GRAHAM CLULEY
The company's rapid remediation and mitigation measures saved thousands of small and medium-sized businesses, saved them from suffering devastating impacts to their operations, ensured business continuity, was never a threat, nor had any impact to critical infrastructure.
Tut tut tut tut tut!
CAROLE THERIAULT
Go back about your business, people! It's fine!
Unknown
Smashing Security, Episode 235: Rival Returns, TikTok Grows, and Get Her Defaced with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security, Episode 235. My name is Graham Cluley.
CAROLE THERIAULT
And I'm Carole Theriault.
GRAHAM CLULEY
And Carole, this week we have joining us somebody who hasn't been on the show before, but they are a technology journalist and author of some renown. It is Chris Stokel Walker.
Hello, Chris.
CHRIS STOKEL WALKER
Hi, thanks for having me.
CAROLE THERIAULT
Thanks for coming on. I mean, you've done probably more writing than we ever have in the whole 235 episodes.
CHRIS STOKEL WALKER
I hire a whole load of monkeys and typewriters. That's the thing that people don't know is I outsource a lot of it.
GRAHAM CLULEY
Because you're well known for having written a book about YouTube, aren't you? But more recently you've been writing another book.
CHRIS STOKEL WALKER
Yeah, well, I wrote a book about YouTube, Graham. I wouldn't say I'm well known for it because books don't sell.
But yeah, I wrote a book about YouTube because I wanted to justify the amount of time that I spent on YouTube. And then suddenly TikTok took over my life in the same way.
So I needed to do the same thing so that my girlfriend didn't shout at me. So I have a book coming out on TikTok on July 22nd.
GRAHAM CLULEY
And have you managed to keep this girlfriend despite spending so much time on TikTok?
CAROLE THERIAULT
Or does she love TikTok too?
CHRIS STOKEL WALKER
Well, this is the thing, Carole. She spends more time on TikTok than I do.
CAROLE THERIAULT
You have chosen smartly.
CHRIS STOKEL WALKER
Well, have I? I mean, we sit on the sofa and then just suddenly I hear this music that I hear on TikTok about a year ago.
And then suddenly I'm saying, you are on there all the time now. So what's happening?
CAROLE THERIAULT
Okay, but I've never ever been on TikTok in my life.
CHRIS STOKEL WALKER
No, nor me.
CAROLE THERIAULT
That is not out of pride. Well, maybe a little tiny bit.
GRAHAM CLULEY
I think it's a generational thing, Carole. I think TikTok has passed us by.
CHRIS STOKEL WALKER
67% of people on TikTok are over the age of 25. That is a data point in my book that TikTok does not want the world to know.
But because I have sneaky sources, I know that sort of stuff.
CAROLE THERIAULT
What about over 40?
GRAHAM CLULEY
Ah. Pass. Over 50s.
CHRIS STOKEL WALKER
I've interviewed an 87-year-old for my book. So, you know, there is still hope for you yet.
CAROLE THERIAULT
And they just said, I've never heard of TikTok?
CHRIS STOKEL WALKER
No, he has millions of fans. It's obscene.
CAROLE THERIAULT
Okay, I'm gonna have to buy your book now. Everyone, we gotta do this. Let's thank this week's sponsors, 1Password, KnowBe4, and privacy.com.
Their support helps us give you this show for free. Now, coming up on today's show, Graham, what do you got?
GRAHAM CLULEY
Oh, I've got ransomware, which has been rampaging around the world.
CAROLE THERIAULT
And what about you, Chris? We know TikTok.
CHRIS STOKEL WALKER
Unsurprisingly, but I also have some other stuff about the future of tech.
CAROLE THERIAULT
And I'm visiting Is it Together, the new Twitter for some users? Let's find out. All this and much more coming up on this episode of Smashing Security.
GRAHAM CLULEY
Now, chums, in recent days here in the United Kingdom, we've had marvelous news shared with us by our glorious leader, Mr. Alexander Boris de Puthethel Johnson.
CAROLE THERIAULT
I was told I'm not allowed to call him BoJo because it's too affectionate. I was told that in the weekend.
GRAHAM CLULEY
Oh, what are you—
CAROLE THERIAULT
I was suggesting— the suggestion was shit, actually.
GRAHAM CLULEY
Oh, steady.
CAROLE THERIAULT
I was at a girls' weekend, so, you know.
GRAHAM CLULEY
Oh, I see. Well, anyway, apparently something called Freedom Day is approaching us, as opposed to Non-Wearing-Mask Apocalypse Day. I'm not sure.
Anyway, the UK government has decided, oh, we're a bit bored with all this sort of isolation and working from home and all that sort of nonsense.
CAROLE THERIAULT
And so they're going to say, basically, it's up to you, England, to sort yourself out.
GRAHAM CLULEY
We've been living like this, haven't we, for 18 months, right? And people have been homeworking.
And according to some reports, around about 3/4 of companies are looking to permanently shift to more remote work post-pandemic, which is a fabulous idea.
You know, I'm all in favour of that.
CAROLE THERIAULT
I think in some situations— Are you?
GRAHAM CLULEY
Well, yeah. Well, mostly because I've been working at home for the last 8 years.
CAROLE THERIAULT
You like your home as well, and you're happy there. So, yeah.
GRAHAM CLULEY
Exactly. I'm fairly happy here. But I think for some people, it does give you more flexibility. There are some benefits.
CAROLE THERIAULT
If you were our fellow podcaster, Javad, who has 4 kids, would you also think living at home for the last 18 months and trying to work full-time job would've been fun and easy?
GRAHAM CLULEY
I think that would be quite a challenge. Right? Put the children out in the garden or something, or up the chimney.
CHRIS STOKEL WALKER
That's not how it works, Graham. They're not rabbits.
GRAHAM CLULEY
It sounds maybe it was a family of rabbits breeding, you know, if they've got 4 kids.
But anyway, the thing is this, it's great, this idea of remote work and having the option, but if you are a business, you still need to be able to keep your users patched and keep their software updated.
GRAHAM CLULEY
Ensure that they stay secure. And there are products out there on the marketplace which help companies do that. Products one called Kaseya VSA.
And what that aims to do is to help you manage IT inside your company.
CAROLE THERIAULT
So they sell to companies saying this will help you and all your remote workers stay safer type thing.
GRAHAM CLULEY
Yeah, they sell it to companies. They also sell it to MSPs, which are managed service providers. So they sell it to other companies who will then take on their own customers.
CHRIS STOKEL WALKER
Capitalism.
GRAHAM CLULEY
Yeah, exactly. It's a great way to sell it, right? So even if your staff are working from home, you can monitor the security of their devices.
You can ensure that they get the latest security patches.
CAROLE THERIAULT
Sounds marvelous. In their own words, Kaseya says this maximizes efficiency, enhances security, and reduces costs.
GRAHAM CLULEY
I love marketing messages so much. So much.
CAROLE THERIAULT
Sounds marvelous.
CAROLE THERIAULT
What could possibly go wrong?
GRAHAM CLULEY
TM Graham Cluley.
CAROLE THERIAULT
Well, last Friday night, July 2nd, just as American companies were shutting down for their Independence Day holiday weekend.
GRAHAM CLULEY
Big weekend. Yeah.
CAROLE THERIAULT
Apparently quite a big deal in America. They get quite excited about that.
GRAHAM CLULEY
Well, yeah.
CAROLE THERIAULT
Well, companies on that day, they began to report if they were using Kaseya VSA, that they started to have some issues.
GRAHAM CLULEY
Okay, what?
