 If you’re one of those folks who likes to be a little alternative, and has chosen to use the Opera browser to surf the web (rather than better known names like Internet Explorer, Chrome or Firefox), then there is some important security news.
If you’re one of those folks who likes to be a little alternative, and has chosen to use the Opera browser to surf the web (rather than better known names like Internet Explorer, Chrome or Firefox), then there is some important security news.
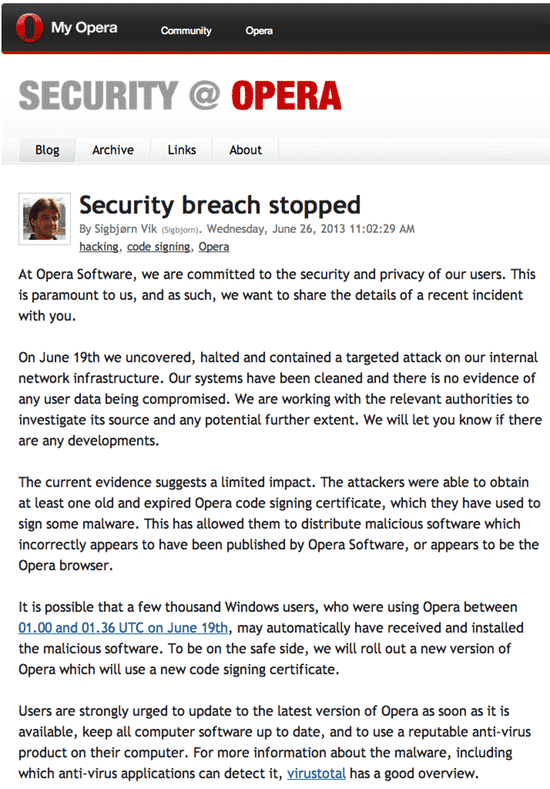
Opera Software, the Norwegian makers of the Opera browser, has gone public that its network was recently hacked. During the hack, criminals were able to steal “at least one” code-signing certificate, which they then used to sign malicious code.
As a result, says the company in a blog post by their security team, cybercriminals gave been able to “distribute malicious software which incorrectly appears to have been published by Opera Software, or appears to be the Opera browser.”
You can’t help but raise an eyebrow at the spin Opera is valiantly trying to put on the incident, titling their announcement “Security breach stopped”. And questions may be asked as to why it took Opera a week after they discovered the security breach before they went public with details.
The details of the precise nature of the breach, and how the hackers managed to take advantage of the situation, are still unclear. But hopefully Opera will be sharing more information for its users in the coming days. In these situations, transparency is often the only way to turn a potential disaster into an opportunity to rekindle some love from users.
To its credit, however, Opera has published a link to a VirusTotal page for the Windows Trojan that was signed using the stolen certificate, giving reassurance to some anti-virus users at least as to whether they are likely to be protected or not.
Sigbjørn Vik, a member of quality assurance’s team, wrote in the blog entry that the hackers could have exploited a 36 minute window of opportunity to spread their signed malware:
It is possible that a few thousand Windows users, who were using Opera between 01.00 and 01.36 UTC on June 19th, may automatically have received and installed the malicious software. To be on the safe side, we will roll out a new version of Opera which will use a new code signing certificate.
Users of the Windows version of Opera would be wise to visit the official Opera website, download the latest version, and ensure that their anti-virus is properly updated… Just in case.
The news of this security breach couldn’t really have come at a worse time for Opera.
Although the product’s supporters are notoriously outspoken about their preference for an alternative browser, their numbers have been dwindling for some time as they have been crowded out by the popularity of competitors such as Google Chrome.


