Booking.com got hacked five years ago, and didn’t tell its customers… but now we know who might have been behind it. Bossware rears its ugly head again in the workplace, spying on employees. And did you receive a warning email from the FBI?
All this and much more is discussed in the latest edition of the award-winning “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by Brian Klaas of the “Power Corrupts” podcast.
Plus we have a featured interview with Perimeter 81 co-founder and CEO Amit Bareket.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
He's a journalist and he dresses up as various things to do undercover journalism, to expose people. So he once dressed up like a rock, which I absolutely love.
It's like this sandstone. Not like the rock, not like Dwayne Johnson.
Like literally a piece of sandstone that has two eye holes in it. It's hilarious, right?
Smashing Security, episode 252. Hotel Hacks, Workplace Spies and the FBI. With Carole Theriault and Graham Cluley. Hello, hello and welcome to Smashing Security, episode 252. My name's Graham Cluley. And I'm Carole Theriault. And, Carole, we are joined this week by a returning guest. It's Brian Klaas of the Power Corrupts podcast. Hello, Brian.
Hello. The very wonderful Power Corrupts podcast. I'm on episode five at the moment of season two. I love it, love it, love it, Brian.
Oh, thank you so much. That's very nice of you. Glad to have you in my ranks of listeners.
Well, I am. I'm a big cheerleader for it. But it's not just a podcast you've got up your sleeve, is it? You've also got a brand new book out.
I do, yes, indeed. Just came out. It's called Corruptible, Who Gets Power and How It Changes Us. So I give you the very brief pitch of it. Go on, yes, please. Okay. So basically, I studied dictators and authoritarian leaders mostly in my career. And I started at one point to think, wait a minute, I've recognized these people who I've met in palaces, actually in mid-level management and homeowners associations. I think we all have this experience of the dictatorial personality. So I sort of started to think, is the name of my podcast actually true? Is it actually the case that power corrupts? And the book draws on 500 interviews that I did with all sorts of awful people around the world. And then also brings in neuroscience, psychology, evolutionary biology, political science, all sorts of studies. And it completely flipped my view of power. And so it was a fascinating project, and I hope people will check it out. Are you power hungry now? Did it rub off on you? You know, I don't think so. But I've managed to squeak in a lot of the interviews and fly around before the pandemic struck. One of the ones I was going to do that got scratched because it was going to happen in April of 2020 was I was going to get my brain scanned to see if there was any traces of psychopathy inside there. Wow. Being a psychopath. Because they can actually look at it. So I was curious and it didn't happen. But I think I'm on the right side of that divide, hopefully. Yeah, well, I'm buying this book for my dad for Christmas. So there you go.
So that's happening. If I can get a signed copy, let's talk later. What does it tell you about him? Exactly. Well, thanks to this week's sponsors, 1Password, Perimeter81, and Qualys. It's their support that helps us give you this show for free. Now, coming up on today's show, Graham, what do you got?
Well, I'm going to be returning to an old data breach that you may not have heard of.
Ooh, and what about you, Brian?
I'm going to talk about workplace surveillance and how companies are spying on people without their knowledge.
And I am going to be talking about an FBI snafu. Plus, we have a featured interview with Amit Barakat. He's the CEO and co-founder of Perimeter 81, an industry-leading SaaS security platform. So all this and much more coming up on this episode of Smashing Security.
Brian, you were just telling me that you interviewed 500 horrible people, you said.
I did, yes, indeed.
You say you've interviewed 500 horrible people. Does that mean if someone gets a request from you that you want to interview them, you've kind of tipped them off in advance? They may be rather vile.
Well, I will say that some of them were actually really lovely people. Most of them had no business being in power, but there were some exceptions.
Well, your travels, they must have taken you all around the world. Moscow, Berlin, Paris, London, Tokyo, Slough, you know, some of the most glamorous places on the planet. Beloved by the jet set and glitterati. You must have loved checking into luxurious hotels, hot and cold running water, playing around with the trouser press. Wasn't it great filling yourself up to the neck with complimentary room service? Yes, Carole, you like to stuff yourself, don't you, with a macaroon if you're on holiday or traveling?
A macaron, please. Right. Say it properly. Macaroon's a completely different thing.
Well, maybe, maybe when you've been traveling around, maybe you've booked your stay via a website like Booking.com. You heard of Booking.com, you too?
Yes. Of course. And I have booked via Booking.com. I have too because they allow you to cancel last minute.
Ah, okay. Well, one of the world's leading online travel companies, it's where you can book flights, hotel stays, car rentals. What possible reason would someone want to hack Booking.com? Any theories? Why would you want to hack Booking.com?
Steal data, put the ransomware on their butts. Right, yeah. Steal payment details. Yeah, yeah. I'm trying to be a little bit more imaginative. I thought you meant you'd, you know, screw around with the pictures and put little cockroaches in them.
Oh, you could. Pictures going across the bed. If you managed to hack the site or hack accounts, maybe you could do that.
Some sort of power hungry bed and breakfast kingpin to do this.
