Carole’s in her sick bed, which leaves Graham in charge of the good ship “Smashing Security” as it navigates the choppy seas of credential stuffing and avoids the swirling waters of apps being sloppy with sensitive information.
Find out more in this latest edition of the “Smashing Security” podcast, hosted by Graham Cluley with special guest BJ Mendelson.
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
My name's Graham Cluley.
So maybe I'll let her fill in the gaps if she returns to the show next week and if she's in a healthy way. I hope she gets better, obviously. Yeah, no, we—
These are things that, you know, people listening to the show— if you don't have a YubiKey, I'd be shocked, right? Or some kind of hardware authentication token.
But there is a severe knowledge gap, particularly in the United States, about securing your data and how to protect it and how to keep private.
So we wanted to make it as stupid and as simple as possible so that anybody listening could do it. Including me.
But before we kick off, let's thank this week's sponsors, Bitwarden, ManageEngine, and Digicert. Their support helps us give you folks the show for free.
Now, coming up on today's show, this is the bit Carole normally does. Coming up on today's show, Graham, what have you got? Oh, thank you for asking, Kroll.
I'm going to be talking about a police raid which could have gone very wrong.
And being a police officer, it sort of has that dichotomy. Just here in the United States, there seem to be more on the bad side than the good side.
It involved over 64 agencies, an operation called Protect the Innocent, and it was specifically targeting people who were involved in possession, distribution, creation of child sexual abuse material.
So obviously we want those bad guys rounded up. Right.
I think I saw that in theaters? What phase of the Marvel Cinematic Universe is that?
I mean, it must be difficult for the police to come up with new code names all the time for their operations.
I don't know how they— I mean, we have a hard enough time naming our hurricanes, don't we?
It's hard enough, as we found today, getting 3 people to show up for the podcast, let alone people from different law enforcement agencies and police departments, getting everyone lined up.
And this is what we're going to do, and this is when we're going to knock on the door, and, you know, make sure that we all do it at the right time and we've got all the information we need.
So it's no surprise that the authorities like to use tech, they like to use technology to share information before a raid and helps coordinate.
They used a free trial of an app. Were they not prepared to pay the $0.99 in the App Store? I don't know. But anyway, they used a free trial of an app called Sweep Wizard.
So yes, there are wizards. And sorry, not— well, obviously there are wizards. There are.
I doubt they sell for 99 cents, but well, maybe. Maybe you have to buy a subscription. I don't know. Depending on how many agencies are involved.
Anyway, the raids last September were a big success. They arrested hundreds of people.
Including over 100 for possession, distribution, and manufacture of child sexual abuse material. They contacted over 500 targets. You know, there was a lot which they did with this.
And so, you know, that's all good news, right? These people have been rounded up. They're going to be questioned.
Hopefully, if they're guilty, they'll be brought to justice, blah, blah, blah, blah, blah.
That's maybe when the real wizards actually get involved with Sweep Wizard.
All you had to do to find out information about the raid was simply visit a specific URL on the Sweep Wizard website. It didn't authenticate. It didn't ask for a password.
Nothing at all. Oh, wow.
And also it would obviously cast suspicion on people who hadn't yet been convicted of anything, because anyone could go there and say, oh, Bob down the road, he's obviously a wrong'un, because he's been rounded up by the cops.
So the Sweep Wizard app is built by a company called, unpretentiously, Odin Intelligence.
Now, Sweep Wizard didn't just leak information about the Protect the Innocent raid, which happened last September.
It had also been leaking confidential details from about 200 other raids that dozens of departments have organized over multiple years.
If you went to these URLs, you could find out details about the police officers, hundreds of them, thousands of suspects, the locations of suspects' homes, the time and location of raids, their contact information, sometimes even the suspects' Social Security numbers.
So as if someone wasn't having a bad enough day that they were being raided by the cops, you could also defraud them in other ways.
In some instances, it included their height, their weight, their eye color, and even whether they were homeless or not.
So we would think, right, that they were pretty sure on who they were targeting in this, we think.
I'm sure some of them, they were pretty certain these are people who we've got lots of evidence on, but others may simply have been, well, we think he seems to be associated with these guys.
