On the second Tuesday of every month, regular as clockwork, Microsoft issues security fixes for users of its software – protecting against newly discovered vulnerabilities and bugs.
And normally, the advice is to roll them out across your enterprise at your earliest opportunity – particularly in the case of the most serious critical security patches, which could be exploited by malicious hackers to spread a worm or compromise computer systems without the users’ knowledge.
In the crudest terms, it’s in Microsoft’s interest for your company to keep itself patched. Keeping computers protected not only helps avoid Microsoft’s software gaining a bad reputation for security, it also makes the internet a safer place for all of us. A win-win you might say.
But where things begin to break down is if Microsoft releases patches that don’t work, or cause conflicts, or if it’s forced to embarrassedly withdraw a security patch after it has been issued on Patch Tuesday after a bug is found.
And that, unfortunately, is precisely the problem which appears to have hit this month’s Patch Tuesday bundle.
Yesterday, Microsoft announced that it was recalling a botched security patch for Exchange Server that it had released the day before (Tuesday December 9) in security bulletin MS14-075.
That security bulletin was supposed to fix four different vulnerabilities – including an “Outlook Web App Token Spoofing Vulnerability” (known as CVE-2014-6319) that could allow a malicious attacker to send email that appears to come from another user.
In other words, an attacker could easily exploit the flaw to spoof a message – perhaps tricking recipients into taking an unsafe course of action (such as clicking on a link, or sharing information inappropriately).
Unfortunately, if you’re an organisation using Microsoft Exchange Server 2010 Service Pack 3, then you’ll see that the patch is no longer available for download. (Users of other versions of Microsoft Exchange Server appear to be fine).
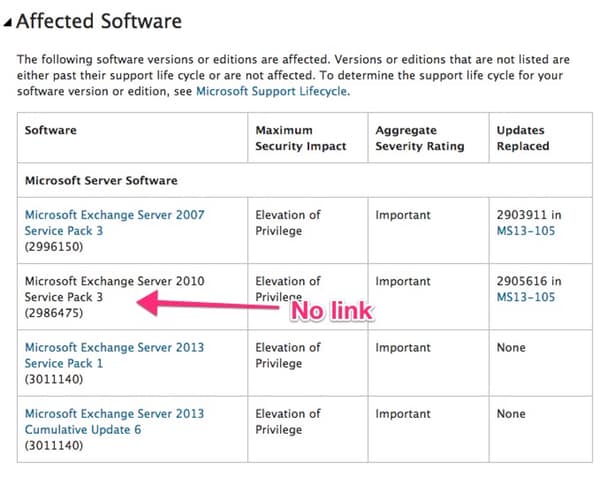
In a blog post Microsoft’s Exchange team explained that it has withdrawn the security update for Exchange Server 2010 SP3, and is advising organisations that have already installed it to rollback. The developers are promising to release a revised version of the patch as soon as they have been able to fix it.

“The update has been recalled and is no longer available on the download center pending a new RU8 release. Customers should not proceed with deployments of this update until the new RU8 version is made available. Customers who have already started deployment of RU8 should rollback this update.”
Unfortunately for Microsoft (and indeed its users) there have been a number of botched security updates in recent months.
But the problematical patch for Exchange Server SP3 isn’t the end of Microsoft’s Patch Tuesday woe.
It has also come to light that computers running Windows 7 Service Pack 1 and Windows Server 2008 R2 Service Pack 1 are experiencing problems after applying the latest update for the Windows Root Certificate Program (known as the KB3004394 update).

As PC World reports, Windows 7 users are being urged to uninstall the broken update because of the problems it can cause, including preventing graphics drivers from being installed and – perhaps most seriously – the prevention of installing future Windows Updates.
Ouch!
Microsoft has issued a fix which reportedly removes the faulty update from Windows 7 computers, or you can also uninstall it manually via Control Panel.
Clearly if there is the smallest chance that your Windows 7 computers may no longer update themselves because of the buggy security patch being in place, it makes sense to follow Microsoft’s advice and remove it.
Meanwhile, however, Microsoft’s reputation as a reliable provider of security updates takes another hit. The firm cannot afford to keep messing up every Patch Tuesday, or there is a risk that more and more companies will choose to hold off rolling out patches until they are sure that there aren’t any unwanted bugs lurking within.
This article originally appeared on the Optimal Security blog.