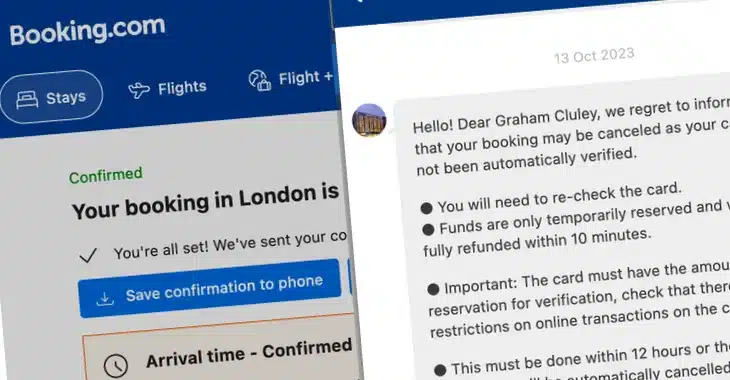
That's what I aspire to be. Yes, that sort of power hungry. Now, that wouldn't have been your motivation if you were the hacker who is said to have broken into Booking.com systems in 2016. Yes, I am going back five years, actually to early 2016, so nearly six years. I like to keep things topical.
It's OK. Short-term memory goes away as you get older, Graham. It makes sense you have to go back to the old days.
Well, this hacker who broke into Booking.com's servers, he stole details of thousands of hotel reservations in countries in the Middle East. And Booking.com's IT security team realised they had a serious problem, and they began to investigate the breach alongside the Dutch intelligence service. I think Booking.com is one of those companies. I think it was founded in the Netherlands, but is also half American. So it's sort of a Dutch company. And they determined that the culprit, they did lots of investigation with the Dutch intelligence service, and they determined that the culprit was a hacker called Andrew.
Oh, God, Andrew. Not that useful, really.
It instantly made me think of a certain Andrew who's rather famous here in Blighty, famous for not sweating very much but enjoying the Pizza Express facilities. But not him as far as I know. Now, do you remember reading the news stories about Booking.com at the time back in 2016? No. No, you don't, do you?
Well, no, but I wouldn't remember. I don't even remember what story I did last week. No, you're probably too addled. You don't remember anything. They were dissuaded? By whom?
Yeah. Who could possibly have a reason to want it to be hushed up and to withhold details of the hack from thousands of their victims?
The board. The board. Investors.
Well, yeah, exactly. The bosses. The bosses ultimately made the decision. And the argument that's been given is that Booking.com checked with its London-based lawyers and was told that it was not legally required to tell the authorities or individuals affected because, quote, no sensitive or financial information was accessed. And so they didn't.
So sensitive? So no names? Names were taken. Email?
Some details, yeah. And that's where people were staying as well. But no sensitive. This is before GDPR came into force. And according to Booking.com, it abided by all the laws and they were not required. They could quite happily keep quiet. Now, of course, some people knew about this hack but weren't very happy about this plan not to tell anyone, which included the IT experts who'd actually investigated, the people who actually worked inside Booking.com. But under privacy laws at the time, Booking.com says that it was only required to notify people affected by the data theft if it would likely have adverse effect on their private lives.
There's a lot of words here that have a lot of meaning. What does that mean, adverse effect?
Right. It's open to interpretation. Because I would argue that it was sensitive information because thousands of hotel reservations accessed involving countries such as Saudi Arabia, Qatar, the United Arab Emirates, names, travel plans, reservation details were in the hands of this mysterious hacker, Andrew. And according to these journalists who've investigated, they say that the Dutch intelligence service determined that Andrew was working for a US-based company that often did work for US intelligence agencies. In other words it was U.S. spies it appears who hacked this Dutch company in order to steal information about some of their customers ones who were in the Middle East.
They also lean on the legal team saying hush hush guys if you know what's good for you.
I don't know. But, you know, you do begin to worry a little bit, don't you? It feels a lot of power that these guys had. Right, Brian?
Indeed, yes. And I do think it's obviously private information.
So if the journalist's book is accurate, the spying was carried out by the US against foreign diplomats and other people of interest in the Middle East. And the theory goes that if the United States knew which hotels people of interest were staying at, they could cross check it against their list of hotels who they've already determined are fairly easy to exploit to plant surveillance equipment in or gather other information.
Playing devil's advocate, but how many other companies and corporations did also act strong, right, pre-GDPR? I mean, that's part of the reason GDPR is here, because it was just going, it was rife. So I get that. And it's hard, you know, 2020, you know, going back now and saying, how dare they? What's annoying is the loose language, you know, the skirting around the truth and what is sensitive and what isn't. And I think we have that definition now. You know, it's been defined. It certainly seems that more and more companies now are going public about having been hacked. So, Graham, are you going to never book from Booking.com?
I don't know that I have ever used Booking.com. But this is the thing, is that other travel companies, chances are that they've been hacked as well from time to time. You know, if intelligence agencies want to get into one, they probably want to get into others too. So who do I go to? That's
a very wise statement, Graham. That's very wise.
Thank you very much. I feel rather nervous now you said that. Brian, what do you want to talk to us about this week?
