CAROLE THERIAULT
Hi, before we kick off the show, we just want to send a huge thank you to just a few of our amazing Patreon supporters: Thomas Fenjens, David Peter, Ruben, Dimitri, Richard Van Liesum, Chayenne Aerosmith, Marcus Vinter, Pete H., Macaulay McCulkin, and Scotia.
Thank you all. Your support really helps us. If you want to join our Patreon community, check us out at smashingsecurity.com/patreon.
GRAHAM CLULEY
And they are giving people a red baseball cap with white writing on it and a white t-shirt bearing an American eagle with the old star and stripes.
JOHN HAWES
No crazy orange hairpieces.
GRAHAM CLULEY
No, don't give people ideas, John. I know what you're like.
JOHN HAWES
A really long tie.
Unknown
Smashing Security, episode 185. Bieber fever, Roblox, and ransomware with Carole Theriault and Graham Cluley. Hello, hello, and welcome to Smashing Security episode 185.
My name's Graham Cluley.
CAROLE THERIAULT
And I'm Carole Theriault.
GRAHAM CLULEY
And Carole, we've got a special guest this week. Who is it, pray tell?
CAROLE THERIAULT
It's someone who's been on a number of times before. Mr. John Hawes. Mr. John Hawes, thank you so much for coming back on.
JOHN HAWES
Hello, Carole. Hello, Graham. Nice to be here.
GRAHAM CLULEY
Hi. Thank you very much for coming back to Smashing Security Towers for yet another— well, actually, it's virtual, of course. Virtual Towers. Yes.
CAROLE THERIAULT
It's always been virtual, though. It's not like we're being on trend here. We're just—
GRAHAM CLULEY
Same old, same old.
CAROLE THERIAULT
Oh, you getting bored?
GRAHAM CLULEY
No, no, I'm not bored at all. It's not like I've been cramped up in my podcast pleasure palace for 4 months or anything like that. No, I'm fine. I'm fine.
What's going on in your world, John? Anything interesting?
JOHN HAWES
Well, apart from not having left the house for 6 months, pretty much the same as everybody else, I think.
GRAHAM CLULEY
6 months? Are you Father Christmas? I've seen that beard of yours. Has it gone white?
JOHN HAWES
You know, I'm an early adopter.
GRAHAM CLULEY
What's coming up on the show this week, Carole?
CAROLE THERIAULT
Well, first, thanks to this week's sponsors, Authentik8 and LastPass. Their support helps us give you this show for free.
Now on today's show, Graham explains why the latest Roblox hack is so unusual. John reveals which US university just paid what might be the biggest ransomware fee ever.
And I talk Pizzagate because it's back with a Gen Z makeover. All this and much more coming up on this episode of Smashing Security.
GRAHAM CLULEY
Now, chums, we were alluding to it in our introduction, but what a ridiculous year it's been. So full of news.
I started off the year in Australia, of all places, where bushfires were going on left, right, and centre. Horrendous. And then we had Megxit.
I imagine you're both still quite upset about Megxit.
CAROLE THERIAULT
These were certainly last year's dramas.
GRAHAM CLULEY
Well, they carried—
CAROLE THERIAULT
I think you're predating 2019 dramas to 2020. And I think 2020 is pretty shit.
GRAHAM CLULEY
So the bushfires carried on until 2020, and Megxit is when they actually left. And Britain has not been the same since Meghan and Harry left. We've really missed them.
JOHN HAWES
We also got Brexit done as well, remember?
GRAHAM CLULEY
Oh, that's true. Yes. Now it's all been done and it's all sorted. Nothing more to worry about there. We had Trump's first impeachment.
I say first, 'cause I'm hoping there may be another one still to come. Global pandemic and lockdown, of course. I doubt you've even noticed that.
Protests around the world after George Floyd's death. Hundreds of billions of locusts. Did you hear that story about the locust swarms?
CAROLE THERIAULT
Yes, not good. Not good for food production at all.
GRAHAM CLULEY
Not good at all. And Tiger King came out on Netflix.
CAROLE THERIAULT
I have not watched that. I refuse.
JOHN HAWES
Is it the mullets?
CAROLE THERIAULT
I listened to a podcast from Wondery on it a few years ago, and that was enough for me.
GRAHAM CLULEY
Well, if that wasn't crazy enough, things have just got a whole load crazier because somebody is hacking Roblox accounts to get kids to persuade their parents to vote in a particular direction in the US presidential race.
CAROLE THERIAULT
Are you kidding me?
GRAHAM CLULEY
No. That's what's happening.
CAROLE THERIAULT
Okay, make your case.
GRAHAM CLULEY
Make your case. So—
CAROLE THERIAULT
Oh my god.
GRAHAM CLULEY
So, Roblox, of course, is an immensely popular online gaming platform. 100 million users. You have little Lego men.
And you create your games, and you publish them for other people to play. Anyone of any age can play it. There's no age limit. But it's really for tweenies and young teens.
I think they're the biggest market.
CAROLE THERIAULT
Does your son play this?
GRAHAM CLULEY
He doesn't. He would love to play Roblox.
CAROLE THERIAULT
Oh, but you don't let him yet, because he's too young?
GRAHAM CLULEY
Well, there's just some nasty stuff which goes on on Roblox. I think we'd have to police it quite a lot. However, these hackers are breaking into accounts.
They're taking over accounts. And one of the things you can do with Roblox is you can customise your gaming experience.
So just with Fortnite or with Animal Crossing, even, you can buy items and skins. You can change the appearance of your in-game character.
You can give them t-shirts and hats and other accessories.
Now, what the hackers are doing in the last week or so is they're breaking into Roblox accounts and they're not doing it, as far as we can tell, to make money.
GRAHAM CLULEY
What they're doing is they're modifying players' profiles.
