A critical vulnerability in a WordPress plugin used on over one million websites has been patched, after evidence emerged that malicious hackers were actively exploited in the wild.
WordPress has pushed out a forced automatic update to the widely-used Ninja Forms plugin after security researchers.
According to an analysis by experts at WordFence, the vulnerability “could allow attackers to execute arbitrary code or delete arbitrary files on sites.”
In short, an unauthenticated attacker could exploit the security hole in the Ninja Forms WordPress plugin to run code of their own choice, and gain complete control over a vulnerable website.
Nasty. And clearly WordPress thought so, as it appears to have initiated a forced update to third-party WordPress-powered websites running vulnerable versions of the plugin.
That forced update to the plugin took some website owners by surprise, as it occurred without any prior communication:

Website administrators who view the Ninja Forms changelog may not initially recognise quite how serious things the vulnerability was:
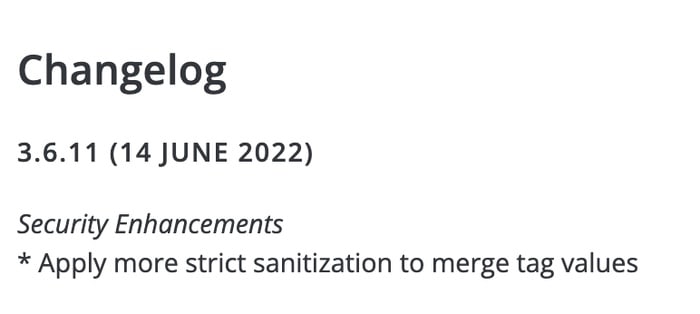
3.6.11 (14 June 2022)
Security Enhancements
* Apply more strict sanitization to merge tag values
If you run the Ninja Forms plugin on your WordPress website, make sure that you are running the latest version. According to Wordfence, the flaw has been fully patched in versions 3.0.34.2, 3.1.10, 3.2.28, 3.3.21.4, 3.4.34.2, 3.5.8.4, and 3.6.11.