I want to talk to you about companies that are surveilling their employees without them knowing. So there's a story out today in the Los Angeles Times that cites various research. One of them is by Terramin, the Miami-based provider of employee monitoring software. And it said that basically about 70% of its sales came from companies concerned about security before the pandemic and 30% that used to be concerned about worker productivity. And now after the pandemic has struck, that relationship is completely flipped. So it's mostly about surveillance and less about security. And when they've looked at the actual amount of companies that are using surveillance software, they say that about 60% of companies are doing it double what it was early on in 2020. And the rub here is that a lot of people aren't aware that this is happening to them. It can be done through webcams. It can be done through keystroke logging, if it's company computers and so on. And this also relates to... I can't miss an opportunity to make the link to the book that came out last week of my own. which is that I think that there is a systematic problem that we have in diagnosing who is worth watching. So what I mean by that is I have a chapter where I talk about how powerful oversight is for producing accountability in human behavior. And I've drawn a whole bunch of different studies from neuroscience to behavioral economics and so on. But one of the things that I think we're getting wrong is that when you look at these corporate scandals, or you look at abuse of power by big fish, the real problem is happening at the top, right? It's happening in the boardrooms. It's happening behind closed doors and corner offices. The companies like Enron aren't getting brought down by the person who's stealing 10 minutes on their lunch break or takes a paperclip home with them. Yeah, it has an extra long poop, right? It's by the people at the top. Yeah. So I think, you know, we have this weird relationship with power in our society where powerful people design systems to relentlessly observe and surveil powerless people. And in fact, most of the damage is being done by the people who are watching, not the people who are watched. And so I think that this needs to be inverted. Now, it's not to say that we want to have a surveillance state by any means. And I think that in general, this general trend is bad. But I think that if you're going to have surveillance software, maybe some of it should be looking at what people who are actually moving millions of dollars around what they're up to. 24-hour video cam for CEOs. Love
it. Webcam their houses, their mansions. Webcam of the politicians. Isn't that what happened to Matt Hancock, I think? Isn't that how we discovered he was snogging his aide? Yeah.
Yeah. But I think it gets to something more profound about the sort of power imbalances that come with tech. And I think it's something about our own behavior where we have to think about who's actually doing the damage. Most people who are working from home are actually trying to get their work done. They might not do it on the clock in the exact same way that the employer wants them to, but as long as they get the work done, it's not going to bring the company down. On the other hand, there's a lot of people in the higher positions who actually can bring the companies down and have over time.
I've read about boss ware, what the kind of colloquial term is. But they'll take pictures every 15 seconds to make sure that said employee or student is sitting with their butt on the seat looking at the screen. Worse than that, I mean, when I was doing research for this, there are even chairs that exist. This is in the before times in the actual physical office. There are chairs that have pressure sensors to tell whether you're actually sitting in it.
It's like this not like the rock not like Dwayne Johnson like literally a piece of sandstone that has two eye holes in it it's hilarious right But the thing that I also love about him, I spoke to him on Skype. This is two years ago before Zoom was a big thing. And I couldn't see his face because he covers it with these beads. And the reason he does that is because he wants everybody in society who's powerful to think anybody could be him, right? So he never reveals his identity. He's a secret figure who's known as Anas, but no one knows who he is with the idea that anytime Anas could be watching you. And not good if you've got a bad back and you want to stand at your desk, you know, if you have to keep your butt off. Yeah, you're off the chair. The chair starts having an alarm.
Right? Maybe they have standing mats for those people who knows.
It is. I would have
a dictionary if people, you know, you wouldn't know if your chair has these sensors, right? So anyone who's going to go for an extra long bathroom break, make sure you bring a dictionary and slap it on the seat. What if you're really, really small?
Is there a particular book that you could put on your stool, if we want to use the phrase stool? Oh, yes, Brian. How heavy is your book, Brian?
You know, it's 270 pages or so. So it's not massive by
Three copies. Definitely buy hardbacks. Three hardbacks.
Yeah, I think so. I think you're going to have to get the... It's got... On the cover, it's got sort of gold foil. I think you'd need actual gold for it to work properly.
Carole, what have you got for us this week?
Okay. So we're going to imagine it's November 12th, and you guys are IT administrators.
Yes, I am.
And you're sitting around, you know, feet on your desk, definitely with butt in chair, so there's no alarms. Yes. And you get an email with a subject saying urgent threat actor and systems. Now, this isn't in your quarantine or spam folder, but sitting right there in your mainstream mail. Right. What's your first do then? Do you just get up, get a sandwich, ignore it, open it up? What do you do?
Well, I'd probably open, I wouldn't open the attachment or if there was an attachment or click on any links. Maybe I'd look at the actual message and see who it's come in from.
Yes. Let's check the sender. Yeah. Yeah. Okay, so the email is sent to you from the official email address of the FBI, so eims.jcfbi.gov. And you look this up, and it's a totally legit address. It's part of the FBI's Law Enforcement Enterprise Portal, or something called LEAP. This is a one-stop shop to share intel across different departments. And maybe you check the IP address, and indeed, it is the FBI's IP address.
And this isn't an accidental message that's been sent. You remember in Hawaii, they accidentally sent a message to everyone there saying that.
Oh, yes. And then later, oops.
North Korea launched a missile towards Hawaii, which caused a slight panic. Yeah. So it's not a test that's gone wrong or something like that.
Should we read the email? OK.
Go on. Yeah, tell me what the email says. OK, we're going to go sentence by sentence. All right. OK.
So it says, our intelligent monitoring indicates exfiltration of several of your virtualized clusters in a sophisticated chain attack.
Well, it's already lost me. It sounds quite technical.
It sounds quite technical. It sounds like they know what they're talking about, the FBI. I don't know what half those words mean. Exactly.