GRAHAM CLULEY
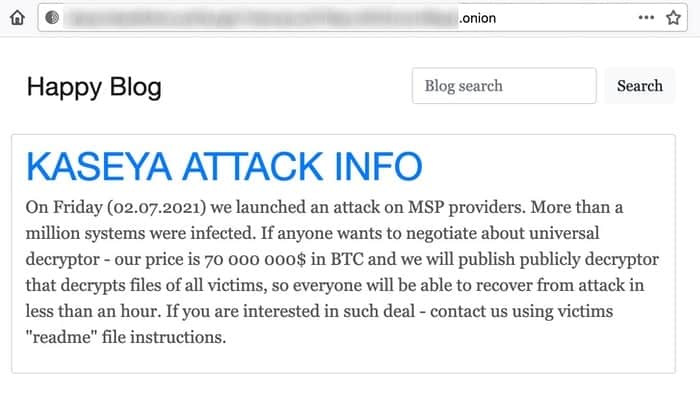
And it turned out that the REvil gang, or REvil gang, a ransomware gang, had exploited a vulnerability in Kaseya VSA, in that software, to install ransomware onto companies' PCs, encrypting their data, locking them out of VSA, and demanding a ransom.
There were victims around the world. So we came to when you wouldn't want it to happen.
CAROLE THERIAULT
It sounds very exciting, but it sounds also like very typical ransomware stuff.
GRAHAM CLULEY
Not exactly, no, because usually what happens is you'll hear a report of one company being hit by ransomware or another company. And those are fairly common occurrences.
But what happened here was a fairly simultaneous attack against hundreds.
CAROLE THERIAULT
Zero-day plus ransomware means wonga wonga? Is that what you're saying?
GRAHAM CLULEY
Right, right. Okay.
CAROLE THERIAULT
It took 'em a while to figure that one out actually. If I were a ransomware guy, I would've figured that way earlier. I'm just saying.
GRAHAM CLULEY
Yeah, but you have to find a vulnerability in a piece of software that loads people into.
CAROLE THERIAULT
There's not many of those. You're right.
GRAHAM CLULEY
Yeah. Well, it's caused problems. So there's a Swedish supermarket chain, which is either called Co-op or Coop, which we might know ourselves.
CAROLE THERIAULT
I always go to the Co-op.
GRAHAM CLULEY
Yeah, right. Well, they shut down about 500 of their stores.
GRAHAM CLULEY
Cash registers were on the blink. Self-service tills weren't working. Meatballs, mashed potatoes, and lingonberries went unsold.
When it began to open some stores, people asked, "Well, look, I can see you've got some sausages there, and some bacon, and some mashed potato.
Could you pay for that on the smartphone?"
CHRIS STOKEL WALKER
Can you pay for that online? They also got rid of lots of strawberries, because they couldn't sell the strawberries.
GRAHAM CLULEY
That's right.
CHRIS STOKEL WALKER
Which is fantastic.
CAROLE THERIAULT
What do you mean, Chris? By get rid of, they didn't just throw them out or give them to the rats. They hand them out to people.
CHRIS STOKEL WALKER
They gave them away. You could have free strawberries.
CAROLE THERIAULT
Oh, that's very good, Co-op. Very good.
GRAHAM CLULEY
Is there a Bergman film Wild Strawberries or something. Yes, there you go. It's a little bit of culture for you. Yes, here on Smashing Security. Not the Swedish supermarkets, though.
Schools and kindergartens in New Zealand, they were affected as well, right?
CAROLE THERIAULT
So a global attack, people all over got hit.
GRAHAM CLULEY
Awful.
And this gang, the REvil gang, largely made up of Russian-speaking hackers, they were demanding $45,000 worth of bitcoin to decrypt every infected PC, or if you want to decrypt your entire domain, $5 million.
CAROLE THERIAULT
But that's really shit because loads of companies that got hit wouldn't even have that cash lying about if they were small businesses.
GRAHAM CLULEY
Oh, you don't think that's a very good idea? You don't think that's good? You don't think that's a good thing that's happened?
GRAHAM CLULEY
Oh, I see. You're not applauding the capitalism and the entrepreneurialship of these ransomware attackers. Oh, okay. All right. Interesting.
Now, kindergartens don't have that kind of money.
CHRIS STOKEL WALKER
I think they do.
GRAHAM CLULEY
They have that.
CHRIS STOKEL WALKER
You do, right? Because have you ever seen a kid count? You know, if you can imagine them at the play tills and they're just going, "Yeah, here's $45,000.
Yeah, that's absolutely fine."
GRAHAM CLULEY
I'm not sure if that would be acceptable to the ransomware gang. So how did this happen?
Well, as Carole has already alluded to, the hackers exploited a zero-day vulnerability in Kaseya's software, which was running on-premises, planting a malicious update that then got rolled out to the users.
Now, I said the vulnerability was a zero-day, but actually, Kaseya did know about the vulnerability. They just hadn't rolled out a patch for it yet.
They had been told about the vulnerability a while before by a bunch of researchers called DIVD. And DIVD is the Dutch Institute for Vulnerability Disclosure.
I don't know if they're a real institute. Anyone can call themselves an institute.
CAROLE THERIAULT
Right. And they got in touch with them and it was suitably ignored. No, no, no.
GRAHAM CLULEY
It wasn't ignored. No.
GRAHAM CLULEY
So the Dutch researchers got in touch with Kaseya and said, "Hey, we found a bit of a problem."
GRAHAM CLULEY
"We think this could be exploited by bad guys."
GRAHAM CLULEY
"Maybe you want to patch against this." And so Kaseya were going through the back and forth of, "Okay, thank you for telling us about this. We're exploring it.
Oh, we think we fixed it, here's our patch, can you tell us if our patch is working properly?" So there's all this going back and forth.
GRAHAM CLULEY
So it hadn't quite been properly fixed or publicized, but somehow the hackers found out about the vulnerability as well. Now, whether that was coincidence.
CAROLE THERIAULT
Yeah, exactly. I've already got conspiracy hat on. I'm like, I wonder if there's a leak somewhere.
GRAHAM CLULEY
Because, well, that's an interesting question, isn't it?
Because potentially, if you're charging millions and millions to have companies' systems decrypted by ransomware, a gang would potentially pay you a few million dollars for a vulnerability like that, right?
GRAHAM CLULEY
If they saw the potential.
So there could have been someone on the inside who did it, or maybe the hackers actually were intercepting the communications between the security researchers and Kaseya, or maybe they'd compromised Kaseya.
Or maybe they're disgruntled employee from one of the places and they haven't changed any of the usernames and passwords, so they still have full access.
Or maybe it really is just a coincidence.
CAROLE THERIAULT
Quinky dinks.
GRAHAM CLULEY
You know, it's a bit like inventing television in the same place simultaneously.
CAROLE THERIAULT
Columbo wouldn't believe it was a coincidence, would he?
GRAHAM CLULEY
I was watching some Columbo a couple of days ago.
GRAHAM CLULEY
So good. I did it when I was 30 as well. It's not an age thing. If I've got the choice between watching Columbo and TikTok, I'm going to watch Columbo.
CHRIS STOKEL WALKER
Yeah, it's probably an opportunity to create a Columbo account on TikTok. Is Peter Falk dead?
GRAHAM CLULEY
Yes, I'm afraid so. He got very, very ill towards the end. And there were stories that his widow was preventing his kids from seeing him. Oh, I think he had Alzheimer's or something.
CHRIS STOKEL WALKER
This turned depressing.
CAROLE THERIAULT
Don't worry, it's a comedy show. It'll be fine. We'll do some weird turnaround in a second.
