Updated
A massive database, containing more than five billion records derived from past security breaches between 2012 and 2019, has been left unprotected, without any password protection on the internet.
And who left it exposed? A security firm.
Researcher Bob Diachenko says that he found the unsecured “data breach database” on a publicly-accessible Elasticsearch instance, managed by British security outfit ███████ ████, on March 16th.
Diachenko immediately sent ███████ ████ an alert about the security breach, and although he never received a reply the data was taken offline within one hour.
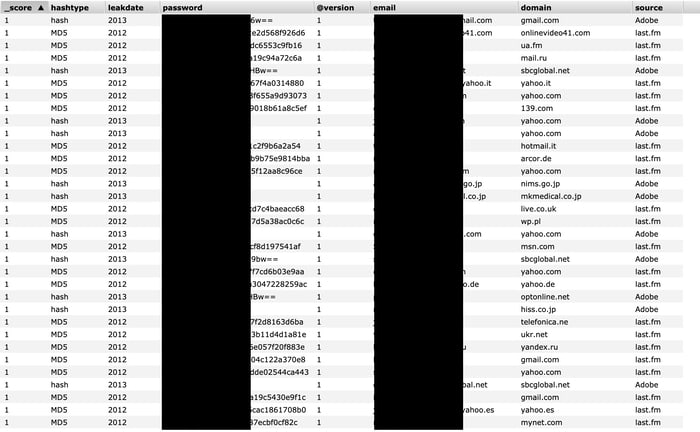
The data that Diachenko stumbled across (and that anyone else could potentially have accessed) included:
- hashtype (for instance, whether the password was represented as MD5 hash or plaintext)
- the year that the data leaked
- the password (hashed, encrypted or plaintext)
- the email address of the breached user
- the source of the leak (for instance, Adobe, Last.fm, Twitter, LinkedIn, etc)
Of course this was data that had been previously exposed in past security breaches, and so it’s not as though users whose details were included in this leak were not already at some risk.
But that’s really no excuse for a security company to be so lax about its own security, and potentially compound the risks of users still further.
Presumably ███████ ████ was storing its huge database of previously-breached records in order to conduct its own research into security incidents, or provide a service to its customers. What it has actually done, however, is put at an awful lot of people at increased risk.
Security features on Elasticsearch instances are disabled by default, making it seemingly all-too-easy for administrators to effectively ignore the essential requirement to implement a proper defense before making their systems live on the internet.
Two months ago, Microsoft admitted that it had left 250 million customer service and support records exposed on five unsecured Elasticsearch servers.
Update 3 June 2020:
This article has been updated to redact the name of a security firm after it threatened this site with legal action.
I gave the firm multiple opportunities over the last three months to offer a statement giving their point of view, or to answer questions related to the incident, but they declined. Instead, they chose to threaten an independent blogger with legal action if their name was not removed.
I hope readers will accept my apologies for what is clearly unsatisfactory, but I can ill-afford to get embroiled in a legal fight.
I have closed comments on this article, to prevent others from naming the firm concerned.



Great reporting! Thank you Graham and stay healthy.
Oh dear me… One might argue that it's not as if the data wasn't already available so is it really that much more harm? Except that it's together collectively and it also gives another source of it.
One hopes that they will have learnt the lesson but in the meantime more exposure is never a good thing.
Stay safe and healthy (and sane) – to everyone even!