Yeah, it sounds like they know more than I do about something. Yes, right.
Okay, so you probably want to read the next sentence. Right, yes. Yeah. Okay, we tried to black hole the transit nodes used by this advanced persistent threat actor. However, there is a huge chance he will modify his attack with a fast flux technology, which he proxies through multiple global accelerators.
Sounds like those FBI guys really know what they're talking about now. And we're up against some serious hackers.
I mean, fast flux, guys. Fast flux. Yeah. Yeah.
Where's the bank account to send the money to the Nigerian prince now?
We identified the threat actor to be Vinnie Troia, whom is believed to be affiliated with the extortion gang, the Dark Overlord. Oh, my—
Cousin Vinnie. Yeah. Okay. Vinnie. Yeah. Well, Vinnie's an all right guy. Right.
I think at this point, I think I'd be going, what, why would you be telling me who the threat actor is? And what does this have to do with anything? And you're telling me that your intelligence monitoring, my virtualized clusters, tell me about them. Anyway, it says, we highly recommend you check your systems in IDS monitoring. Right. And then it signs off with stay safe. Okay, US Department of Homeland Security.
Well, that does sound authentic. I can imagine that the Department of Security would sign off with a stay safe. Really? No, but that's the sort of, yes, I can actually. I'm not joking. I'm not being sarcastic. No, they might. Well, what are they going to do? Say yours sincerely? It's too—
Cutesy, Brian. Brian, you've read loads of government documents, I'm sure, in your time. I'm sure you've read loads through your career.
I think it depends what country it's coming from. I think that, you know, if it's American, they'd say, have a good day or something like that.
Stay safe. Yeah. Okay. Okay. So what do you do at this point? Because there's no instructions. There's no attachments. There's no links.
FBI.
I would go onto Twitter. I would go onto Twitter and I'd see if other people have received something like this. Right. Okay. Well, Vinny's on the speaking circuit.
Yes, he is on the speaking circuit. Yes.
He's one of those sort of people who stand up on a stage and give talks about cyber security. Blah, blah, blah. Can you imagine how horrendous that is? No, no. That sort of person. Yeah, no, he's basically the competition for me, Carole. People like Vinny. But, you know, he's an author and, you know, he investigates cyber crime and things. So I'm a little bit surprised that he's now turned to the dark side and is now exfiltrating data from my network.
Graham, you identified him very well because I didn't know him. So I had to do a bit of looking in. So he's also head of security research at the dark web intelligent company Night Lion and Shadowbite. And Bleeping Computer got in touch with Vinny to ask him why he's being blamed in this email. And he says, my best guess is Pom Pom Purin and his band of minions. These are the guys behind the incident. Pom Pom Purin.
Pom Pom Purin. That sounds a bit like Chim Chimery. Chim-chim-chiru. What kind of name? Is that a name of a hacker, is it?
Well, apparently, Pom-Pom Purin contacted Troia a few hours before the spam email campaign started and simply to say, enjoy, as a warning that something involving the research was about to happen. And apparently, Pom-Pom Purin messages them every time they start an attack to discredit Troia. So there's a long-running feud, apparently, between the members of the raid forums hacking community.
Is it really doing that much damage to Vinnie Troia? I would imagine his name gets out there much, much more because...
Oh, are you in the market for someone to start bad-mouthing you in spam emails? Is that what you're looking for?
I've given people plenty of reason in the past. I don't think I'm important enough for them to bother.
Well, Mark Gaddafi contacts me all the time, so... And he's dead.
Well, so I was pom-pom purin, what is going on, right? So I went looking around and turns out Krebs got a missive from an actor claiming responsibility. And his first line is, hey, it's pom-pom purin. Check headers of the email. It's actually coming from FBI server. I'm contacting you today because we located a botnet being hosted on your forehead. Please take immediate action. Thanks.
Sorry, Brian Krebs has a botnet on his forehead? I don't really know what that means. I thought I was gonna ask you, you're a bit more geeky. I think it's a comment on Brian's haircut possibly. Maybe he doesn't have a big enough fringe to cover his forehead. Well, I think he looks perfectly fine but maybe the hackers have got some sort of issue with how he looks. It sounds rather juvenile to me. Is that possible cyber criminal?
Well, he said so speaking of Krebs he said I could have 1,000% used this to send more legit looking emails, trick companies into handing over data, etc. And this would have never been found by anyone who would responsibly disclose due to the notice the feds have on their website. So that's interesting. He's basically saying that he could not responsibly disclose because of some legalese. Some legalese of the feds.
Right, saying you can't do this on our server if you find a phone. Well, couldn't the FBI now say, look, we're actually really grateful you found this. If you would telling us your full name and address. Pom-pom-purin, Mr. Pom-pom-purin. We will send a special delegation round to your house to deliver your bug bounty personally. And a couple of extra surprises.
The thing was, they did manage to hack this page, but none of the data that was on the LEAP system was accessed. It was all scraped from another database. So it really was just a juvenile kind of trick, but it did cause some drama. I think people would not have been as lazy as you, and they might have contacted the FBI and going, what the fuck, guys? WTF?
Well, clearly, yeah, clearly people did. Even if they didn't lose any data, they still had a portal exploited by a mischievous little runt.
My final question. My final question. Do you think the FBI has apologized for their oversight on the website?
I think yes, they have.
I would guess no.
