Two security researchers say that they have found multiple ways to bypass Bouncer, Google’s automated system for detecting malicious Android apps before they are made available in the Google Play store.
Two security researchers say that they have found multiple ways to bypass Bouncer, Google’s automated system for detecting malicious Android apps before they are made available in the Google Play store.
Google automatically runs newly uploaded apps through Bouncer before making them available to the general public. Bouncer emulates an Android smartphone, inside a virtual environment, and attempts to tell if the submitted app is capable of stealing data, sending expensive SMS messages, steal information, and so forth.
The challenge for malware authors, therefore, is to see if they can bypass Bouncer’s checks and sneak their malicious Android apps into the Google Play store.
Security researchers Charlie Miller and Jon Oberheide claim to have found multiple ways for Android apps to realise they are being tested by Bouncer and behave differently during the examination. If apps hide their malicious intentions while they are being tested (in other words, tell the difference between running on a real Android phone and running on Bouncer’s virtual environment) they could avoid detection.
 With Bouncer subverted, malicious apps could make their way onto Android smartphones belonging to the general public.
With Bouncer subverted, malicious apps could make their way onto Android smartphones belonging to the general public.
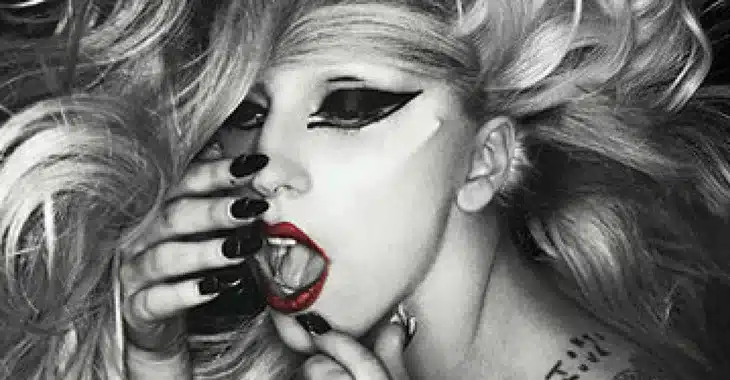
Miller and Oberheide discovered a number of tell-tale signs that their app was running on Google Bouncer rather than a real smartphone. For instance, their investigation discovered that Google’s simulations were all registered to the same account (), had only one contact in the address book () and contained a photo of Lady Gaga and an image of a cat.
If, without permission, an app tried to access the address book contact, or steal the Lady Gaga image, Bouncer would know the app being analysed was suspicious.
In a YouTube video published before their talk, Jon Oberheide demonstrates one of the ways in which Bouncer can be bypassed.
In the particular example shown, an app uploaded to the Google Play Android market can tell it is running on Bouncer’s emulated Android device, and remotely give the researchers access – allowing them to learn more and fingerprint the environment.
[youtube=http://www.youtube.com/watch?v=ZEIED2ZLEbQ&rel=0&w=500&h=311]
The concept of malware using smart tricks to determine if it is being analysed or examined in a virtual environment – rather than a potential victim’s real device – is not a new one. For instance, there has been much Windows malware over the years which has incorporated anti-sandboxing, virtual machine detection and anti-debugging tricks to make analysis more difficult.
Miller and Oberheide, who are due to demonstrate their findings at a security conference in New York City today, shared their research in advance with Google, who presumably have taken steps to improve their systems.
There seems little doubt that we will see criminals using similar tricks when attempting to get their malware into the Google Play marketplace in the future. As ever, the battle continues with one side trying to get an advantage over the other.
By the way, if you’re worried about protecting your Android smartphone or tablet against the rising tide of Android malware be sure to check out the free beta of Sophos Mobile Security.