CHRIS STOKEL WALKER
Keep it light, you said.
CAROLE THERIAULT
Anywho, Graham, you were saying.
GRAHAM CLULEY
So, so. Where did the bad guys get the vulnerability? Did they find it themselves? Was it given to them by the Russians? Or somebody else?
And was there a significance to the attack happening just before July 4th? Because one of the things which the malware does is it changes the password on your computer.
Do you know it changes the password to—
CAROLE THERIAULT
Bastards!
GRAHAM CLULEY
Jesus! It changes it to 'dtrumpforever,' or maybe 'dtrump,' for all I know.
CAROLE THERIAULT
Oh, interesting.
GRAHAM CLULEY
Hard to know what that's related to.
CAROLE THERIAULT
So do you think it's kind of trying to do a pro— pro—
GRAHAM CLULEY
I don't think it was Donald Trump who did the coding somehow. I don't think he was the programmer.
He does claim his son Barron is very, very skilled at computers, but I don't think—
CHRIS STOKEL WALKER
By that, does he mean that he plays Fortnite? Is that what Barron Trump is skilled at computers about?
GRAHAM CLULEY
Oh, it could be, couldn't it? It also set a registry key, Black Lives Matter. I don't know what all the relevance of this was, but this was in the code.
CAROLE THERIAULT
It sounds very disinformation-y. It sounds someone who was just going, blah, blah, blah, blah, blah, blah. Let's just say loads of stuff. Stuff to confuse everybody because we can.
GRAHAM CLULEY
It could be that. Now, we are recording this podcast 4 days after the attack, and much has been written about it already. It's made really big news.
Kaseya, of course, are trying to put some spin, some positive spin on the story to rescue its reputation.
CAROLE THERIAULT
Hey, don't worry, your information has not been stolen yet.
GRAHAM CLULEY
Well, let me tell you the headline of the press release.
CAROLE THERIAULT
Can you do it in a really happy, supportive voice, trying to make me— you would a child to say, this is a good thing.
GRAHAM CLULEY
Okay. Okay. Kaseya responds swiftly to sophisticated cyberattack, mitigating global disruption to customers. That sounds good news, doesn't it? Yeah.
Companies working alongside agencies and leading incident response teams to support impacted small and medium-sized businesses.
The company's rapid remediation and mitigation measures saved thousands of small and medium-sized businesses.
CAROLE THERIAULT
We're amazing!
GRAHAM CLULEY
Oh yeah, save them from suffering devastating impacts to their operations, ensured business continuity. Don't mention the ones who got hit. Huzzah!
This attack was never a threat nor had any impact to critical infrastructure.
CAROLE THERIAULT
Go back about your business, people. It's fine.
CHRIS STOKEL WALKER
D-Tron forever.
GRAHAM CLULEY
Well, so that all sounds marvelous. I think IT is considered critical infrastructure actually by the NSC in the States, but the spin continued and they released a video.
Kaseya's CEO, a guy called Fred Vockler.
CAROLE THERIAULT
God, can I just guess? Can I just guess before you say what it was?
Is he talking to camera and he has no tie, but a shirt on with a button open, bit Tony Blair-y, and his elbows are on the desk. He's on a desk, 'cause it's serious.
There's a desk between him and then he's talking right to camera saying this is a serious— I haven't seen this. I'm just guessing.
GRAHAM CLULEY
He's wearing a polo shirt, actually, because he's got some impressive guns, I suspect. Oh, not guns as in firearms. Well, maybe he does. Who knows?
But, you know, he looks he might do CrossFit. You know, he looks a bit beefy.
CAROLE THERIAULT
Maybe he does the Peloton with his hands.
GRAHAM CLULEY
He might do. And he's there in his corner office, and he's— what the one thing he wants to emphasize is that Kaseya has 40,000 customers, but only 50, he says, have been affected.
Only 50. And they put out a press release about this as well.
CAROLE THERIAULT
Does he work out the stats for us? Like the percentage for that? It's like 0.001.
GRAHAM CLULEY
It is a small percentage, but of course many of Kaseya's customers are managed service providers.
CAROLE THERIAULT
Representing.
GRAHAM CLULEY
Right, yep. And apparently they support around about 1 million businesses around the world.
CAROLE THERIAULT
This is where a positive spin bites you in the, you know where, eh?
GRAHAM CLULEY
So they're quite right in a way in saying maybe very few of their direct customers were affected.
So they are saying that of the around about 1 million local and small businesses that are managed by Kaseya's customers, brackets, their MSPs, only around 800 to 1,500 have been compromised.
And that sounds awfully like they're blaming their MSP customers rather than their own buggy software for this problem and for the screw-up.
So it's really hard to come out with accurate numbers as to how many businesses have been affected.
We know about the Swedes, we know about the Kiwis, we know about some other companies around the world who've been hit by this.
Really, the only group which truly knows the scale of the attack is the REvil ransomware group themselves.
They are saying on their website, because of course, like all good ransomware gangs, they run a website on the darkweb where they publicize their attacks and issue press releases.
They are saying—
CAROLE THERIAULT
Do they have one of those little thermometers that we used to have in schools where it's like, we've almost reached our goal of infecting this many people?
GRAHAM CLULEY
Like a telethon.
CAROLE THERIAULT
Yeah, yeah, exactly.
GRAHAM CLULEY
They don't have that. But they're saying round about a million systems were infected.
And what they've very kindly offered to do is they said, look, we do have a way of producing an uber decryption tool, not a decryption tool to do with taxicabs, an uber decryption tool, a sort of motherfucker decryption tool.
Well, okay, mother-flipping decryption tool that will decrypt files of everybody. And they say you can buy this for a mere $70 million worth of bitcoin.
CAROLE THERIAULT
Crowdfunded, people, is what they're saying. Oh my God, I should totally be a ransomware hacker.
GRAHAM CLULEY
You should work in their marketing department.
CAROLE THERIAULT
I should. God.
GRAHAM CLULEY
Chris, do you think Carole would be any good if she were to publicize either our podcast or maybe ransomware gangs on TikTok?
CHRIS STOKEL WALKER
I think so.
I think it would run the risk of undoing a lot of the work though, because isn't the whole point of this that you don't really draw attention to it until you're ready to spring the, hey, here's all of our customers tied up and things like that.
Whereas, yeah, Carole seems like a hype woman. She's very, you know—
GRAHAM CLULEY
Tell me about it. You should hear her plug in her other podcast, plug in her art website. Constant. All the time, absolutely constant.
CHRIS STOKEL WALKER
Me, me, me.
GRAHAM CLULEY
Yeah. Now Reuters asked Fred. Fred is— Is he like Cher?
CAROLE THERIAULT
Is he like Cher? He just has one name.
GRAHAM CLULEY
Yeah, exactly. Fred is now saying, if only I could turn back time.
CAROLE THERIAULT
If I could find a way.
GRAHAM CLULEY
He's refused to say to Reuters whether he is prepared to talk to the hackers or not. He says, I can't comment yes, no, or maybe.
CAROLE THERIAULT
Yeah, because that's because he's being locked down by the board who is saying, wait till legal, we're waiting for legal.
GRAHAM CLULEY
He says no comment on anything to do with negotiating with terrorists in any way.
GRAHAM CLULEY
So, you know, and of course, many governments are now trying to discourage companies from negotiating, aren't they, when they get hit by ransomware attacks? Good.
Do you think it's good?
CAROLE THERIAULT
Yes, I do think it's good. I realise that it can be very difficult. Like, I could agree that there's a lot of grey and it's not an easy decision.
