The Wall Street Journal published a fun article yesterday by Robert McMillan, cutely entitled “The Man Who Wrote Those Password Rules Has a New Tip: N3v$r M1^d!”.
Here’s part of the article:
Long, easy-to-remember phrases now get the nod over crazy characters, and users should be forced to change passwords only if there is a sign they may have been stolen, says NIST, the federal agency that helps set industrial standards in the U.S.
Amy LaMere had long suspected she was wasting her time with the hour a month it takes to keep track of the hundreds of passwords she has to juggle for her job as a client-resources manager with a trade-show-display company in Minneapolis. “The rules make it harder for you to remember what your password is,” she said. “Then you have to reset it and it just makes it take longer.”
When informed that password advice is changing, however, she wasn’t outraged. Instead, she said it just made her feel better. “I’m right,” she said of the previous rules. “It just doesn’t make sense.”
Academics who have studied passwords say using a series of four words can be harder for hackers to crack than a shorter hodgepodge of strange characters— since having a large number of letters makes things harder than a smaller number of letters, characters and numbers.
It’s an enjoyable article, but what it fails to tackle is one of the central challenges for all of us who use passwords. No, not the challenge of generating a memorable but hard-to-crack password. The challenge is how are we going to do that over and over and over again.
Because the simple truth is that we need a lot of passwords to run our online life (I have over 1000), and security experts tell us that it’s a very bad idea to reuse the same passwords in different places.
The problem with all advice about how to concoct passwords is that it simply doesn’t scale to deal with our need to have oodles of different passwords.
It’s all very well educating the public how to make a decent password if they only have one, two or three passwords to remember… but what happens when they go on the internet, and start needing new passwords faster than a one-legged man in a butt-kicking competition?
I’ve been on the internet for almost 30 years and, like I said, have well over 1000 different passwords. There’s no way I can remember them all. It’s this problem which makes people keep choosing dumb, easy-to-guess passwords or (worse) reuse the same passwords over and over again.
The only sensible advice is to use password management software that generates long, complex passwords for you… and then stores them securely for you. Meaning that you – with your puny human brain – don’t have to attempt to remember them.
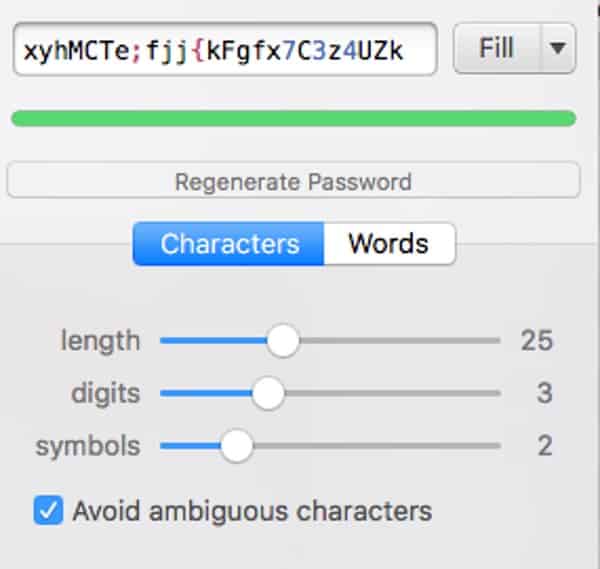
If you find passwords a burden – simply use password management software like Bitwarden, 1Password, and KeePass to make them both safer and easier to remember.
Do that, and you won’t have to remember your passwords, and you won’t have to remember your secure method of making up passwords. You now have a program that does it for you.
Oh, and by the way, I agree with NIST’s advice that users should be forced to change their passwords only if there is a risk that they have been breached, for reasons I have previously described.
For further discussion on passwords, make sure to listen to this episode of the “Smashing Security” podcast:



why not listing lastpass?
If you keep up with the infosec News, they have made News often, so, google them, with "vulnerabilities" and find out.
Password managers sound great in many ways, but I don't trust cloud syncing for my passwords, even if they're encrypted or whatever. Is there a password manager that's multi-platform (desktop and mobile) and doesn't require you to put your passwords in the cloud?
You could use one of the various free software tools, and sync the repository between devices.
However whichever method you choose to sync your store will almost certainly be less secure than a dedicate cloud service for the same thing. Nearly all the mobile file sync software is awful.