And specifically, according to the report in Bleeping Computer, who did some research into this, they are changing people's profiles to say in the About section, ask your parents to vote for Trump this year.
#MAGA2020.
CAROLE THERIAULT
Is that Make America Great Again? See, I didn't even know that.
GRAHAM CLULEY
It is, yes.
JOHN HAWES
Does that really work?
JOHN HAWES
Mummy, Mummy, can you vote for President Trump, please?
GRAHAM CLULEY
Well, I was going to vote for Joe Biden, but now—
CAROLE THERIAULT
Thanks, little Richie.
GRAHAM CLULEY
As I do everything that you want me to do, because you are my spoilt child, I'll also vote the way you want. It's astonishing, isn't it? It's incredible.
CAROLE THERIAULT
Okay, so do we have any information on who might be behind it?
GRAHAM CLULEY
We don't know who's behind this. My guess is, Carole—
GRAHAM CLULEY
My guess is it's someone who supports Donald Trump. So that narrows it down.
CAROLE THERIAULT
Well, you see, it could be— it could be— what's it called? A double bluff.
GRAHAM CLULEY
Oh, I see. A Joe job.
CAROLE THERIAULT
Yeah. Is that what it's called? A Joe job?
GRAHAM CLULEY
Well, a Joe job is where you do something naughty, but you make it look as though someone else did something naughty.
CAROLE THERIAULT
Oh, I've done that.
GRAHAM CLULEY
And then they get the blame for it. It happens sometimes with spam campaigns.
CAROLE THERIAULT
I just wonder, right, if the people behind this might be actually not wanting Trump to win, so that the kids go up to mom and dad and say, "Please vote for Trump, Daddy.
Please vote for Trump, Mummy." And they go, "Outrageous! No, I will not! Why did you say that?"
GRAHAM CLULEY
"I'm definitely voting Biden!" You're not a parent, are you, Carole? No.
CAROLE THERIAULT
What did I get wrong on that?
GRAHAM CLULEY
I just simply don't know if the child nagging them to vote one way would actually get them to vote either for that person or against that person.
CAROLE THERIAULT
No, I don't think it would be them. I think it would be the outrage that the Trump campaign might have used this method to convince them.
Because presumably, as soon as a child asks this, they're going to say, "Where did you get that from?" And they will show them.
GRAHAM CLULEY
That's an interesting theory, because I mean, that would of course increase the potential pool of perpetrators, wouldn't it?
And it obviously has to be someone with some time on their hands. And I'm thinking, That Hillary Clinton, she's had a lot of time on it.
I mean, she's sorted out her email server now. Maybe she's—
CAROLE THERIAULT
I'm glad you brought that up because she's coming up in my story.
GRAHAM CLULEY
Is she a special guest later in the show?
CAROLE THERIAULT
Yes, yes, she had nothing to do, so I called her up and said—
GRAHAM CLULEY
We should drop her a line, shouldn't we? We should get her on the show.
Now, the hackers aren't just changing Roblox profiles to say, "Tell your parents to vote for Trump, MAGA 2020." They are also buying online clothes for the character who they've hacked, for the player.
And they are giving people a red baseball cap with white writing on it. And a white t-shirt bearing an American eagle with the old stars and stripes.
They haven't got, obviously, a t-shirt with a Confederate flag. So it's just the traditional stars and stripes.
JOHN HAWES
No crazy orange hairpieces.
GRAHAM CLULEY
I bet that's possible.
JOHN HAWES
Must be, surely.
GRAHAM CLULEY
Don't give people ideas, John. I know what you're like.
JOHN HAWES
A really long tie.
GRAHAM CLULEY
Over 1,000 accounts appear to have already been hacked. And I wondered whether we might see rival hackers try and fight back.
Because rather like sometimes hackers will create a botnet of compromised computers and get them to do their bidding, this is where hackers have taken over Roblox profiles effectively.
Maybe we could see hackers who maybe support the Democrats.
CAROLE THERIAULT
Or maybe we could see Roblox actually strengthen their security.
GRAHAM CLULEY
Well, is it really Roblox's fault, I wonder?
CAROLE THERIAULT
Well, let me ask some questions. Do they have multifactor authentication available?
GRAHAM CLULEY
They do have, yeah, it's two-step verification. They have that available. But of course, is the typical 11-year-old kid going to have turned it on?
CAROLE THERIAULT
By default or do you have to go into some weird setting to go enable it?
GRAHAM CLULEY
I'm not a Roblox user. I'm pretty sure it's not turned on by default, just as in most of the world it isn't, of course. So you do have to go to some effort and you have to find out.
And what we'll do is we'll put in a link in the show notes as to how to turn on your two-step verification. You should also make your password unique and hard to crack.
It appears that these are people who've had easy-to-crack passwords.
GRAHAM CLULEY
You also should log off when you're not playing Roblox. So tell your kids to do that as well.
And that prevents— I'm not suggesting it's the kid next to you who's changing profiles to say this.
CAROLE THERIAULT
You're not blaming little Jimmy.
GRAHAM CLULEY
No, no. But if Hillary Clinton comes up to you pretending to be a kid and reaches for your laptop, it could, of course, be her.
Don't be tricked into entering your username and password into an in-game form because these games can actually present forms to you, which might appear to be a dialogue from the real Roblox.
And some kids are tricked, because what they all want to do, of course, is they want free Robux. Robux is the currency.
Yeah, I know, we say yeah, 'cause of course we know what that is.
CAROLE THERIAULT
Well, no, we've covered it before on the show as well.
GRAHAM CLULEY
Yeah, and we're familiar with Animal Crossing Bells, of course. Lots of kids are after free Robux and prizes and cheats or membership of the Builders Club.
And again, they will install programs or browser extensions to try and get hold of them. And their computer is compromised.
Now, wouldn't it be interesting if we did see rival hackers?
