
As I reported earlier this month, there’s an unpatched zero-day vulnerability in Internet Explorer that is being exploited in targeted attacks.
Microsoft still hasn’t issued an official patch for what is technically known as CVE-2020-0674, but did detail what it described as a “workaround” in its security advisory, suggesting that concerned users might want to consider restricting access to JScript.dll.
But wait, there’s a problem.
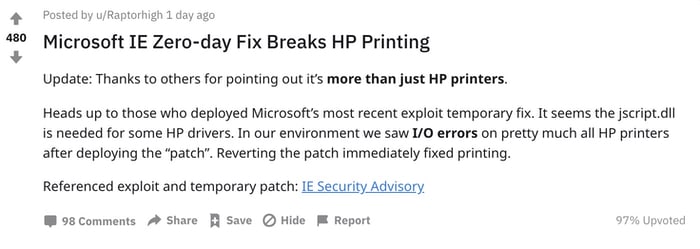
Users are now reporting on Reddit that after they applied the workaround they began to see errors when printing.
Microsoft says it is only aware of “limited targeted attacks” related to the Internet Explorer zero-day vulnerability. You’ll be the best judge as to whether your organisation needs to take that threat seriously, or whether it would prefer to have working printers.
If you need to undo the workaround, here are Microsoft’s instructions from the original security advisory:
How to undo the workaround
For 32-bit systems, enter the following command at an administrative command prompt:
cacls %windir%system32jscript.dll /E /R everyone
For 64-bit systems, enter the following command at an administrative command prompt:
cacls %windir%system32jscript.dll /E /R everyone
cacls %windir%syswow64jscript.dll /E /R everyone
Stay safe folks.


