 For the past three years, Hector Xavier Monsegur, an unemployed Puerto Rican father-of-two, living in public housing project in New York’s Lower East Side, has been helping the authorities on both sides of the Atlantic identify members of the LulzSec and Anonymous hacktivist groups and bring them to justice.
For the past three years, Hector Xavier Monsegur, an unemployed Puerto Rican father-of-two, living in public housing project in New York’s Lower East Side, has been helping the authorities on both sides of the Atlantic identify members of the LulzSec and Anonymous hacktivist groups and bring them to justice.
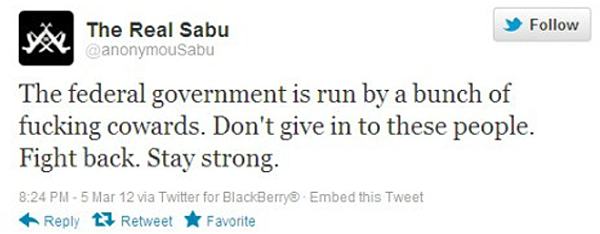
And how did Monsegur do that? Well, on the internet Monsegur didn’t call himself “Hector” or “Xavier”. Instead, he styled himself as “Sabu” – a prominent mouthpiece for the hacktivist community.
He was regularly seen tweeting – encouraging hacktivists to attack websites and goading the authorities on their inability to determine his true identity.
And what those hacktivists didn’t know (until his arrest was made public in 2012) was that Sabu was really working for the FBI.
Wired reports that Monsegur is due to be sentenced later today, and that because he was an “extremely valuable and productive cooperator” the authorities are calling for a federal court to sentence Monsegur to time already served – a mere seven months.
According to documents acquired by Wired, Monsegur provided information which resulted in the arrest and eventual conviction of members of the notorious LulzSec gang including Ryan Ackroyd (aka “Kayla”), Jake Davis (aka “Topiary”), Mustafa Al-Bassam (aka “T-Flow”), Darren Martyn (aka “pwnsauce”).
In addition, Monsegur helped the authorities identity and bring to justice Jeremy Hammond (aka “Anarchaos”), Ryan Cleary and Donncha O’Cearrbhail (aka “palladium”).
Prosecutors claim that Monsegur’s evidence also led them to another individual, Matthew Keys, who is currently charged in California with allegedly conspiring with Anonymous to attack the computer systems of Tribune Company, his former employer.
The moral of the story?
Well, if you’re a hacker be very careful who you trust on the internet. It could be that the people who you think are on your side, have really been convinced by the Feds to help them instead.
And if you’re a hacker who happens to be caught by the authorities. The lesson here is to co-operate with them – after all it might reduce your sentence and make life an awful lot more comfortable in the future.
The real moral of course is very simple. Don’t break the law in the first place.



Wait until sentencing to see how it turns out.
Cleary was jailed for 32 months
Davis for two years
Ackroyd for 30 months
Al Bassam was given a 20-month suspended sentence.
Avunit was never identified
Darren Martyn & Donncha O Cearbhaill seem to have gotten no jail time at all.
Jeremy Hammond (the really political one) maximum of ten years in jail.
He was also arrested before for…..Anti-Nazi protesting, altercation with anti-gay protesters, Protesting Holocaust Denier David Irving, among others including anti-war stuff and of course stratfor.
Wait to see how Sabu's sentencing goes before claiming "The lesson here is to co-operate ".
Even the most innocent man's lawyer will tell him to say nothing. Everything will be used against him. The slightest mistake by him may be used to throw him in jail as he can be proven to be lying and thus be totally "discredited".
http://www.kirkpiccione.com/10-reasons-not-talk-police/
Sabu "walked free" then
https://www.youtube.com/watch?v=SRyI9oSBbUo
http://www.theguardian.com/technology/2014/may/27/hacker-sabu-walks-free-sentenced-time-served
The lenient sentence, handed down by a New York judge on Tuesday, amounts to seven months in prison last year. It was a reward for what the judge called Monsegur's “extraordinary cooperation” with authorities, leading to the arrest and conviction of numerous other members of the hacking collectives.
Actually, the moral is it's okay if you break the law, so long as you agree to encourage others to do the same, then rat them out.