It's not black or white, but— Well, what if it means you lose your job, Carole?
GRAHAM CLULEY
You, your business goes kaput because you got encrypted one day and you can't get your data back and your backups are screwed.
CAROLE THERIAULT
But I have to pay them what money?
GRAHAM CLULEY
Yeah, you have to pay them, let's say, £2,000 and you can get your data back.
CAROLE THERIAULT
Yeah, well, I hear you, right? I'd like to say no, you know.
GRAHAM CLULEY
Would you say no?
CHRIS STOKEL WALKER
Probably.
CAROLE THERIAULT
I'd probably just start a new company the next day.
GRAHAM CLULEY
What about you, Chris? Would you say no?
CHRIS STOKEL WALKER
Well, I'm fascinated by ransomware negotiators, which seem to have just popped up out of nowhere and are getting a lot of press.
So I think I would probably say yes, because I more than anything want to see how it works.
GRAHAM CLULEY
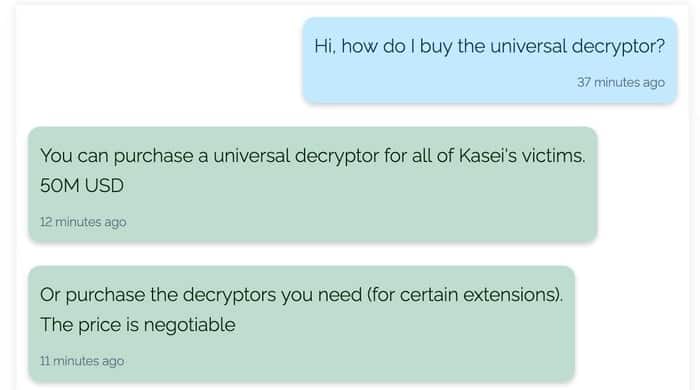
Because someone has contacted them already and said, "How can we go about buying this big decryptor?" And they said, "Well, look, for you, $50 million." So they already cut $20 million off the price to one person.
CHRIS STOKEL WALKER
You never negotiate against yourself.
CAROLE THERIAULT
Yeah, yeah, exactly. So they basically, they want $5 mil. They're just—
GRAHAM CLULEY
No, they want 70.
CAROLE THERIAULT
They want 70. Yeah, they wanted 70. Like, what they want and what they're gonna end up saying okay to.
GRAHAM CLULEY
But I think if you could make friends with them, if you could find some common ground, like if you found out they were Barbra Streisand fans, for instance, then they might feel a little bit more prepared to help you out.
That's what I see people doing all the time in these movies when someone's taken hostage.
CHRIS STOKEL WALKER
But these people are terrorists. Fred says they're terrorists.
CAROLE THERIAULT
What they always do is send pizza, right? It's like, can I get you some food? Can I get you some pizza? That's what terrorist negotiators seem to do, in my view.
GRAHAM CLULEY
I think you're mixing up Just Eat with— Chris, what have you got to talk to us about this week?
CHRIS STOKEL WALKER
It's TikTok, and TikTok is sending user data to China, reports CNBC.
CHRIS STOKEL WALKER
Which is shocking, except for the fact that I sort of said this 3 months ago in a separate story, which I think is interesting because it shows how much we need to pay attention to this thing that we don't yet pay attention to.
And it feeds into this broader issue that we're seeing with Didi in China, the Chinese tech giant that is kind of being cracked down on by the ruling Communist Party because it committed the heinous crime of daring to send some of its Chinese user data to the US.
So we kind of just have that Spider-Man meme where everybody is pointing at each other and saying, don't send our user data outside of our countries.
CAROLE THERIAULT
So TikTok is owned— so you tell me if this is true or not true, because I really— I've never been on TikTok in my life. It's owned by ByteDance, am I right?
CHRIS STOKEL WALKER
It is. So it's owned by ByteDance. They have a lot of their engineering team in China. They're trying to diversify that. They're hiring a lot of people in Dublin.
They're hiring a lot of people across Europe and in the United States, basically to start developing their apps. But the majority of their expertise is still based in China.
And so you are bound, unless you want to not patch security issues or anything like that, you're bound to have some data going back to China.
But because of Trump forever, we seem to have this massive fear, I suppose, of data moving offshore. And that's not just China and the US doing that with each other.
You know, Schrems II in Europe is all about moving data away from the European Union.
And it typifies this thing where we have a global internet and lots of people saying, well, actually, I like all the good bits of the global internet, but I don't want you to be able to operate the global internet and all the services that run on it in a truly global way.
I just want you to have everything within 30 miles of me so that I can tap the person on the shoulder that is in control of my data and say, give me my data or something.
I don't really know what the goal is.
GRAHAM CLULEY
So what sort of user data is TikTok actually collecting? Because I've never been on TikTok.
CAROLE THERIAULT
Oh my God, I'll look on my phone while you're talking. Because I'll see what Apple tells me it says.
GRAHAM CLULEY
Okay. I've never been on TikTok, but it's mostly people doing dances and little short, 1-minute video. Is that correct?
CHRIS STOKEL WALKER
Yeah, so basically all the videos are less than a minute long until basically this week when they've started to open it up to all users to be able to upload videos 3 minutes long or less.
CAROLE THERIAULT
Oh, really? So they've trebled their space for each person.
GRAHAM CLULEY
Isn't that going to be rather more tiring for people doing crazy dances? If you do them for 3 minutes rather than 1 minute.
CHRIS STOKEL WALKER
For those 50 and 87-year-olds that are doing those dances, it is. But thankfully people are evolving and doing more than just dances. People are often now pointing at things.
Some of the old persons—
GRAHAM CLULEY
I can do pointing. Pointing isn't a problem.
CHRIS STOKEL WALKER
Well, this is the thing.
There is an old person's playbook for TikTok, which is basically if you're not gonna do the dancing, then the first video that you do is you point at stuff and that's apparently a TikTok, which I never really get.
CAROLE THERIAULT
Well, I've just looked up on my phone, just, you know, you were asking what kind of data do they take from you, right?
So listed on Apple's privacy section, data used to track you: purchases, location, contacts, search history, identifiers, diagnostics, financial info, contact info, user contact, browsing history, and usage data.
And then underneath that, it has a data not linked to you: usage data. So they're in both categories.
GRAHAM CLULEY
So hardly anything. They're hardly collecting anything at all.
CAROLE THERIAULT
They're collecting nothing.
CHRIS STOKEL WALKER
Nothing.
GRAHAM CLULEY
And presumably the stated reason for collecting this information is to target advertising.
CHRIS STOKEL WALKER
Yeah, so the reason that they do that is basically they want to serve you better adverts, and also in order to improve their algorithm, which is one of the big secret sources that has made TikTok so incredible.
So by the power of mind reading, it will know exactly what Carole wants when she downloads the app and starts opening it.
GRAHAM CLULEY
Because they know what videos she's enjoyed before, and so they'll give her more of that, or other videos that people who liked the same videos enjoyed.
So it becomes stickier content in a way.
CHRIS STOKEL WALKER
Exactly.
And because of the fact that it is shorter videos, they get more data points on you because you are engaging with more videos over, say, an hour session on TikTok than on YouTube, where the people rabbit on for so long that you actually get halfway through a video and they've still not got past the first ad break.
GRAHAM CLULEY
So there's also this concern about TikTok white labeling its technology and maybe coming out with different versions of TikTok, or what's the concern here?
CHRIS STOKEL WALKER
So this is partly the benefit of having such a successful app.
