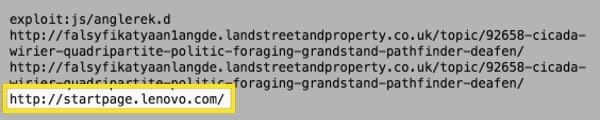
Attackers recently compromised the start page used by Lenovo PC customers in order to redirect users to the malicious Angler exploit kit.
F-Secure security advisor Sean Sullivan explains in a blog post how upstream detection reports from the security firm’s clients indicate that the compromise occurred on March 13th:
“For some (relatively short) period of time, the portal site ‘startpage.lenovo.com’ redirected visitors towards the infamous Angler exploit kit.”
The notorious Angler exploit kit is well known in the world of crypto-ransomware.
Back in October of last year, researchers with Cisco’s Talos Security Intelligence and Research Group helped block about half of the exploit kit’s malicious activity. That is an impressive feat, though Angler remains active to this day.
Most recently, the Angler exploit kit was observed in a drive-by campaign that dropped CryptoWall 4.0 ransomware, two malvertising campaigns targeting Skype users and the Wajam browser add-on, and even a Guardian article unknowingly ironically entitled, “Cybercrime: is it out of control?”

In the meantime, Lenovo is still engaged in an ongoing struggle to regain the trust of its users following the Superfish fiasco last year.
 The Chinese computer technology company did promise a safer PC experience shortly afterwards, but the discovery of rootkit-like utilities, privilege escalation vulnerabilities, and insecure default password configurations in its SHAREit application suggest this is a battle that it is struggling to win.
The Chinese computer technology company did promise a safer PC experience shortly afterwards, but the discovery of rootkit-like utilities, privilege escalation vulnerabilities, and insecure default password configurations in its SHAREit application suggest this is a battle that it is struggling to win.
It’s not even the first time Lenovo has had embarrassing security failures in relation to its online presence. Who can forget that a year ago, the company’s website briefly had its DNS entries hijacked by the Lizard Squad hacking group in order to play a song from teeny-bop Disney flick “High School Musical”?
It’s unlikely this compromise will help Lenovo improve upon that negative image. With that in mind, we can only hope that Lenovo’s start page received very little traffic on Sunday evening.
Exploit kits such as Angler scan unpatched software for vulnerabilities that they can leverage to install malware onto victims’ computers. It is therefore important that users always implement software updates as soon as they become available and exercise caution when clicking on ads they come across on the web.
Update: It appears that attackers did not compromise Lenovo’s website directly. According to a report published by Proofpoint, Lenovo’s start page is just one of several websites to have been compromised in a recent malvertising campaign.
Websites affected by this campaign ultimately redirect users to the Angler exploit kit, a familiar dropper of crypto-ransomware.


