
Following the report published earlier this month by G Data into the “Uroburos” spyware, which heavily hinted the malware could have been written by Russian intelligence, UK-based defence contractor BAE Systems has entered the fray with all guns blazing.
In a technical paper entitled “Snake campaign & cyber espionage toolkit”, BAE says that it has uncovered details of a complex internet espionage campaign of which the Uroburos rootkit is only one part, and that has been in operation since at least 2005.
BAE says it has collected over 100 unique files related to the Snake espionage toolkit as they were submitted to online malware analysis websites like VirusTotal, and that in many cases it has been able to determine the country from where the samples were submitted.
And which country appears to be submitting the most Snake-related malware samples? Ukraine.
According to BAE, there have been at least 22 attacks launched against Ukrainian computer systems since January 2013 and a significant uptick in Snake-related malware submissions from the country this year.
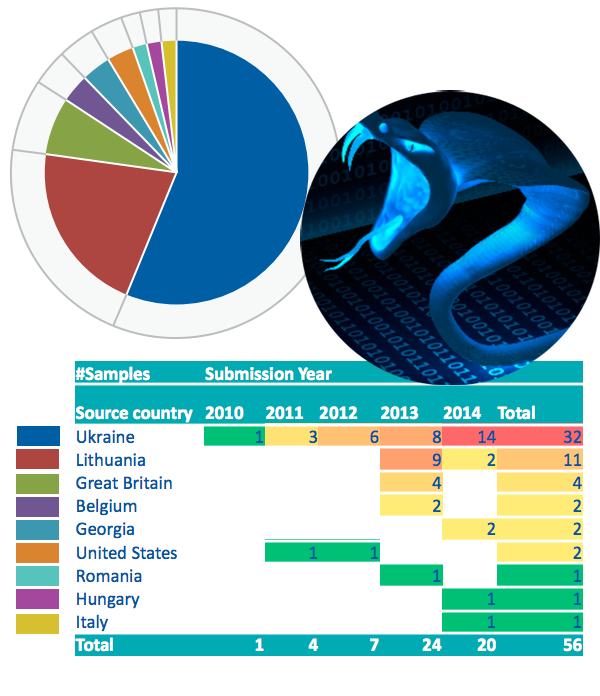
Meanwhile, the malware was reported at least eight times in Ukraine, nine times in Lithuania, four times in Britain, and twice each in Georgia and the United States.
Interestingly, no-one appears to be reporting the malware to analysis sites from Russia. Hmm.
 Does this prove Russian involvement in the creation and usage of this malware?
Does this prove Russian involvement in the creation and usage of this malware?
No. As I’ve mentioned before, it is frustratingly extremely difficult to attribute beyond doubt a particular country or state-sponsored agency to a malware attack.
BAE cites some circumstantial evidence that the Snake attacks may have originated in Russia, and draws connections between it and the Agent.BTZ worm which in 2008 caused the US Army to ban the use of USB and removable media devices after it suffered a breach.
But despite the lack of a smoking gun, the report is definitely interesting – particularly in the context of rising tensions between Russia and Ukraine in the Crimea.
BAE is certain of one thing. The threat to organisations with sensitive information on their network is real.
We view this threat to be a permanent feature of the landscape. Whether they dismantle this toolset and start from scratch, or continue using tools which have been exposed, remains to be seen. For their targets though the considerable challenge of keeping secrets safe on sensitive networks will certainly continue for years to come.
Read more about BAE Systems investigation into “Snake” by downloading the PDF of their report.