This was part of the pain with 1Password in earlier versions, they pushed you to DropBox for sync, which was horrid and way less secure than LastPass's cloud sync, not least they leaked a lot of metadata to DropBox. 1Password are now moving to a cloud service as I understand it, although I'm not sure if it is mandatory.
I understand your hesitation, but if the password manager is properly encrypting, salting and hashing your passwords before it puts any data into the cloud then it's not really putting your *passwords* in the cloud is it?
It's just putting a blob of encrypted data in the cloud, that – again, if you've chosen a decent password manager, – can't be turned back into your passwords by an unauthorised party (or indeed the password manager vendor) because they don't know the private key you're using.
My belief is that for the typical password manager user it's probably better for security to use the cloud to keep in sync than create your own Heath Robinson solution.
Graham-
My concern is this- using a Password Manager is fine at home, but what if we are not allowed to install the software on work computers? Then we can't use the Password Manager because we have no idea what the hashed passwords are!
Many password managers allow you to access your password vault via a web interface – so no need to install a client.
Or there are smartphone apps of course.
I like Dashlane, had problems with LastPass… Graham, old buddy [I talk like that when I want an undeserved favor] how about an article about password managers?
What do you want me to say about them?
I think they're a great idea – and everyone should use one!
Well, I am sure they're a great idea. Security experts such as yourself tell us so, and I don't doubt it. But what would be great would be an article that explains how to choose one and how to use one in terms that my mother could understand. I myself don't use one because I am unsure how it would cope with my 2 Macs, android phone, iPad and what I would need to do if using an unfamiliar computer to access certain accounts (eg a client's Mac to access my Shutterstock account). I really am worried that I would lock myself out of my digital life. A Password Manager 101 article for total n00bs would really help – and might increase uptake of your advice.
Hi Paul,
I use in a similar setup the Keepass 2 on Android and MiniKeePass on iOS with separate Kee-file. I distribute the db manually once a week when changes have occured.
In my opinion an almost failsafe although slow system…
How about an article reviewing the major players in the industry, advantages/disadvantages of their way of implementing the solution and so on? Perhaps some history of the company, any breaches they may have suffered so people can make informed decisions. Plenty of your regular readers will already use one or have a preference but I'm willing to bet that some won't, and it would be an article I could point people towards who should be using a password manager but think they are too complex/not secure enough etc.
Thanks for the suggestion, but I'm not set up to do proper reviews of software – which is why you won't find any on this site. My view is that if you can't do something properly, don't do it!
The good news is that there are plenty of other sites out there which do software reviews.
I'd prefer this site to focus instead on commenting on computer security news, offering practical "how-to" advice, and emerging threats.
Sophos did a series of articles on password managers last year I think. And Troy Hunt has started a series on Passwords last week, to be continued. Just google the subject, there's tons of material out there.
I'm right there with you Max! I too am fond of Dashlane and have been using it for more than a year.
Lastpass does it for me every time. I splashed out on premium membership and bought a 2sv Yubikey for £15 several years ago. Even if someone had my Lastpass password, they'd need my Yubikey to log in.
Agreed, Password managers are really a thing with us IT Pro's, well.. atleast for those who want to enforce good passwords on their accounts.
However, there are sites that do not allow copy/paste with the password field when you reset your password. This is specially hard when you are migrating to a more secure password from a password manager, the last site that I had to deal with, with this kind of issue was paypal. I had to disable the javascript on the reset password page so that I can put in a more secure password from KeePass.
Then I tested the Perform Auto-Type to have KeePass type in my user name and password, then bam! Good result!
Also, I had to memorize atleast one username/Password combination because I put in my database on a OneDrive and I atleast need to access my OneDrive in a worst case scenario where I need to redownload my entire password database.
Hi Android users,
I can't stress enough, that "Keepass 2 for Android" is the safest available app. With the built-in keyboard, that does auto-fill too, it completely bypassed the insecure use of clipboard. You can keep it local, or sync to Cloud storage in settings. And Keepass is available for all other platforms as well. Many Security pro's recommend them.
+1 for bitwarden! All their apps are great.