Maybe we should bring him in and have a little bit of a chat and see if there's more to come. But all of this information wasn't being protected.
It was being understandably exchanged with the other agencies. It was just sitting on a cloud drive somewhere.
That sort of reminds me of this, right? Where it's well, I guess there's 5,700 suspects. We're not really sure, but you know, maybe.
There was no authentication check, which meant that anyone could go to this URL and find all this information.
Now, the police knew nothing about this problem until Wired magazine contacted them. And obviously the cops said they were concerned about this revelation.
And they said specifically, "We don't want people to know when and if we're coming to get them." Which is—
Maybe if they're in a car chase, they would.
I think the people we should be complaining about are Odin Intelligence, who appear to be as incompetent as their fictional existence on Archer.
So they declined to be interviewed by Wired, but they said in a statement, and this reassured me a great deal actually when they said this, I thought, oh, well, that's fair enough then.
They said that they take security very seriously, unquote. And I thought, oh, finally, a company which says they take security very seriously. That's all right then. That's all fixed.
They also said that they'd been unable to reproduce the problem. Which Wired had reported on. But of course, their website's no longer accessible.
Their app has been removed from the Google Play Store and the Apple App Store.
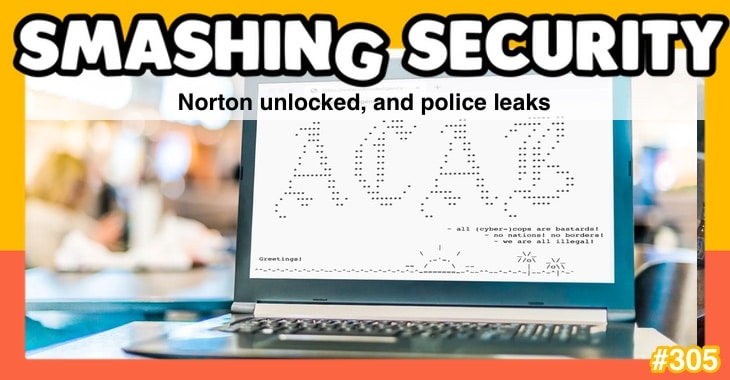
And it actually turns out that Odin Intelligence have got other problems because just a day or two after this Wired story came out, its website was defaced with some rather abusive ASCII art.
So some hackers got in. And they said that all cybercops are bastards. That's a bit mean of them, I think.
But obviously, Odin Intelligence aren't being that smart when it comes to their own security.
I know he's American now, but never mind.
And so he just looks at me and goes, "You're going to Wales?" I'm like, "Yes," he's like, "All right, you're fine, go ahead." BJ, what story have you got for us this week?
I don't know if they were big in the UK, but in the early 2000s and even the early '10s, I guess is what we're calling the previous decade, there was a company called LifeLock.
So that's the company that we're revisiting in today's story, except in that time, I guess through a complicated series of purchases and ownership changes, it's now called Norton LifeLock.
Yeah, and so Norton, for reasons known only to them and God, if you choose to believe that God exists, they have decided to continue offering this LifeLock software.
And so there was a pretty serious security breach that just went down. We still don't know how big and how complicated this is.
It's sort of the LastPass thing, where they did their best to kind of obscure how bad the situation was.
But what was funny to me about this story is that the same service they sell to, you know, promoting and enabling two-factor authentication is the same service that could have stopped this attack in the first place, right?
There was a credential stuffing attack.
You know, people were basically just copying and pasting information that had been previously leaked, and Norton LifeLock, wouldn't you know it, were not exercising good security hygiene, and using strong passwords.
And so someone had reused the password that had been previously leaked, and all hell broke loose. And so now they are dealing with the situation.
And here's the kicker to it, the solution that the company is offering, you'll never guess what it is.
It's usually reusing passwords.
And that seems to be what happened in the Norton LifeLock situation is that, as you said, a whole bunch of usernames and passwords were stolen from who knows where.
Some other site, not from Norton LifeLock, and then they were used to try and unlock accounts at Norton LifeLock.