You know, all those videos that my girlfriend watches so that TikTok can build up a minute detailed profile of what she's interested in has helped fuel the algorithm and make it quite so powerful that now other companies want in on it.
And TikTok's parent company, ByteDance, has realized the power and the potential money-making in that. So they could go down two different routes with all that data.
They could lock it up and demand $700 million to decrypt it or whatever it is, or they could sell the algorithm as a white-label product to other companies.
So you too can have the TikTok algorithm or a probably cut-down version of it, because why would you give away the farm if you've got an app that gives you 732 million monthly active users, and you can then put this version of your algorithm into your company, or your app, or your website.
So they're starting to develop this, and it's interesting because it touches on this idea that Graham's story looked at, which is if you white label lots of things from the same company, you run the risk of concentration, which is great if everything goes right.
So strawberries for everybody at an affordable price in Swedish supermarkets when point of sales service works correctly. But when it goes wrong, it goes wrong catastrophically.
And I think some of the more conspiratorially minded people who worry about the invasion of Chinese tech on the rest of the world will be looking at this and maybe worrying slightly.
CAROLE THERIAULT
I remember just the New York Times and a few maybe American papers were saying, where's your data going? Should your kids be on TikTok?
And there was this whole hoopla about it, but then it died down.
CHRIS STOKEL WALKER
Yeah, well, that's just Josh Hawley, who is the guy who stuck his fist up at the January 6th rioters. So you've got to trust that guy.
That's him basically saying that China and TikTok is a deep state plot to try and poison your kids in the same way that, I don't know, the West did that with McDonald's to the Soviet Union.
I don't know, was that a deep state plot?
GRAHAM CLULEY
It's a bit television or jazz. There's always something in every generation, isn't there, which is going to destroy us all.
CHRIS STOKEL WALKER
Yeah, and apparently that's Charli D'Amelio drinking coffee from Dunkin' Donuts and doing the Renegade. I don't know, to me—
GRAHAM CLULEY
Sorry, I didn't understand any of that. Was that all TikTok meme stuff?
CHRIS STOKEL WALKER
That was all TikTok stuff.
GRAHAM CLULEY
Yeah, okay. Oh, good. I feel good about it going over my head now, right?
CHRIS STOKEL WALKER
There is this idea that some people seem to have that there are spies in China secretly watching your daughter do silly dances in her bedroom.
And the argument that I always have against that is your daughter already does the silly dances and already posts them on Instagram, YouTube, and Facebook, and probably Twitter as well.
So why exactly would they need to go on TikTok to find that? There's this weird leap that I never fully get.
The future of tech is a really important discussion that we need to have and whether or not we're going to have a Silicon Valley-based technology ecosystem for the next 25 years, just as we had for the last 25 years, which those of us outside of the US may feel is not necessarily the best way to do things, or whether or not we have a Chinese-focused future of tech, which again, has its major issues.
I feel like both are on polar opposite ends of a bad spectrum, and we should be somewhere in the middle.
GRAHAM CLULEY
Chris, if I was to pin you down and say TikTok, good or bad, what would your answer be?
CHRIS STOKEL WALKER
TikTok, good. It's—
CHRIS STOKEL WALKER
Well, YouTube also good. But I am generally a tech skeptic. So overall, I think that these things are fine. I dislike the fact that YouTube—
CHRIS STOKEL WALKER
Pornhub, excellent, obviously. Clearly.
CAROLE THERIAULT
Great content.
CHRIS STOKEL WALKER
Again, don't tell my girlfriend.
GRAHAM CLULEY
She's watching it already, Chris.
CHRIS STOKEL WALKER
Yeah, I mean, I agree 100%. Tech companies are terrible. They're run by terrible people. Mark Zuckerberg should not have filmed himself on a waveboard on July 4th.
GRAHAM CLULEY
I just saw that.
CAROLE THERIAULT
I have not seen this.
CHRIS STOKEL WALKER
It's worse than Fred.
GRAHAM CLULEY
We'll put a link in the show notes, Carole.
CAROLE THERIAULT
Don't go click on that link, people.
CHRIS STOKEL WALKER
Do. You need to see it. If I had to see it, you do as well.
GRAHAM CLULEY
It's incredible.
CAROLE THERIAULT
No, I'm not drinking the Kool-Aid.
CHRIS STOKEL WALKER
So basically, the whole point of this thing is that TikTok and ByteDance are coming for the world.
There are serious issues around where we put data flows, and we're starting to see the opposite of that happening in that the West is generally worried about data being shipped to China with TikTok and also Zoom earlier in the pandemic, and the idea that our calls are being routed through China's servers, which is not ideal, I don't think.
GRAHAM CLULEY
Chris, if you want to complain about that, I think you've gone about this the wrong way. You shouldn't have written a book about it.
You should have made a series of 1-minute-long videos and posted them up on TikTok.
CAROLE THERIAULT
Yeah, where you're breakdancing. You could rap it.
CHRIS STOKEL WALKER
But I'm doing both. I wrote the book, and then now I'm chunking the book up into 1-minute-long videos that are being seen.
CAROLE THERIAULT
You're kidding.
GRAHAM CLULEY
I think he only wrote the book to promote his TikTok account, is the truth.
CHRIS STOKEL WALKER
Yes, exactly.
CAROLE THERIAULT
How many followers do you have, Chris?
CHRIS STOKEL WALKER
Not enough at all. I only have 50, because I'm not very good at TikTok. I'm old. I'm 32. So yeah.
GRAHAM CLULEY
Point at something. Carole, what's your story for us this week?
CAROLE THERIAULT
Okay, so imagine there's a brand new online service, social service that becomes available online. TikTok. Oh, TM. That's a TM, isn't it? Say, a new social media platform.
And let's say in your echo chamber, everyone is abuzz about it. What would be your modus operandi? Would you sign up because, you know, FOMO?
Would you proceed with caution, reading the terms and conditions, being careful about it?
GRAHAM CLULEY
No, that sounds boring. No, if my friends were on it and if I thought this would be a fun place to hang out, then maybe I would check it out and compare it with other places.
CAROLE THERIAULT
With your master email address?
GRAHAM CLULEY
Yeah, sure, why not? Or maybe I'd create, 'cause I've got my own domain name, I could create anything in the— Oh, you're so cool. User bit.
CHRIS STOKEL WALKER
Wow. The power.
CAROLE THERIAULT
Oh, he's amazing. Chris, what about you?
CHRIS STOKEL WALKER
I would stay away. I'm one of those who did not join Yo, sadly.
GRAHAM CLULEY
Oh, the Yo app.
CHRIS STOKEL WALKER
And I feel like I did not miss out. I also didn't join the Matt Hancock app, and thank God I did not.
CAROLE THERIAULT
What's the Yo app? It just said yo? It just said yo to people. Yeah, I remember that.
CHRIS STOKEL WALKER
That was hugely popular amongst a certain group of BuzzFeed reporters about 5 years ago.
CAROLE THERIAULT
It's so clever because it does nothing.
GRAHAM CLULEY
Yeah. Yeah.
CAROLE THERIAULT
Meta, meta, man, meta. Because, okay, so there's that saying, the reason I'm asking this, right, is there's that saying, the early bird gets the worm.
And I think that might be true for a few unpredictable internet instances, maybe buying bitcoin early, right?
But I would argue when it comes to tech and online service, the early bird, you know, all a flap because the marketing message resonates, or there's an incentive, or all my mates are doing it, Graham says, might just find themselves ensnared by online yuckiness.
Case in point, gentleman Graham and listeners. Let me—
GRAHAM CLULEY
What about Chris? Chris is a gentleman.
CHRIS STOKEL WALKER
I'm not loud.
