A new Android banking trojan poses as a legitimate weather forecast app in an effort to steal users’ banking credentials.
The malware, dubbed Trojan.Android/Spy.Banker.HU, mimicked the legitimate Good Weather app to skirt Google’s security mechanisms and infiltrate the Play Store.
Spy.Banker.HU was available for all of two days before ESET reported it. But that doesn’t mean the malware isn’t preying on users who happened to install it during that time period.
Let’s take a look at how the malware works.
Upon installation, the fake app’s weather-related icon disappears. The trojan then requests administrative privileges for a “System update.” It needs these to execute its malicious activity.
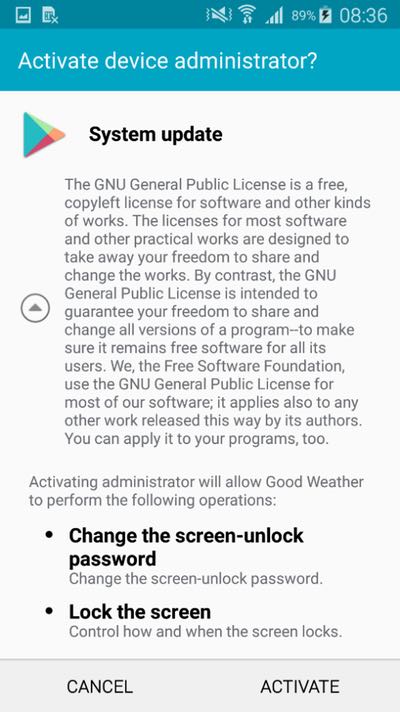
Whoa… hold on a second.
“Change the screen-unlock password”? “Lock the screen”?
Those are some pretty bold requests for a weather app!
But that’s exactly what Spy.Banker.HU wants. As ESET researcher Lukas Stefanko explains in a blog post:
The trojan displays a fake login screen once the user runs one of the targeted banking apps and sends entered data to the attacker….
As for the device locking, we suspect this function enters the picture when cashing out the compromised bank account, to keep the fraudulent activity hidden from the user. Once locked out, all victims can do is wait until the malware receives a command to unlock the device.
Like other banking trojans that have come before it, the malware also has the ability to intercept SMS messages. This allows the malware to raid a user’s banking account even if they have SMS-based two-step verification enabled.
To defend against this malware and others like it, users should review the privileges of an app carefully before they install it. If what an app is requesting doesn’t line up with its intended function, they should find an alternative.
It’s also a good idea for users to consider keeping an anti-virus solution installed on their mobile device.