GRAHAM CLULEY
Well, here's what they could do, right? So these hackers are giving people baseball caps and American Eagle t-shirts. What if people came in and gave them all face masks, right?
So if you're going to one of those Trump rallies, maybe there's an online rally inside Roblox. At least you'd all be protected from each other and not spreading disease.
JOHN HAWES
Did children have rallies?
GRAHAM CLULEY
Well, there was Hitler Youth, wasn't there? They probably had a get-together. I mean, what is a rally? It's just a meeting in a scout hut, isn't it?
CAROLE THERIAULT
It's kind of gross that kids are being targeted though. From whoever is behind this, you know, the fact that they're actually targeting kids is pretty yucky in my view.
GRAHAM CLULEY
It is. I mean, it's quite possibly a 14-year-old kid who's doing it as well.
CAROLE THERIAULT
I have a feeling that today's 14-year-olds know a lot more than I did at 14.
GRAHAM CLULEY
Well, Carole, there's some things I hope that you— Some things.
CAROLE THERIAULT
So what were you trying to say? What insult are you trying to land there awkwardly?
GRAHAM CLULEY
I was just gonna say, I hope there's some kids who don't know what you knew at 14. That's all I was gonna say, Carole.
CAROLE THERIAULT
Oh, well, I didn't know you, so— Well—
GRAHAM CLULEY
Excellent. Excellent. And let's move on. What's your story for us this week?
JOHN HAWES
So all of the big headlines for the last couple of days have been about a US university which has paid out over $1 million to ransomware.
This is the University of California in San Francisco, which is basically the medical part of the University of California.
So it's a major medical research center, it's got a major teaching hospital attached.
CAROLE THERIAULT
Okay. Okay.
JOHN HAWES
So a few weeks ago, several ransomware groups said, because of the pandemic, we're going to be nice and not go after hospitals and universities who are researching to try and cure this.
And by not attacking them, we're going to save the world, which was very nice of them.
GRAHAM CLULEY
But then the lockdown dragged on a bit and they were thinking, oh crikey, we need—
CAROLE THERIAULT
They got bored.
GRAHAM CLULEY
They got bored. We still need to make some money. Maybe we can just infect a few hospitals. They didn't really care so much.
JOHN HAWES
Well, and also I think the group that's supposedly behind this, which is known as Netwalker, they were not part of that announcement anyway.
JOHN HAWES
Yeah, so anyway, I mean, the UCSF—
CAROLE THERIAULT
That's the university, right?
JOHN HAWES
The University of California, San Francisco. They claim that none of their COVID-related research was affected and also that no patient info was leaked.
But obviously it's very hard to be sure on these things. It seems like they were madly running around the building pulling plugs on servers when they noticed this was happening.
It's hard to tell where it all got stopped.
CAROLE THERIAULT
Were they complacent with security, do you know? Or were they just targeted?
JOHN HAWES
It's very difficult to tell. Universities and hospitals— this is why we've had so many stories about ransomware in those kinds of settings recently.
They're very big, diverse organizations.
They tend to have lots of different kinds of hardware and software that they need to run on some kind of ancient machines in some places, and it's very difficult to keep all that secured.
Which is why they're big fat targets for nasty people.
JOHN HAWES
They've been quite good on the communication side. I mean, the actual attack was on June 1st, and they made a very clear statement on, I think, June 3rd, and a couple more since.
And the last one, which was last week, is the one that revealed that they had actually made this payment. Whoa.
CAROLE THERIAULT
So they admitted to making an over $1 million payment.
JOHN HAWES
So somehow the BBC learned about this thanks to an anonymous tip. And they had access to the actual negotiations that were going on with the ransomware people.
CAROLE THERIAULT
Oh, really?
JOHN HAWES
Yes. Not really quite clear how it worked out that somebody gave them all the details of the—
CAROLE THERIAULT
So what kind of things were they saying?
JOHN HAWES
Well, it's very interesting. So I've not seen any of this side of it before at all.
In movies, if there's a ransom, you kind of expect, you know, Mel Gibson cutting out bits of newspapers or at least going to a payphone and putting a hanky over the mouthpiece.
CAROLE THERIAULT
That's right.
GRAHAM CLULEY
You can't kidnap someone without a hanky over the mouthpiece. Doesn't count.
JOHN HAWES
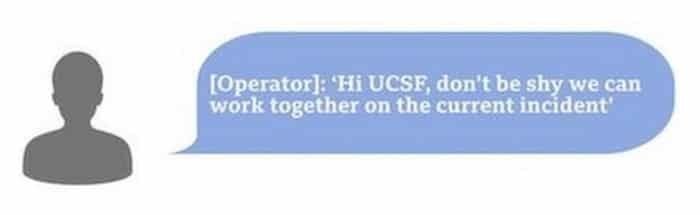
Of course not. In the modern age, so apparently they have a dark web website complete with FAQs and a web chat system.
CAROLE THERIAULT
These are the ransom guys.
JOHN HAWES
So they apparently, you go to the site, you enter your code that you were given in your ransom note, and that connects you with an operator and you can have a little online chat.
GRAHAM CLULEY
You're just in the queue. Please wait. We'll get around to you. All of our operators are busy at the moment.
CAROLE THERIAULT
This is not the first time we've talked about kind of malware and attacks like this actually operating like corporations.
GRAHAM CLULEY
Well, it's properly professional business, isn't it? I mean, that's the message everyone needs to learn.
JOHN HAWES
It looks very slick. So the BBC has actually published a bunch of the conversation, although only the ransomware side, not the university side.
It's very interesting to see how the conversation develops and the sort of language they use.
CAROLE THERIAULT
Tell us some of it.
JOHN HAWES
So the UCSF— They were asked for $3 million, and they came in with an opening bid of $780,000, which seemed like a pretty high starting point.