CAROLE THERIAULT
He's a gentleman, right? Comma Graham, comma, and listeners. Gentleman.
GRAHAM CLULEY
I think, yeah, well, very formal.
CHRIS STOKEL WALKER
Thank you.
CAROLE THERIAULT
You're very, very welcome. Let me introduce you to what looks like a Twitter ripoff, Gettr.
Now this has been created by the former president's team, and they quietly launched a new social media platform basically in mid-June, and the big launch was going to be on Independence Day, July 4th.
And it was being billed as an alternative to big tech sites. So the name is Gettr and it advertises itself as a marketplace of ideas.
Okay, quote, "Fighting cancel culture, promoting common sense, defending free speech, challenging social media monopolies, and creating a true marketplace of ideas."
CHRIS STOKEL WALKER
Amazing.
CAROLE THERIAULT
Now, okay, first, is it just me? Okay, but Gettr, okay, spelled G-E-T-T-R, sounds a lot like "get her," right? Get the witch. Yeah, doesn't it?
Well, Gettr, I don't know, seeing all the accusations that have been made against the former president, you'd think they would have thought, seen that, or, you know.
But anyway, they apparently came from get, getting together.
GRAHAM CLULEY
Should have been grab her instead, do you think?
GRAHAM CLULEY
Yeah. Oh my God.
CHRIS STOKEL WALKER
What I like about this is that it seems to be trying to capture the kind of old school Twitter thing of, you remember when Twitter didn't actually have any vowels in it?
CAROLE THERIAULT
That's right. I forgot that.
CHRIS STOKEL WALKER
And if you look at the person who's behind it, Jason Miller, I'm kind of inclined to believe that the last time that he was on the internet was possibly when Twitter launched as twttr.
CAROLE THERIAULT
So according to Politico, Getter, the app, is apparently one of the highest profile projects of the pro-MAGA social media platform.
And it's largely fueled by a sense that Big Tech is attempting to silence conservative and pro-Trump ideology.
And, you know, to be fair, there is quite a lot of problems on that front, isn't there?
Because he's been banned from YouTube, he's been suspended by Facebook until 2023, and by Google, or Alphabet, actually, the parent company of Google.
GRAHAM CLULEY
Yes, but he did create that website from the desk of Donald Trump, didn't he?
CAROLE THERIAULT
That went away very quickly, didn't it?
GRAHAM CLULEY
Yeah, it disappeared after a couple of weeks. Yeah, no, no, come on, we mustn't laugh. Good for him to try.
CAROLE THERIAULT
He launched, right? Pre-launch, pre-independence day.
It wasn't actually smooth sailing because according to Mother Jones, there was spam comment left en masse below the Getter welcome message, which said, "Welcome to Getter and start a new journey," including— so the spam included things like anime porn and repeated copies of an image depicting Hillary Clinton's head photoshopped onto another woman's nude body.
So really mature. Phishing stuff done by some really high-class hackers, or I don't know, I don't want to use the word hackers. I don't know, online miscreants.
Basically, they just didn't have the right filters in place, the right protections.
CHRIS STOKEL WALKER
What was the app that was linked to the January 6th stuff that disappeared as well? It wasn't Gab, was it?
CAROLE THERIAULT
Oh yeah, we covered it, I think.
CHRIS STOKEL WALKER
This shows you though how likely Getter is to survive, isn't it? These weird alt-right apps.
CAROLE THERIAULT
Well, if you ask Steve Bannon, you know what he said? He called it a Twitter killer.
CHRIS STOKEL WALKER
No, Twitter killer.
CAROLE THERIAULT
Twitter killer. Now, do you want to guess what the initial trending topics on Getter when it launched officially were?
CHRIS STOKEL WALKER
DTrumpForever, hashtag Trump, Black Lives Matter.
CAROLE THERIAULT
No, funny. No, funny. No, no, more like hashtag virus origin. #NRA and #unrestrictedbioweapon. So fun stuff.
CHRIS STOKEL WALKER
They're not very good at hashtags, are they?
CAROLE THERIAULT
It's a long one, isn't it? So other than the spam stuff, there were one or two snafus maybe that happened during this launch.
So one is there's a remarkable similarity to Twitter, as you mentioned. This is again from Politico.
Republican state candidate Sean Parnell of Pennsylvania had over 175,000 followers on Getter as of Thursday afternoon.
Wow, that's impressive, despite only joining the platform on Thursday that same day.
GRAHAM CLULEY
Wow, that's amazing.
CHRIS STOKEL WALKER
Oh, sorry, did I cough?
CAROLE THERIAULT
And two, according to several media sources like Reuters, on July 4th, the day Getter was scheduled to be officially launched and was, it got hacked by someone called Juba Baghdad, or J-U-B-A Baghdad.
According to Insider, the accounts were first hacked around 8:30 AM Eastern Standard Time on Sunday, and the majority of the profiles returned to their previous state by an hour and a half later, by 10 AM.
And one of Getter's creators— I don't know if it was our Jason Miller guy that said this, but one of them, one of the guys there said the problem was detected and sealed in a matter of minutes.
And all the intruder was able to accomplish was to change a few usernames. Well, when I looked into it, it was a little bit more than that.
CNET reported that the account profiles were being defaced with pro-Palestinian messages.
And the attacks were— Mike Pompeo's account was affected, Steve Bannon's, Marjorie Taylor Greene, Harlan Hill, Sean Parnell, and Newsmax were hacked.
GRAHAM CLULEY
I'd say I'm quite pleased because a few days ago when I first heard about Getter, I thought, oh, that sounds interesting.
CAROLE THERIAULT
I'll go get an account.
GRAHAM CLULEY
Yeah, I'll go and get an account. And unfortunately, I failed to be able to create an account because it fell over with some kind of bug. Maybe it was too— possibly.
I don't know if they would have known that, but maybe it's just been too popular. It just couldn't stand all the interest.
CAROLE THERIAULT
Well, there's some people have been able to get 100,000 followers in just an afternoon, Graham. So if only you got on.
GRAHAM CLULEY
Yeah, exactly. But when I look at it, it is remarkably like Twitter. I mean, the whole design, the icons, almost everything.
If you go to someone's profile, it's just a complete ripoff. Is there not anything that can be done about it?
CAROLE THERIAULT
Twitter refused to comment in all the places I looked today, so I have not seen any comment from them at all on this point.
But interestingly, the guy that kind of did this whole hacky thing, Juba Baghdad, told Insider that although Getter fixed the initial bug, he was still able to scrape user data from individual accounts, including email addresses and birth years.
And he confirmed this by sharing the details of a test account Insider set up, right? And he said the whole attack took him 20 minutes to work and it was just for fun.
So that makes me worry about their security a little bit, guys. And thirdly, their poster boy, Trump, ain't a member, right?
And he's probably waiting to see what happens before he joins.
So I gotta think maybe he does have a brain cell or 5 because he's standing back to see if it's, he's not gonna go in half-cocked.
GRAHAM CLULEY
Maybe he can't remember his password. Maybe he's having the same trouble I had trying to create an account.
CAROLE THERIAULT
I think every journalist in the world are asking, has he joined?
GRAHAM CLULEY
So I saw a suggestion that some of these follow statistics may be a little bit bogus and that maybe Getter has been scraping Twitter for information.
And that maybe some of these accounts have been sort of set up to make people appear more popular than they really are.
GRAHAM CLULEY
And that maybe some of these accounts have been sort of set up to make people appear more popular than they really are.
CAROLE THERIAULT
Yeah, I think that is a very, very likely scenario.
