Security experts at Fox-IT are warning of a malware campaign that they have seen spammed out in the Netherlands.
Researcher Maarten van Dantzig warns that large numbers of emails have been sent out using Dutch text in both the body of the email and the attached boobytrapped Word document.
What makes the attack particularly interesting, explains Maarten van Dantzig, is that the emails have been constructed using information taken from LinkedIn profiles, in an attempt to make them look more convincing with the intention, one assumes the criminals hope, of more people opening the poisoned attachment:
“The first name, last name, role and company name are all values that are taken from the LinkedIn page of the receiver of the phishing mail, giving the e-mail a very personalized look.
“The subject of the e-mail contain the company name, with a semi-random invoice related subject.”
Furthermore, the malicious Word document’s filename is also based on personal information of the receiver:
Company-Firstname-Lastname.doc
As I have described before, if you’re a criminal and want someone to open your malicious email – disguising your targeted attack as a LinkedIn message might be one of the best tricks you have. These emails don’t come from LinkedIn itself, but their use of accurate information that you have stored in your LinkedIn profile will surely help them to appear more convincing.
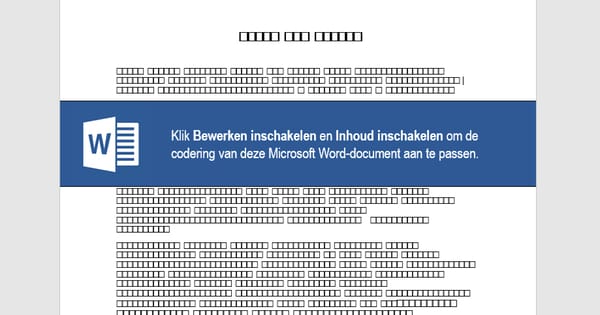
If you make the mistake of opening the attached .DOC file, you will be presented with what appears to be a garbled document – presumably to trick unsuspecting recipients that they will need to enable macros to view the content.

As regular readers of this site will know all too well, enabling macros in Microsoft Word documents can be all that a cybercriminal needs to run malicious code on your computer.
Fox-IT reports that the malicious Word macro code attempts to download the Zeus Panda banking malware to victims’ computers.
It’s not known whether the carefully-composed attack has been crafted using data recently released from the LinkedIn mega breach, but it’s a clear sign of just how much damage can be done by a data leak – even if you are no longer using the same passwords.
And remember this – if online criminals can launch a campaign like this in Dutch, they can launch it in any language they choose.



…grammatically wrong Dutch by the way. Clearly a non-Dutch, or a very low educated one must have written this short text.