Correct. Brian's right. No. Well, not the first time.
Perimeter 81 is the first ever cybersecurity experience platform designed around instant deployment, unified management, integrated security and full visibility. Perimeter 81 allows organizations of any and all industry sizes to support IT teams with robust tools to secure and manage your global network with one unified platform. Securing remote access for cloud and hybrid businesses and organizations, Perimeter81 provides unified solutions such as zero trust network access, firewall as a service, device posture check and more. Learn more and request a demo at perimeter81.com. That's perimeter81.com.
We're also sponsored by Qualys, one of the pioneering providers of disruptive cloud-based IT. Qualys delivers continuous critical security intelligence via their Qualys cloud platform and integrated cloud apps. And they're powerful solutions and power organizations to streamline and consolidate their security and compliance solutions in a single platform, achieving greater business agility, better outcomes, and substantial cost savings. Qualys announces three solutions, ransomware risk assessment, cybersecurity asset management, and zero-touch patch management. Want to learn more? Of course you do. Check out smashingsecurity.com/Qualys. Q-U-A-L-Y-S. That's smashingsecurity.com/Qualys. And thanks to Qualys for sponsoring the show.
1Password 8 for Windows is out right now. 1Password 8 for Windows has been reimagined to feel right at home on the world's most popular desktop operating system. From dark mode and passwordless integration to smart search and secure items sharing, 1Password 8 is the new home for your digital life. Productivity improvements, enhanced security and privacy features, and a modern design deliver a first-class experience that offers the best of Windows 11. 1Password 8 for Windows helps you manage, remember, and protect your sensitive information more easily and securely than ever before. So, what are you waiting for? Find out more. Try 1Password free for 14 days at 1Password.com. And thanks to the folks at 1Password for supporting the show. And welcome back. Can you join us at our favourite part of the show? The part of the show that we call Pick Of The Week. Pick Of The Week. Pick Of The Week. Perfect. Pick Of The Week is the part of the show where everyone chooses something that could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. It doesn't have to be security-related necessarily. Better not be. Now, in a slight change, I'm going to do a little bit of a shout out because it was my niece Marlo's birthday recently and I sent her some little cupcakes, which was frankly a bit of a lazy gift. And yeah, did you make them? No. Thank God. Lucky her. She should be grateful, shouldn't she? She definitely should be. But as a penance, she has asked me to give a bit of a shout out on the podcast to, and indeed I'm going to dedicate my Pick of the Week suggestion to Paul Frost of Streatham and Clapham High School, London. He is the best computer science teacher within the Streatham and Clapham catchment area. Aww. As voted for by my two nieces, Mallory and Marlow. So, Paul, congratulations. This pick of the week is for you. And hopefully I've got off any birthday shenanigans for another year. So my pick of the week this week is not security related. It is a video game called Trail Makers, which I've been playing with my son on the PlayStation. But it is also available on Steam and on the Xbox. It is a physics-based game where it's a bit like Lego. It's a bit like technical Lego, where you can build cars and monster trucks and boats and submarines and tanks and aircraft and amphibious vehicles, all sorts of things. You can even build an ATAT from Star Wars. Or, you know, it's basically you're limited by your imagination. Your imagination and your ability to make them aerodynamic or having a good centre of gravity, because it turns out, Carole, I don't know if you found this as well, Brian, it turns out it's quite hard to make a working helicopter or an aircraft and to actually get it to go up in the air and not crash. If you can get it to leave the ground at all. Turns out it's tricky.
You know, you're giving me a great idea for a game. Imagine you could scan your body and then say, how do I become aerodynamic? And you'd have to lengthen your arms or whatever to kind of be weightless enough. And you could find out what length of arms you would require. Listeners, someone run with it. It's yours.
And having designed these things, you can share them online. You can have other people download them and adapt them. My son and I, we've been doing little build challenges, and he came up with the idea of how about we build some monster trucks dad but let's make them look like dogs and so we've been driving dogs around this island in a little sandbox island. Well his drove around complete with a wagging head and tail, mine just sort of fell over. It had the oddest way of steering you've ever seen in your life but anyway I've had great fun. The game is called Trailmakers, I will put some links in the show notes where you can check it out or check out the video as well. I think if your kids are going to play video games, this is a better kind of video game to play because you are creative, you're learning about physics, you're learning about engineering, and it was all good fun. So that is my pick of the week. Nice. Yay.
Brian, what's your pick of the week? All right. So my pick of the week is a book. It's not my book, but it's featured in my book. So it
should be your book. What's your name of the book again? What have you got a book out, Brian? Have you ever written a book? Oh, right. It's funny you mentioned it. It's called Corruptible, Who Gets Power and How It Changes Us. But the book of the week that I'm going to, my pick of the week is actually a book that inspired a chapter. And it's a book by a journalist called Mitch Moxley, one of the other good people in the 500 that I've interviewed. He's a journalist who spent a lot of time in China. And the book is Apologies to My Censor, as I say. And just to be absolutely clear on this, because I think I've only just tweaked, this wasn't for a scam or anything. This is purely for prestige and kudos. It's just, oh, look, we've got this man coming along who's involved.
Exactly. So there's actually a cottage industry. There are people who make their money in China who are expats. They're white. And they're brought in to give the veneer of legitimacy to Chinese operations to show that they have international appeal. So they sometimes will have attractive white women at the opening of bars to show that they're...