CHRIS STOKEL WALKER
Shocking.
CAROLE THERIAULT
We're waiting for Twitter to comment. I think that would be, that's what I'm waiting for. I want to see what they say about this. Are they just thinking, who cares?
It's going to go away in a month.
GRAHAM CLULEY
I don't think Getter would be improved by having some short videos of people dancing or older people pointing at things.
CHRIS STOKEL WALKER
I think it would.
CAROLE THERIAULT
Dad dances?
CHRIS STOKEL WALKER
I mean, there's nothing more than I like than pro-MAGA people dancing.
GRAHAM CLULEY
Chris, is your girlfriend on Getter at all? Has she shown any interest?
CHRIS STOKEL WALKER
She is not. Although, as soon as she does, I will inform the relevant authorities. As long as she stays off, she's a good girl.
CAROLE THERIAULT
Keeper, Chris.
GRAHAM CLULEY
It's horrific, isn't it though?
CHRIS STOKEL WALKER
It's just terrible. It's a terrible, terrible thing.
CAROLE THERIAULT
It's terrible.
CHRIS STOKEL WALKER
All of these things are terrible and we should just— There is an argument to be made about the whole idea of, do you deplatform people?
And I covered a paper on this for New Scientist a couple of weeks ago, which looked at 11,000 YouTube channels and whether or not the audience for them moved on to these sort of alt-right platforms when they were kicked off YouTube, as they inevitably are for all sorts of terrible, terrible things.
And the example that they gave was Alex Jones, who then ended up on BitChute, which is kind of the getter of YouTube, I suppose.
And he went from having millions of followers there to hardly any on these places.
So is sunlight the best disinfectant, or is it actually a case of just shoving people off into the corner?
CAROLE THERIAULT
I don't know. Yeah, it's going to take a while to get right though, right?
I'd rather them struggle with who should they block and not block than let everyone, because I think the way that was going was getting extremely scary. I don't know.
But yeah, it's a complicated issue.
GRAHAM CLULEY
So, Carole, I assume you don't have a problem with the idea of Getter and sites it for that community if they feel they don't have a home elsewhere, but you have a problem with the security and the fact that it's been hacked and maybe they've been— there's some dubious—
CAROLE THERIAULT
And a cut and paste of Twitter, and it just seems a little bit half-baked. And I worry that they're going after an audience that may be less au fait with tech.
And may not be on the ball as much because they might be older or less used to this kind of stuff. And they might, you know, just do it.
I mean, I remember meeting companies that were basically trying to be a service for old people to say, we'll help you protect yourselves from ads and bad stuff on your computer.
Ad blocker, basically. Right? Free things that you can download as a plugin. And they would charge something 25 quid per user.
To old people because they would pay because they didn't know anything else because they weren't using the internet in the same way that we were.
CHRIS STOKEL WALKER
Is that the beta version of ransomware?
CAROLE THERIAULT
Yeah.
And I just think it's, you know, look after your parents, folks, no matter what side you're on all this, look after your parents and just make sure they're not doing crazy stuff on the internet.
GRAHAM CLULEY
Smashing Security is sponsored this week by 1Password, did you know that almost two-thirds of all IT workers admit to reusing enterprise secrets between different projects, creating a potential gateway for attackers?
1Password's new research report, Hiding in Plain Sight, reveals the breadth and depth of mismanaged business secrets code, passwords, credentials, and keys, and that secrets mismanagement is the next big cybersecurity threat.
Learn more by reading the full report at 1password.com/resources. And thanks to 1Password for supporting the show.
CAROLE THERIAULT
So what's a con game? It's a fraud that works by getting the victim to misplace their confidence in the con artist.
In the world of security, we call confidence tricks social engineering. And as our sponsors KnowBe4 can tell you, human error is how most organizations get compromised.
Where there's human contact, there can be con games.
It's important to build the kind of security culture in which your employees are enabled to make smart security decisions, and to do that, they need new-school security awareness training.
KnowBe4, the provider of the world's largest security awareness and simulated phishing platform. See how your security culture stacks up against KnowBe4's free phishing test.
Get it now at knowbe4.com/freetest. That's K-N-O-W-B-E and the number 4 dot com slash freetest. Think of KnowBe4 for your security training.
GRAHAM CLULEY
This episode is brought to you by the folks at Privacy.com.
Privacy lets you buy things online using virtual cards instead of having to use your real ones, protecting your identity privacy and bank information on the internet.
What a fantastic idea that is, and a great way of keeping your details out of the hands of the bad guys.
Right now, new customers will automatically get $5 to spend on their first purchase. All you've got to do is go to privacy.com/smashing to sign up now.
And thanks to privacy.com for supporting the show. And welcome back and join us at our favorite part of the show, the part of the show that what we like to call Pick of the Week.
CAROLE THERIAULT
Pick of the Week.
CHRIS STOKEL WALKER
Pick of the Week.
GRAHAM CLULEY
Pick of the Week is the part of the show where everyone chooses something they like.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security-related necessarily.
CAROLE THERIAULT
Better not be.
GRAHAM CLULEY
Well, my Pick of the Week this week is not security-related. My Pick of the Week this week is a computer video game which I have been playing with my son.
I'm a big fan of point-and-click adventure games. This one is a little bit old. I managed to pick it up because it was on special offer in the Nintendo Switch store.
It only cost me about £5.
CAROLE THERIAULT
Oh, because there was a deal, right? There was a deal recently. There was a flash sale or something.
GRAHAM CLULEY
There was a special deal. You can also get it for Windows, OS X, Linux, PlayStation, Android, iOS, etc., etc., etc. It is called Broken Sword 5: The Serpent's Curse.
GRAHAM CLULEY
Let me paint the scene. A painting is stolen in Paris. Henri, the art gallery owner, is shot dead in the robbery, but all is not as it seems.
You play the part of art insurance dude George Stobart, and with a little help from journalist Nicole Collard, you investigate the theft and the murder, and great fun it is too.
It's been around for years. I've never played it before, but we checked it out, and it's really intriguing.
CAROLE THERIAULT
Did your son like it?
GRAHAM CLULEY
Amusing. He does. He really likes it.
CAROLE THERIAULT
You got it for a fiver, right? How much would you pay now that you've played it?
GRAHAM CLULEY
Well, I obviously could always— I think it's probably worth about £25 or £30.
CHRIS STOKEL WALKER
I would say. Is it worth £45,000 per PC?
GRAHAM CLULEY
It is jolly good fun. And all of the— I don't know if this was true when it first came out, but certainly in the modern editions they've got all of the characters are also voiced.
So the words don't just come up on the screen, but they also have actors going, "I love it." There is a very amusing and very—
CHRIS STOKEL WALKER
Yeah.
CAROLE THERIAULT
That's my French impression. Yeah.
GRAHAM CLULEY
There's a very amusing Parisian waiter in it, who's— Well, he goes, "Mon Dieu!" No, he is just, "How dare you come into my restaurant and demand—"
CAROLE THERIAULT
The stereotypical, yeah. Parisian.
GRAHAM CLULEY
Yeah. Very Parisian kind of service. Stereotypes. I found it very funny. I found it quite entertaining. And that is why Broken Sword 5: The Serpent's Curse is my pick of the week.
Go and check it out.
CAROLE THERIAULT
Did you choose the number 5 so that you can actually have 4, 3, 2, and 1 in future? Future Picks of the Week is lame.
GRAHAM CLULEY
Well, I haven't played any others. This is the thing, right? This is my first introduction to the Broken Sword series. So cool.
Also, by the way, with this particular version, you get behind the scenes videos about the creation of the game.
