A security analyst found himself banned after he publicly disclosed multiple vulnerabilities affecting a series of web forums.
On July 10, reverse engineer and security analyst Andrew Tierney tweeted out NeighbourNet’s suspension of his account following alleged ID misuse.
Not an ideal response to reporting security issues… pic.twitter.com/8MhL0jmlho
— Cybergibbons (@cybergibbons) July 10, 2016
NeighbourNet is a network of local news and community information websites based in West and South West London. The platform powers www.BrentfordTW8.com, www.ChiswickW4.com, and other websites.
Tierney’s relationship to NeighbourNet dates back at least to the beginning of May, when he first informed the platform’s administrators of four security problems.
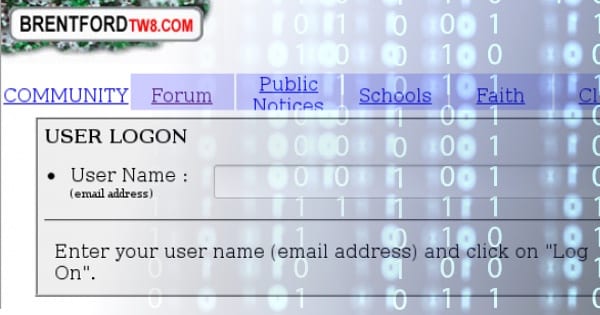
Many if not all of the issues result from an overly simplistic website design. For instance, users do not need a password to authenticate themselves. All they need is their email.

The issues don’t get better once users have signed in. NeighbourNet’s forums pass a user’s name and email as a parameter whenever they post a message. That means someone could masquerade as other users and post messages under their names.
In addition to providing no cross-site request forgery protection, the platform also allows embedding of untrusted third-party content.
This is a dangerous security oversight, as Tierney explains in a blog post:
“The site embeds its own content using a URL passed as a GET parameter. The source of this content is not whitelisted or validated, so you can just embed your own content. This has only been tested with plain HTML, but if JavaScript, Flash or other content could be embedded, this would lead to cross-site scripting or malware delivery to users.”

Tierney first notified NeighbourNet of the security flaws on May 3. After chasing for a response from the company, he decided to notify the platform on June 14 that he would go public with the vulnerabilities around July 4 if the bugs weren’t fixed by then.
On June 17, he received this response from the company:
“Chatted to the development team about the issues you raised.
They acknowledged that you have identified some potential security holes but they have existed for a long time without ever been exploited and there seems little incentive for anyone to try to do so.
We have been for some time now working on completely overhauled site architecture and whilst this project has been ongoing for sometime we are now talking in terms of months rather than years before implementation. This would close these security holes and others.”
NeighbourNet went on to tell The Register that the company’s sites contain no “nasty vulnerabilities that could compromise users” and that Tierney had so far failed “to give a single example of any actual occasion on which security is compromised.”
As revealed by its comments, while NeighbourNet is willing to acknowledge its site contains some “potential security holes,” it refuses to accept the fact that anyone has or will ever have any motivation to exploit those flaws in the future.
That’s pretty small thinking. NeighbourNet is an information resource, which means attackers could at the very least deface it, spread hateful messages while posing as legitimate users, and disseminate malware to unsuspecting visitors.
Ignorance and blind faith might feel reassuring in the moment, but at the end of the day, they’re only a mindset. They don’t efface the seriousness of glaring security vulnerabilities, which is why Tierney decided to go public with them on July 10.
NeighbourNet might have banned him as a result, but all of us in the security community should thank Tierney for practicing responsible disclosure and for attempting to work with a platform in order to keep its users safe.



There are a few problems here! The law of the land and ethics. The main problem is a legal one for the analyst, the Computer Misuse Act 1990, it is still unlawful unauthorised access, modification, interference, even though in principle the analyst is right ethically, legally he is in the wrong. Look at what happened to Daniel Cuthbert a few years ago. You can't just go around hacking into what you want to (being a "white hat" or "grey hat"), unless you own it, or have explicit consent to carry out security testing. Clearly the site owners are small minded, and should be more data subject focussed (Facebook and Google let you hack your own account for example), there is some guidance for these "business people" on the ICO website, "IT Security for small businesses", and users of the sites will probably have a claim for distress under the new changes in case-law under the DPA should they become a victim of anyone compromising the site….and yes of course anyone can hack in, but you've named yourself! and fallen on your own sword…
It's hardly 'hacking', though, is it?
You don't need to be a 'grey hat' or 'white hat' hacker to be able to see that only your e-mail is required to log in. Anyone who uses the website can see that, even people who aren't particularly computer-savvy.
You don't have to change the website/page's source code or anything complicated like that. All you have to do is go to the website, click on "Membership" in the left menu and then on "Logon".
Besides, Tierney's disclosure was specifically about the login procedure being unsecure and thus a security vulnerability, and about the user's name and e-mail being passed as URL parameters when posting something, allowing users to pretend to be someone else (which also isn't rocket science – although it does involve changing URL parameters, which may come close to 'hacking', but still isn't an attempt to gain access to a computer file or network).
There was no mention of him trying to gain access to the company's computer or network illegally.
———————————-
hack (hăk)
v. hacked, hack·ing, hacks
v.tr.
a. Informal To alter (a computer program): "hacked her text editor to read HTML."
b. To gain access to (a computer file or network) illegally or without authorization: "hacked the firm's personnel database."
———————————-
Besides, that case you're talking about, the one involving Daniel Cuthbert, was in 2005. More than 10 years ago, and certainly more than 'a few years ago'.
Sounds like a news story waiting to happen