I would have probably come in with nothing.
CAROLE THERIAULT
That to me says right away they want to pay a million.
JOHN HAWES
Yeah, it does. It's basically giving away that you're willing to pay a lot.
CAROLE THERIAULT
If they come back and said, how about $780?
JOHN HAWES
Or how about just giving us our stuff back and not being bad people?
GRAHAM CLULEY
But the thing is with this ransomware is that there was a ticking countdown as well.
So there was an urgency on the university's part to do something about this, not only because they've been doing coronavirus research and looking into possible treatments there, but also because it was possible their data would either be permanently deleted or published for everyone to see.
JOHN HAWES
So when they made this £780,000 offer, the response was, keep that £780k to buy McDonald's for your employees.
GRAHAM CLULEY
John, could you do that in a sort of kidnapper voice?
JOHN HAWES
That was my kidnapper voice.
GRAHAM CLULEY
Oh, okay. Good to know for future reference.
JOHN HAWES
So I worked out, apparently there's 25,000 people working at the UCSF, so they could have all had 7 Big Macs each and still had change for a few drinks.
CAROLE THERIAULT
Is it even possible to eat 7 Big Macs in one single day?
CAROLE THERIAULT
I could not do that.
GRAHAM CLULEY
You need to try harder.
JOHN HAWES
Yeah, also I imagine given that most of them are probably health professionals, they would—
CAROLE THERIAULT
They would rather die than put that poison into their stomachs. Good for them.
GRAHAM CLULEY
We're in lockdown, Carole. Everyone needs a hobby. I think you can try and do it before we have it eaten.
CAROLE THERIAULT
Yeah, no, you just want me to die. Jeez.
JOHN HAWES
Anyway, so after a day or two of this chat, went back and forth messages every few hours, they finally settled on this $1.14 million. Which the UCSF paid in bitcoin the next day.
And my first thought was, is that the highest ransomware ever? Because I couldn't remember hearing of anything like that high. Also, that seems like a very odd amount.
It wasn't even exactly 1.1, but it was 1.147.
GRAHAM CLULEY
Oh, but did you divide it by the price of bitcoin on that particular day? Maybe it was something like 8,000 bitcoin.
JOHN HAWES
Well, again, I think it was 116.4 bitcoin. It wasn't a round number of bitcoin either, although maybe it was the day before or something.
GRAHAM CLULEY
Yeah, maybe.
JOHN HAWES
But what I did find, so I looked what the biggest payouts ever, and there was one in 2017 made by a South Korean web hosting firm who paid out $1 million, which is widely listed as the biggest one ever.
But if you then look back at the stories from the time, they quote it as 1.3 billion won, which at the time was $1.14 million.
GRAHAM CLULEY
Oh, exactly the same.
CAROLE THERIAULT
Interesting, John.
JOHN HAWES
So it sounds like they knew that and they have deliberately refused to budge until it went to the highest ever, or at least publicly released.
Obviously, there's going to be some that were kept secret that could easily be higher than that.
GRAHAM CLULEY
So Netwalker have got this quite professional criminal organization where they have people online available to chat with you if you happen to be a victim of that.
Do you think one of their operators thought, "I'm going to really impress the boss.
I'm gonna hold out until I can go back to my bosses and say, 'Hey, I've brought in, actually, the biggest ransom ever.' So I'm aiming for that amount." I think that's very possible, yes.
CAROLE THERIAULT
This is a really big problem though, because they have basically financially incentivized a bunch of bad guys.
GRAHAM CLULEY
Okay, but there's a couple of things. So, as a general principle, I agree, you shouldn't pay criminals for this kind of thing, and it just encourages them to launch more attacks.
However, there is a global pandemic going on, and this is— these are medical researchers who are working on trying to find better treatments for COVID-19.
So that increases the urgency, and there was the risk this data would be released in public and maybe endangering other people's privacy as well.
And so I think under those circumstances, you may think, well, just to be up and running as quickly as possible.
CAROLE THERIAULT
I know, I completely understand that. Is that enough though to say, here, bad guys, here is $1 million?
JOHN HAWES
Well, that's also, that's the other side of this is for a long time we've been saying, oh, ransomware, if as long as you've got good backups, you don't have to pay out, you can just restore and you'll be fine.
But more and more of them nowadays are actually taking stuff away as well and saying, okay, either pay the ransom and you'll get your stuff back and we'll delete our copy of it, or we will release this and you'll be destroyed.
But in a way, they've almost sort of doubled the uncertainty around paying the ransom, 'cause in the past you pay the ransom and you might get the decryption keys.
And now it's you pay the ransom, you might get the decryption keys, they might delete their copy, they almost certainly won't, they might just not release it for a little while, but you've kind of stretched that likelihood of it being released further down the road, and you've told them that you're willing to pay lots of money to them.
GRAHAM CLULEY
I don't know.
I think if I was the criminal who'd stolen the data and I had been paid, I think in order to make my future attacks more successful, I wouldn't release the data at a later time.
I wouldn't double-cross.
JOHN HAWES
Or you just change your name.
GRAHAM CLULEY
Oh, well, yeah, maybe.
CAROLE THERIAULT
Yeah, but you might change your mind in 10 years or 20 years. I mean, you may be 20 years old right now and have successfully done this, right?
JOHN HAWES
And storage is cheap.
CAROLE THERIAULT
Yeah. I mean, you, yeah, you used to say, oh, all these guys, they're all mostly script kiddies writing little viruses, 'cause back then it was mostly true.
Ain't true anymore, sunshine.
GRAHAM CLULEY
No, not true. And as John just said, we used to say the answer is backups, and sure, you should have backups, but actually these days prevention is the thing which you need.
You want this to stop happening in the first place.
JOHN HAWES
The main way in for most of these attacks is almost always some kind of phishing.
