The whole idea of being imprisoned is that you have some of your rights taken away from you.
Your right to pop down the shops for a carton of milk and Sunday newspaper, your right to choose a meal other than bread and water, and – in some countries – your right to vote.
And even though as a prisoner you may not have complete privacy, I do believe you have a right and expectation that your personal information and data should be treated with respect and properly secured from unauthorised access.
So it’s depressing to hear that researchers at VPNMentor have uncovered a data leak that has exposed prescription records, mugshots, and other sensitive information related to an unknown number of inmates.
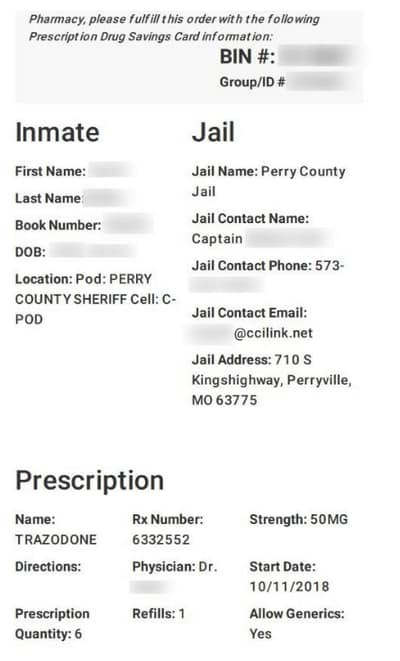
On January 3, the researchers found that over 36,000 PDF files had been exposed on an unsecured Amazon Web Services S3 bucket (natch) used by JailCore, a cloud-based app used by several US states’ correctional facilities. The researchers informed the company two days later, but hit a brick wall.
It was only when the Pentagon was informed on January 15 that the bucket was rapidly secured – presumably after pressure was applied on JailCore from above.
It’s not as though no-one has ever heard of the problem of leaving data in Amazon cloud buckets completely unsecured before. Countless organisations have had their incompetence on show for one and all, after leaving data accessible to anyone who happens to stumble across a URL – no password required.
This is the reason why Amazon has tried to help organisations avoid accidental misconfigurations that could result in sensitive data being exposed.
But then we shouldn’t be surprised by JailCore showing such scant disregard for security and privacy. Because, if all this weren’t humiliating enough, the researchers noted that JailCore’s website doesn’t use https…
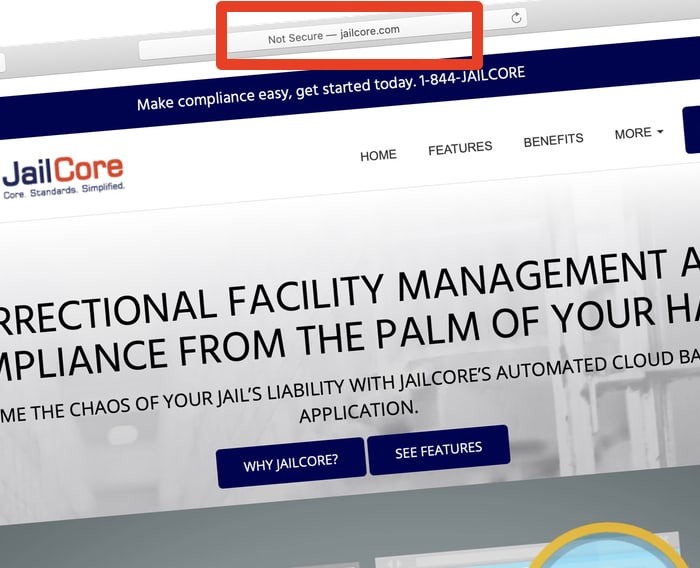
Yup, it’s 2020 and there’s no SSL padlock to be seen when you visit JailCore’s website selling software for prisons.