korea – supposedly angered by Kim Jong-Un assassination comedy, “The Interview”.
The New York Times reports that the NSA has a secret foothold inside North Korea’s computer networks, and actually saw the first spear-phishing attacks against Sony Pictures in early September 2014.
According to the two unnamed American officials who spoke to the New York Times, and a newly disclosed NSA document published by Der Spiegel, the NSA has been able to spy on the internal workings of many of the computers used by North Korea’ hackers since 2010.
However, the report claims that the NSA failed to recognise the significance of the attack and did not warn Sony.
And there lies the obvious question – if the NSA were secretly spying so comprehensively on the networks used by North Korea’s hackers, how come they didn’t warn Sony Pictures?
And what does that say about the United States’s national security efforts – have other attacks against corporations gone unnoticed? Is it possible that attacks against more critical infrastructure in the States than a movie production house have similarly slipped past unnoticed?
Huh. I wonder how Sony Pictures feels about this… According to the reports, the attack was initiated by a bog-standard spear-phishing attack against a Sony network administrator, giving the hackers access to internal computer systems. It’s hardly rocket science or “unparalleled”…
If the claims are true, it would certainly help explain why the White House so quickly and definitively blamed North Korea for the attack – even in the apparent absence of convincing evidence.
But it doesn’t explain why in the earliest communications between the hackers and Sony Pictures, there was no mention of “The Interview” and the hackers’ demands were not for a movie to be withdrawn, but for Sony Pictures to stump up a ransom.

And it doesn’t explain why the crippling hack attack against Sony Pictures came across so *personal*, with a digitally-altered image of Sony Entertainment CEO Michael Lynton’s head, the release of private email exchanges between executives, and spreadsheets showing what aliases celebrities use when they book into hotels.
Are these latest claims plausible?
It certainly makes the White House’s blaming of North Korea for the Sony Pictures attack much more believable if we know that North Korea had been hacked itself by the United States.
But once again, it’s healthy to be skeptical – especially as those speaking to the media continue to do so anonymously, with no ability to question their motives for leaking information.
And, presumably, the cat is now out of the bag.
These news stories may take some of the heat off the States from some of those in the IT security world who were skeptical about the claims of North Korean involvement, but it also tips off North Korea that it may want to be a little more careful about its own computer security.
What’s curious is that before the United States was that it couldn’t tell us all the reasons it believed North Korea was responsible for the Sony hack without compromising “national security”.
So how comes this latest leak hasn’t compromised national security too?



From bottom top:
"… but it also tips off North Korea that it may want to be a little more careful about its own computer security."
Maybe we need to (that is, maybe we SHOULD) remind Sony of this too? I mean this is not the first time they came to such a huge security breach. Then again, it goes for everyone – users, organisations, corporations, and all types of devices as well as the media (wireless, wired, combination) and even the application layer (where applicable..that came too easily) like email, social networks… and if you want to go to the lower levels again, even key loggers (including the kind that are attached to keyboards) as well as social engineering (in person).
"Is it possible that attacks against more critical infrastructure in the States than a movie production house have similarly slipped past unnoticed?"
I'll take that as a rhetorical question. True to my nature, I'll answer it: absolutely yes.
As for the situation. It would be even more ironic if the compromised network in NK, was actually used as the starting point of the attack (if it 'did' come from NK). That is to say, if the NSA did break in to their network, what if they made a mistake and allowed someone else to launch the attack (maybe they unknowingly or knowingly opened a back door, perhaps to get in themselves ? one possibility).
In the end, it is all speculation. Which is one of the many reasons the accusations are so serious. But one could hardly blame NK (again, IF and it is a big IF) for it, after that.
In that light, I'll raise the obvious question that conspiracy theorists would love:
"If the NSA was in their network, did the NSA cause controversy to cause trouble for NK ? That is, did they attack Sony themselves ?"
"…a feint within a feint..within a feint…", etc.