And for those users who hadn't enabled multifactor authentication, obviously those credentials were enough to get them in.
So my question is, why wasn't Norton LifeLock enabling two-factor authentication by default?
Right, surely that would have— if Norton LifeLock is storing really sensitive information, including people's passwords, then you need an additional level of protection than just a dumb password to protect that account.
Yeah, but then I look at something like Norton, who should know better, right, and has been around forever I'm convinced that it's just at this point they're cashing checks and they're not really taking this stuff seriously.
But of course, it's no longer Peter Norton with his crossed arms who's running the company.
That brand name has been sold on and on and on from different companies and different organizations.
And it's now part of this big security conglomerate, the overarching parent company is called GenDigital, and they also own Avast and Avira, I think, and CCleaner as well as Norton.
You know, there may be some very smart people working there, but there's probably resistance from inside maybe the product team or the marketing team saying, well, yes, of course it would make sense to make two-factor authentication mandatory.
But it's going to really piss off our customers because it's going to be a nuisance. They're going to say, oh, well, why do I have to type this 6-digit number in?
Or why do I have to do this? It's suddenly become more difficult to use. And there's always that battle, isn't there, between ease of use and security.
And it feels like in this case, the people arguing for it should be easier won to the detriment of securing those accounts.
This is the service you sell and for you to not be using it tells me not to use your product. I can't think of a more clear, this is true of any tech company, right?
If they're not using their own product in-house, you should avoid them.
I mean, I think this isn't as catastrophic as what we saw at LastPass.
In the case of Norton LifeLock, it does feel like maybe they could have gone a few extra steps to better protect their customer base from what was, as you said, a credential stuffing attack.
There was someone else who got hacked, not them, which led to this happening. Yes.
And these are credentials being flung at their logging pages, but they could have done rate limiting, they could have looked for suspicious behavior.
You know, when you're protecting passwords, you've really got to go the extra mile, I think.
They just want to know that they're secure.
And so it's to me partly the responsibility of these companies to take that extra step for people because I think that privacy and security is complicated. Right?
And so if I'm paying for a solution like Norton LifeLock, then my expectation is that you're going to kind of take that complexity out of my life and into yours.
And so I'm always disappointed because I just feel like, you know, until we get to the point where my generation and younger are taking privacy and security a bit more seriously than we do, that extra layer of protection just needs to come from the companies.
And clearly in this case, it wasn't there.
So there's probably a lot of Smashing Security listeners out there who might be concerned after hearing about the data breach which recently occurred at LastPass.
Now, that allowed hackers to steal customers' password vaults, and unfortunately there were parts of those password vaults which were astonishingly unencrypted.
There's no doubt a lot of questions users are going to ask LastPass about how that could have happened and why some of that data was left in that insecure state.
But one password manager that isn't making that mistake is our sponsor Bitwarden.
Customers of Bitwarden know that their vaults are entirely end-to-end encrypted with zero-knowledge encryption, including, unlike LastPass, the URLs for the websites which you have saved passwords for.
You can learn more about that in the Bitwarden Help Center and at bitwarden.com/privacy.
And if you happen to be looking to switch password managers right now, well, Bitwarden makes it easy.
They support importing from lots of other solutions, and there's even a LastPass migration guide available. Learn more at bitwarden.com/migrate. That's bitwarden.com/migrate.
And stay safe. You've probably heard that organizations are experiencing increased pressure to manage digital trust at scale across multiple functions in IT.
The problem is many have a lack of centralized visibility and control, and this is why companies are looking for a unified digital trust strategy.
Enter DigiCert Trust Lifecycle Manager. The Trust Lifecycle Manager from DigiCert sets a new bar for unified management of digital trust.
DigiCert Trust Lifecycle Manager is a full-stack solution that unifies CA-agnostic certificate management, private PKI services, and public trust issuance for seamless digital trust infrastructure.
Find out how you can implement a full-stack solution in a single pane of glass that offers superior performance, handling, and automation with a single vendor accountability.
All you gotta do is visit smashingsecurity.com/digicert. That's smashingsecurity.com/digicert. And thanks to DigiCert for sponsoring the show. Hacks are happening all the time.
