
If you’re a long-time Twitter user, you’ve probably come across your fair share of third-party apps. Most of these tools exist for completely harmless purposes – analysing your follower metrics, scheduling posts or posting results from a quiz.
In a nutshell, third-party Twitter apps are applications that are built to run on Twitter’s API platform but are not owned by Twitter. Hootsuite, Buffer, Klout and Pinterest application are all examples of legitimate third-party services that have apps which can connect to your Twitter account.
Twitter’s Application Permission Model is flexible, meaning that third-party apps can request varying levels of account access. It’s likely that you’ve come across these when clicking through the “Authorise This App” permission screen.
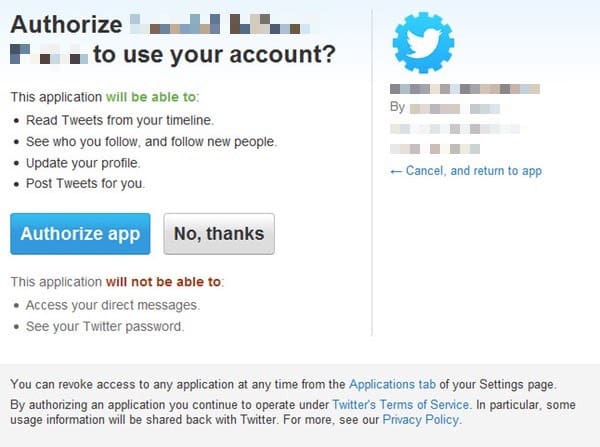
You’ll typically find that some third-party Twitter apps ask for much fewer permissions than others. For instance, some will only want read access to your tweets, whereas others might also want to be able to post messages on your behalf.
The case of Twitter Counter
Tracking over 350 million Twitter accounts with two million users, Twitter Counter is a major contender in the social analytics space. A popular choice for startups and large firms alike, the Amsterdam-based outfit provides insights and promotional services with a scalable range of pricing plans.
Imagine the confusion and surprise when some high-profile accounts started spouting crudely constructed ads at the end of last week, urging users to click on a link if they wanted more followers on Twitter.


As I tweeted at the time, what connected the hijacked accounts was that all the spam messages could be tied back to API calls from Twitter Counter.
https://twitter.com/SecurityYasin/status/799887650631151616
Victims included popular brands and well-known organisations such as The Next Web, HTC, Withings, the Red Cross, PlayStation and Xbox. In addition, prominent individuals such as pro footballer Lionel Messi and actor Charlie Sheen were also affected.
Twitter Counter confirmed there was a problem by (appropriately enough) tweeting about it:
https://twitter.com/thecounter/status/799992721792331776
By all accounts, the malicious actors abused a cookie storage function to impersonate users on a one-by-one basis. Twitter Counter CEO Omer Ginor confirmed the nature of the incident in an press statement issued three days later.
Despite the screw-up, Ginor’s apology assured users that they were now safe, and that Twitter Counter does not store users’ Twitter credentials nor payment details in any form.
“Twitter Counter is deeply sorry about the spam posts which were posted via our service and we sincerely apologize to the affected users. As the industry’s prime service for Twitter account analytics, our users’ account security is of paramount importance to us. We are committed to providing the most insightful Twitter marketing tool within the highest standards of privacy and security the most secure service for small and large brands to use. This attitude has enabled us to be a market leader and we intend to stay true to it. The security vulnerabilities we’ve had are being sealed and we are confident that this is an isolated incident. We know who the hackers are and are going to take legal action against them to make sure they can’t commit such acts again nor profit from them.”
Of course, Twitter Counter isn’t the first service to be abused by hackers in this way in order to send spam – a notable prior example is the Buffer hack of 2013 – and it probably won’t be the last.
For that reason it makes good sense to have a spring clean of what apps can access your Twitter account from time to time, and to exercise caution about which ones you allow in future.
Audit your apps
Fortunately, checking the apps that can access your Twitter account is a very straightforward process. Simply log in to your Twitter account, visit Settings and look for the “Apps” option (or click on this link).
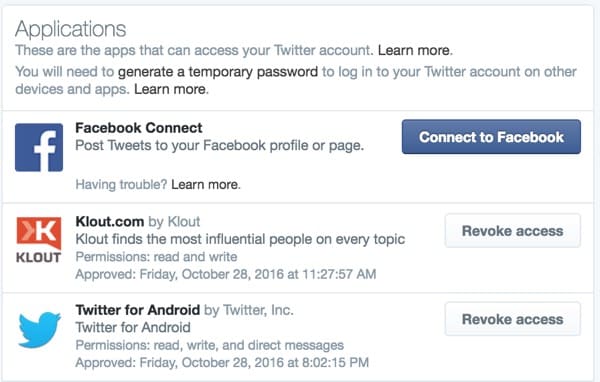
Revoking apps and signs of compromise
Revoke access to any apps you’ve stopped using or are unsure about. If you think your account has been compromised, refer to Twitter’s help guide for further details.
The telltale signs that your Twitter account might have fallen under the control of a third-party app running rogue include:
- Unexpected Tweets posted from your account
- Unexpected Direct Messages sent from your account
- Unauthorised follows, unfollows and blocks
- Compromised account warning from Twitter
- Changed account details alert from Twitter
- Locked out after an unexpected password change
Remain cautious of third-party applications, especially those promising to get you a large number of followers quickly, monetise your account, or gain “blue-tick” Verified status.
By the way, don’t forget to enable two-step verification (if you haven’t already) for an additional layer of security from other threats.


