While the world continues to wait for Kaseya to issue an update to patch VSA installations against a vulnerability exploited by the REvil ransomware gang, security firm Malwarebytes has spotted a malware campaign which is taking advantage of the vacuum.
In a tweet, security researchers shared details of a malicious email that was sent to a business in the UK, posing as a security update.
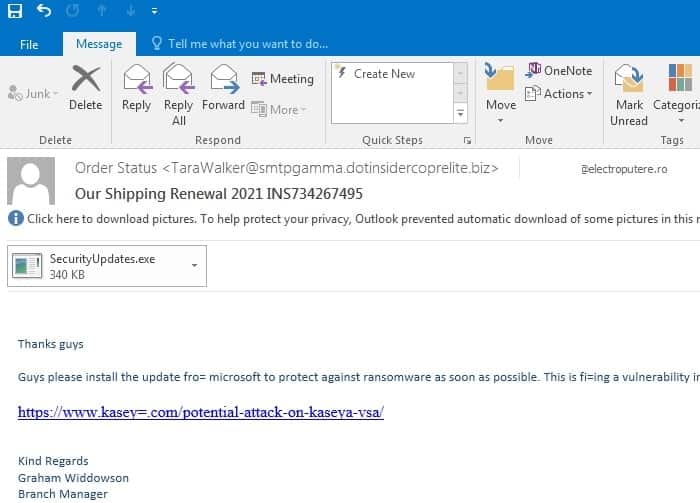
Guys please install the update for microsoft to protect against ransomware as soon as possible. This is fixing a vulnerability in Kaseya.
Attached to the email was a file called SecurityUpdates.exe, and the link itself actually pointed to a server containing a malicious download.
The intent of the attack appears to have been to install Cobalt Strike, which could have granted malicious hackers remote access to the targeted company’s network and PCs.
It should go without saying that you should always get security updates directly from the vendor, rather than trust attachments and links that have been emailed to you.
The latest news from Kaseya is that its attempt to bring its SaaS services back online has failed, missing its original intention of making systems online and accessible by July 7th 6AM US EDT:
During the VSA SaaS deployment, an issue was discovered that has blocked the release. Unfortunately, the VSA SaaS rollout will not be completed in the previously communicated timeline. We apologize for the delay and R&D and operations are continuing to work around the clock to resolve this issue and restore service. We will be providing a status update at 8 AM US EDT.
It’s unclear presently whether its patch for on-premises VSA software is similarly delayed, but I wouldn’t be surprised.