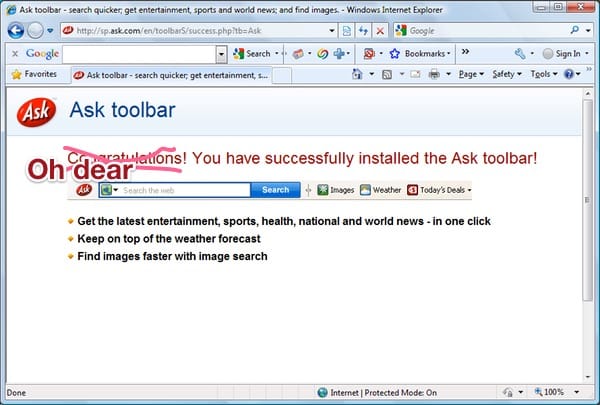
For years people have been opening their browser and asking, “how the heck did that Ask Toolbar get installed?”
Chances are that if you don’t have the Ask.com search toolbar haunting your PC, you may have friends or family who are afflicted.
Normally the Ask toolbar is installed in a slightly underhand fashion. Users install the likes of Java (as though there weren’t a mistake in itself!) and have unwanted additional software foisted upon them, as they fail to read the small print and don’t spot that they’ve accidentally agreed to install the Ask.com toolbar.

The good news is that the Ask toolbar isn’t malware. It definitely cannot be compared to something as out-and-out evil as ransomware, for instance.
But in the eyes of most security companies it is definitely a “potentially unwanted program”, changing your browser’s default search engine and delivering contextual advertising.
In the past, even Microsoft described the Ask Toolbar as “unwanted software”, and updated its anti-malware products to detect and remove older versions of the Ask Toolbar because of its meddling with search engine results.
All of which, to my mind, is good enough reason to consign the Ask toolbar to the garbage can.
 But there’s more.
But there’s more.
Last November, for instance, malicious hackers hijacked the Ask Toolbar’s update mechanism to cause it to download malicious code onto unsuspecting users’ PCs.
And now, security firm Carbon Black has revealed that despite the efforts of the Ask Partner Network (APN) to fix the issue, the attacks continued:
Last November, our partner Red Canary reported on a supply-chain compromise of APN, distributors of the Ask.com toolbar. This compromise allowed malicious software to be signed and distributed as though it were a legitimate Ask software update.
APN responded quickly to address the problem, revoked the compromised certificate and distributed software updates to customers. This should have been the end of the story, but it unfortunately wasn’t.
One month later, Carbon Black detected and stopped an attack that originated from the APN Updater using malware signed with the certificate issued after the November incident. Analysis by the Carbon Black Threat Research team confirmed this to be a continuation of the earlier activity, and indicative of a sophisticated adversary based on the control of a widely used update mechanism to deliver targeted attacks using signed updates containing malicious content. The investigation revealed these activities to be part of a larger campaign spanning at least the end of 2016 and into 2017.
According to Carbon Black’s researchers, attackers had launched a remote command shell within 60 seconds of gaining access to a targeted computer, and it only took 45 minutes to capture credentials and begin moving laterally across the victim’s network.
Fortunately Carbon Black has worked closely with APN, and has seen no recurrence of the attacks.
Nonetheless, it’s worth remembering that you create a bigger attack surface for malicious hackers to attack everytime you introduce toolbars and browser extensions onto your computer.
So why allow unnecessary ones like the Ask Toolbar to sneak onto your systems?
My advice? Remove the Ask Toolbar, and eradicate it from the computers of your friends and family too.



I found some users reaching out to ask.com , despite fairly aggressive purging of the toolbar.
Found the root of the problem, a few had selected Norton Safesearch within the Chrome browser.
Norton and Ask have "teamed up" as they say in an announcement on the Norton website.
Ask is one of the worst companies to ever exist. Their search engine is so useless they need to pay companies to bundle it. When are they going out of business?
From memory – a few years ago now – the ASK toolbar was definitely NOT easy to remove
and was designed to be so – this is why APN should be prosecuted.
Since first encountering it, I have considered the Ask toolbar a close approximation of malware, to be extirpated as quickly and ruthlessly as possible.