As The Register reports, UK water service supplier Southern Water made it all too easy for unauthorised parties to view customers’ billing documents and account details.
A chap called Chris H uncovered the problem, and posted a blog about how the utility company allowed any logged-in customer to view bills and documents from other customers.
As Chris describes in his blog post, as a customer of Southern Water he is able to log into his account and view recent correspondence sent to him about his water bill.
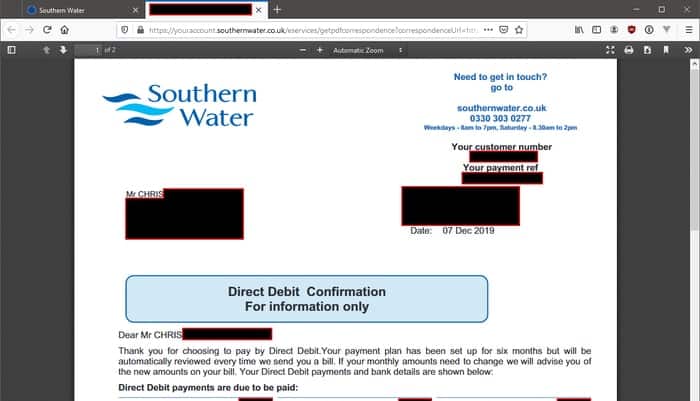
This includes being able to view his Direct Debit statement.
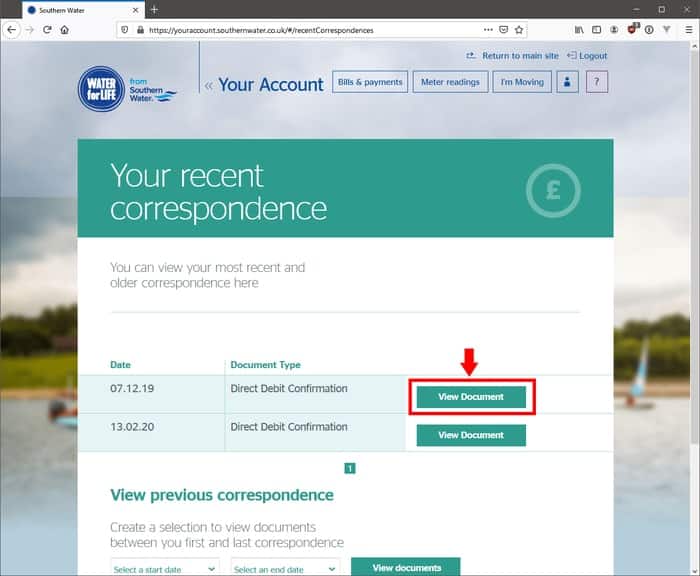
Clicking on the link takes Chris, as you would expect, to a PDF of the document.
Where’s the harm in that you might wonder?
Well, take a look – like Chris did – at the URL.

Chris found that the PDF document is actually stored on Southern Water’s internal SharePoint database, and the link to that document is used as a parameter in the URL visible within the customer’s browser.
https://youraccount.southernwater.co.uk/eservices/getpdfcorrespondence?correspondenceUrl=https://[redacted].sharepoint.com/sites/[redacted]/12/09_12_0_s1/[redacted].pdf
With a little twiddling of the parameters in the URL, it was easy to access bills belonging to other people – including their full names, addresses, customer account numbers, payment reference numbers, bill and payment dates, account balances, payment accounts, meter recordings, and so on… with no checks made as to whether the access was authorised.
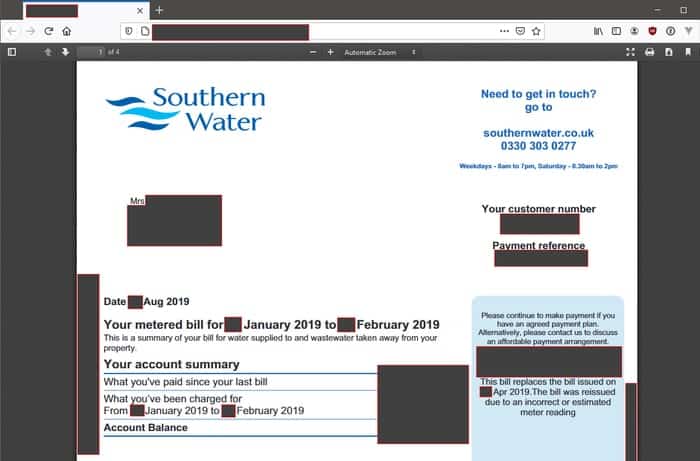
That’s the kind of information that shouldn’t be public. After all, if someone rang you up claiming to be your water company and confirmed their identity by telling you some of those details… you might very well believe them, right?
Which would be a boon to scammers. And as utility bills are frequently requested as a proof of identity when making credit applications, there are plenty of opportunities for foul play.
Thankfully, the Southern Water website has now been reportedly been fixed, and data should no longer be leaking out. Albeit after a PR representative for the firm foolishly mentioned to Chris that it might look at taking legal action against him for pointing out their glaring flaw.
I wonder if other utility firms might be similarly behind-the-times when it comes to handling vulnerability reports appropriately.