It's an email either tricking you into handing over usernames and passwords or to running something nasty on your machine that starts it all off.
So I think that probably the biggest step towards reducing this kind of problem is gonna be better phishing prevention.
CAROLE THERIAULT
Yeah, but also have backups.
GRAHAM CLULEY
Yeah, and also have backups.
GRAHAM CLULEY
Carole, what have you got for us?
CAROLE THERIAULT
Well, clue: I'm gonna talk about a serious topic this week, and so you can rest easy that I will not be funnier than you this week. Okay, but first I think you should come clean.
Do you want to tell everybody about what? Well, about your secret love affair with Piers Morgan and Sean Hannity.
GRAHAM CLULEY
What are you talking about? Why? Why?
CAROLE THERIAULT
No, seriously, don't you think our wonderful listeners have the right to know the truth?
CAROLE THERIAULT
Right now, if I carried on with this— Please don't. It could cause a lot of problems for your life, right?
CAROLE THERIAULT
And that is why I'm talking about Pizzagate. And you'd say, why Pizzagate? Wasn't Pizzagate that conspiracy theory that reared its head during the Clinton email scandal? Yes.
GRAHAM CLULEY
That was insane, wasn't it?
CAROLE THERIAULT
It was. What do you remember about it? Do you remember it?
GRAHAM CLULEY
Well, I remember it wasn't a conspiracy involving the use of pineapple on pizza.
It was that there was some kind of child trafficking pedophile ring running out of a Washington pizza parlor, which was—
CAROLE THERIAULT
Yeah, it's a friend of Podesta's brother runs this pizza place.
GRAHAM CLULEY
Yeah, and crazy QAnon people were sort of spreading stuff and photographs, and eventually some nutter turned up there with a gun. And yeah, just general internet insanity.
Basically 2020 was happening a couple of years ago with—
CAROLE THERIAULT
Yeah, 2016 actually, right? So at the time after this all happened, fact-checkers debunked the conspiracy.
And we might have thought that it might just disappear because it really seemed to be all around the kind of Podesta-Clinton emails, which is no longer the flavor du jour, as we have much bigger fish to fry these days.
So the question is, how does a 4-year-old scandal show up today? There are more than 80 million views of TikTok videos with Pizzagate-related hashtags in the last few months.
80 million.
According to New York Times journalist Shira Frenkel, younger people on TikTok and other social media platforms have made Pizzagate more relatable by roping in celebrities that they know, like Justin Bieber.
CAROLE THERIAULT
So I'm gonna tell you this conspiracy as far as I understand it, because of course with all conspiracies, there's a lot of twists and turns to keep everyone out of being able to tie it all together.
That's part of the joy of conspiracies.
But the gist seems to be: A documentary promoting Pizzagate, which was called Out of the Shadows, was made by a former Hollywood stuntman, and it was released on YouTube earlier this year.
CAROLE THERIAULT
It was passed around in the QAnon community, and in May, the idea that Mr. Bieber was connected to the conspiracy surfaced. Okay, so this was in May, two months ago.
CAROLE THERIAULT
Later that month, Justin Bieber was doing an Instagram video with commenters.
You know, when people can kind of write questions and you answer the questions and you interact with people.
GRAHAM CLULEY
Oh, it's a live chat.
CAROLE THERIAULT
Like a live Instagram chat, something.
CAROLE THERIAULT
And someone had posted the comment asking Justin to touch his hat if he had been a victim of the child trafficking ring known as Pizzagate.
CAROLE THERIAULT
And 4 minutes into the video, Justin Bieber leans into the camera and adjusts the front of his black knit beanie.
And for some, not an insignificant number of his 130 million followers, this was admission that he had been a victim of the alleged Pizzagate child trafficking ring.
GRAHAM CLULEY
Hang on. Yes. Hang on. So a few things, right? So they were asking Justin Bieber to give a secret sign if he was somehow involved in this child trafficking ring.
Well, if he'd been a victim of it, right?
CAROLE THERIAULT
Yes, I'm imagining that they understand that he wouldn't want to come forward on his own and he has to do it.
GRAHAM CLULEY
So yeah, it wouldn't be that surreptitious, would it, to do it in a public Instagram having just been asked a few minutes before?
Whether he would touch his hat to give it away, and then he touched his hat. So that's one comment.
The second one is, if you're wearing a hat, it's going to be quite hard not to occasionally touch it or to touch your nose.
CAROLE THERIAULT
Do not touch your nose.
GRAHAM CLULEY
Right, exactly. Don't think of pink elephants, right? You're going to do it. Okay, so tell us more, Carole, tell us more.
CAROLE THERIAULT
So the problem, one of the problems that was pointed out by the New York Times reporters was that thousands of comments were flooding in at the time.
So there's no evidence, they say, that Bieber saw the message, right?
GRAHAM CLULEY
Oh, so in the live chat, everyone was chatting to— of course, because he's Justin Bieber.
GRAHAM CLULEY
And so he probably doesn't see 99.99% of the comments. Okay, right.
CAROLE THERIAULT
So, however, the viewers that noticed the hat scratch went nutso, right? And hundreds of videos online analyzing Mr. Bieber's actions started.
They were translated into Spanish, Portuguese, other languages, right? Amassing millions of views.
Now that's different from the original Pizzagate, which really centered in the States, right?
CAROLE THERIAULT
Only when contacted by Times did TikTok take steps to mitigate the spread of the hashtag. But in social digital terms, they categorically missed the boat, right?
GRAHAM CLULEY
And even if they mute the hashtag or whatever the phrase is, people are going to read that as, oh, here we go again. Here is deep state controlled.
CAROLE THERIAULT
It also helps stem the spread of the conspiracy.
So because Facebook and Instagram and Twitter were actually strongly rooted in existence when it first happened in 2016 and after the pizza gun incident, there were loads of social media stopping the search for Pizzagate or stopping the hashtags from being used.