As we all have read about many apps, mfr's claims about their security often aren't lived up to. This software introduces a vulnerability: the 1 key that unlocks the password 'safe', the metakey to the kingdom, in addition to holding all the individual passwords. If there's one type of software that is most attractive to compromise, this is it, so it's safe to assume nation-states would put a lot of effort into compromises – a zero day for the most popular ones would command a hefty price. So while a password mgr is a practical & great idea, esp for warehousing many passwords as the article says, what independent assurance exists the password software doesn't have security problems? The mere facts a lot of people like it or it's been around a long time doesn't mean it's secure. Where's the published independent hard core cracking/penetration testing of this genre of software? How do we know the encryption algorithm and it's implementation is truly secure, the random # generator used doesn't have 'holes', the software doesn't have any back doors or secret master keys, and it doesn't leave a trail that facilitates cracking? Is authentication & encryption used for performing updates? Etc etc.
Also, what happens at the border when your device is seized and access demanded? One master password unlocks the entire private kingdom. The more apps' passwords you leave out of the password mgr, the less useful it is & the more likely a less secure log of them will be used. And in some jurisdictions, for now, it matters legally if the database is in the cloud or in the device/on person.
Okay, DaB, I had come back to this page to ask the same question that you have put forward: Wouldn't a password site be the best possible site to hack?
Time and time again Graham has talked about hacks and about malicious code slipped into software. Why wouldn't password generating software be the ideal place to hack into?
Why should we trust this software, Graham???
"Wouldn't a password site be the best possible site to hack?"
Only if there was some way to reverse the encrypted, salted hashes back into their original password form.
I think an attacker might find it simpler to attack the user's actual computer.
Even if the encryption algorithm and random # generator don't have flaws, there's plenty that can go wrong in implementation (as Bruce Schneier has often written about), multiplied by the # of platforms it's released for & an individual has. Involving the cloud & cross-platform capabilities adds more opportunities for flaws & weaknesses. That's all where rigorous 3rd party testing of password managers is crucially needed. NOT: popularity contests, features lists & mere product description "reviews" (aka PR). This is as much an issue for SMB & corporate password protection, esp in a BYOD environment, so there's a lot at stake here.
I agree completely with Graham common practices are abysmal, but a flawed password manager yields an immense amount of use leverage compared to breaking into different individuals' devices one at a time and avoiding their gauntlets of intrusion prevention measures etc. How do we know migrating to a given password mgr isn't going from the frying pan into the fire? Buying false security?
This is a weak link case: If somebody wants into your bank account, health information via your patient portal, and strongly protected info, what's the weak link to it all if your strong access passwords to everything highly protected are all in one place via one piece of software with one master password? It may be common that devices are hacked, but there also could be attacks that involve both device and password mgr software at various steps. What we can rely on is they'll do whatever is necessary to compromise such software due to it's high value contents, so locking down devices isn't necessarily sufficient if the password mgr is flawed.
Bottom line is the password mgr must be bulletproof and we all need to see the results of rigorous testing of this genre of products/services. It's AWOL, at least in the public domain, which raises the Q if unpublished testing was done why isn't it public? The possibilities are ominous! If this genre of products were all bulletproof, there would be no incentive or value in withholding testing results……
So we need bug bounties, plus hack into contests at the conferences, AND rigorous real 3rd party published testing.
"Also, what happens at the border when your device is seized and access demanded? One master password unlocks the entire private kingdom."
Some password managers have recognised this issue, and developed "travel modes" which allow you to reduce the risk:
https://blog.agilebits.com/2017/05/18/introducing-travel-mode-protect-your-data-when-crossing-borders/
You're right, of course. It's very hard to be 100% certain of anything and there's always the possibility that a vulnerability exists, or that a service has been nobbled by bad guys or over-reaching intelligence agencies that might leave you exposed in some fashion.
All I can say is that what most people are doing with passwords is a recipe for complete disaster, and as a security professional I feel the best course of action that I, and regular members of the public, should follow is to use a decent password manager.
Masterpassword is the answer to the problem of not having your passwords stored in the cloud. http://masterpasswordapp.com/
No passwords are stored anywhere, but are generated for any given website by a fixed, deterministic algorithm which is the same in every device on which it runs. There is also a Firefox extension available.
I looked into LastPass' corporate edition, and found an interesting feature: the Administrator can reset any user's password. Certainly a useful feature in a corporate setting. Or, is it? This reset doesn't break the password storage (as, for example, it does on macOS with a Keychain reset). I asked LastPass how this is possible, and how can I be certain they don't have this capability to reset *my* password. Their answer: vague promises and irrelevant information about their fine IT infrastructure. The fact remains, LastPass can reset your password, just as a corporate administrator can reset an employee's password.