 Do you have a digital thermostat in your home?
Do you have a digital thermostat in your home?
Are you confident that it has been configured securely, and cannot be exploited by remote hackers?
Maybe now is a good time to check that the latest gadgetry you’ve introduced to your home is safe, after digital thermostat manufacturer Heatmiser contacted its customers, informing them that their devices are vulnerable to attacks which could leak their WiFi credentials.
As ThreatPost describes, the vulnerabilities were brought to Heatmiser’s attention by bug hunter Andrew Tierney who documented the various problems he found with the devices, and discovered over 7000 vulnerable thermostats connected to the net.
The digital thermostats make the cardinal mistake of shipping with default usernames and passwords (both “admin” – imaginative, eh?) and an access PIN of “1234”.
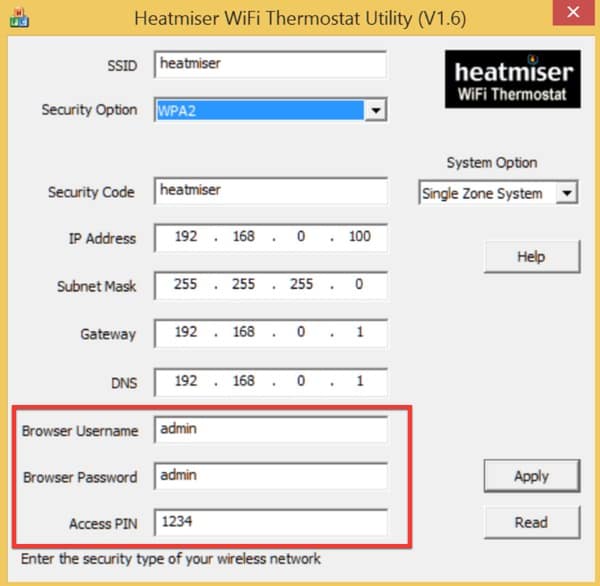
Disappointingly, at no point is a stronger password or PIN advised, let alone enforced.

That would be bad enough, but further examination by Tierney uncovered a method by which it was possible to access any of the device’s administration pages, regardless of whether the username and password had been guessed or not.
In a mastery of understatement, the researcher summed up this particular flaw as “really not good.”
Tierney also discovered that once logged into a Heatmiser device, he discovered that the user’s username, password, WiFi SSID and WiFi password “are all filled into the form and can be viewed easily by examine the source of the webpage.”
During his investigations, Tierney uncovered that the devices were vulnerable to a number of threats including cross-site request forgery (CSRF) attacks.
Tierney informed Heatmiser of the issues he uncovered, and the firm has now emailed its customers a brief security advisory.
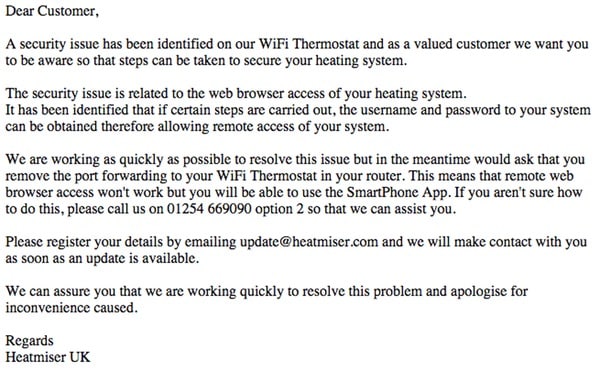
Part of the email reads:
A security issue has been identified on our WiFi Thermostat and as a valued customer we want you to be aware so that steps can be taken to secure your heating system.
The security issue is related to the web browser access of your heating system.
It has been identified that if certain steps are carried out, the username and password to your system can be obtained therefore allowing remote access of your system.We are working as quickly as possible to resolve this issue but in the meantime would ask that you remove the port forwarding to your WiFi Thermostat in your router. This means that remote web browser access won’t work but you will be able to use the SmartPhone App. If you aren’t sure how to do this, please call us on 01254 669090 option 2 so that we can assist you.
Until Heatmiser fixes the vulnerabilities, the most sensible thing to do may be to disable port 80 on your thermostat and disable its WiFi capability.



I think the problem with these sorts of advisories, is that people just shrug and think 'So what, big deal, they have access to my thermometer'. Maybe you should underline a bit more heavily the risks involved in letting people in. Are there any beyond leaking your wifi AP and password? Although this is serious, it's only exploitable if you're in the same geographic area, which is pretty unlikely in fact if you found the device by Google Hacking.
I'm also an IT security consultant, and have had to explain, time and time again, that "Your Gmail account is not 'just a bunch of emails' and THIS is how it can be used against you … "
It's not just exploitable if you're in the same geographical area – if users have opened port 80 and 8068 on their home routers, then it's exploitable from anywhere in the world.
Mine was setup with changed admin credentials and only port 8068 forwarded to the unit for the android app access – so I'm not sure any of the above exploits would work in that configuration – but still, I've turned it off and will now just enable my OpenVPN connection before using the app – thus encapsulating the insecure traffic and passing over a secure tunnel – that then completely negates the security flaws with the unit.
Still, I will be asking for a firmware update, but I'll have to send my unit away no doubt for it to be done. Might wait until next spring, in that case!!
At the root of the password problem is the cognitive phenomena called “interference of memory”, by which we cannot firmly remember more than 5 text passwords on average. What worries us is not the password, but the textual password. The textual memory is only a small part of what we remember. We could think of making use of the larger part of our memory that is less subject to interference of memory. More attention could be paid to the efforts of expanding the password system to include images, particularly KNOWN images, as well as conventional texts.
Most of the humans are thousands times better at dealing with image memories than text memories. The former dates back to hundreds of millions of years ago while the latter's history is less than a fraction of it. I wonder what merits we have in confining ourselves in the narrow corridor of text memories when CPUs are fast enough, bandwidth broad enough, memory storage cheap enough, and cameras built in mobile devices.
Who in their right mind would connect an appliance to the Internet?
BTW, if connected to the power grid, any digital appliance can be hacked from anywhere in the world.
And, then there's your OnStar….
Because it is novel to be able to control home devices when you're away from home – that is obvious and not unexpected in the slightest.
Manufacturers of home router devices should appreciate that this is what people want to do with their connected devices, and they should be providing really easy VPN solutions to enable people to connect back to their homes in a secure fashion.
If every home router manufacturer included a simple downloadable VPN app for common phones and tablets, it would make things a hell of a lot more secure for the average user.