I've never seen a Western company do that ever. So
it's an amazing... I mean, it's an amazing statement on race and power and all sorts of things, but it's a whole cottage industry, apparently. And Mitch just sort of stumbled across it and said, this actually is something that a lot of people do and it's how they earn their money in modern China.
Maybe there are actually agencies which have a variety of sort of white men on their books you can choose from. Maybe with a clarinet, maybe not.
The funniest thing about this, I talked to him about this. And he was featured in the hundred hottest bachelors in China's Cosmo, Cosmopolitan magazine. And they hadn't seen a picture of him before they picked him. He happens to be a good looking guy, but it's just, it's just a very funny thing where they're like, they just picked a hundred white people and put them in this magazine. And it's just, oh my God, how does this happen in the 21st century? It's just so unbelievable. Did he get paid well though? I think he got paid $1,000 and then got lodging, but he was in this sort of backwater town. So I think he did it for the story because ultimately he wrote about this in The Atlantic. And then I think an agent probably contacted him and he turned it into a book about all about his adventures in modern China.
Fantastic. So the book's called Apologies to My Censor by Mitch Moxley. Terrific. Carole, what's your pick of the week?
Okay, we're heading to entertainment and culture. So, Graham and I, we share some tastes, actually, but we don't share everything. Like, you hate nuts, for example, which is ironically nuts.
I don't like the clock on the wall in your room.
Yes, which is an amazing clock. I should send a picture to our listeners and they will agree with
me. I don't think they'll like it either.
I think they will. But I think you're going to like this pick of the week. Actually, I should ask you first, do you like Billie Piper?
Billie Piper, Rose from Doctor Who. She's terrific. Yeah, Secret Diary of a Call Girl.
Exactly. Okay, so have you heard of a series called I Hate Suzy?
I think I have heard of it. I haven't seen it.
I hadn't either, but friend of the show, Dave Bittner, sent me a message saying you should check it out. It was right up my street. And I obviously trust him because I had to purchase it because I don't have Sky or anything like that. So Billie Piper stars in it. She plays Suzy Pickles, a former child screen star. And as the character, she has poor impulse control. She's irresponsible. She's high maintenance. But she also has a number of assholes in her life that don't help matters at all. But things get super complicated when a compromising sex scandal involving the married Pickles hits the papers, all thanks to a phone hack. Oh my God, that's security related. Oh, hello. Apologies for that. Her phone is hacked, eh? Yeah, I'm sorry guys. Anyway, so it has a lot of references to things that have happened in the UK press over the last decade or so, two decades probably. And also it probably follows a lot of tangents in her own career because she was a child star, right? A singer.
Yeah, she was.
And the writing is very fresh. It's written by Lucy Prebble who also wrote Secret Diary of a Call Girl and has the same gritty sadness. It's funny, it's lewd, it's a little wild, a little dangerous but you just feel like you're on a roller coaster and you think the thing's going to fly off the track at any point and you can't predict it. And that's hard to do in a story. So this is definitely not for kids but my pick of the week this week is a TV series called I Hate Suzy. Thanks D-Dog Dave.
Oh right, and where can people watch this?
I had to buy it so you can get it on Sky in the UK. I purchased it off, you know, wherever you can buy TV series, right? So Apple or Amazon or any of these.
Oh interesting. Okay. Check it out, Graham. It's worth it. You'll like it. All right. Okay. Well, Carole, you've had a busy week, haven't you? You've been speaking to the folks at Perimeter 81.
Yes, I spoke with Amit. Interesting interview. Check it out. Okay, today we are speaking with Amit Barakat, CEO and co-founder of Perimeter 81, an industry leading SaaS security platform. Welcome to the show, Amit.
Thank you very much. I'm happy to be here.
Now, you are the co-founder of Perimeter 81. Can you tell us a little bit about what drove you to launch this SaaS security platform? Was there a problem you wanted to fix or what drove you?
Actually, it's a very deep question. I had my previous company, SaferVPN, a consumer VPN company that me and my co-founder sold to a public company in the US. Back then in 2013, we've developed a consumer VPN solution, which was our first startup, our first company that we've incorporated together after I left my corporate job at IBM and Siegate Siemens. Back then, we wanted to develop a cloud security solution for consumers. But while we were working with our customers, back then the consumers, we've heard a lot of demand from the business side, from businesses to consume security and networking from the cloud. Back then, fiber started and 5G, there were discussions about it, and the internet became faster and faster. It was before COVID, but we saw a trend where the internet is going to become the new corporate network. We thought, how can we utilize our knowledge and know-how, both on building SaaS solutions specifically for B2C, business to consumer security solution, to build a secure network for organizations to be delivered over the internet. So it doesn't matter where the employees are. When they open their laptop, they have the same security experience.
That's incredible because your timing is perfect in a way, considering the last few years that we went through where people were having to work from home for the first time in their lives in some cases.
That's right. It's absolutely correct. COVID really accelerated this trend overnight in February 2020. I remember that very clearly. For us, COVID accelerated this trend, which in any way would happen, but instead of 10 years, everything shrunk into two years. It accelerated our product development and adoption. We strongly believe that it will only get stronger.
Yeah. You know, I've heard you guys refer to the cyber complexity trap. Can you tell me a bit about that?
