Sheesh.
Check out this newly published knowledgebase article from McAfee Intel Security:
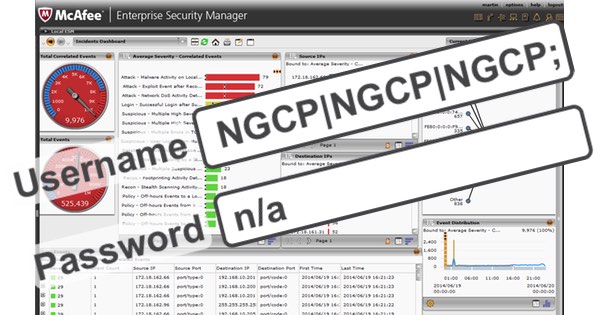
A specially crafted username can bypass SIEM ESM authentication (password is not validated) if the ESM is configured to use Active Directory or LDAP authentication sources. This can result in the attacker gaining NGCP (master user) access to the ESM.
This update resolves an issue where the login username is mishandled.
CVE-2015-8024
McAfee Enterprise Security Manager (ESM), Enterprise Security Manager/Log Manager (ESMLM), and Enterprise Security Manager/Receiver (ESMREC) 9.3.x before 9.3.2MR19, 9.4.x before 9.4.2MR9, and 9.5.x before 9.5.0MR8, when configured to use Active Directory or LDAP authentication sources, allow remote attackers to bypass authentication by logging in with the username “NGCP|NGCP|NGCP;” and any password.
https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-8024
I’m speechless.
In fact, I don’t think I believe my eyes. So, let’s let that sink in…
You can login remotely as an administrator to McAfee Enterprise Security Manager using the username “NGCP|NGCP|NGCP;” and it doesn’t care what password you enter.
Nope, still finding it hard to believe.
It beggars belief doesn’t it? In case you had forgotten, McAfee was a security company.
If your company is going to continue using McAfee Enterprise Security Manager please ensure that the patches are installed. Pronto.
Hat-tip: The Register.



'You can login remotely as an administrator to McAfee Enterprise Security Manager using the username "NGCP|NGCP|NGCP;" and it doesn't care what password you enter.
Nope, still finding it hard to believe.'
This reminds me of the old r* UNIX services. Depending on configuration (that could be user specific or system specific) you could have it so as long as you use the correct login you don't need a password. It could be that it is from any host or a specific host[1] but the end result is many systems were vulnerable to the first part of being rooted (…assuming that the system didn't allow root access without a password..and I'm sure there were many where this did happen). People would argue that it doesn't matter if the attacker has root on their own box but they're missing something here – if they do they can create any user so they can login to a remote system with a different name just as easily.
Needless to say, the r* services are long obsolete.
[1] Trust relationship can be exploited. This is one of those places where DoS attacks were useful (at least in part of the attack). But many didn't care what host you come from as long as it is the same user name. Laziness and security do not mix.
I guess little Bobby Tables has found a job at McAfee…
Wow! But not totally surprised! A few yeas ago,a researcher name Koret discovered many vulnerabilities in security products of the top 14. And it gets worse for McAfee,and others, because they have other vulns. Read here at Security Week:
http://www.securityweek.com/critical-flaw-found-avg-mcafee-kaspersky-products . And so,the question needs asking,do security product protect more,or do they only increase the attack surface? I'm starting to wonder too if this is careless coding, or accidentally on purpose back doors,giving plausible deniability? I mean,we see these kinds of openings in all kinds of products these days. Thank God for the researchers!! And blogs like this to keep us informed.