
The SoakSoak botnet is compromising business websites so that they redirect visitors to the Neutrino exploit kit and CryptXXX ransomware.
Researchers at Invincea note it’s nothing personal for SoakSoak. Like most botnets, SoakSoak does not specifically select which websites to compromise. Instead it scans a large number of potential targets for weaknesses it can exploit.
As the researchers explain in a blog post:
“Websites are often compromised by botnets that scan websites for vulnerable software or application plugins. The most popular and vulnerable slideshow plugin is Revslider according to Sucuri’s 1Q 2016 report. Once a botnet identifies a vulnerable server, it compromises it by adding redirection scripts so that visitors are sent to an alternate site hosting an exploit kit to deliver the ransomware to the unwitting victim. The infographic below shows the process.”

SoakSoak has been around for a couple of years now. Named after the Russian domain from which it originally launched, the botnet made headlines in December 2014 for a campaign targeting the WordPress RevSlider slideshow plugin.
As a result of those attacks, Google blocked 100,000 websites hosted on WordPress, including 11,000 sites just in one day.
The botnet is once again leveraging RevSlider and other vulnerable plugins to compromise self-hosted WordPress websites, although the affected version of the former is not known as of this writing.
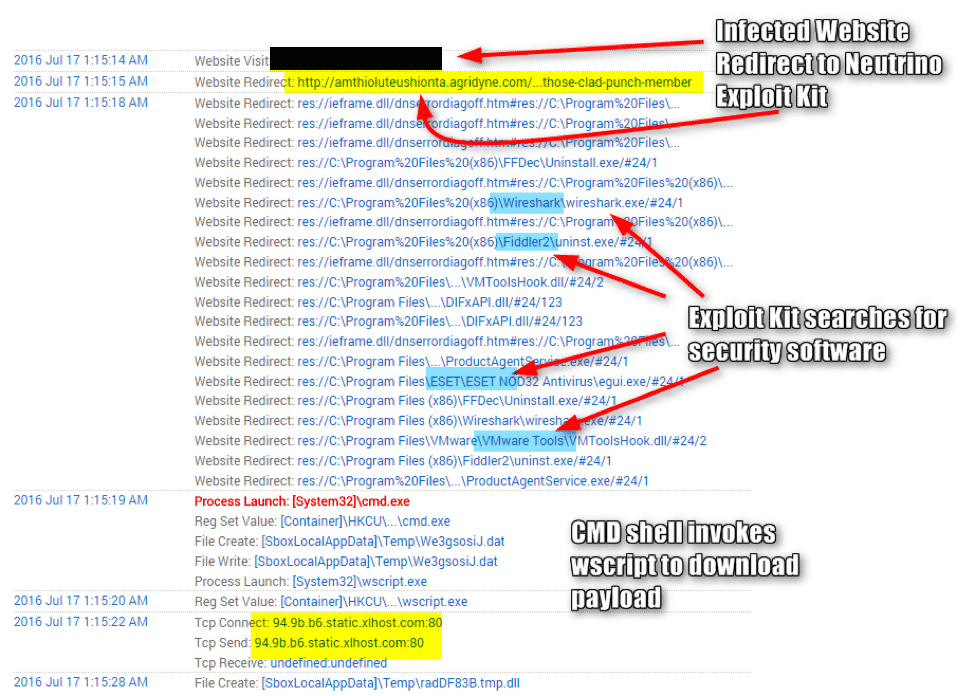
The infection process is always the same in these attacks: redirection to a landing page for the Neutrino exploit kit, and checks to determine whether it’s “safe” to download CryptXXX onto the victim’s computer.
Invincea’s research team provides more information:
“Once a victim is redirected to the Neutrino Exploit Kit, the endpoint is scanned to check if it is using any security software such as VMWare, Wireshark, ESET, Fiddler or a Flash player debugging utility. If those programs are not present on the victim host the Command Shell is opened and the windows utility of Wscript is accessed to download the ransomware payload from a Command and Control server.”
This is not the first time Neutrino and CryptXXX have teamed up to ruin users’ day. In June, attackers injected a popular anime site with code to redirect unsuspecting visitors to the terrible twosome.
An up-to-date anti-virus solution can help protect users against this campaign. Website operators can also stem the tide of SoakSoak attacks by regularly updating their websites and plugins, monitoring their access logs for suspicious activity, and making use of WordPress security plugins and/or anti-ransomware tools.