And so Twitter and Facebook and the like already had some mechanisms to handle it already in place, but TikTok was in its infancy then. It didn't exist.
GRAHAM CLULEY
But even if Pizzagate is being stamped on by social media, all someone has to do is start something about pasta goat, for instance, right?
You can get a goat and you can have some goat meat with pasta.
CAROLE THERIAULT
Give them ideas.
GRAHAM CLULEY
Right. Well, no, I'm not trying to give them ideas.
CAROLE THERIAULT
Well done. Well done.
CAROLE THERIAULT
John, Graham, you guys. Okay, now here's my question to you guys.
CAROLE THERIAULT
The big question I have is once I read about this, I was like, well, what is Justin saying about all this?
CAROLE THERIAULT
And as far as I can see, nothing. Now, he has 112 million followers on Twitter alone. Okay, that's three times the size of Canada.
GRAHAM CLULEY
The universal measurement of size.
CAROLE THERIAULT
Yes, the Carole measurement of big.
GRAHAM CLULEY
Three Canadas big. Yeah.
CAROLE THERIAULT
So I'm guessing, okay, so on one side you could say he's just going to ignore it because it's crazy, right? Doesn't want to get involved in it.
And even if he did get involved and say, okay, it didn't happen and you guys have to all stop it, like, oh, you see, he's denying it because he's embarrassed.
So I don't think he can get— he can't win by getting involved? But does he win by not getting involved?
GRAHAM CLULEY
No, he can't get— he can't win.
Because during his video where he says, "This is all a load of cobblers," he would scratch his nose, or he'd stop to bite a piece of pizza while leaning up against his garden gate, or there'll be something which someone would analyse in the video and say, "There!
There's a secret message he's embedded in there to tell us what's really going on." I don't think he can win.
CAROLE THERIAULT
Yeah, it's depressing. I think I actually feel sorry for him, you know. I mean, he's been— I do. Okay, he's Canadian.
It's not that someone feels sorry for him, but, you know, I have more empathy for Canadians.
GRAHAM CLULEY
I feel sorry for people who are Canadian.
CAROLE THERIAULT
And two, he has been the butt of viruses, phishing scams since he was a young teen.
JOHN HAWES
So maybe that's why he keeps quiet about it. He's just like, yeah, yeah, whatever.
CAROLE THERIAULT
Too much. He's jaded, man.
GRAHAM CLULEY
He probably just thinks that people are idiots. And he probably thinks all these fanatics, whether they be fans of his music or fans of QAnon or whatever, are just insane.
It's better just to keep your head down.
CAROLE THERIAULT
I think it would be wrong to assume that everyone who are contributing to this conspiracy are actually buying what they're peddling.
I think a lot of them, from what I'm reading, see this a bit as play gaming. It's almost community-driven conspiracy mystery storyline.
I think it's exciting and fun for a lot of them, and I think they're doing it ironically.
Problem is there's loads and loads, millions, that are not in on the joke, and they're falling for it hook, line, and sinker.
JOHN HAWES
At least they're not doing it on Roblox.
CAROLE THERIAULT
Well, yes, yet, yet, yet it'll come. Yeah, yeah, fake news is evil shit in my book, right? So shouldn't do it.
Doesn't make you any better than the leaders that are contributing to all the disinformation garbage anyway. So can we stop it?
JOHN HAWES
How do we stop it?
CAROLE THERIAULT
Stay true, man. It's the only way.
GRAHAM CLULEY
I think cut people's fingers off with bolt cutters and just remove them from the internet.
CAROLE THERIAULT
So I ask you again, Graham.
CAROLE THERIAULT
In the interest of honesty, are we going to talk about your secret love affair with Piers Morgan and Sean Hannity?
JOHN HAWES
For goodness sake.
CAROLE THERIAULT
I'm going to get a hashtag. I wish I'd sorted one out already. Use a password manager. Just do it. These aren't my words. These are the words of Brian X.
Chen, the lead consumer technology writer at The New York Times. It's time that everybody uses a password manager, both at home and at work.
Now get this, LastPass from LogMeIn offer businesses a secure vault with centralized secure access, single sign-on, and simplifies remote management of all these accounts.
And guess what, you home users out there, you can get LastPass free. For more info, go to smashingsecurity.com/lastpass. That's smashingsecurity.com/lastpass.
GRAHAM CLULEY
Silo for Research Toolbox from Authenticate is a secure and anonymous web browsing solution that enables threat intelligence, security, and public safety professionals to conduct research, collect evidence, and analyze data across the open, deep, and darkweb.
To learn how Silo for Research enables teams to timely and efficiently investigate while ensuring maximum security and oversight to ensure compliance, including GDPR, go to smashingsecurity.com/authenticate.
That's smashingsecurity.com/authenticate, and that is spelt authentic with a number 8 on the end.
And welcome back, and you join us on our favorite part of the show, the part of the show that we like to call Pick of the Week.
CAROLE THERIAULT
Pick of the Week.
JOHN HAWES
Pick of the Week.
GRAHAM CLULEY
Pick of the Week is the part of the show where everyone chooses something they like.
Could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website, or an app. Whatever they wish. Doesn't have to be security-related necessarily.
CAROLE THERIAULT
Better not be.
GRAHAM CLULEY
And my Pick of the Week this week is not security-related. There is a chap called Mark Rober. He runs a very popular YouTube channel, and you may have seen his latest video already.
It's had millions of views. I'll own I'm a bit late to this.
CAROLE THERIAULT
I haven't even seen it yet, so.
GRAHAM CLULEY
It's been around for a few weeks, this one. Now, I heard about this particular video on the latest episode of the Frackulous podcast, which I was listening to this morning.
Frackulous, of course, stars friend of the show, David McClelland. Yes.
