Kitchenware store Lakeland has emailed customers telling them that hackers managed to gain unauthorised access to its web systems and databases late last week.
Although the company has confirmed that hackers accessed “two encrypted databases”, it has been unable to ascertain whether information was stolen.
Perhaps reasonably, the firm has chosen to assume the worst, and reset all customers’ passwords and asked them to choose new passwords next time they login.
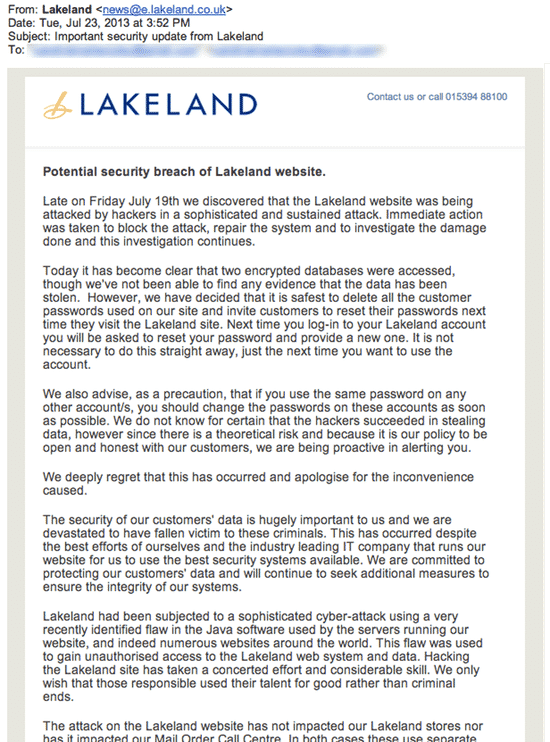
Part of the email reads:
Late on Friday July 19th we discovered that the Lakeland website was being attacked by hackers in a sophisticated and sustained attack. Immediate action was taken to block the attack, repair the system and to investigate the damage done and this investigation continues.
Today it has become clear that two encrypted databases were accessed, though we've not been able to find any evidence that the data has been stolen. However, we have decided that it is safest to delete all the customer passwords used on our site and invite customers to reset their passwords next time they visit the Lakeland site. Next time you log-in to your Lakeland account you will be asked to reset your password and provide a new one. It is not necessary to do this straight away, just the next time you want to use the account.
Lakeland has also advised customers to ensure that they are not using the same passwords anywhere else on the internet.
That’s advice that really needs to be underlined. Far too many people use the same password for multiple websites, meaning that if their password gets hacked in one place they could find other online accounts are subsequently compromised.
With good password management tools like 1Password, LastPass and KeePass available it really is inexcusable for users to still be recycling passwords rather than picking new, hard-to-crack ones.
Interestingly, in its warning emailed out to customers, Lakeland gives a clue as to how the hackers might have managed to breach its systems:
Lakeland had been subjected to a sophisticated cyber-attack using a very recently identified flaw in the Java software used by the servers running our website, and indeed numerous websites around the world. This flaw was used to gain unauthorised access to the Lakeland web system and data. Hacking the Lakeland site has taken a concerted effort and considerable skill. We only wish that those responsible used their talent for good rather than criminal ends.
Quite what Java vulnerability Lakeland is referring to isn’t currently clear, but add it to the pile of reasons (if you needed any more) why you probably want to keep as far away from that vulnerability-ridden technology as possible.


Inexcusable?! What planet are you on? As an extremely busy mother with a full on career, exactly WHEN would you like me to research password management tools? I'm sure an awful lot of busy normal people who don't have time to read all about the latest craze, gadget or app wouldn't know these exist. Although I am offended at your tone, I will amend my 'inexcusable' behaviour and utilise some type if password system, thank you for letting me know they exist – no need to be so nasty about it though.
Great.
Now you know about LastPass, KeePass and 1Password you have no excuse.
Sounds like this website has done its job. If you have time (and the energy – I know how tiring it can be looking after a child and trying to hold down a job) then please share the job by telling the world about the benefits of password management software.
Good luck for the future.
The real problem is that too many sites – Lakeland included – require you to create an account in order to buy from them. I've bought from Lakeland once, in 2009, and they've kept my data all this time? Not only is this is an obvious-to-foresee security issue but is almost certainly contrary to DPA because personal data is being kept for longer than necessary.
And even this site (https://grahamcluley.com) requires an email address which isn't necessary and is sent in plain text. Practice what you preach, Mr Cluley.
Please don't call me Mr Cluley, it makes me feel like I'm in trouble with the headmaster. Graham is just fine. :)
I'm not sure I agree that 4 years, in your case, is an excessive length of time for Lakeland to keep a record of the email address associated with the online account that you created for the purpose of purchasing items from them. What length of time would you suggest should elapse before an online store should delete records of your account, and require you to create a new account or make a purchase face-to-face?
If you feel that Lakeland has acted inappropriately in regard to that section of the Data Protection Act you should lodge your complaint with the Information Commissioner's Office.
I actually found Lakeland's approach to communicating with their customers quite refreshing, particularly if you compare with other recent examples of organisations finding themselves in the middle of a data breach.
And just to be clear regarding this site (https://grahamcluley.com). You don't have to give me an email address at all, unless you want to leave a comment. I ask for an email address so that I can have an off-site conversation with you about issues you have raised (if appropriate) and so that you benefit from a pretty gravatar mugshot (if you have set one up at gravatar.com). Users find it easier to follow conversations I find when they have some way of telling commenters apart.
If you don't want to give me your email address that's absolutely fine with me. Either enter a bogus email address (I don't verify the email addresses, so you can claim to be Mother Theresa or Zaphod Beeblebrox if you want to) or sign in via Google (which is over https, natch).
If you have any concerns, I suggest that that's what you do.
While I welcome their approach to resetting passwords and informing users of the breach, I do think they could have done it sooner, given the breach was last Friday.
They also claim they are being open and honest – if that were truly the case, they would disclose more info about the attack to help other retailers and their customers prepare for future breaches.
I'm one of the good guys who seeks out the bad ones on a daily basis and from what I see each and everyday is that commercial organisations do not take all the precautions they should in protecting there clients private details.
If I put my private details into a form on a website I expect the owners to take sufficient precautions with my information so that it is not hacked or stolen and then used to commit fraud. I don't agree with you that the answer is to buy a password generator and as the lady said half of the population would not even know what one was!
Each enterprise has a "Duty of Care" to its customer and part of that duty of care is to protect clients information, so in this particular case with Lakeland if this is a known exploit why had they not protected themselves against the threat, probably because they where not aware of the threat until it happened.
Therefore there processes and procedures are not adequate enough because if they where they would have known of the threat and taken preventative action before the site was hacked.
Cheers