Databases are being breached. And as we know, 80% of all breaches happen when passwords are compromised, stolen, or abused.
An efficient way to combat threats is using a Privileged Access Management solution, or PAM.
An enterprise PAM tool like ManageEngine PAM360 offers a holistic picture of all the privileged devices, users, and credentials in your IT infrastructure.
ManageEngine comes from Zoho, which offers IT management solutions to over 280,000 enterprises around the world, so you're in safe hands.
Well, ManageEngine PAM360, fully functional privileged access management suite, easy to adopt and implement.
From managing and governing access to all your enterprise resources to automating the access management lifecycle in your organization, PAM360 does it all.
And they offer great support for businesses looking to do this without making a dent in your IT budget.
Learn more for yourself about ManageEngine PAM360 at smashingsecurity.com/pam360. That's smashingsecurity.com/pam360. And welcome back.
Can you join us on our favorite part of the show? The part of the show that we like to call Pick of the Week.
It doesn't have to be security-related necessarily.
He wants you to use the official Twitter app because that is festooned with ads and its algorithm keeps on recommending that you follow vaccine deniers and conspiracy theorists.
But it was seen as sort of the liberal social media place.
He's thinking the more people I get to use the official app, the more people will eyeball the ads which we're making money from.
And the biggest users of Twitter are, I would suspect, people who aren't using the official Twitter app. Yes, that's right.
They've gone to the effort of finding a better app to use Twitter. They're making the content which people want to read on Twitter.
So stopping all of those people suddenly overnight from accessing Twitter, not a good idea.
I was part of that initial vanguard and there has always been TweetDeck and services that people have preferred to use over the main app.
It's funny 'cause I always thought it'd be a matter of time before they clamped down on it. It's just interesting that it had to happen under this guy of all people.
What he should have done is this Twitter Blue subscription thing he's trying to get us to pay for, you know, a way of paying $9 a month to prove that we're idiotic enough to care about a blue little badge.
If he'd said one of the benefits is you will be able to use third-party apps— Yes. I might have even actually been prepared to sign up. Maybe, maybe.
You know, the other thing is that— and I'm just putting my marketing hat on for a second— you know, Twitter ads have always been terrible.
I can think of maybe one or two instances since 2007 where I can point to and say, wow, that did really well, that was a Twitter ad campaign.
But now not only are you putting money into a service that doesn't really perform well, but you're now actively saying I support Nazis by running ads.
So even if Twitter Blue allowed you that third-party access, I would still be a little hesitant to give this guy my money, you know?
The reason why my Pick of the Week is not Elon Musk being an idiot, my Pick of the Week is an app called Spring.
Spring is a highly customizable Twitter app, third party, which is available for iPhone, iPad, and the Apple Mac, and it hasn't been shut down yet.
You don't get the ads, you don't get the promoted posts, you don't get the ghastliness of recommendations as to who to follow, which you really don't want.
But this app is like, oh, if only the official Twitter app were like this, it's really good. And they've also produced one for Mastodon as well, so that's in beta at the moment.
So I'm on Mastodon. I'm a big fan. I like Mastodon. I like the idea of it, and it's working well.
I feel like that would have solved 90% of the onboarding problems for them. But yeah, I've enjoyed it so far. Do you like it?
And I have switched occasionally from instance to instance because, you know, frankly, the one I was on just got so clogged down and slow when there was this huge migration of people to Mastodon from Twitter when Elon Musk took over Twitter.
So I have changed from time to time, but now I'm more active on Mastodon than I am on Twitter, and I find it more interesting and more useful and just a nicer conversation.
And Mastodon, so far anyway, I feel like if I post something, I get much more thoughtful responses.
But yeah, so far Mastodon, it doesn't seem to have that problem yet.
If you do become a customer of Spring, so I paid them, I don't know, $9 or whatever it was, then you can also get an early access to Mona, their app for Mastodon, which looks identical, works brilliantly so far.
So I'm really impressed, and that is my pick of the week. So BJ, what's your pick of the week?