CAROLE THERIAULT
When are you coming back on, David?
GRAHAM CLULEY
And they were talking about this video called Building the Perfect Squirrel Proof.
JOHN HAWES
Perfect Squirrel Proof.
GRAHAM CLULEY
Squirrel Proof. But it is 2020. Building the perfect squirrel-proof bird feeder.
CAROLE THERIAULT
Okay. That's a difficult thing.
GRAHAM CLULEY
Well, it sounds from the title like it's going to be something quite practical.
It's a problem, because you want to feed birds, but you don't want the squirrels stealing all the nuts.
GRAHAM CLULEY
It's not that kind of video at all. Instead, this should really be called Squirrel Ninja Warrior Course.
GRAHAM CLULEY
So, what this chap has done is, because of lockdown, he set up a bird feeder, and he noticed that squirrels kept on stealing the walnuts or whatever.
So, he thought, right, I'm going to have a bit of fun. I'm going to give the squirrels more and more of a challenge.
And he ended up with this huge assault course, which the squirrels had to complete in order to get the nuts.
CAROLE THERIAULT
I'm looking at it now. It's incredible.
GRAHAM CLULEY
It is pretty cool.
And there's a variety of ways and challenges for the squirrels, which they have to complete in order to get to their nuts in what he stresses is a squirrel-friendly fashion.
Some of them include, for instance, I remember the homewrecker, and the homewrecker stage is where there's a stuffed toy squirrel with a blonde wig and wearing a bikini.
CAROLE THERIAULT
No, there isn't.
GRAHAM CLULEY
There is. And if the squirrel stops by it for too long, there's a pressure sensor underneath it, and it gently flicks the squirrel up into the air.
GRAHAM CLULEY
Yeah, well—
CAROLE THERIAULT
You just put that in so you don't look cruel.
GRAHAM CLULEY
I believe this.
He does stress this over and over again, and he shows you the video in slow motion of how the squirrels— so it's quite interesting actually how both squirrels and cats manage to land quite safely from remarkable distances.
So there's that.
There's another one which is a bit like when you go to the British seaside, you might find one of those sort of stand-up placard things with a hole cut out for your head.
You stick your head through and suddenly you're a fat lady or something like that and you get your photograph taken.
Well, he's built one of those for the squirrels and incentivised them with a nut to stick their head through and so he can then take their photograph.
There's all manner of things like this.
CAROLE THERIAULT
Oh my God.
GRAHAM CLULEY
And I have to say, squirrels are incredible things.
So if you haven't already seen Mark Rober's perfect squirrel-proof bird feeder video, I would recommend it because it is my pick of the week.
CAROLE THERIAULT
Do you know what? It's a serious problem, Graham.
Seriously, my parents and my whole childhood, that was one of the big concerns in our wood where we lived was how to protect the bird seeds from the plethora of squirrels.
GRAHAM CLULEY
Oh, I thought you meant homewrecker squirrels ruining relationships.
CAROLE THERIAULT
I'm just saying it's a real problem that people face every day.
JOHN HAWES
Surely drones are the answer.
CAROLE THERIAULT
Oh really? How would you do that?
JOHN HAWES
You hang your bird feeder from a drone and you fly it up in the air, and then the squirrels can't get at it.
CAROLE THERIAULT
All while decapitating all the birds?
JOHN HAWES
Well, no, the birds fly in from underneath, or, you know, the drone has little guards around its blades.
CAROLE THERIAULT
Okay. I'm glad you're not in charge.
GRAHAM CLULEY
Just saying. John, what is your pick of the week?
JOHN HAWES
So I wanted to talk about a TV show called Dark.
CAROLE THERIAULT
Oh, this sounds fun.
JOHN HAWES
Pretty sure has been brought up on this show in the past.
GRAHAM CLULEY
It rings a kind of bell, actually.
JOHN HAWES
It's a great, great show. And season 3 came out the other day at the weekend, I think. Apparently final season.
CAROLE THERIAULT
Are you a big fan of Dark?
JOHN HAWES
Absolutely love it. It's glorious.
GRAHAM CLULEY
Remind us again what the show is about.
JOHN HAWES
So it's a German teen time travel thriller, I guess you could call it.
It's set in a small German town in the countryside, and there's 3 or 4 families that we focus on, and some kids have been going missing, and one of them finds a spooky tunnel leading to the past and possibly the future.
And from there it kind of builds and builds and builds and it becomes insanely complicated.
You've got these sort of 30 core people and you're seeing them as small children and then as teenagers and as middle-aged and old people.
But some of them are moving through these tunnels and then some of them also develop time travel machines, which they use to time travel, and then sometimes take the time travel machine through the time travel tunnel.
GRAHAM CLULEY
So John, to keep track of what's going on in this TV show, have you got flowcharts? Have you got an obsession wall?
JOHN HAWES
It is the most tempting show I've ever seen to go out and build an obsession wall. But I don't think you could do it on a wall.
I think you would need some kind of 5-dimensional thing. There is actually, there is an excellent— so Netflix, on Netflix.
And they have built a website to go with it that you can— it's got a list of all the different people and all the interesting concepts.
And as you arrive, you tell it which episode you're up to so you don't get any spoilers.
GRAHAM CLULEY
Oh, that's a cool idea. You say it's a German show. Is it dubbed or is it subtitled?
JOHN HAWES
Well, Netflix has been really pushing dubbing. They're trying to make that come back again.
So I've been watching it dubbed, but also subtitled, which is also part of the fun because I have no idea why they do this, but they have different writers, I guess, doing the dub part and the subtitle part.
So you're watching and somebody might walk in and go, "Fuck you, motherfucker!" And the subtitle says, "You're not very nice." It's quite often there's weird clashes between the two, which is quite fun too.
