
A new Android trojan has the ability to intercept text messages and bypass the SMS-based two-factor authentication system protecting customers’ bank accounts.
Lukas Stefanko, a malware analyst at ESET, notes in a blog post that the trojan, detected as “Android/Spy.Agent.SI,” is currently targeting customers of 20 large banks located in Australia, New Zealand, and Turkey via their mobile apps.
The malware tricks users into downloading it onto their devices by masquerading as Adobe Flash Player. Upon installation, it requests that the user grant the malicious app administrator rights, before seemingly disappearing from view.
Rest assured, however, that while the Flash Player icon might no longer be visible, the trojan is just getting started.
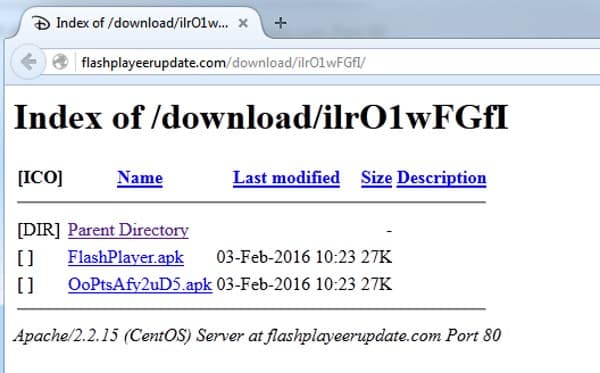
At this point, Android/Spy.Agent.SI contacts a remote server hosting malicious APK files whose corresponding URL paths are regenerated hourly in a bid to avoid detection by anti-virus software.
The trojan uses this connection to send information about the infected device, along with the package names of installed applications, to its operators. Stefanko explains that if any of the apps are identified as a target, the remote server responds with a list of 49 apps that Android/Spy.Agent.SI is equipped to attack via a phishing attack:
“The malware manifests itself as an overlay, appearing over the launched banking application: this phishing activity behaves like a lock screen, which can’t be terminated without the user entering their login credentials. The malware does not verify the credibility of the data entered, instead sending them to a remote server, at which point the malicious overlay closes. The malware does not focus only on mobile banking apps, but also tries to obtain Google account credentials as well.”

Just in case the victim’s account is protected with two-factor authentication, Android/Spy.Agent.SI also has the ability to send all SMS communications to the remote server upon request.
This allows the malware’s author to bypass 2FA protection.
Nick FitzGerald, a senior research fellow at ESET, put the threat into perspective when speaking to ABC News:
“We’re not seeing a large amount of this happening, but the fact that the bad guys behind this are now attacking the two-factor authentication mechanisms used by these banks means that it’s very likely that we’ll see more Android banking Trojan software, malware, and possibly smaller sorts of malware for other platforms doing this in the future.”
Fortunately, there are things you can do to protect yourself.
First, if you ever see anything masquerading as Adobe Flash Player on Android, you can be sure it’s a fake. Flash Player hasn’t created a client for Android since 2012, so there’s no way anything legitimate is still making the rounds on the mobile platform.
Second, you would be wise to install mobile apps from the official Google Play Store rather than less-trustworthy third-party sites, and should always keep a mobile anti-virus solution running on your phone as an added layer of defense.
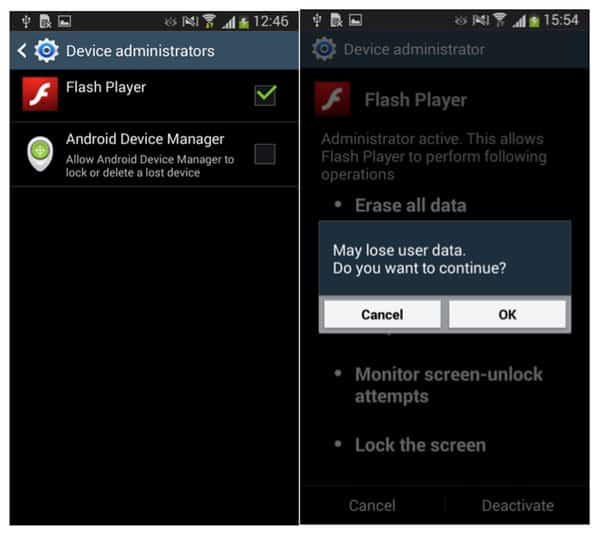
Last but not least, if you do become infected with Android/Spy.Agent.SI, you can remove the malware by disabling the fake Flash Player’s administrator privileges in Settings or by removing it while in Safe Mode.
For more information on the trojan, please read ESET’s report.


I get sick to the back teeth of seeing Android vulnerabilities: the platform seems to be riddled with malware and spyware. Installing 'untrusted' apps is the biggest way to compromise your mobile but there have been numerous cases where even 'approved' apps within the Google Play store have been infected with various viruses, trojans, malware etc.
In contract iOS and Windows Phone have very few vectors which result in system compromise and, for the Apple Store, a human reviews the app to ensure compliance (not perfect but a massive improvement on Google's automatic process).
'(not perfect but a massive improvement on Google's automatic process).'
Telling and scary then, isn't it, the risks of AI advancements (not that I didn't know this already) ? And Google being a champion of this is obviously relevant. But tell that to Google; they really don't care about anyone or anything but their supposed improvements to the world.
iOS has topped the CVE vulnerabilities list for the past two years. iOS gets hacked 8 times more often than Android despite having an eight of the market share. XCodeGhost was the single largest hacking incident in history with over 8000 infected apps on Apple's app store, and over 200 million iOS users compromised. Just, the security community has a double standard with Apple. You'll never actually get the truth about iPhones from them.
When 200 million iOS users got hacked by XCodeGhost, I stopped doing banking on my phones. They clearly aren't up to the task yet.
Apple and Windows Phone effectively sandbox their apps to mitigate against system-wide compromise. Granted this was a serious vulnerability but something which was remedied quickly by Apple.
None of this exists in Google play, these are present in rogue/unknown website. If you don't turn on install from 'unknown sources' you will never get infected. This threat is just exaggerated ,iOS and windows are as much prone to malware and vulnerabilities as Android. Android is open source so we it more in news.
These vulnerabilities do exist in the Google Play store though – admittedly unknown sources increase the risk.
The problem with Android is its fragmented nature as you've got to rely upon:
1: your mobile operator allowing you to install any updates
2: your handset manufacturer allowing you to install any updates
3: the updates working properly/being compatible with your specific device
With iOS you're almost always guaranteed (unless you're using a very old handset) to receive any updates. Apple have a very high number of customers using the latest version as a result: as of 7th March 79% of devices are using iOS 9.
https://developer.apple.com/support/app-store/
Comparatively a minuscule proportion of Android users are on the latest version.
http://www.droid-life.com/tag/distribution/
Windows Phone is considered by many experts to be the most secure.
http://betanews.com/2015/06/11/windows-phone-security-is-top-notch-says-kaspersky/
http://mspoweruser.com/hacker-claims-windows-phone-the-most-secure-smartphone-os/
I therefore don't accept your argument that the threat in Android is "exaggerated". Their OS is riddled with bugs that become public (and get ruthlessly exploited) and are the majority of their user base can't protect themselves because of the shoddy update process.
Also on many versions of Android full-disk encryption isn't enabled by default, another issue.
2.3% of Android users are on Marshmallow (the latest version of their operating system).
That's terrible.
Has ESET or anyone released any data about whether the 2FA program's effectiveness in reducing fraud makes it worthwhile on the whole? Is this really just of proof-of-concept? If the bank has the same or more fraud less than the cost of the program, get back to me, otherwise this is more FUD.