Absolutely. So what we found out that not only employees are working from home and resources are moving to the cloud and the internet is the corporate network. But today there are many, many different cyber security solutions. The average IT manager, and we've done a survey, managed about 20 different security solutions. Each one managed separately as its own setup, installation, sometimes most of the time hardware, management console. And that increase the inflation of security solutions basically creates a paradox, a trap where there are dozens of tools to manage. Because of that, you don't see anything. And even you don't know which security solution you need to implement. So when you ask an IT manager, what is your current area of focus? He's confused. And it's also increased the ability to provide impact. That basically complexity, we call it the cyber security complexity trap, where employees are working from everywhere, and the internet is now the corporate network. There are many devices, many resources, many hybrid environments, but there are dozens of tools to manage.
Yeah. The complexity for the IT professional and the CISO has just grown exponentially, I think, over the past maybe even five to ten years. And yet, I'm not sure the resources have climbed with that. I wonder how many of them have actually pulled their hair out completely because of the new situation that they're facing. SPEAKER_01. So absolutely. I think that if two years ago, a year ago, during COVID, right, the discussion was around how I'm going to secure my employees while they're working from home, how I'm going to secure my cloud environments, right? Today is how I'm going to deal with all those tools. This is a very hard topic because that inflation of different tools and solutions is decreasing the impact on security and what we found that it's not only important to provide a tool to secure, to unify security and networking over the cloud, but also building an experience, in order to deliver cybersecurity in a simple way and engineer the solution, right, not only to answer the use cases, but rather put the people in the center and think and engineer, right? Invest many hours and days and weeks and years into a maker evolution, not evolution in the way that cybersecurity is being consumed. This is one of the reasons why we launched a new category now, which we call the Cybersecurity Experience Platform. Perfect. I really wanted to ask about that. So please tell us about that. Tell us about this new service. SPEAKER_01. So the cybersecurity experience platform, what we've done along the way, and we've heard from our customers that we managed to build a solution that is very simple. It increases productivity, it increases the impact on the organization, the ability to implement security solutions, that we basically build a radically simple cybersecurity solution. That's what we're hearing from our customers. As we continue to hear that, we'd like to double down on that, right? To invest more, to continue engineer our solution, right? To provide insights that will be evolutionary step in cybersecurity for any businesses. Is it fair to say almost out of the box is what people really need right now? Because they don't want to spend too much time worrying about security. They want expert partners that are going to do that for them. SPEAKER_01. Right. It's the one, the minimal efforts, we call it becoming a Sherpa, right? A partner where you basically give them solutions for today's needs, but also for tomorrow and take them hand by hand throughout this journey to implement a modern cybersecurity posture within the organization, specifically in this new world where the internet is the new corporate network. Our platform includes a few parts of the tips to do it, like the deployment is instantly and you don't need to wait or order any hardware. Everything is being done via software. There is one management concept that is unified and provides lots of insights and data and extract the juice, right? The important thing to the IT managers and the security personnel in a very effective way. Integrations with all the important security solutions like identity provider and SIM service in a very holistic way, not just a PR or a blog post about integration, but really to drill down deeply into how we can be better together with the link security services and to unify the experience, full visibility and partnership and guidance as well with our customers. If you had a new customer who's listening to this and going, this sounds absolutely fantastic. One of the things that they often ask first is what is the onboarding times? From actually looking at it and getting it to actually having it up and running and protecting you. SPEAKER_01. We made it very, very easy. Just like implementing Office 365 can be done very quickly in an hour, sometimes some deployment, a bit more. But it is important to stress that companies that are starting with us, not overnight, basically removing all their existing security solutions and appliances, it's a process. It's not rip and replace, but it's migrate, right? So as you move to the cloud, we have integrations with all the existing security solutions, including all the firewalls out there, and allowing companies to do the migration in their face, right? We don't push them to do it in one day to completely change the way the IT and security is being delivered. But rather than joining this journey, you can start with a small team, for example, third parties. We have many larger enterprises that instead of moving the entire company to consume networking and security from the internet and the cloud within Pernet81, they choose to do it only with a third party. So any chain of supply, instead of giving them access to the legacy network of the organization, they provide them a different network that is secured by Pernet81 and slowly, slowly adding more departments. And so from what I'm getting, actually, this is a solution that is not just suitable for large enterprises or small businesses, but actually can accommodate across the whole spectrum of company sizes. SPEAKER_01. You can think about it like Gmail, right? Gmail can be for a small company, a very large enterprise. Yeah, yeah. Is there anything that you'd like to add for our listeners? Yes, I think that we are in a point of time that is revolutionary in matter of cybersecurity and networking infrastructure that is being developed and we are here to help. I think that it's better to prepare ahead for this revolution. It will increase, I think we're just in the beginning, it will increase over the next few years and it's very very meaningful. We see all the attacks that are happening in the world to start and double down on the security portion of the organization and regardless to implementing or not we have a team and the consultancy team that helping through that journey and transformation that is happening today in the market so feel free to reach out to us and ask us anything that you have in your mind. I actually have one more question for you if that's okay. I just was wondering your opinion on the plethora of cloud services out there that have default settings that may not be necessarily in the best cybersecurity interest of the company. Have you seen that as well? Is that your experience?