And it's incredible the amount of effort which they go to, which as a former games programmer myself, I was very interested in watching how they had developed it and some of the, how the engine works.
Cool. Very, very interesting. Chris, what is your pick of the week?
CHRIS STOKEL WALKER
I originally had as my pick of the week a New Scientist story, but then I decided that that's a bit boring about security.
So instead, I thought I'd talk about the Netflix series that I'm currently binging, which is This Is a Robbery: The World's Biggest Art Heist.
CAROLE THERIAULT
I've seen this.
CHRIS STOKEL WALKER
Yeah, it's a theme going on here. It's brilliant. So 1990, The Boston Art Museum had the world's most expensive art heist. Priceless paintings. Well, they're not priceless, obviously.
They had a price because there is a number attached to it, but you get the idea. It was stolen by two people that have never been found.
And I found this really interesting because alongside doing sort of tech reporting, I sometimes do what in journalism is called general features.
Which is basically you sidle up to interesting people and say, "Well, what's all your life about then?" And get them to tell you all of it.
So I once went to Amsterdam to interview a guy who reunites stolen art with its owners. He's kind of like an—
CAROLE THERIAULT
Oh, wow.
CHRIS STOKEL WALKER
Yeah, he's an Indiana Jones character. This was obviously pre-pandemic, but it wasn't too long before the pandemic.
This guy was like, I've spent decades of my life reuniting works of art with their owners. I've never been able to crack this case. And the series is brilliant.
It's really interestingly told. It is, as with all Netflix series, probably one or two episodes too long.
CAROLE THERIAULT
So, yeah, because I think I heard this. I think I heard a podcast all about this art heist recently.
CHRIS STOKEL WALKER
I think I have too, yes.
CAROLE THERIAULT
But I haven't seen the Netflix show. Brilliant. Okay, that's so great. That's a great recommendation for me.
GRAHAM CLULEY
Is this the one— I think I remember seeing— is this the one where the thieves dressed up as policemen? It's late at night.
CAROLE THERIAULT
Yes! It is.
CHRIS STOKEL WALKER
And they somehow managed to get buzzed into a museum where there are really expensive Rembrandts, and the people involved who were patrolling the museum that night just happened to end up being tied up in a basement.
GRAHAM CLULEY
Yes! That's right. There'd been a lot of weed being smoked by some of them as well, I think. They'd maybe been quite relaxed. Jazz cigarettes, please.
CAROLE THERIAULT
Yes. And didn't they— I seem to remember from the podcast, the thing I found most impressive is they actually sawed the pictures out of the frames.
CHRIS STOKEL WALKER
They did. And this is the thing. They don't care. They don't care about the actual artwork.
They just kind of cut it out so that it can end up in some Russian or Irish or Italian oligarch's front room somewhere that they can just kind of show off to their mafiosi friends.
CAROLE THERIAULT
Oh, it's— what a great pick of the week though. Okay, I'm totally watching this.
GRAHAM CLULEY
Very cool. Carole, what's your pick of the week?
CAROLE THERIAULT
Mine, I don't want to let anyone down, mine's a podcast.
And not just a podcast, but an audio drama, and a very highly produced one with real actors and thriller-y plot and all sorts of wonderful nonsense. And it's called Passenger List.
Have any of you heard it?
CHRIS STOKEL WALKER
No, but I'm going after reading the website.
CAROLE THERIAULT
Oh, it's so cool, it's so cool.
So it just finished its second season, so I'm going to be careful about what I say here and just stick to the first season for those that haven't heard it.
I will say that I had to re-listen to the entirety of season 1 from last year. So I heard, I don't know, whenever it came out to keep up with the new season.
It moves fast and it assumes that you had lost no knowledge when you start season 2. So if you can binge it all at once, recommend it. So this is a Radiotopia podcast.
They produce tons of great content.
And it was created by John Scott Dryden and co-written by Lauren Shippen, who created The Bright Sessions, another fave audio drama podcast of mine.
Plus, the soundscape is awesome by Mark Phillips. And actors, you've got Kelly Marie Tran, you've got Colin Morgan, you've got Rob Benedict.
GRAHAM CLULEY
What's it about, Carole? What's it— give me the— hey, okay, talk about burying the lead. Tell me what the bloody podcast is about.
CAROLE THERIAULT
Ooh, pot kettle. Atlantic Airlines Flight 702 has disappeared mid-flight between London and New York. And there's 256 passengers on board.
Caitlin Le, she's a college student with a brother who was on the flight, right, is determined to uncover the truth because the plane has vanished.
Well, Le, aided by anonymous helpers, okay, sets out to chase down the leads and works her way through a sprawling web of conspiracy theories.
GRAHAM CLULEY
I think you'd like it, actually.
CAROLE THERIAULT
This would be a good audio drama for you to try. I think this would be— this is one I'd recommend for you. I'm not saying any more because I don't want to ruin anything.
GRAHAM CLULEY
But shrinking ray, shrinking— they were shrunk.
CAROLE THERIAULT
If you need an escape with some weird conspiracy theories to boot, check out Passenger List from Radiotopia. Links in the show notes as always.
GRAHAM CLULEY
Terrific. Well, what a great bunch of picks of the week, Chris. I'm sure lots of our listeners would love to follow you online and maybe find out more about your book as well.
I don't think you've mentioned the name of your new book yet. What's the best way for folks to do that and to learn more?
CHRIS STOKEL WALKER
They can go to my Twitter bio because I don't really use much else.
It is @Stokel, which is S-T-O-K-E-L, and there they can find out all about TikTok Boom, which is China's Dynamite App and the Superpower Race for Social Media.
GRAHAM CLULEY
Fantastic. And you can follow us on Twitter as well, @SmashingSecurity, no G, Twitter won't allow us to have a G. And we've also got a Smashing Security subreddit.
And don't forget to ensure you never miss another episode, follow Smashing Security in your favorite podcast app, such as Overcast, Spotify, and Google Podcasts.
CAROLE THERIAULT
And thanks to this episode's sponsors, 1Password, KnowBe4, and privacy.com, and to our wonderful Patreon community. It's thanks to all of them that this show is free.
And for episode show notes, sponsorship information, guest lists, and the entire back catalog of more than 236 episodes, check out smashingsecurity.com.
GRAHAM CLULEY
Until next time. Cheerio. Bye-bye. Bye.
CAROLE THERIAULT
Chris, do you want to say bye? Or fuck them?
CHRIS STOKEL WALKER
Yeah, bye. Fuck them. Sorry. Fuck you guys.
CAROLE THERIAULT
Hey everybody, Carole here. Boy, we got a few sweet reviews this week. I am so chuffed. I'll read my favorite because it mentions me.
By One Star Guru, quote, "I love listening to your podcast while cooking, and my flatmate always wonders why I'm laughing so hard with my pots and pans.
I love the humor and information. Brilliant hosts and guests. Catching up on old episodes. PS: Carole's paintings are cool. Can I order?" Not yet, but thanks for saying that.
Promise I'll announce it on the show when they're available. We also got a review by Auberge. "Hands down the most entertaining security podcast. Great hosts and guests.
Highly recommend listening to the back catalog." Thank you, Auberge. And MD126. "This is one of the two podcasts I consistently listen to every week.
I tell everyone it's because of the infosec news and insightful commentary, but it's really for the pick of the week.
All my friends and family think I'm awesome as I'm always recommending cool stuff to them.
Keep it up." Thank you, MD126, and thank you all of you listeners, Patreon supporters, sponsors, and reviewers. We love you guys. See you next week.

 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.