It's this goofy little gangster show with Sylvester Stallone, and anything with him when he's not punching people in the face tends to be bad, right?
You can track good Sylvester Stallone content based on how often he punches someone in the face.
In this, he knocks someone right down in the first episode. It's terrific. So you know you're in for a good time. And so, you know, I'm always looking for these little escapes.
The juxtaposition of the American West with this old-school gangster who looks like he rolled out of a 1980s mobster flick is just terrific.
They don't know what to do with him. So basically on a lark, just to get rid of him, they're like, "Why don't you go out to Tulsa?" It's like, "What?
So Oklahoma?" And so he goes and you have this character who does not belong there, is right out of Brooklyn in the 1980s interacting with the things you would come to expect with Oklahoma.
And just the juxtaposition of it is very funny, it's very entertaining, and the characters are terrific. Gilfoyle from— what was that called on HBO? Oh, Silicon Valley.
He's also in there and there's actually a really nice tie all back together to the show.
In the season finale, he makes a reference to most hacks occur because of poor security hygiene.
And I thought that was really nice and really great to hear in a TV show because it's just a really smart observation about security in general.
But I can't say enough good things about it. If you're looking for a little bit of an escape, if you don't have access to it, use a VPN to access.
I don't know what the global restrictions are, which to me is stupid. This is one planet, let's all enjoy our content together.
But if you can't access it, please use a VPN to go and check it out.
Hopefully Carole will be back next week, but really appreciate you stepping in. It's terrific.
I'm sure lots of our listeners would love to hear more about Stupid Sexy Privacy, your podcast, and the other things which you're up to, what's the best way for folks to do that?
So I just send people to Stupid Sexy Privacy.
It's a 24-episode miniseries, which is why we gladly promote Smashing Security throughout the show, because our time on the topic will end with episode before, but we always prefer people come and listen to this show and listen to yourself.
But yeah, as I said, it's just we want to make this as simple as possible when it comes to privacy because so much of the discussions on a high intellectual level.
We wanted to bring it down into the dirt, where everyone could enjoy it.
The easiest way to find it is go to smashingsecurity.com/mastodon and that'll take you straight there. And you can also look up the Smashing Security subreddit as well.
And don't forget to ensure you never miss another episode. Follow Smashing Security in your favorite podcast apps such as Apple Podcasts, Spotify, and Google Podcasts.
Thanks as well to our episode sponsors, Bitwarden, DigiCert, and ManageEngine PAM360. And to our lovely supporters on Patreon and Apple Podcasts as well.
Thanks to them, this show is free. For episode show notes, sponsorship information, guest lists, and much, much more, check out smashingsecurity.com.
Until next time, cheerio, bye-bye, farewell, toodle-oo, pip-pip.
Host:
Graham Cluley:
Guest:
BJ Mendelson – @bjmendelson
Episode links:
- Operation Protect the Innocent – LA Police Department.
- A Police App Exposed Secret Details About Raids and Suspects – Wired.
- ODIN Intelligence website is defaced as hackers claim breach – TechCrunch.
- Norton LifeLock says thousands of customer accounts breached – TechCrunch.
- Ugh! Norton LifeLock password manager accounts accessed by hackers – Graham Cluley.
- Reports: Twitter’s sudden third-party client lockouts were intentional – Ars Technica.
- Spring app – Twitter.
- Spring app – Mac App Store.
- Mona app – Mastodon.
- Tulsa King trailer – YouTube.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Bitwarden – Bitwarden vaults are end-to-end encrypted with zero-knowledge encryption, including, the URLs for the websites you have accounts for. Migrate to Bitwarden for a more secure password manager.
- ManageEngine PAM360 – A fully functional privileged access management suite that offers a holistic picture of all the privileged devices, users, and credentials in the IT infrastructure. From managing and governing access to all your enterprise resources to automating the access management life cycle in your organization, PAM360 does it all.
- DigiCert – DigiCert’s Trust Lifecycle Manager sets a new bar for unified management of digital trust.
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a supporter via Patreon or Apple Podcasts for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky at @smashingsecurity.com, or on Mastodon, on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.




