 Security experts at G Data, the German anti-virus firm, have discovered a “very complex and sophisticated piece of malware, designed to steal confidential data”.
Security experts at G Data, the German anti-virus firm, have discovered a “very complex and sophisticated piece of malware, designed to steal confidential data”.
So far that sounds reasonably interesting, but (frankly) not that extraordinary in these days of targeted attacks against organisations.
But what makes the Uroburos rootkit stand out from the crowd is that G Data’s detailed report into the malware reveals that their researchers believe it to have been created by a country’s intelligence agency, and drops some heavy hints that Russia are to blame.
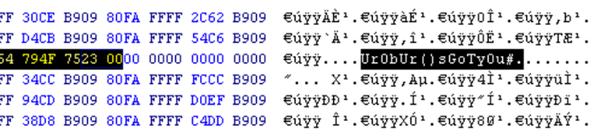
The Uroburos rootkit takes its name from a mythical serpent or dragon that ate its own tail, and a sequence of characters concealed deep within the malware’s code: Ur0bUr()sGotyOu#
Uroburos steals files from infected computers and captures network traffic, and has some sophisticated tricks up its sleeve to help hackers exfiltrate information from targeted organisations.
For instance, it’s designed to work in peer-to-peer mode, with infected PCs communicating amongst each other. The remote attackers only need to command one infected computer which has an internet connection, in order to infect, control and steal from other infected computers on the network which may not have net access.
Another interesting feature of the malware is that it uses two virtual file systems to disguise its activities from observers:
The Uroburos rootkit uses two virtual file systems – one NTFS file system and one FAT file system. They are stored locally, on the infected machine. This means that the victim’s computer contains an encrypted file, which, in reality, hosts another file system.
The virtual file systems are used as a work space by the attackers. They can store third party tools, post-exploitation tools, temporary files and binary output. The virtual file systems can be accessed through the devices DeviceRawDisk1 and DeviceRawDisk2 and the volume \.Hd1 and \.Hd2.
According to G Data, the Uroburos malware’s technical complexity suggests connections to intelligence agencies:
The development of a framework like Uroburos is a huge investment. The development team behind this malware obviously comprises highly skilled computer experts, as you can infer from the structure and the advanced design of the rootkit. We believe that the team behind Uroburos has continued working on even more advanced variants, which are still to be discovered.
…
Due to many technical details (file name, encryption keys, behavior and more details mentioned in this report), we assume that the group behind Uroburos is the same group that performed a cyberattack against the United States of America in 2008 with a malware called Agent.BTZ. Uroburos checks for the presence of Agent.BTZ and remains inactive if it is installed. It appears that the authors of Uroburos speak Russian (the language appears in a sample), which corroborates the relation to Agent.BTZ. Furthermore, according to public newspaper articles, this fact, the usage of Russian, also applied for the authors of Agent.BTZ.
In 2008, the spread of Agent.BTZ worm resulted in the US Army banning the use of USB and removable media devices. At the time it was claimed that the Agent.BTZ attack was initiated after an infected USB stick was deliberately “lost” in the US Department of Defense’s car park.
All of this adds up, in the opinion of G Data’s report, to one conclusion – whoever was responsible for creating Uroburos wasn’t the common-or-garden malware author.
According to all indications we gathered from the malware analyses and the research, we are sure of the fact that attacks carried out with Uroburos are not targeting John Doe but high profile enterprises, nation states, intelligence agencies and similar targets.
Of course, we’ve been here before. Not a month goes by without someone accusing country X or country Y of being responsible for a malware attack.
As always, we need to be careful about jumping to conclusions.
 Although it’s easy to piece together pieces of “evidence” from malware code such as snippets of language, or resources which have been compiled with certain language settings that *isn’t* necessarily proof beyond reasonable doubt that citizens of a particular country were responsible, let alone that the attack has the backing of the country’s government.
Although it’s easy to piece together pieces of “evidence” from malware code such as snippets of language, or resources which have been compiled with certain language settings that *isn’t* necessarily proof beyond reasonable doubt that citizens of a particular country were responsible, let alone that the attack has the backing of the country’s government.
The truth is that attribution when it comes to malware attacks is extremely difficult.
At the same time, we would be naive to think that many countries around the world are not taking advantage of malware, vulnerabilities and hacks to spy upon other nations.
Meanwhile, details are still frustratingly missing. No light has been shined on how Uroburos might infect victim computers (although USB infection and targeted email attacks seem plausible), or who the victims might have been, or what data might have been stolen.
What’s perhaps most embarrassing for all concerned is G Data’s claim that one of the oldest drivers identified in the Uroburos rootkit was compiled in 2011, meaning that it has gone undetected by everyone for at least three years.
You can learn more about Uroburos in G Data’s report on the malware.



Thanks for the information about this gruesome piece of malware, but is there any clue yet how to determine an infection?
I read trough the article of G Data, but all I was able to extract was that it really well covers up its activities, and that you wont find any obvious entries like Ultra3 in the registry whatsoever.
Any clues how else to find out?
Big thanksies in advance,
wondrous
The date of the driver is not necessarily related to the date of the campaign. It sounds like they jumped to another conclusion.
So this thing has roots going back to 2011, and A/V vendors still don't detect it. What seems diabolical may be allowed by mere ineptitude.