
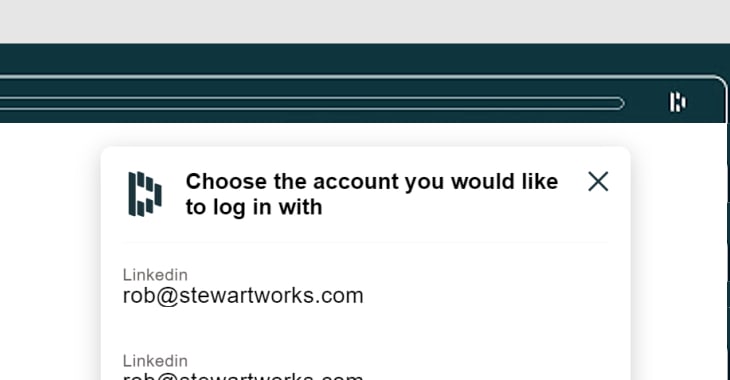
Popular password manager LastPass says that it has fixed a vulnerability in its Chrome and Opera browser extensions that could have potentially seen an attacker steal the username and password filled-in by the software on the previously-visited website.
In other words, you are someone using LastPass, you use LastPass to log into a website, you then visit a malicious webpage that – through some jiggerypokery – tricks the browser extension into serving up the password again.
As the LastPass team explains in its blog post, exploitation of the security hole is not completely straightforward:
“To exploit this bug, a series of actions would need to be taken by a LastPass user including filling a password with the LastPass icon, then visiting a compromised or malicious site and finally being tricked into clicking on the page several times. This exploit may result in the last site credentials filled by LastPass to be exposed.”
Even though there’s no evidence that the flaw was maliciously exploited, it makes sense to patch it.
LastPass version 4.33.0 and later fix the vulnerability, and according to the developers users’ browser extensions will update automatically without any user action required.
If you want to double-check the version number of your LastPass browser extension, click on the LastPass icon in the corner of your browser’s menu, and select the “Tools” option from the submenu.
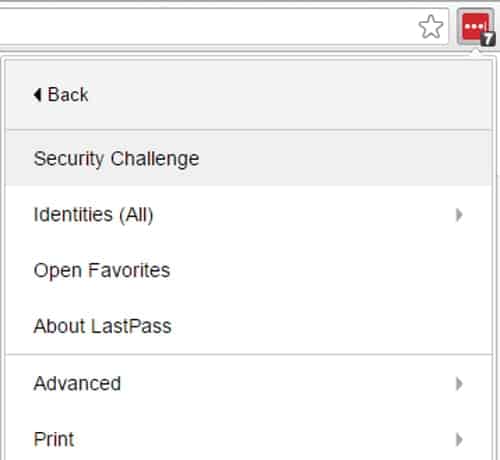
Choosing “About LastPass” will then show you the version number and build date of the browser plugin.
Google bug hunter extraordinaire Tavis Ormandy discovered the vulnerability which was in how the browser extension generated pop-up windows, and informed LastPass’s developers.
Details of the flaw were only made public after a security fix was published.
LastPass offers up to $5000 to security researchers who responsibly disclose details of flaws through its bug bounty programme.
Although it can be unsettling to hear about vulnerabilities in password managers as they contain such sensitive data, I continue to believe that the vast majority of users are much safer using a password manager than going without.
And, it should go without saying that users should defend their online accounts with multi-factor authentication and remain wary of suspicious links.


Improve your security by copying your password in plaintext to the clipboard first. Strewth. Good to hear LastPass got the fix in place quickly.