Yeah, I saw that a lot. That is an area that we, Perimeter81, would like to continue and develop as well within our platform, definitely all that posture management of SaaS solutions. And it's a big topic now, whether 2FA is enabled or not, right? How you can have visibility to all your SaaS applications. You have lots of different SaaS applications, and it's a very hot and relevant topic these days.
Yeah, absolutely. Well, Smashing Security listeners, you wonderful people can learn all about Perimeter81 and its flagship cybersecurity experience platform. And you can even book a demo. So go to Perimeter81, that is perimeter81.com. Amit Barakat, CEO and co-founder of Perimeter81, thank you so much for coming on and speaking to us about cloud security.
Absolutely. It was a pleasure. Thank you so much.
Terrific. Well that just about wraps up the show for this week. Brian, I'm sure lots of our listeners would love to follow you online, find out more about your book. What's the best way for folks to do that?
Yeah, so my Twitter handle is Brian Klaas, which is Brian with an I and Klaas K-L-A-A-S. And the podcast is Power Corrupts and the book is Corruptible: Who Gets Power and How It Changes Us. Go out and buy it, people.
Fantastic. And you can follow us on Twitter at Smashing Security. No G. Twitter now stuffed the G. And we've also got a Smashing Security subreddit. And don't forget, to ensure you never miss another episode, follow Smashing Security in your favourite podcast app, such as Apple Podcasts, Spotify and Google Podcasts.
And finally, thanks to this episode's sponsor, 1Password, Qualys and Perimeter81, and to our wonderful Patreon community. It's thanks to them all this show is free. For episode show notes, sponsorship information, guest lists, and the entire back catalogue of more than 251 episodes, check out smashingsecurity.com.
Until next time, cheerio. Bye-bye.
Bye. Bye.
And actually Brian, I have to ask this because I wasn't sure. Do you have a clip of Piers Morgan speaking in one of your Power Corrupts episodes? Do you remember?
I don't think so. I can't remember.
Okay. Oh, God. Okay. Maybe it wasn't him. I was just thinking it sounds like him. I can't remember even which one it was now. I was just listening to it yesterday.
It's possible. The thing is, I draw clips from all sorts of news things, so it's totally possible, but I don't remember him specifically.
Anyway, it was just because Graham has a bit of a love affair with him.
Oh, right. I think when you say love affair, what you actually mean is deep, deep hatred.
I thought that that might be the case. Yeah.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Brian Klaas – @brianklaas
Show notes:
- American spy hacked Booking.com, company stayed silent — NRC.
- Booking.com was reportedly hacked by a US intel agency but never told customers — Ars Technica.
- Dutch newspaper links Booking.com break-in to US spy groups — The Register.
- Belgium’s largest telecoms company says it was hacked — Graham Cluley.
- GCHQ “infected Belgium’s largest telecom company with spyware” — Graham Cluley.
- Is your company secretly monitoring your work at home? — Los Angeles Times.
- School janitor says she was fired for not installing smartphone tracking app — Graham Cluley.
- Hawaii’s ballistic missile false alarm and a user interface failure — Graham Cluley.
- FBI system hacked to email 'urgent' warning about fake cyberattacks — Bleeping Computer.
- Hoax Email Blast Abused Poor Coding in FBI Website — Krebs on Security.
- Vinny Troia's website.
- FBI Statement on Incident Involving Fake Emails — FBI.
- What is Trailmakers? — YouTube.
- Trailmakers – Build vehicles and explore the world.
- "Apologies to My Censor" by Mitch Moxley.
- "I Hate Suzie" trailer.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff
- Support us on Patreon!
1Password 8 for Windows has been reimagined to feel right at home on the world’s most popular desktop operating system.
From Dark Mode and passwordless integration to smart search and secure item sharing, 1Password 8 is the new home for your digital life.
Productivity improvements, enhanced security and privacy features, and a modern design deliver a first-class experience that offers the best of Windows 11.
1Password 8 for Windows helps you manage, remember, and protect your sensitive information more easily and securely than ever before.
Take the 14 day free trial now at 1password.com
Qualys was one of the first SaaS security companies, and delivers continuous, critical security intelligence via their Qualys Cloud Platform and integrated Cloud Apps.
Its powerful solutions empower organisations to streamline and consolidate their security and compliance solutions in a single platform and achieve greater business agility, better outcomes and substantial cost savings.
Qualys recently announced three new solutions designed to address today’s challenges faced by enterprises: Ransomware Risk Assessment, Cybersecurity Asset Management, and Zero Touch Patch Management.
Learn more at qualys.com
Perimeter 81 is the first-ever Cybersecurity Experience Platform, designed around Instant Deployment, Unified Management, Integrated Security, and Full Visibility.
Perimeter 81 allows organizations of any and all industry sizes to support IT teams with robust tools to secure and manage your global network with one unified platform.
Securing remote access for cloud and hybrid businesses and organizations, Perimeter 81 provides unified solutions such as Zero Trust Network Access, Firewall as a Service, Device Posture Check, and more.
Learn more and request a demo at perimeter81.com
Follow the show:
Follow the show on Bluesky at @smashingsecurity.com, on the Smashing Security subreddit, or visit our website for more episodes.
Remember: Subscribe on Apple Podcasts, or your favourite podcast app, to catch all of the episodes as they go live. Thanks for listening!
Warning: This podcast may contain nuts, adult themes, and rude language.