This situation would not be surprising. In Vietnam of the 1960s, U.S. intelligence was aware that the North Vietnamese had replaced their first SAM missile site with wooden poles painted white (to look like SAM missiles). However, the U.S. didn't want the NV to know that we were aware of the fakery — so we sent aircraft in to bomb the wooden poles anyway…losing several pilots and multimillion-dollar aircraft in the process.
And there lies the obvious question – if the NSA were *secretly* spying so comprehensively on the networks used by North Korea’s hackers, how come they didn’t warn Sony Pictures?
And here lies the obvious answer – It was a 'secret'!
… Except you're ignoring context by a large margin. The point is not whether it was secret or not. The point is if they were monitoring NK (despite what might have been claimed there or anywhere else) then why did they not warn Sony? THAT is far more important and that is the point. So in summary you answered a question that wasn't asked (and I don't see how it could be asked aside from 'was it a secret or not ?' and that is a rather silly question to ask – it has more than one answer depending on who you ask and what they know/don't know and whether they are assuming/guessing/are responsible/etc, whether they've been misled, lied to, are lying, list goes on …i.e. it is asking useless nonsense that no sensible person would ask (and arguably no sensible person would try to answer)).
I see only one question about the disclosures that begs an answer: Why would the NSA disclose the fact that they had hacked North Korea if it's true? This would give away valuable information that they would naturally like to keep secret.
Why didn't they warn Sony? That's not why the NSA exists. Warning companies in other countries doesn't exactly fit their "mandate", to protect the U.S.
Did they want to attribute the Sony attack on North Korea? Someone higher up must have decided that the release of this information would make North Korea look bad, & that the risk to blowing their cyber cover would be worth it.
There is after all a "cold war" going on between NK & most of the Western World, so a propaganda opportunity is something valuable. I don't see it being valuable enough to hint that you've hacked their systems, but I'm not a politician, so I see things differently. ;^)
According to Jim Rogers (former partner of George Soros) who recently visited NK, it is experiencing a huge economic growth boom, & would be a good place to invest, if it were not illegal in all the countries that have agreed to sanction NK.
Perhaps, another reason to make them look bad. ;^)
My guess is that the NSA hackers had other back doors installed as backups (not uncommon), & that giving away their hacks did little harm to them. In fact, it could be used to reassure NK hackers that the ones they've found were the only ones.
So, this may well be the answer to the question above, why give away the fact that you've hacked their systems? It works for you, that's why (as usual;^)
They call them Never Say Anything for a reason :)
Seriously though, the NYT article is *entirely* based on a page grab from a secure forum page from 2007, part of the Snowden documents I believe, which states, at that time, they had stolen access details from SK who had hacked into NK, and bootstrapped access that way.
So, presumably if they *still* have access, then the FBI would have been able to pull it from the NSA databases after the fact, but not use that info directly; it would also call into question the timetable, as Norse are claiming the attack began months before the claims of the FBI, and the FBI have suggested that third parties "assisted" the NK attack – so possibly the initial attack wasn't NK at all, but NK bought access into Sony when the movie thing came up, from the original hackers – and if the NSA can bootstrap via SK, surely NK could bootstrap via GoP
Many people have suffered because a route to privileged information was deemed to be more valuable than risking its exposure by acting upon the information it can provide.
For example Enigma was cracked by Turing during WW2, but kept secret because governments continued to use it in the belief that it was secure, giving the UK many years of eavesdropping ability.
I heard somewhere that Churchill knew Pearl Harbour was to be bombed, but didn't inform the USA because he wanted them to join the war, and that would do it.
Of course, what really happens behind the scenes is very different to the reality carefully prepared for public consumption, and on that we can only speculate.
I don't get why people say this was to sophisticated to be nk – looking at the claimed entry point malware 61bf45be644e03bebd4fbf33c1c14be2 it really doesnt look that complicated, i cant even see any packing in the strings