
Lenovo is urging users to uninstall its Accelerator application following the discovery of a serious remote code execution (RCE) vulnerability.
The Chinese multinational technology company recently published a security advisory that provides some details about CVE-2016-3944, a high-severity RCE flaw:
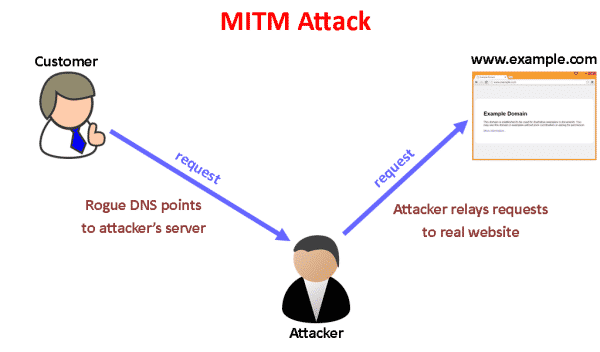
“A vulnerability was identified in the Lenovo Accelerator Application software which could lead to exploitation by an attacker with man-in-the-middle capabilities. The vulnerability resides within the update mechanism where a Lenovo server is queried to identify if application updates are available.”
The Accelerator app helps speed up the launch of Lenovo applications. It comes installed in some notebook and desktop systems preloaded with the Windows 10 operating system, which means 46 notebook and 25 desktop lines including the Erazer and IdeaCentre are affected.
The vulnerability does not affect Lenovo ThinkPad or ThinkStation devices, as the Chinese computer corporation never installed the Accelerator app on either product types.
Man-in-the-middle (MitM) attacks are no laughing matter. They occur on either a machine infected with a malware variant that comes with surveillance capabilities or on a vulnerable web browser that is communicating with an infected server.
Attackers use MitM campaigns to intercept and steal users’ login credentials, financial data, and other personal information. Oftentimes, users won’t even know their communications are being intercepted before it’s too late.
CVE-2016-3944 is just one of a dozen vulnerabilities spotted by Duo Security in a review of several original equipment manufacturers (OEM) updaters, or software responsible for updating a computer once it is first booted up after being purchased.
The security firm is careful to note that most of these OEM updaters are junk software or “bloatware” that allegedly add value but in actuality do very little to facilitate a new computer’s initial boot-up.
In its study, Duo found high-risk vulnerabilities affecting Dell, Hewlett Packard, Asus, Acer, and of course Lenovo.
These results call to the mind last year’s Superfish fiasco, only this time it’s apparent bloatware is an industry-wide problem that affects all types of vendors. As Duo researchers warn in their paper:
“The OEM software landscape is complicated and includes a depressing amount of superfluous tools for vendor support, free software trials, and other vendor-incentivized crapware. Some apps do nothing more than add a shortcut to launch your web browser to a specific site.”
Lenovo is not bothering to fix this flaw. The Accelerator app is bloatware, so it feels it has no need to do so. Instead it is urging users to uninstall the app altogether by going to “Apps and Features” in Windows 10, selecting the Lenovo Accelerator Application, and clicking on “uninstall.”
Good riddance.



'Man-in-the-middle (MitM) attacks are no laughing matter. They occur on either a machine infected with a malware variant that comes with surveillance capabilities or on a vulnerable web browser that is communicating with an infected server.'
Just to point out: MiTM attacks are NOT web specific (which is the way I interpret your latter part of that sentence but I presume that was merely an oversight). Actually, openssh has blatant warnings (including possible MiTM attacks) (formatting not maintained here and I've removed the '@'s which surround the first line on all sides and I've removed all but the warning itself):
'WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED!
IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY!
Someone could be eavesdropping on you right now (man-in-the-middle attack)!
It is also possible that a host key has just been changed.'
You are then forced to address the problem before you're allowed to login. This error might be because the server installed from scratch (for one example valid cause) but despite it saying warning it won't let you proceed; you have to fix it (they also advise contacting the system administrator if you actually aren't the admin and aren't aware of why it changed and if it was legitimately changed).
Does this include Android – cannot see an Accelerator App?
One of the easiest wins for performance and security is to immediately flatten the HDD on a new laptop, especially at the cheaper end of the market, and install a preferred OS minus all the crapware/AV 'trials' etc. I have done this countless times for non-techy friends – Plenty have initially said that there's no need as the new laptop usually runs well enough out of the box, then a few months down the line it all starts crunching and gets rebuilt (ideally with an SSD). The laptop is then better than new. I would urge anybody to do the same and avoid vendor malware if they possibly can..