But yes, the website is actually probably vital, especially if it's been a while since you saw season 2, because there's so many faces.
Each character has at least 3 different faces. And some of them are played by different people, obviously, because the child and the grandpa are the same person.
GRAHAM CLULEY
Oh my goodness.
JOHN HAWES
I think pretty much every episode ends with a little sort of montage scene where you see all the different characters that have been in the episode and then it kind of merges into a face of what they were like in a different period and stuff.
CAROLE THERIAULT
So this is for people that have a lot of time on their hands, enjoy complicated plot structures and teen thriller type things.
JOHN HAWES
And time travel shows. And it's not a lot of time. I think it's only— it's an 8-part series or something. It's not very, very long.
CAROLE THERIAULT
With 3 series.
JOHN HAWES
Yes. Well, yes, I would say actually, if you've not seen any of it yet, I would thoroughly recommend trying to watch the whole thing in one weekend.
CAROLE THERIAULT
What? Well, 3 series.
JOHN HAWES
Well, because otherwise, if you leave it a few days and you come back to it, you're suddenly scratching your head going, who's that guy again? Is that the granddad of that guy?
Or is that the same guy, just a bit older? I don't know. Just watch it all at once and it's much easier to remember.
CAROLE THERIAULT
John, is your home life okay? Just checking.
JOHN HAWES
Or use the online obsession wall, which is very useful.
CAROLE THERIAULT
Fascinating. So that's the Netflix series Dark, and the latest third series has just come out.
GRAHAM CLULEY
Yes. Fantastic. Carole, what's your pick of the week?
CAROLE THERIAULT
Okay, mine's an article. And it all involves Sherlock Holmes. And I think, John, you mentioned before that you're an avid fan.
JOHN HAWES
I do, I do love a bit of Sherlock Holmes.
CAROLE THERIAULT
Right, right, right. So I partly chose this article because I knew you were coming on the show. So let me just set the scene. Arthur Conan Doyle has an estate, right?
And according to The Verge, the Arthur Conan Doyle estate is suing Netflix for giving Sherlock Holmes, the character in an upcoming movie, too many feelings. For real. Okay.
So Enola Holmes, this is the character, is based on a series of novels by Nancy Springer. Okay, nothing to do with the Arthur Conan Doyle empire.
And it stars a newly created teenage sister of the famous detective. Right, and Netflix are going to do a movie of these novels.
Now, the gist is the Sherlock Holmes books 10 of them are still owned by the estate. The rest are now in— was it publicly owned?
GRAHAM CLULEY
Oh, I see. Okay.
CAROLE THERIAULT
And the ones that the estate owns are those later in life. This is after Arthur Conan Doyle experienced World War I and lost a son.
And this translates, the estate argues, into when Sherlock started showing a more human side because Arthur Conan Doyle had saw more of life.
But in the earlier books, the ones that are available to everybody and are not subject to the estate copyright, features an unsympathetic, cold rationalist of a detective.
And the problem is in the movie, Sherlock is portrayed to be a kindly, loving brother.
Ipso facto, they and the author and the publishers all need to pay up to the estate in order to portray Sherlock giving a shit.
GRAHAM CLULEY
Oh, this is bullshit, isn't it?
CAROLE THERIAULT
It's ridiculous. Anyway, so I just think it's a great story. It's written quite cutely from The Verge, written by Addie Robertson.
I will put a link in the show notes, and you should enjoy it. I think it sounds like it's going to be fun.
JOHN HAWES
And also, I've just opened the article. So the actor playing Enola Holmes was Eleven from Stranger Things, another spooky teen sci-fi.
CAROLE THERIAULT
There you go. Check it out. And, you know, greedy estates.
GRAHAM CLULEY
Well, on that ridiculous note, I think we've just about wrapped up the show for this week. John, I'm sure lots of our listeners would love to follow you online. Unfortunately—
JOHN HAWES
They're not allowed.
GRAHAM CLULEY
You don't really exist online, do you, John?
GRAHAM CLULEY
Right. Okay.
CAROLE THERIAULT
See, you're so secure, John. You should start your own blog explaining how people can unplug and be cool.
JOHN HAWES
You know, I do have things plugged in. I just don't to shout about it.
GRAHAM CLULEY
Well, you can follow us on Twitter @SmashingSecurity, no G, Twitter won't allow us to have a G. And you can also join us on our subreddit up on Reddit.
Just look for Smashing Security. And don't forget, if you want to be sure never to miss another episode, subscribe in your favorite podcast app.
Such as Spotify, Apple Podcasts, or Pocket Casts.
CAROLE THERIAULT
And huge thank yous as always from us for listening, for supporting us, for sharing our content, for liking it. It means the world to us.
Also, thank you to this week's Smashing Security sponsors, Authentik8 and LastPass. Their support helps us give you this show for free.
Check out smashingsecurity.com for past episodes, sponsorship details, and information on how to get in touch with us.
GRAHAM CLULEY
Until next time, cheerio. Bye bye. Bye.
CAROLE THERIAULT
Did you notice that we opened the show thanking a few of our wonderful Patreon supporters? From this show forward, we plan to thank each and every one of you that support us.
It's just another way for us to say, you humans really make a difference and we salute you. Listen out for your Patreon name.
Oh, and if you aren't yet a supporter and want to join the Smashing Security community, visit smashingsecurity.com/patreon.
And thank you from the bottom of my heart— not Graham's, because we're not sure he has one, right?




 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.




They should have used linux :p
if you pay out, more will come because they see you as easy pickings
I am still seeing clients who have substantial Server 2003 footprint. At some point you have to ask whether these orgs are actually taking security seriously. A modern OS with modern antimalware and a cyber recovery solution for the most critical systems would seem to be the minimum any competent organisation should be implementing.
Living proof that crime does pay. What does this say about all those ideals you learned during childhood?