
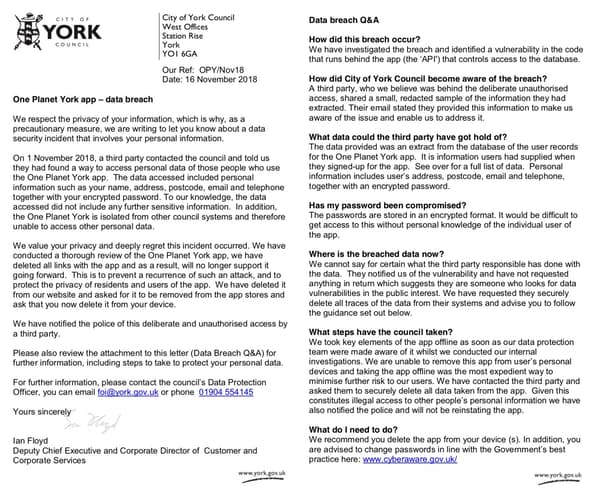
Earlier this month, the council of the British city of York contacted users of its One Planet York app, warning that an unauthorised third-party had accessed their personal information including name, addresses, postcode, email addresses, and telephone number, alongside their “encrypted password.”
The One Planet York app, which aimed to improve the city’s environmental performance by providing recycling advice and a bin collection calendar for residents, was said to contain an API vulnerability that could allow unauthorised parties to access personal data.
According to City of York Council, the app was permanently withdrawn and users were advised to remove it from their smartphones and change their passwords. According to a BBC News, almost 6000 people could be affected by the data breach which, the council said, had been reported to the police.
It’s a story we’ve heard before, right? Bad guy hacks service. Grabs lots of personal data with the possible intention of scamming innocent users, or breaking into their other online accounts. Cops on the trail…
Well, not so fast.
Because if you read a little deeper, you find out just how the council discovered its app had a security hole:
How did City of York Council become aware of the breach?
A third party, who we believe was behind the deliberate unauthorised access, shared a small, redacted sample of the information they had extracted. Their email stated they provided this information to make us aware of the issue and enable us to address it.
That’s not a huge amount of detail, but that sounds very much like a vulnerability researcher discovered a security hole in an app used by thousands of people, and reported the problem privately and responsibly.
So what has happened to the data now? The City of York Council says it can’t be sure, but attempts to reassure users that the person who contacted them appeared to be publicly-spirited rather than criminally-minded.
Where is the breached data now?
We cannot say for certain what the third party responsible has done with the data. They notified us of the vulnerability and have not requested anything in return which suggests they are someone who looks for data vulnerabilities in the public interest. We have requested they securely delete all traces of the data from their systems and advise you to follow the guidance set out below.
Some in the computer security community feel that the council over-reacted by reporting the incident to the police. See this tweet from HaveIBeenPwned’s Troy Hunt, for instance.
This breach notice from @CityofYork doesn’t feel good: are they saying they built a product with a vulnerability in it, someone reported it to them privately and now they’ve called the cops? Geez I hope not. pic.twitter.com/eQwyRwahf2
— Troy Hunt (@troyhunt) November 26, 2018
And I agree that this particular wording in the notification letter to users does feel uncomfortable:
“We have notified the police of this deliberate and unauthorised access by a third party.”
It’s not as though anything in that sentence is untrue. It *was* deliberate access, and it was done without the permission of the council. But the implication is that it was also done with criminal intent.
Words matter.
After all, the last thing we want is to strike fear into security researchers that responsibly disclosing vulnerabilities might lead to their collar being felt.
But was informing the cybercrime-fighting authorities necessarily inappropriate? I’m not sure it was.
On Twitter, the council said that it attempted to discuss the security incident with the person who informed them (and to understand their actions) but received no reply.

Ask yourself this, if you were a public body who had apparently left thousands of citizens’ personal information exposed for unauthorised parties to access – wouldn’t you think it’s better to cover all your bases, rather than cross your fingers and hope things will turn out alright?
Even if the vulnerability reporter had no intention of exploiting the vulnerable data, who was to say that others might not have taken advantage of the same security hole with malicious intent?
Maybe the advisory to One York App’s users could have been written more carefully, but I’m not sure – from what has been disclosed publicly so far – that they really did anything else that wrong in their handling of this incident.
For its part, North Yorkshire Police’s Digital Investigation & Intelligence Unit today sent out a positive message reinforcing its belief that the researcher had acted properly and that responsible vulnerability disclosure was an important part of security.
@troyhunt @Scott_Helme We are aware of the York 'data breach' but please be reassured we don't regard this incident as criminal. We recognise the benefits of software vuln disclosure as part of a healthy security environment and the researcher has acted correctly.
— N Yorks DIIU (@NYPDIIU) November 26, 2018
The story it seems is this: Guy found software vulnerability in app, app withdrawn, users advised to change their passwords in an abundance of caution.
Lets hope that no-one else exploited the vulnerability, and rather than devoting too much time on beating up City of York Council we devote a little more effort into wondering what other vulnerable apps might be out there that could be leaking innocent users’ data.
Update November 27 2018: More details on One Planet York app vulnerability don’t paint council in a good light


